Hi,
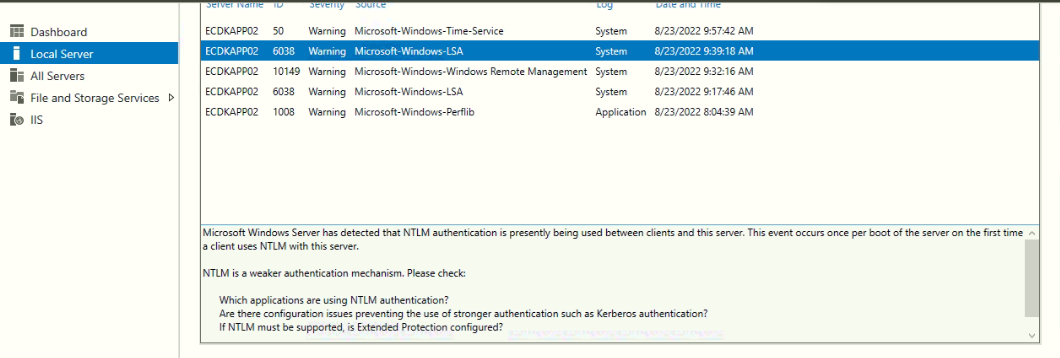
By default, Windows server does not report where NTLM requests are coming from, so auditing needs to be enabled. It seems some application or some device is sending NTLM requests and events are logged to notify the NTLM usage for this investigation we will have to enable auditing.
Please follow these link and steps to enable and audit --
Enabling DC NTLM Auditing Group Policy
Create a New Group Policy Object in your domain. This policy should be linked to your Domain Controllers by OU or Security Filtering.
These policy settings will report what is using NTLM without blocking anything:
Computer Configuration->Policies->Windows Settings->Security Settings->Security Options->Network security: Restrict NTLM: Audit NTLM authentication in this domain. Policy Setting: Audit All
Computer Configuration->Policies->Windows Settings->Security Settings->Security Options->Network security: Restrict NTLM: Audit Incoming NTLM Traffic. Policy Setting: Enable auditing for all accounts
Computer Configuration->Policies->Windows Settings->Security Settings->Security Options->Network security: Restrict NTLM: Outgoing NTLM traffic to remote servers. Policy Setting: Audit all
After enabling these policies, Event ID 8001, 8002, 8003, and 8004 will be recorded in Event Viewer under Applications and Services Logs->Microsoft->Windows->NTLM->Operational.
Post this GPO is deployed you may be able to trace down which applications are using insecure protocols. You may need to link the policy to the server that is making the request to get additional information about which process on that server is making the request.
==
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.