Hello @Banerjee, Somdutta ,
Based on your follow-up question above.
If someone with contributor/owner roles makes a configuration change -can we prevent it or do we have any mechanism to alert on it.
I do not think there is a way to prevent this, but you can set alerts based on the Activity logs of your Bastion.
You can refer to this documentation setting up these alerts. I tried setting up sample alert for my Bastion resource and followed below mentioned steps.
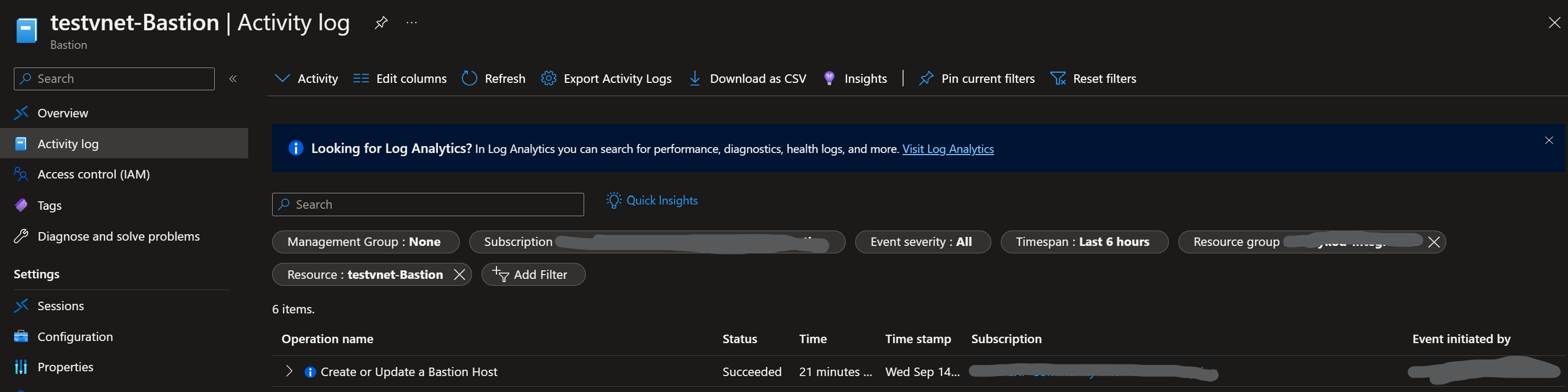
From the activity logs I selected the Create or Update a Bastion Host category. (You can select the categories based on your requirements)
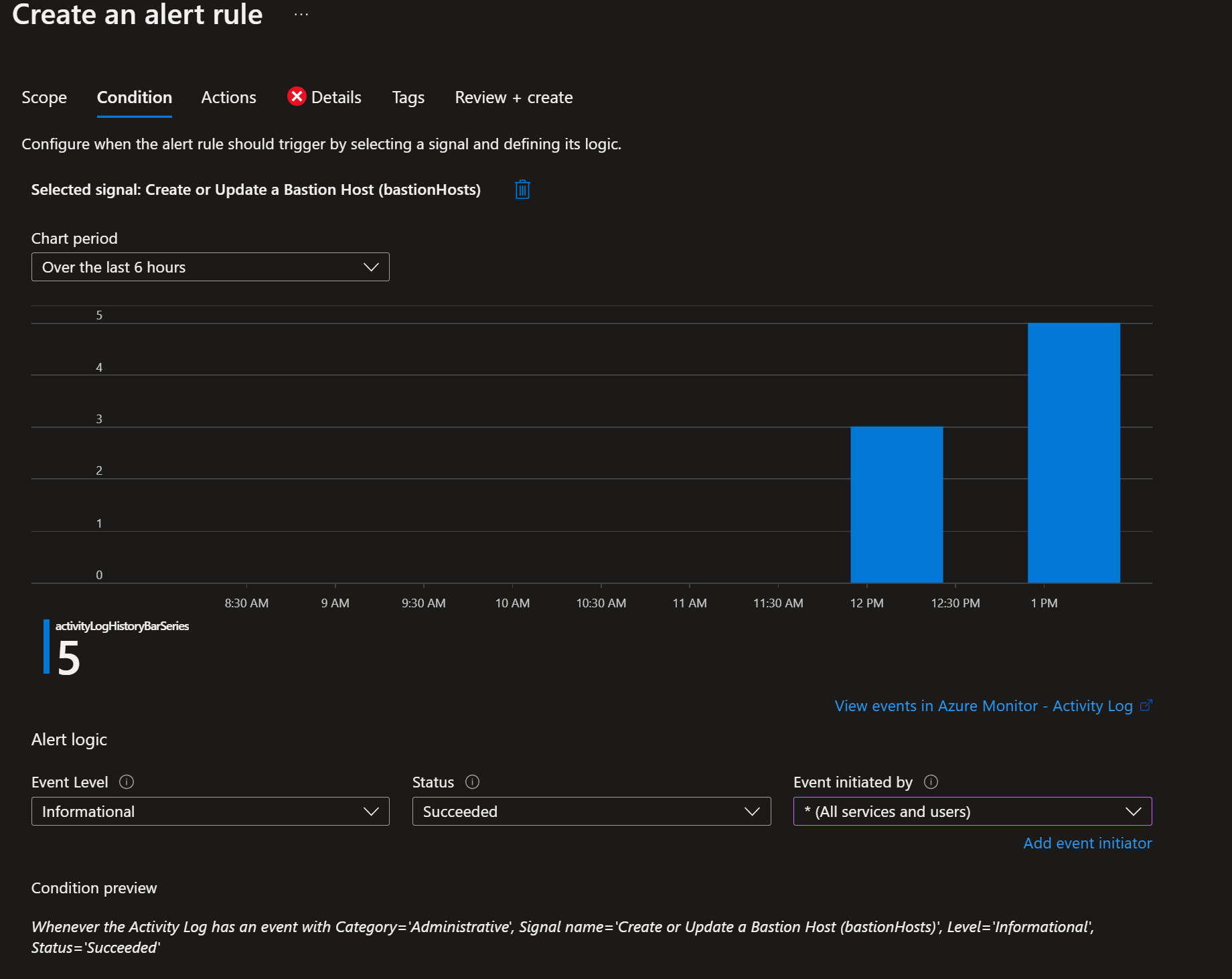
You can click on the specified category and then create an alert for the same.

