Microsoft Teams: Manage it using Mobile Application Management (MAM)
Introduction: The purpose of this blog post is to walk the IT administrator through how to configure Mobile Application Management (MAM) for the Microsoft Teams app.
In this blog post we will cover the following MAM topics:
- How to assign Intune licenses to end-users.
- How to configure Mobile Application Management using the Intune console in the Azure portal.
- The user experience with MAM applied (examples include cut/copy/paste, require PIN,etc).
- How to wipe data from the Microsoft Teams app only selective wipe) using MAM (and not wiping the device).
- The user experience when wiping data from the Microsoft Teams app only.
- MAM for other Microsoft mobile applications.
What is MAM? Mobile Application Management (MAM for short) offers the capability to manage only the app, and its data without having to manage the physical device itself. This is very important, as you do not need to enroll the device into Intune at all and do not need to manage the device itself, just the app. The management of the app and the data within the application is all handled through in-band provisioning (i.e. Mobile Application Management) when the user signs in to the application. This provides the following benefits:
- When management of the device itself is not possible and/or not necessary (enrolling the device into a mobile device management solution)
- Enable user liable (personal) devices to connect to enterprise resources without having to manage the device (device enrollment).
- If you want to manage apps separately from the device (for example, different device management solutions).
MAM is a capability of Intune App Protection, and is covered in more detail here: Protect app data using app protection policies with Microsoft Intune.
Requirements: MAM has the following requirements:
- Microsoft Intune license assigned to each user that MAM will be applied to. (Either Intune standalone, EMS E3, EMS E5 license SKUs).
- iOS version 8.1 or later.
- Android 4 or later.
- Windows 10
Note: There are specific prerequisites if configuring for Windows 10. See Get ready to configure app protection policies for Windows 10 for more information
Assign Intune licenses to end-users:
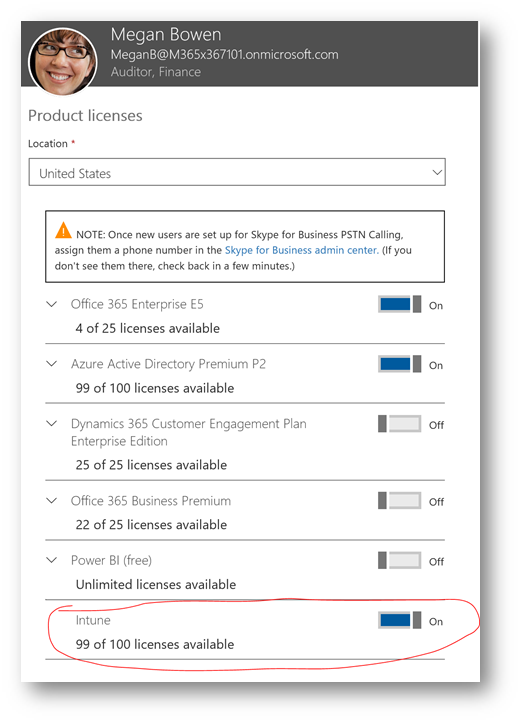
Before we get started with configuring Intune, we first need to assign the Intune license to the end-user(s) who the MAM policies will be applied to. For demonstration purposes, I will be assigning the license to a single user. However to assign licenses to multiple users (i.e. the entire organization, or groups of users) you can follow these articles for automated ways of doing so: Assign licenses to users by group membership in Azure Active Directory (or use PowerShell or other methods).
