Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
I have seen this topic come up more and more recently. In many cases, organizations wish to report on and manage the Schannel registry values. Configuration Manager can help monitor, report, and implement these changes.
Before modifying any of these settings, please make sure that you understand the implications. Please review https://support.microsoft.com/en-us/kb/245030 very cafeully.
First, let's look at the register keys/values that are required for SCHANNEL SSL and TLS settings.
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Client
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Client
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Server
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Client
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client
- HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server
Under each key, there are two values that can be set, Enabled and DisableByDefault.
In a situation like this, your organization may first wish to collect data about what these registry values are set to (if anything) in the environment. To best accomplish this, we need to extend Hardware Inventory in ConfigMgr to gather these registry settings.
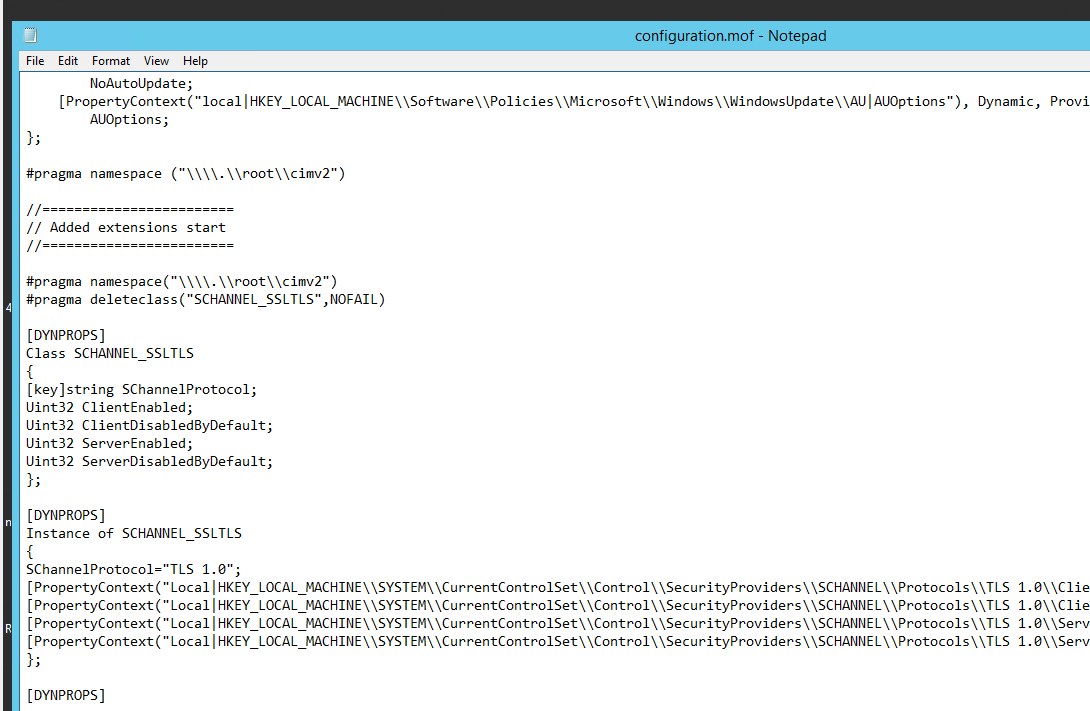
We start by creating entries for the Configuration.mof file. These entries will gather the data from the registry values and store the information in WMI using the WMI Registry Provider.
Download the ZIP file from:
Copy of content of the schannel_ssltls_conf.mof into the configuration.mof file on your CAS/Primary site.
(Place your modifications between the "Added extensions start" and "Added extensions end")
This will allow your clients to create a WMI Class named SCHANNEL_SSLTLS in root\cimv2 that will contain data from the SCHANNEL SSL and TLS registry values
You can confirm this after the clients process policy be using wbemtest or powershell to see that the class exists. If there are not values set in the registry, the instances may show null data.
