PFDAVAdmin - The Ambiguous SID issue - Fixed HERE!
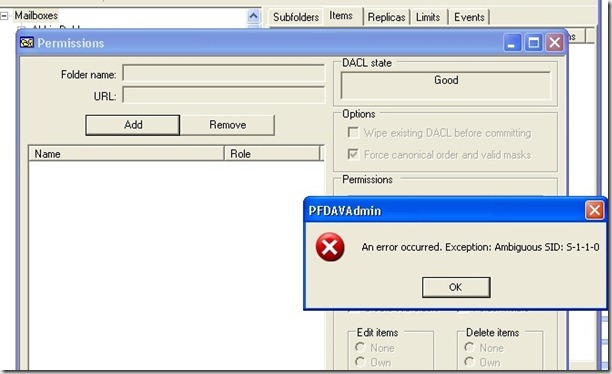
With the release of the new PFDAVAdmin a few weeks ago, some customers started running into an “Ambiguous SID” error when trying to add the Everyone group or Anonymous group in the permissions window. The error looks like this:
When you add a new entity to the permissions window, PFDAVAdmin looks up all objects with that SID to make sure it is unique. However, in some cases it’s actually normal to have more than one object with an ObjectSid that matches the Everyone or Anonymous SID. You should always have one in the configuration context under CN=WellKnown Security Principals, but many environments will also have one in the domain context under CN=Foreign Security Principals. This is when PFDAVAdmin finds two matches for these SIDs, and it chokes.
If you’re getting this error with something other than Everyone or Anonymous, then you can use the following Powershell script to figure out which objects match the SID in question.
# Find-Sid.ps1
#
# The purpose of this script is to find all objects that have a
# given SID in objectSid, sidHistory, or msExchMasterAccountSid.
#
# Syntax:
#
# .\Find-Sid <sid>
#
# Example:
#
# .\Find-Sid S-1-1-0
param([string]$sidString)
$gcRootDSE = [ADSI]"GC://RootDSE"
$gcRoot = [ADSI]("GC://" + $gcRootDSE.dnsHostName)
$sid = new-object System.Security.Principal.SecurityIdentifier($sidString)
[byte[]]$sidBytes = ,0 * $sid.BinaryLength
$sid.GetBinaryForm($sidBytes, 0)
$byteString = ""
for ($x = 0; $x -lt $sidBytes.Length; $x++)
{
$byteString = $byteString + "\" + $sidBytes[$x].ToString("X2")
}
$filter = "(|(objectSid=" + $byteString + ")(sidHistory=" + $byteString + ")(msExchMasterAccountSid=" + $byteString + "))"
$searcher = new-object System.DirectoryServices.DirectorySearcher($gcRoot, $filter, @("distinguishedName"), [System.DirectoryServices.SearchScope]::Subtree)
$results = $searcher.FindAll()
"Matching objects:"
foreach ($result in $results)
{
$result.Properties["distinguishedname"]
}