Within the Office 365 Admin Portal, I will assign the license to my test user Megan:
Configure Mobile Application Management for Microsoft Teams:
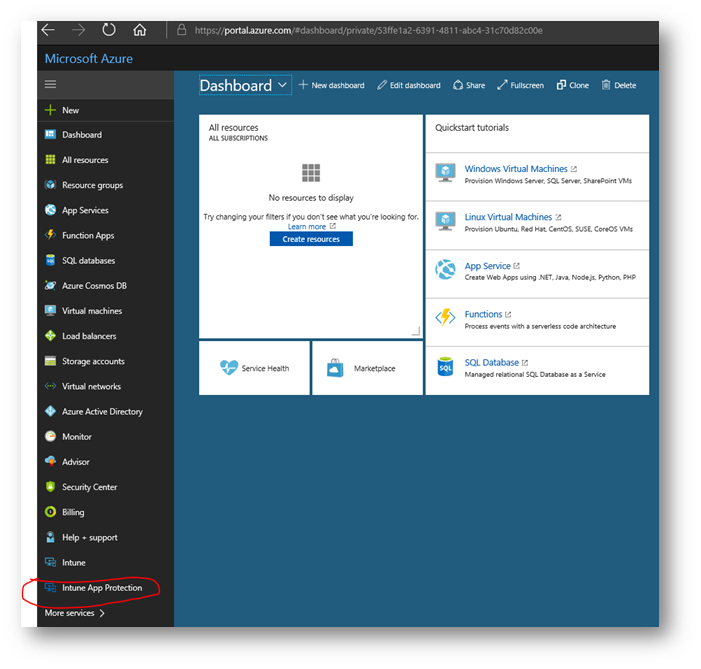
Navigate to https://portal.azure.com and login. On the left side, at the bottom click Intune App Protection:
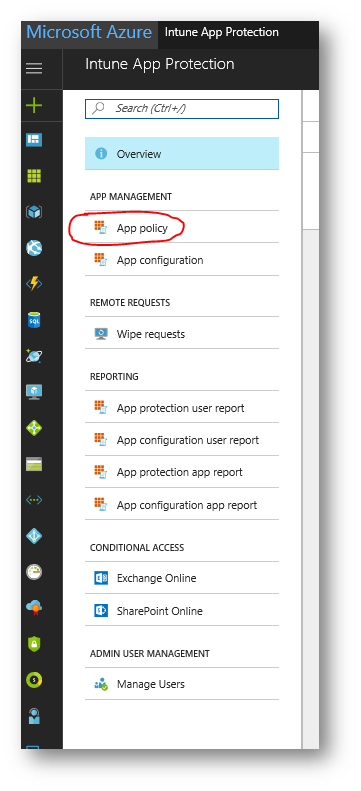
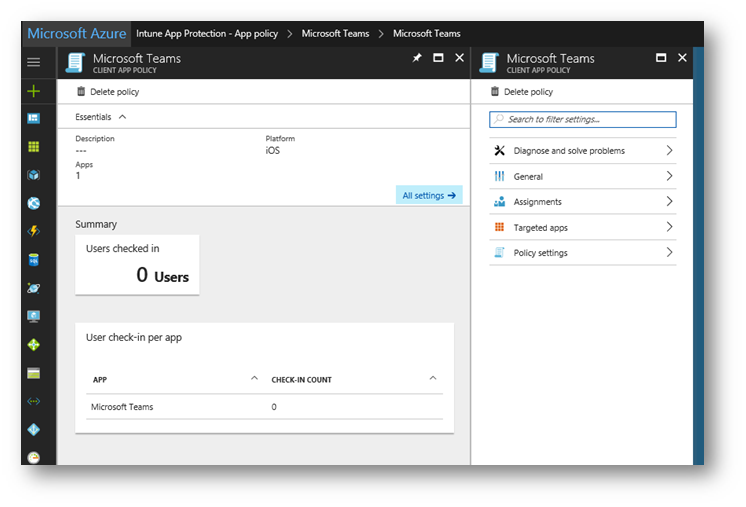
On the Intune App Protection blade, under the App Management category click App Policy:
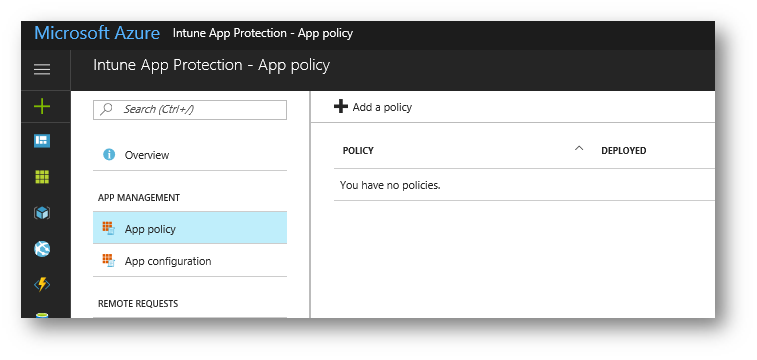
Click Add a policy:
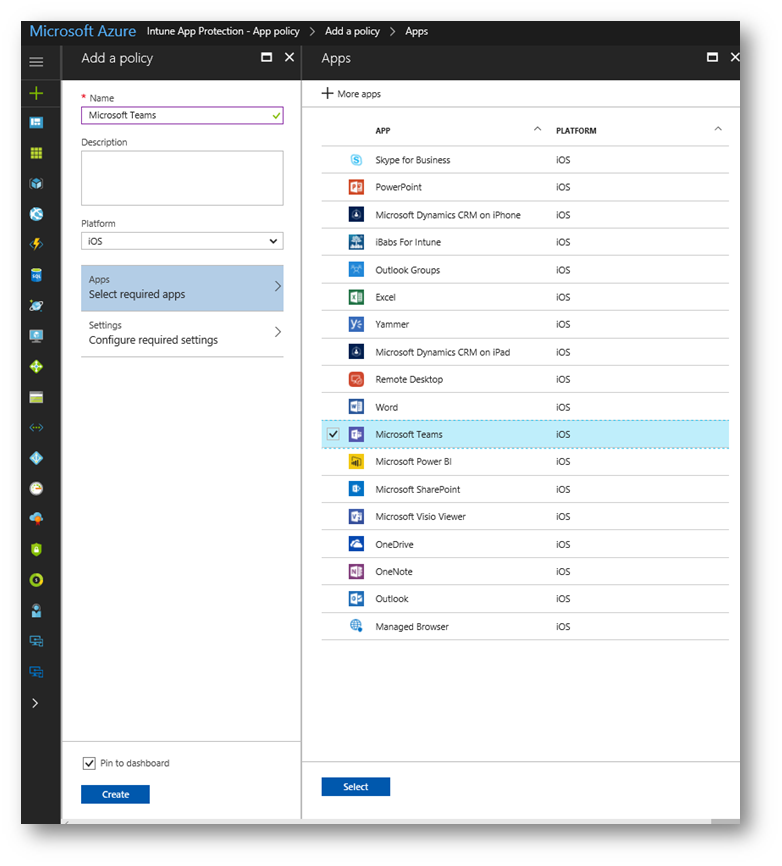
On the Add a Policy blade, I will give the policy a name and for this specific policy I will apply it to