Protecting you from malware
One of the things we talk quite a bit about with Windows 8 is making sure Windows is a safe, secure, and reliable computing environment. We have always provided a broad range of solutions for achieving these goals and work closely with a broad range of industry partners. We continue to enhance these capabilities with Windows 8 while making sure you always have choice and control over how to protect and manage your PC. With Windows 8 we are extending the protections provided by Defender to address a broader range of potential threats. Jason Garms, the group program manager of our reliability and security team authored this post that represents work across several teams. --Steven
I’m excited to share with you some investments we are making in Windows 8 to better protect you against the constantly changing landscape of malicious software (“malware”). In this blog I will talk about enhancements to mitigation features that help protect you against exploits used by malware, improvements to Windows Defender to provide you with real-time protection from all categories of malware, and the use of URL and application reputation to help protect you against social engineering attacks.
A view of the current landscape
Criminal attacks continue to evolve and malware has become their standard weapon against anyone who uses the Internet—on traditional form-factor devices, as well as on mobile devices like tablets and phones. Malware targets all operating systems and browsers, and in recent years, criminal attacks against applications have increased substantially.
Criminals also use social engineering to trick you into performing actions that put you at risk. An increasingly common social engineering strategy uses online advertising campaigns to lure you to a site that installs malware on your computer.
An economy has developed around building reliable vulnerability exploits, which criminals buy to help distribute their malware. Criminals make money from their malware, so they invest in ways to keep it alive such as producing a higher quantity of malware, updating it more frequently—e.g. multiples times each day—and increasing its size and complexity. Some malware is as complex as commercial applications.
Secure by design
We use the Security Development Lifecycle (SDL) to build Windows with the best security design, development and testing practices available. Some highlights include:
- Threat modeling and security design reviews. During the design process we consider how criminals might seek to attack features and scenarios, and incorporate this analysis into our designs.
- Writing secure code. Training and code quality tools help to prevent common coding issues from entering the Windows source code.
- Penetration testing. Security engineers take an attacker’s perspective when reviewing a completed set of features that make up a scenario.
- Security code reviews. Security engineers provide additional security-oriented code reviews for highly sensitive components.
- Security tools. Tools continuously updated with the latest state of the art in finding and exploiting software provide a scalable solution to improve existing code.
Making it harder to create an exploit on Windows 8
With Windows XP SP2, we began creating defenses called mitigations that make it difficult to develop reliable exploits for security vulnerabilities. Each subsequent version of Windows has continued to expand and improve on these mitigations, because a single mitigation feature can break an entire class of exploits. Windows 8 includes mitigation enhancements that further reduce the likelihood of common attacks. Some of these improvements include:
- Address Space Layout Randomization (ASLR). ASLR was first introduced in Windows Vista and works by randomly shuffling the location of most code and data in memory to block assumptions that the code and data are at same address on all PCs. In Windows 8, we extended ASLR’s protection to more parts of Windows and introduced enhancements such as increased randomization that will break many known techniques for circumventing ASLR.
- Windows kernel. In Windows 8, we bring many of the mitigations to the Windows kernel that previously only applied to user-mode applications. These will help improve protection against some of the most common type of threats. For example, we now prevent user-mode processes from allocating the low 64K of process memory, which prevents a whole class of kernel-mode NULL dereference vulnerabilities from being exploited. We also added integrity checks to the kernel pool memory allocator to mitigate kernel pool corruption attacks.
- Windows heap. Applications get dynamically allocated memory from the Windows user-mode heap. Major redesign of the Windows 8 heap adds significant protection in the form of new integrity checks to help defend against many exploit techniques. In addition, the Windows heap now randomizes the order of allocations so that exploits cannot depend on the predictable placement of objects—the same principle that makes ASLR successful. We also added guard pages to certain types of heap allocations, which helps prevent exploits that rely on overrunning the heap.
- Internet Explorer. “Use-after-free” vulnerabilities represented nearly 75% of the vulnerabilities reported in Internet Explorer over the last two years. For Windows 8, we implemented guards in Internet Explorer to prevent an attacker from crafting an invalid virtual function table, making these attacks more difficult. Internet Explorer will also take full advantage of the ASLR improvements provided by Windows 8.
Keeping malware off your PC
Having effective malware protection is important for any device connected to the Internet and almost all Windows PCs sold today include a traditional antimalware solution, though it is often a time-limited or trial version.
Shortly after Windows 7 general availability in October 2009, our telemetry data showed nearly all Windows 7 PCs had up-to-date antimalware software. However, a few months later the trend started to decline month-to-month, likely reflecting antimalware trial subscriptions expiring. A year later, at least 24% of Windows 7 PCs did not have current antimalware protection. Our data also shows that PCs that become unprotected tend to stay in this unprotected state for long periods of time. And when antimalware software is even one week out of date, its ability to protect against new malware drops significantly.
We believe that all Windows 8 users should be protected by traditional antimalware software that provides an effective, industry-recognized level of protection. There are a lot of great antimalware solutions available that we expect will be updated to protect Windows 8 PCs and we believe most PC makers will continue to ship Windows PCs with these solutions installed.
Windows Defender
If you don’t have another solution installed, Windows 8 will provide you protection with a significantly improved version of Windows Defender.
