Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
The information contained in this blog POST has been compiled with the help of the following engineers:
- Alexandre Lafargue – Microsoft
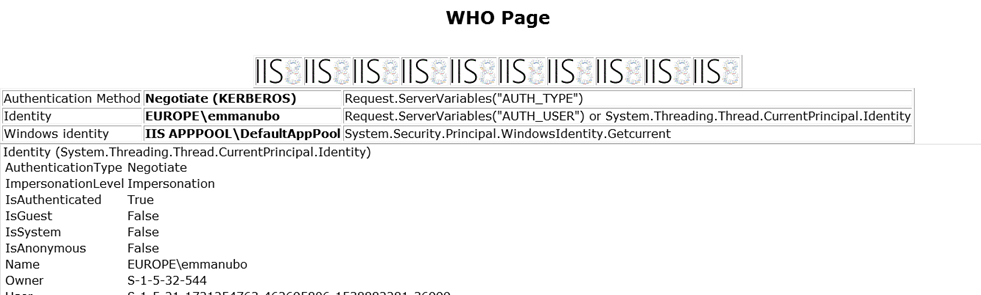
To troubleshoot authentication issues, it's generally a good idea to use a test page in order to display the current authentication method / identity used for a specific client. In our team's blog "Things to check when Kerberos authentication fails using IIS/IE", we provided a couple of links to troubleshooting pages. Unfortunately, these troubleshooting pages were lacking some features and, for this reason, our team has built its own authentication test page. Currently, our diagnosis page provides details regarding the following items:
- authentication method being used
- thread (request) and process identity for the application pool hosting the web application
- SID and group membership
- impersonation level
- dump of server variables
- test form
Here's a typical output of our diagnosis page:
Notes :
Authentication Method - authentication method used (Basic, NTLM, Kerberos, SSL…etc)
Identity – current authenticated user
Windows identity – windows identity for the current request. In this example, we can see that user is authenticated but impersonation is not enabled
ImpersonationLevel – this allows to see if current settings allow impersonation and delegation. If delegation is enabled, ImpersonationLevel=Delegation. Otherwise, ImpersonationLevel=Impersonation. Note that "ImpersonationLevel=Impersonation" doesn't mean that delegation is not possible : if you use constrained delegation, you may be able to get delegation working. Note also that Kerberos ticket may not include the delegate flag depending on Internet Explorer security zone used (see "Why does delegation fails when Kerberos authentication works" in "Things to check when Kerberos authentication fails using IIS/IE")
The diagnosis page also includes a couple of images (IIS8 logo) and a form. The images can be used to check client's behavior regarding request/session based authentication (using a network or HTTPREPLAY trace, you can check if HTTP authentication is request or session based. Using this method, I discovered last month that Kerberos authentication is now session based by default on IIS8/Windows Server 2012!).
The last item in the diagnosis page is a simple form element which can be used to check if pre-authentication is used (in this case, a network trace will show a 0 Content-Length header upon POST).
I hope the Authentication test page will allow you to resolve most authentication issues you may get in the future!
Emmanuel Boersma
Comments
Anonymous
October 17, 2014
Hey,,the page shows authentication as Kerberos...but it is unable to laod the gif images..can you help me pleaseAnonymous
January 20, 2017
Hey thereJust to let you guys know that this little tool helped me a great deal! Thanks!- Anonymous
February 01, 2017
Happy to be of service Vinicius.
- Anonymous