the iOS platform. I will then click Apps and place a check mark next to Microsoft Teams and then click Select:
Note: You must create a separate policy per platform if there are multiple platforms you wish to support (i.e. one for iOS and one for Android)
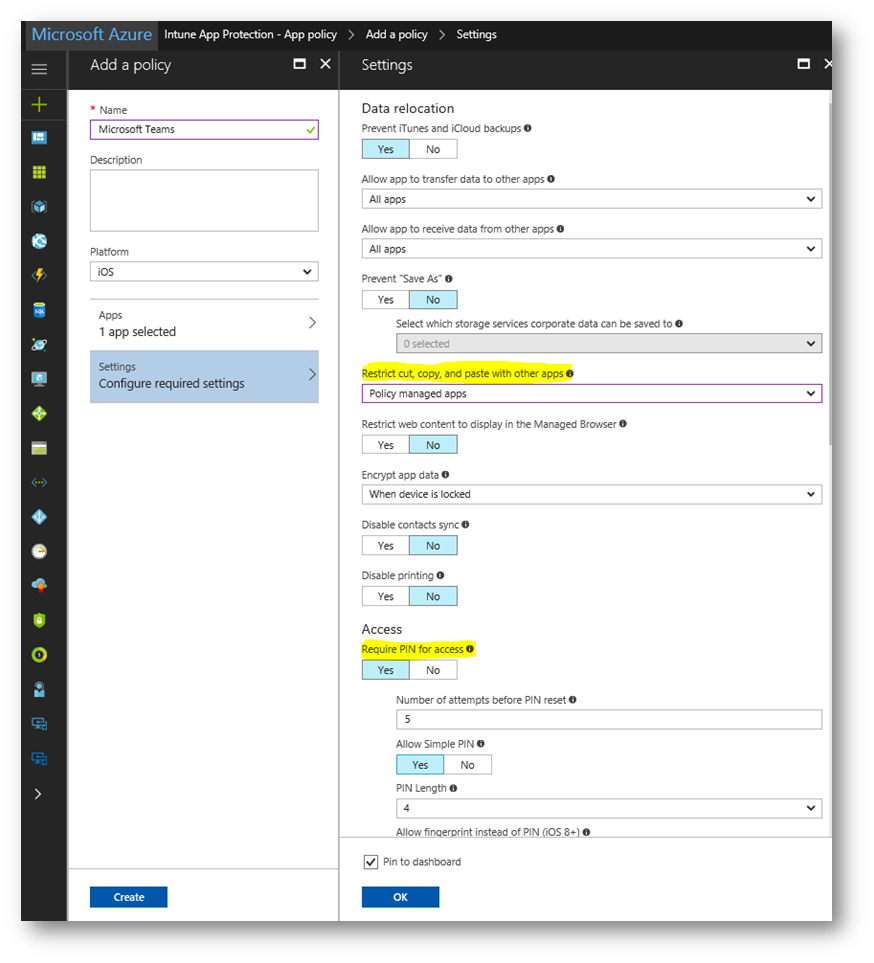
Back on the Add a policy blade, click Settings. For demonstration purposes, I will configure the following two policy settings: Restrict cut, copy, paste with other apps to Policy managed apps and Require PIN for access to Yes. When finished click OK:
Note: For a description of each one of these settings and what they do, see the following articles:
For iOS: iOS mobile app protection policy settings