Improved protection for all types of malware. The improvements to Windows Defender will help protect you from all types of malware, including viruses, worms, bots and rootkits by using the complete set of malware signatures from the Microsoft Malware Protection Center, which Windows Update will deliver regularly along with the latest Microsoft antimalware engine. This expanded set of signatures is a significant improvement over previous versions, which only included signatures for spyware, adware, and potentially unwanted software.
In addition, Windows Defender will now provide you with real-time detection and protection from malware threats using a file system filter, and will interface with Windows secured boot, another new Window 8 protection feature.
When you use a PC that supports UEFI-based Secure Boot (defined in the UEFI 2.3.1 specification), Windows secured boot will help ensure that all firmware and firmware updates are secure, and that the entire Windows boot path up to the antimalware driver has not been tampered with. It does this by loading only properly signed and validated code in the boot path. This helps ensure that malicious code can’t load during boot or resume, and helps to protect you against boot sector and boot loader viruses, as well as bootkit and rootkit malware that try to load as drivers.
The same interfaces for secured boot used by Windows Defender, as well as all APIs used by Windows Defender, are available for use by our antimalware partners to deliver additional protection to Windows customers.
- Improved user experience. We have designed Windows Defender to be unobtrusive for most daily usage, and will notify you only when you need to perform an action, or critical information demands your attention. Windows Defender will also use the new Windows 8 maintenance scheduler to limit interruptions.
- Improved performance. Traditionalantimalware technologies are well known for impacting system performance. It’s not uncommon that running antimalware software doubles the amount of time required for core scenarios like file copy and boot. As you read in last week’s blog entry, we have a lot of people working on system performance and Windows Defender dramatically improves performance on all key scenarios compared to common antimalware solutions on Windows 7, while maintaining strong protection. For example, Windows Defender with its full protection functionality enabled adds only 4% to boot time, while dramatically reducing CPU time during boot by 75%, disk I/O by around 50MB, and peak working set by around 100MB.
These same improvements benefit energy efficiency, meaning Windows Defender consumes less power, and gives you longer battery life.
We’re continuing to work with antimalware partners during the Windows 8 development process so you have the best possible Windows PC experience no matter what antimalware solution you choose. We provide them with resources, such as the technical details of how we architected the performance improvements for Windows Defender, so they have the opportunity to make similar improvements to their products.
Microsoft SmartScreen for Internet Explorer and now for Windows too
Traditional antimalware software plays a critical role in defending and remediating attacks. However, reputation-based technologies can help provide effective protection against social engineering attacks before traditional antimalware signatures are available, especially against malware that pretends to be legitimate software programs.
Windows 8 will help protect you with reputation-based technologies when launching applications as well as browsing with Internet Explorer.
Since its release, the SmartScreen filter has used URL reputation to help protect Internet Explorer customers from more than 1.5 billion attempted malware attacks and over 150 million attempted phishing attacks. Application reputation, a new feature added to SmartScreen in Internet Explorer 9, provides an additional layer of defense to help you make a safer decision when URL reputation and traditional antimalware aren’t enough to catch the attack. Telemetry data shows 95% of Internet Explorer 9 users are choosing to delete or not run malware when they receive a SmartScreen application reputation warning.
We understand that Internet Explorer isn’t the only way you download applications from the Internet, so Windows now uses SmartScreen to perform an application reputation check the first time you launch applications that come from the Internet.
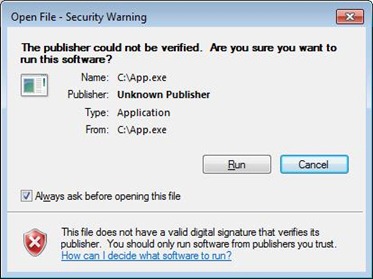
In Windows 7 when launching these downloaded applications, you get the following notification:
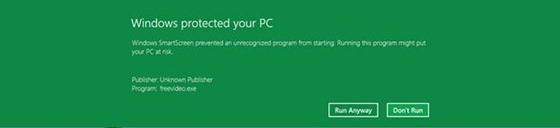
In Windows 8, SmartScreen will only notify you when you run an application that has not yet established a reputation and therefore is a higher risk:
The user experience for applications with an established reputation is simple and clean: you just click and run, removing the prompt you would have seen in Windows 7.
SmartScreen uses a marker placed on files at download time to trigger a reputation check. All major web browsers and many mail clients, and IM services already add this marker, known as the “mark of the web,” to downloaded files.
We expect average users to see a SmartScreen prompt less than twice per year and when they do see it, it will signify a higher risk scenario. Telemetry data shows 92% of applications downloaded via Internet Explorer 9 already have an established reputation and show no warnings. The same data shows that when an application reputation warning is shown, the risk of getting a malware infection by running it is 25-70%. And SmartScreen gives you administrative controls to prevent your non-techie friends or children from ignoring these warnings.
We’ve seen dramatic results with this approach in Internet Explorer and we’re happy to bring it to a broader set of Windows scenarios.
Here’s a video that shows you Windows Defender and SmartScreen URL and application reputation in action:
Download this video to view it in your favorite media player:
High quality MP4 | Lower quality MP4
In conclusion, we’ve taken a very broad approach to improving the level of protection you’ll get from malware in Windows 8, including the use of SDL processes to be secure by design, the implementation and upgrading of mitigations to help protect you against exploits used by malware, improvements to Windows Defender to provide you with real-time protection against all categories of malware, and the use of URL and application reputation to help protect you against social engineering attacks.
Thanks,
--Jason Garms