You can specify the conditions/ actions for these alerts like who will receive these alerts etc.
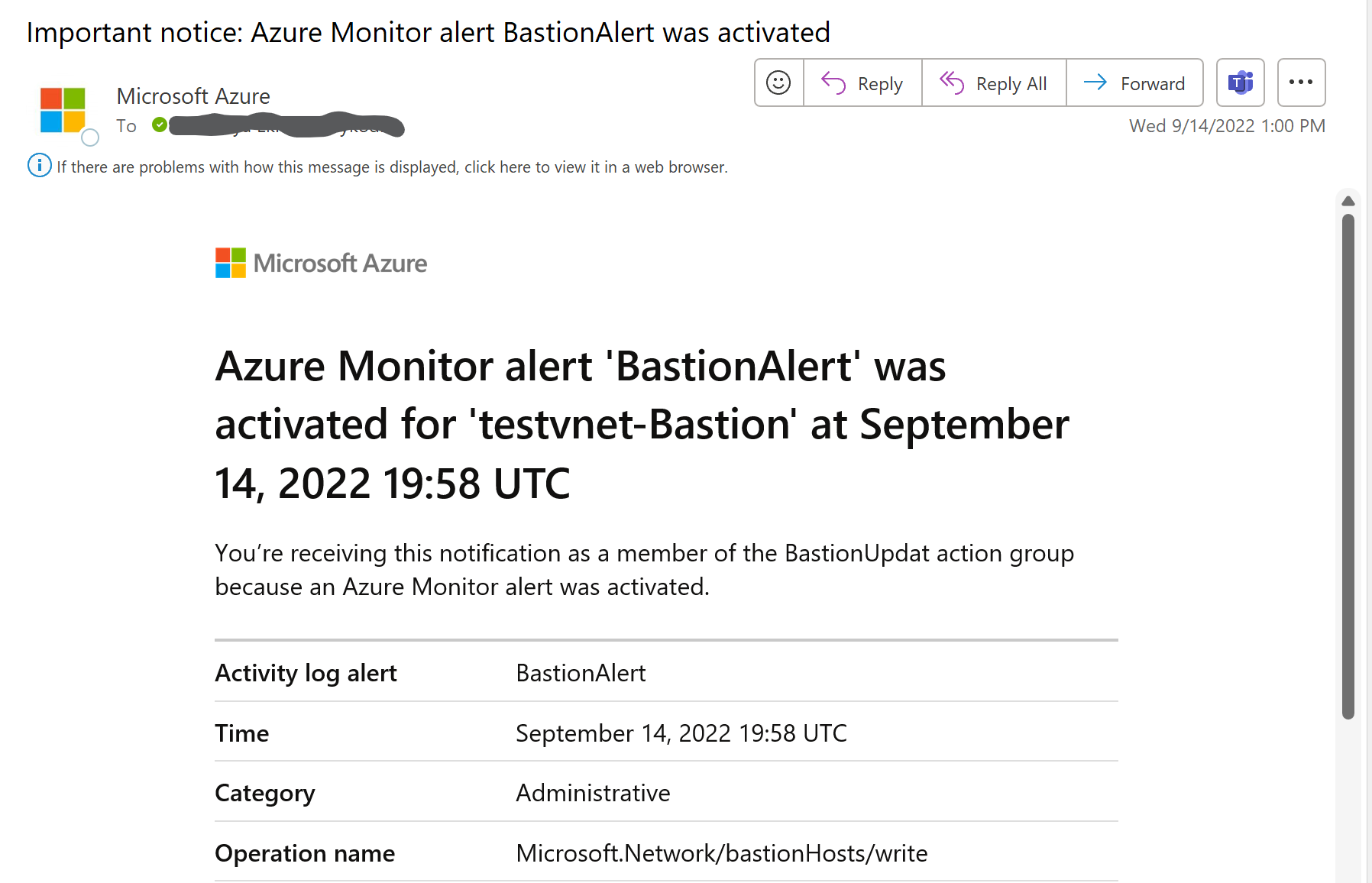
Below is the Sample alert I received after I updated the config of the testvnet-Bastion resource.
Hope this helps. Please let me know if you have any questions. Thank you!
Additional references:
https://learn.microsoft.com/en-us/azure/role-based-access-control/best-practices