For Android: Android app protection policy settings in Microsoft Intune
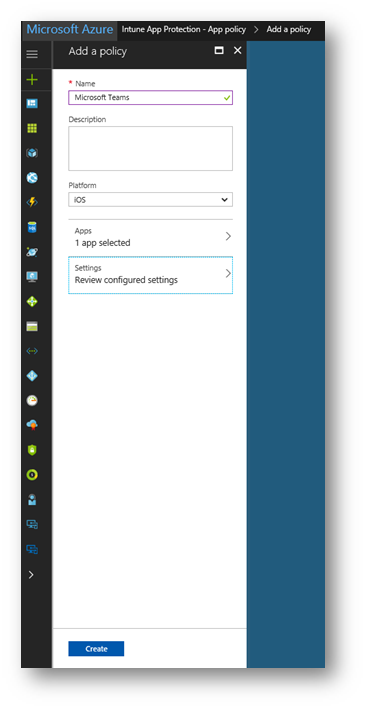
Back on the Add a policy blade, click Create:
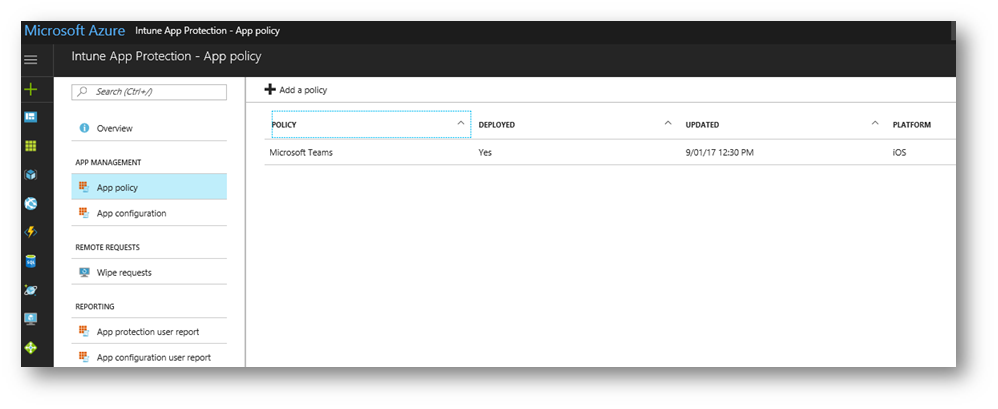
Once the policy has been created, it needs to be deployed (Notice the Deployed column shows No) Click the name of the policy:
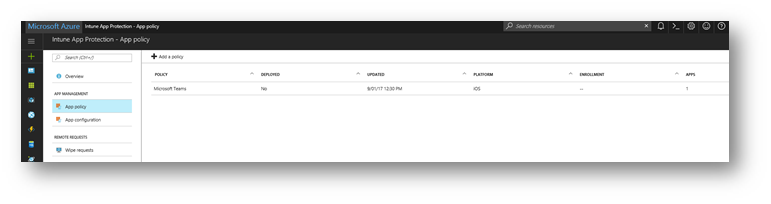
On the Microsoft Teams blade, click Assignments:
MAM policies must be assigned to a group of users. For demonstration purposes, I will use a security group titled Retail Employees. Click Select groups, and place a check mark next to Retail Employees then click Select:
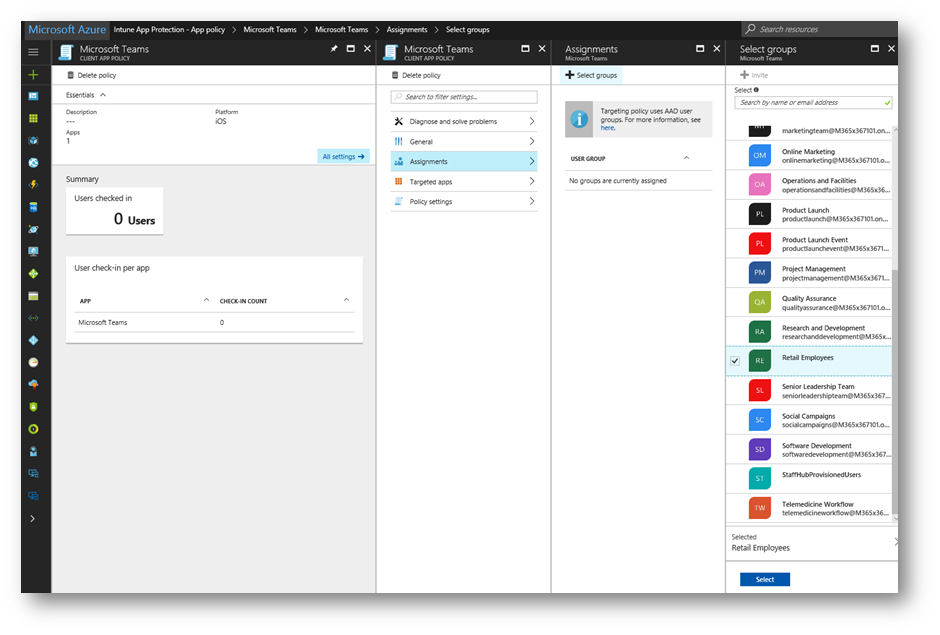
Close the Assignments blade. Close both Microsoft Teams blades and you will be returned to the list of policies . Notice the Deployed column now shows Yes.
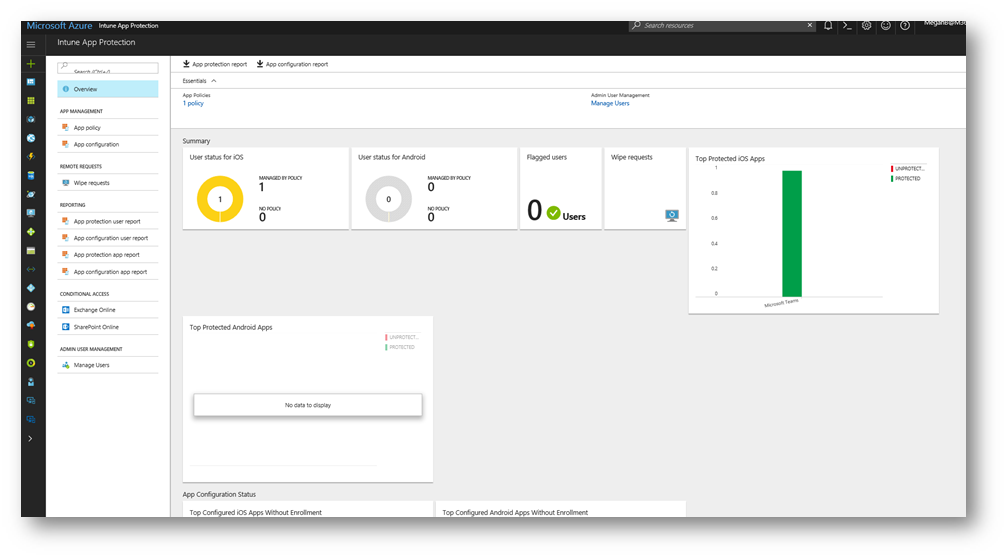
Clicking Overview on the left side will provide me with a dashboard to see MAM status across my apps:
User experience with MAM applied:
IMPORTANT: It may take up to an hour for the policy to be applied after creating it.
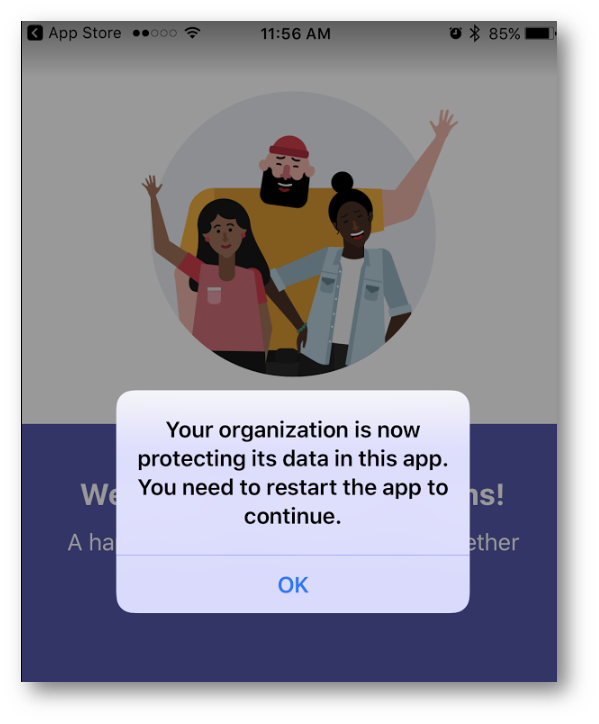
Now that the MAM policy has been created, I will launch the Microsoft Teams app on my smartphone. I will be presented with a new message indicating the MAM policy is now effective. Tap OK.
