
Hi
If you want to allow the 'superuser1' to log on to any workstation but only access the network share from one specific workstation, then I'm not aware of an option to do this.
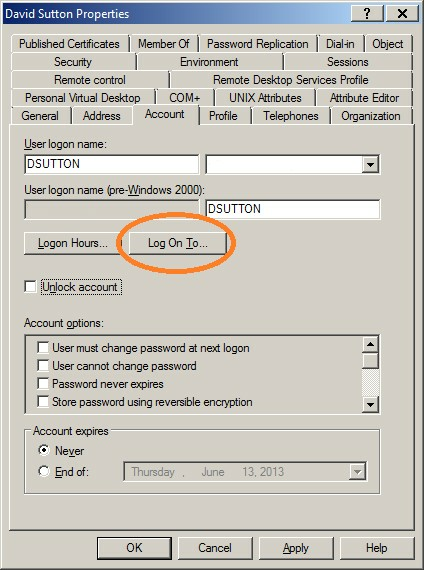
If you want to restrict the superuser1 to only log onto to one specific workstation, you could use the "Deny access to this computer from the network” right and apply this policy to all machine except the one the user is allowed to use. In this scenario it would be easier to use the Log on to workstation restrict on the user account.
There isn't an option to use permissions either, a user's access token, which contains the groups they are a member of, is used to grant access to network shares. The workstation or server the user is connecting from is not included in the user's access token. Therefore it's not possible to use permissions to restrict access from a specific machine using permissions.
Probably the better option is to implement a delegation model, and separate the permissions required by the user to do their job function, and the elevated privileges required to manage the share and assign these to a separate admin account, which can be restricted separately.
Gary.