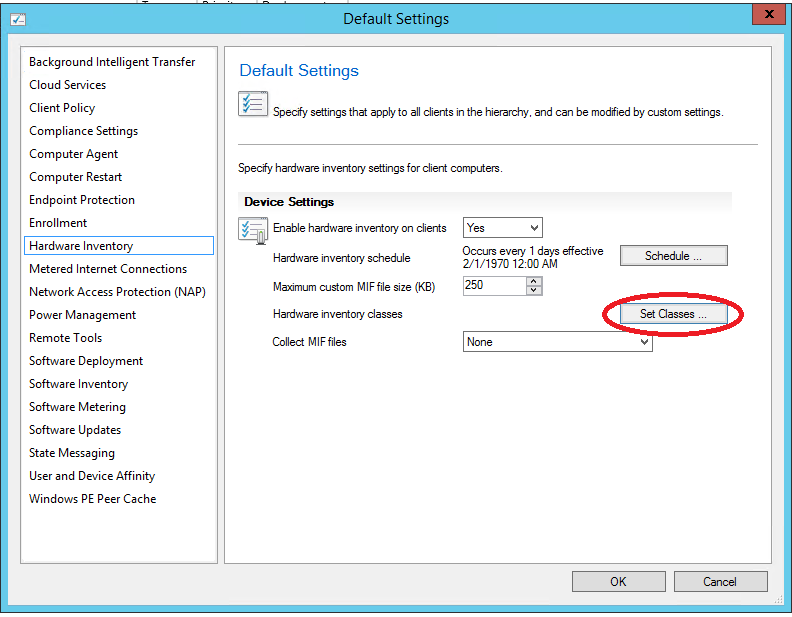
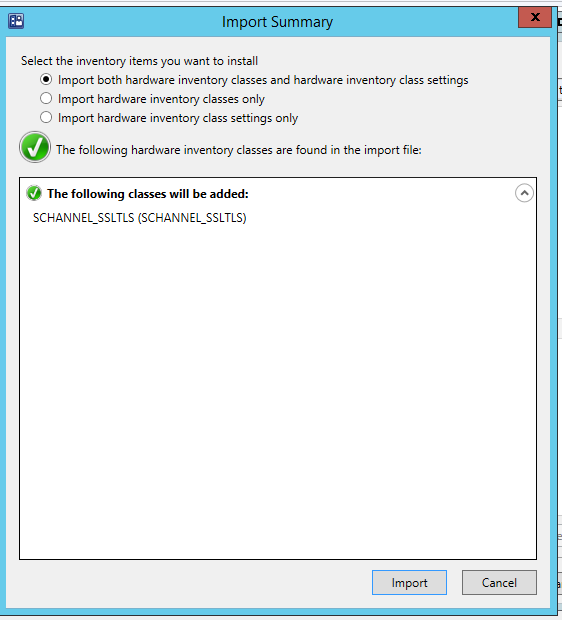
Next, the schannel_ssltls_sms.mof needs to be imported into the default clients settings hardware inventory. When importing, you can choose whether or not you wish to enable the collection of the data in the default settings or not.