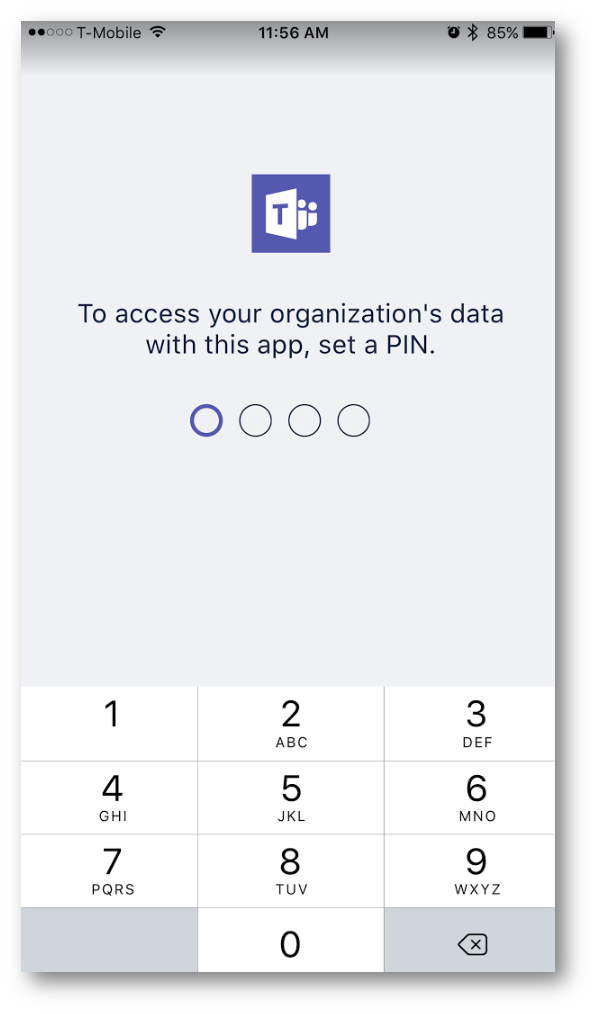
Relaunch the app. Once the app is relaunched, because I configured the MAM policy to require a PIN when using Microsoft Teams, the app will prompt me to create a PIN:
I will now have access to the app:
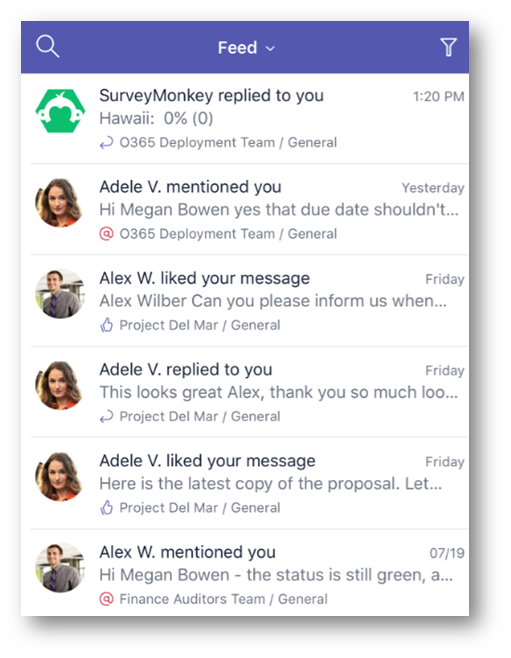
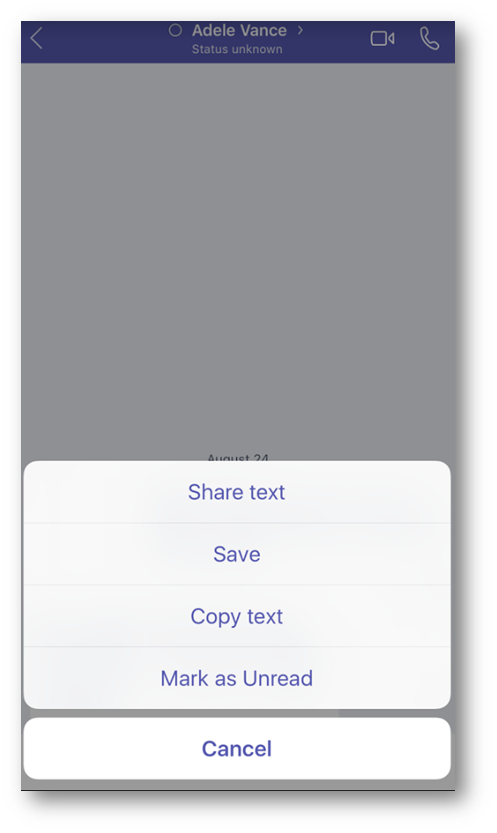
To test the policy setting for restricting cut/copy/paste, I will open an existing private chat with another user:
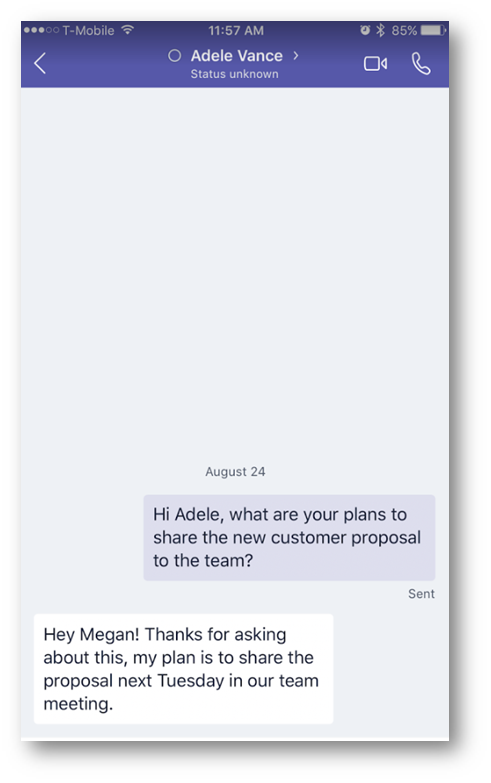
Next, I will highlight some text and with a long press tap Copy text:
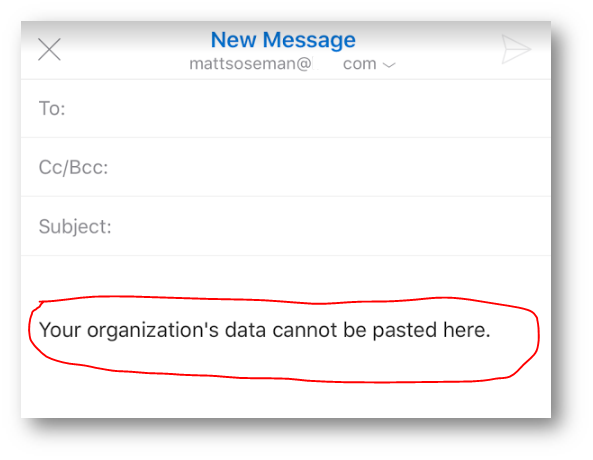
Next, I will open another app (Outlook) where my personal email account is configured and attempt to paste the confidential information from the Microsoft Teams app into a new personal email message. Notice the text that displays indicating the data cannot be pasted (the policy worked!):
