You are using Delegated permissions, the application access policy restrictions apply only to application permissions. In the delegated model, the effective permissions are the cross-section of the user permissions and the permissions granted to the app, they are not affected by the application access policy. To restrict access for delegate scenarios, use the built-in RBAC controls in Exchange Online.
Limiting application permissions to specific Exchange Online mailboxes
 i successfully create a web application that allows access to my email via a token. The issue is it reads all mailboxes instead of just 1.
i successfully create a web application that allows access to my email via a token. The issue is it reads all mailboxes instead of just 1.
I followed the following document
https://learn.microsoft.com/en-us/graph/auth-limit-mailbox-access#configure-applicationaccesspolicy
I even tested it as noted but when I read emails it still shows all email messages from all mailboxes. This is a problem.
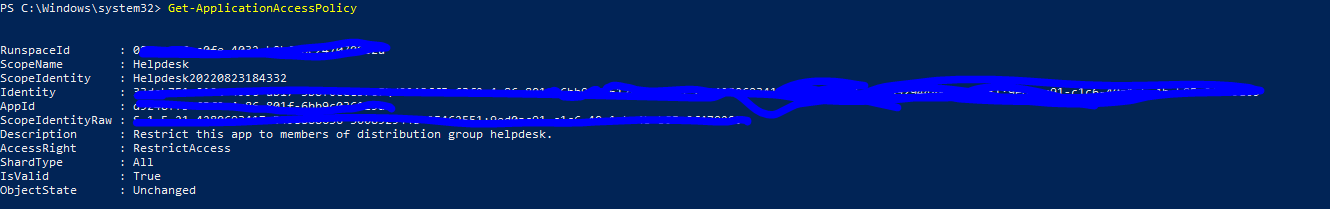
i ran this command
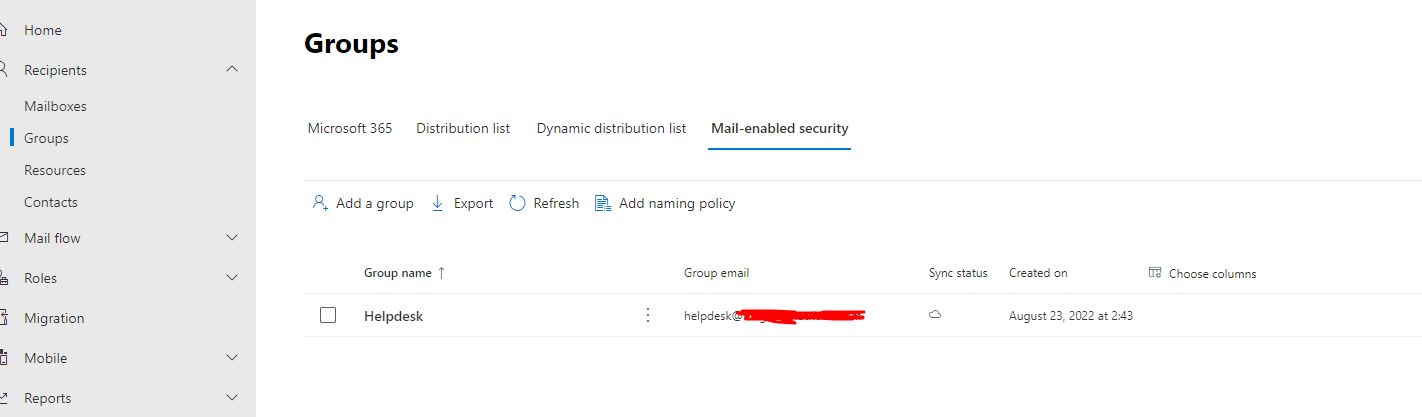
New-ApplicationAccessPolicy -AppId d9248ff5-63f2-4e86-801f-6bb9c036129d -PolicyScopeGroupId 9ed0ac91-c1c6-40a1-ba4b-b85c9f479209 -AccessRight RestrictAccess -Description "Restrict this app to members of distribution group helpdesk."
I included the email i wanted to allow access in this group.