Select Set Classes…
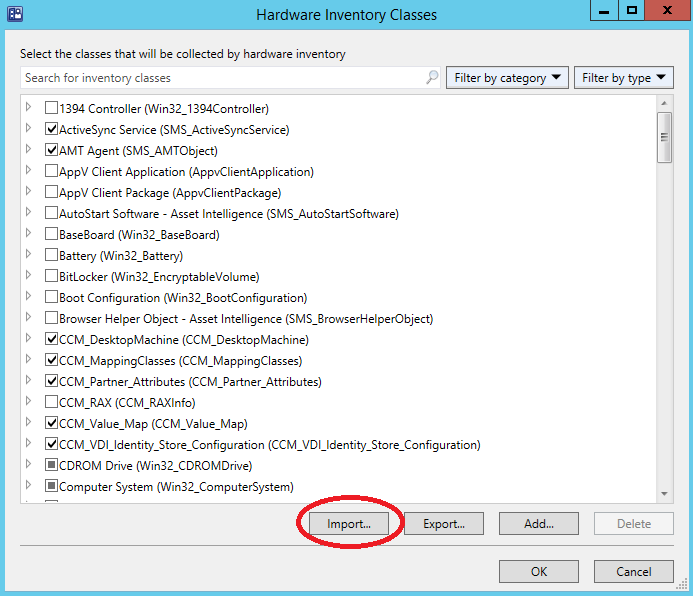
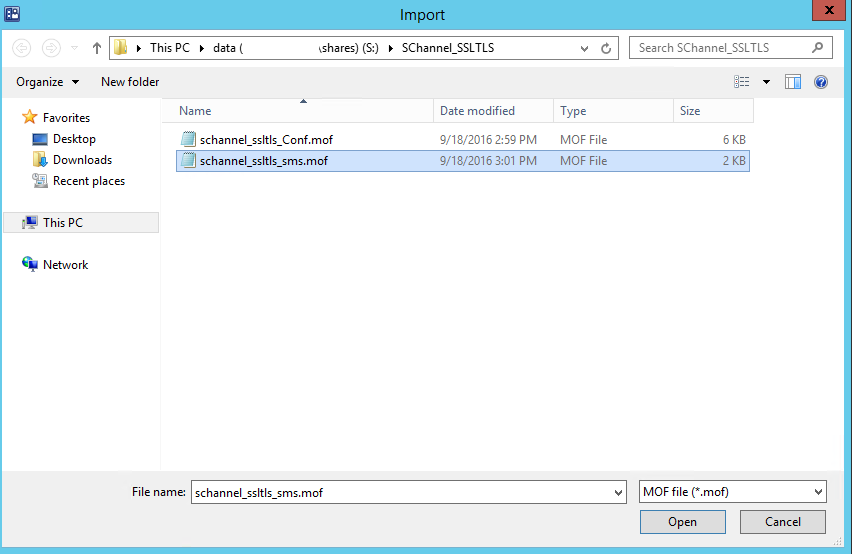
Choose Import…
Browse to where you extracted the ZIP and select the schannel_ssltls_def.mof and choose open
Select Import
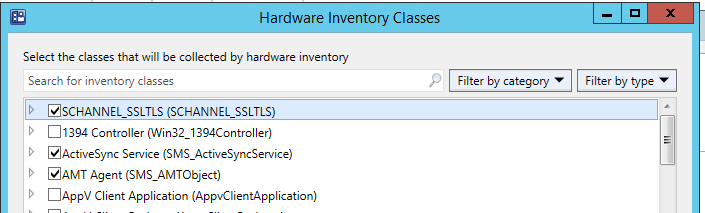
And the new class shows at the top of the list (later it will be in Alpha order). If you wish to not collect the data in the Default Client Settings, you can uncheck the box now, otherwise all clients will begin to try to attempt to collect data from the SCHANNEL_SSLTLS WMI Class.
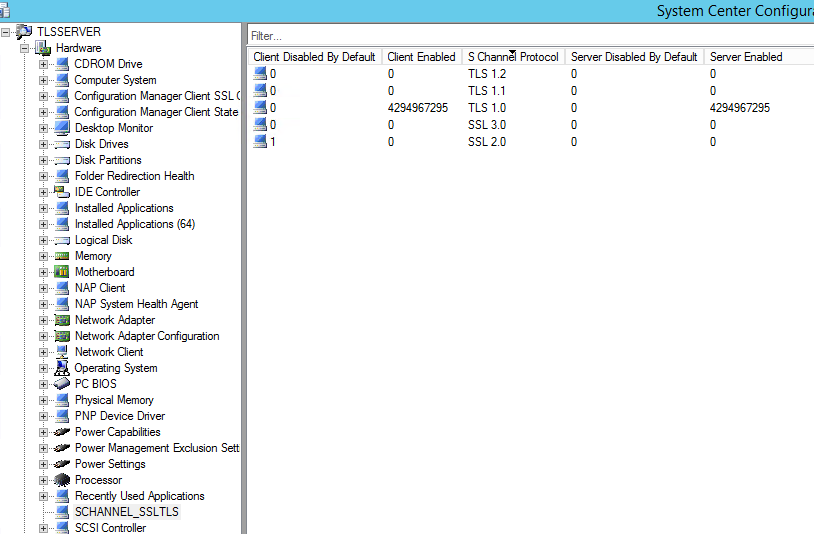
Once the clients begin to collect the data, you can view the information on each client under their Resource Explorer.