Then i created a separate group (after the first didnt work several hours later) to do the opposite.
and ran the following:
New-ApplicationAccessPolicy -AccessRight DenyAccess -AppId "d9248ff5-63f2-4e86-801f-6bb9c036129d" -PolicyScopeGroupId "RestrictedMailGraphEmails" -Description "Do not allow emails in this list to be accessed via app"
still no change.
Please help.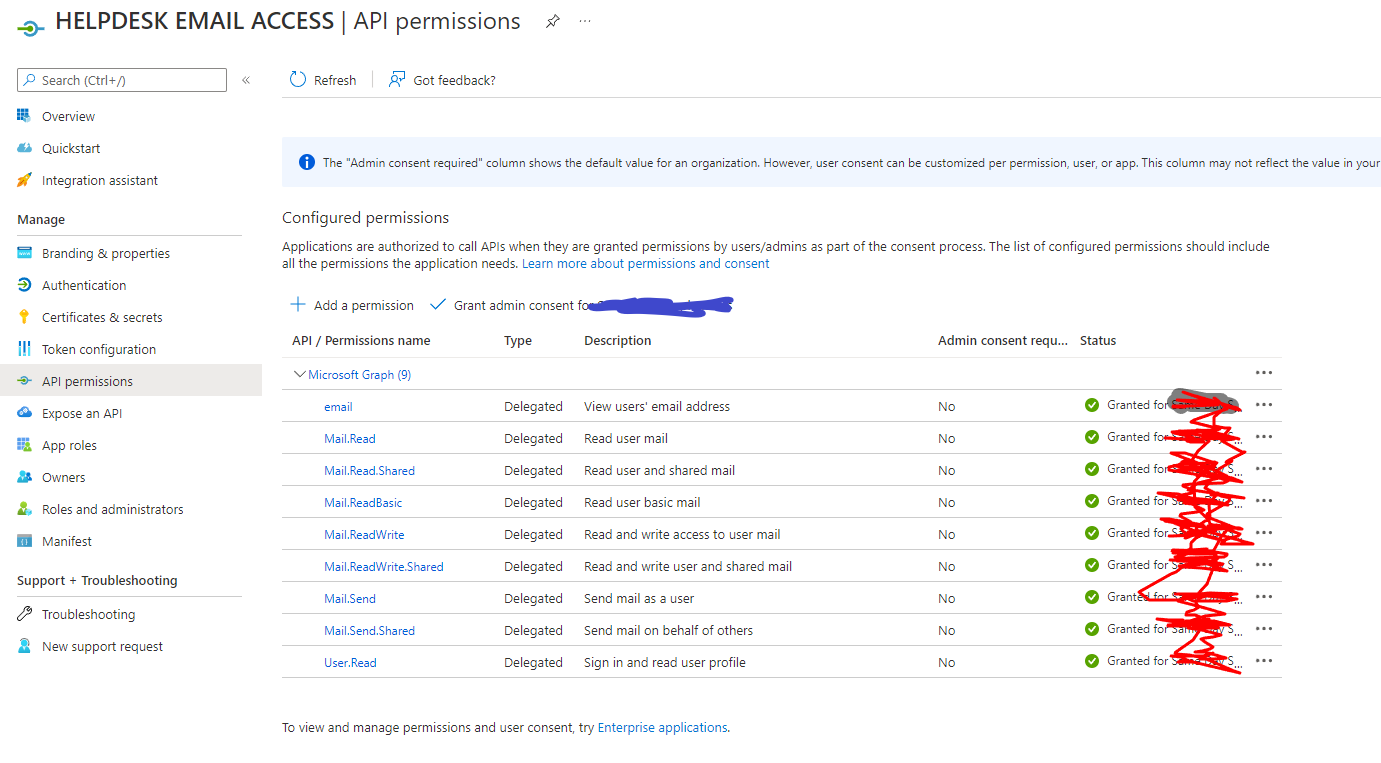
2 answers
Sort by: Most helpful
-
-
 Amit Singh 4,846 Reputation points
Amit Singh 4,846 Reputation points2022-08-24T11:05:01.433+00:00 Instead of creating a self-signed cert for the app registration, create a secret. When you use a secret Connect-MgGraph, it does not have a way to authenticate using it, and so you have to resort to Invoke-RestMethod to authenticate.
Check this article - https://rakhesh.com/azure/limit-app-registration-to-specific-mailbox/