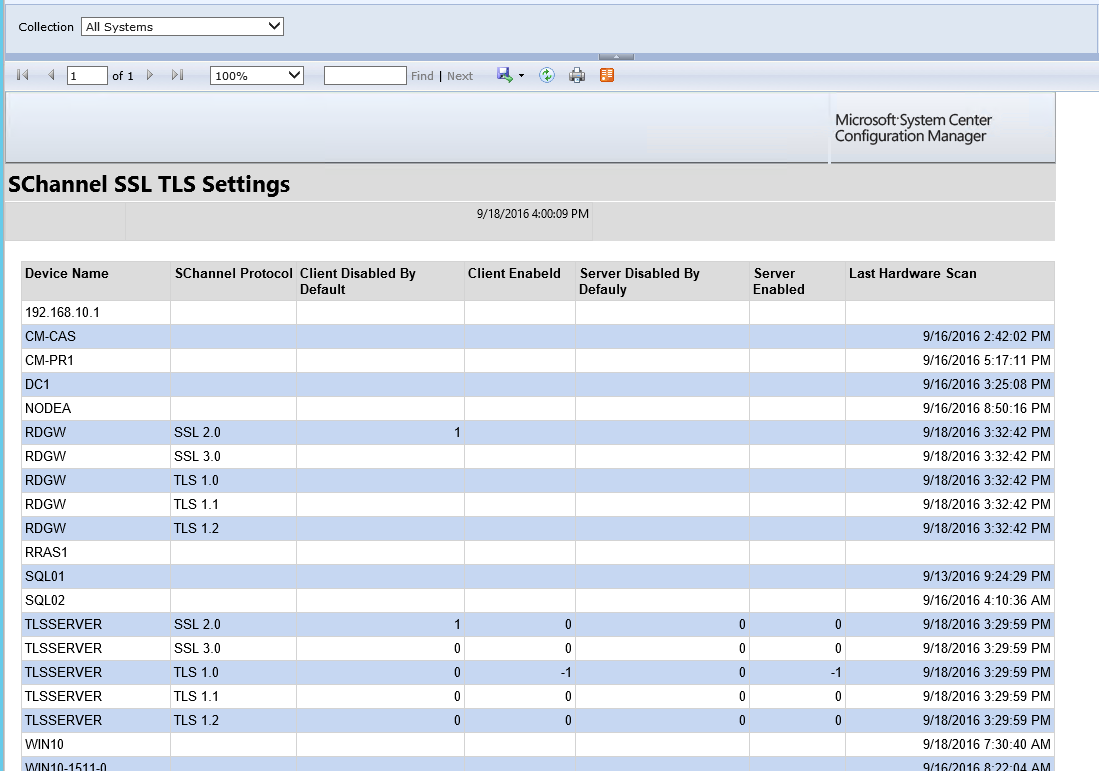
If you have used the provided files, there is also a RDL file that can be loaded into Reporting Services to provide a Per Collection repot for the Schannel Settings.
Comments
- Anonymous
September 18, 2016
Nice write-up here. - Anonymous
September 19, 2016
Importing the RDL file gives me this : Error while loading code module: ‘SrsResources, culture=neutral’. Details: Could not load file or assembly 'SrsResources, Culture=neutral' or one of its dependencies. The system cannot find the file specified. (rsErrorLoadingCodeModule)The Value expression for the report parameter ‘UserTokenSIDs’ contains an error: [BC30451] Name 'SrsResources' is not declared. (rsCompilerErrorInExpression) Any thoughts? - Anonymous
September 19, 2016
OK, just following up on previous comment - turns out it was related to a separate activity to upgrade SQL to 2014. Seems it doesn't take the SRSResources file with it and left it in the old MSSRS.11 folder.Moved the file and import worked fine.Thanks!- Anonymous
September 20, 2016
Great! Sometimes you also need to update the "datasource" on the reports you import as well.
- Anonymous