How to wipe data from the Microsoft Teams app:
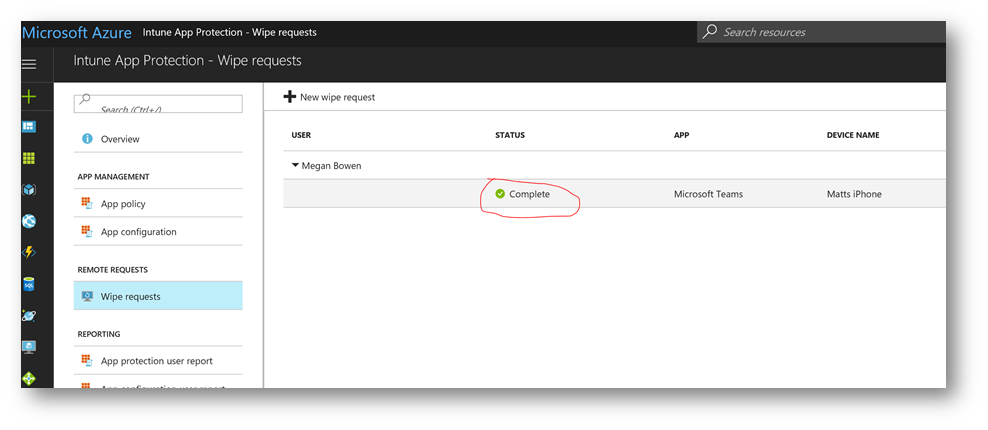
Return to the Intune App Protection blade in the Azure portal. On the left side, under Remote requests, click Wipe Requests:
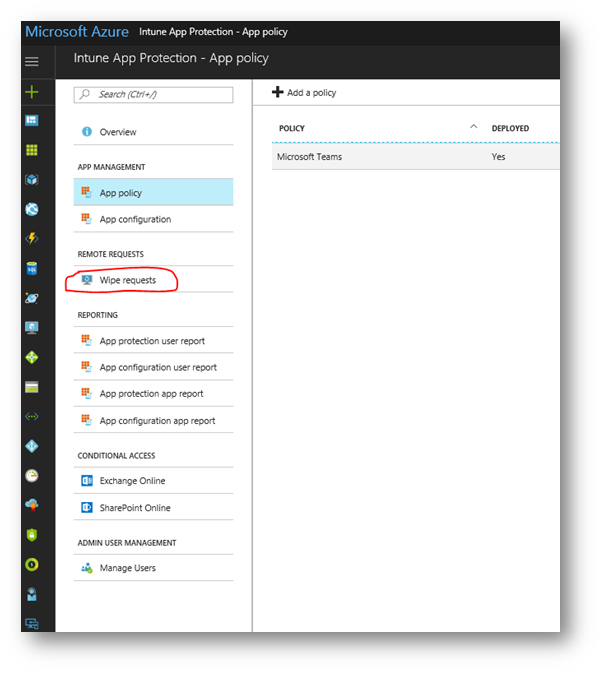
Click New Wipe Request:
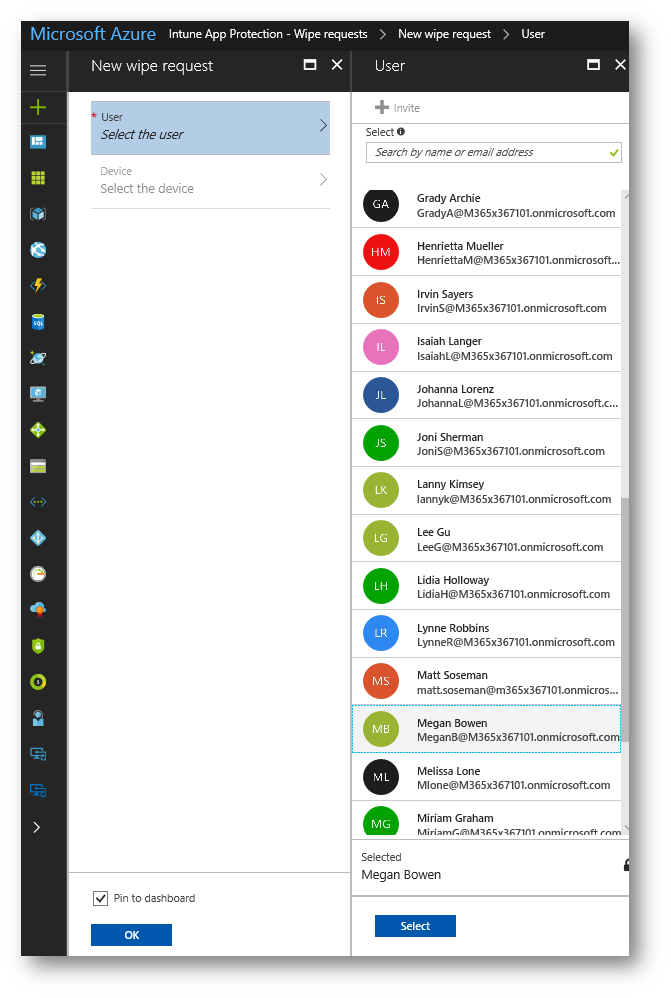
On the New wipe request blade click User. For this demonstration, I will choose Megan. Click Select after choosing the user
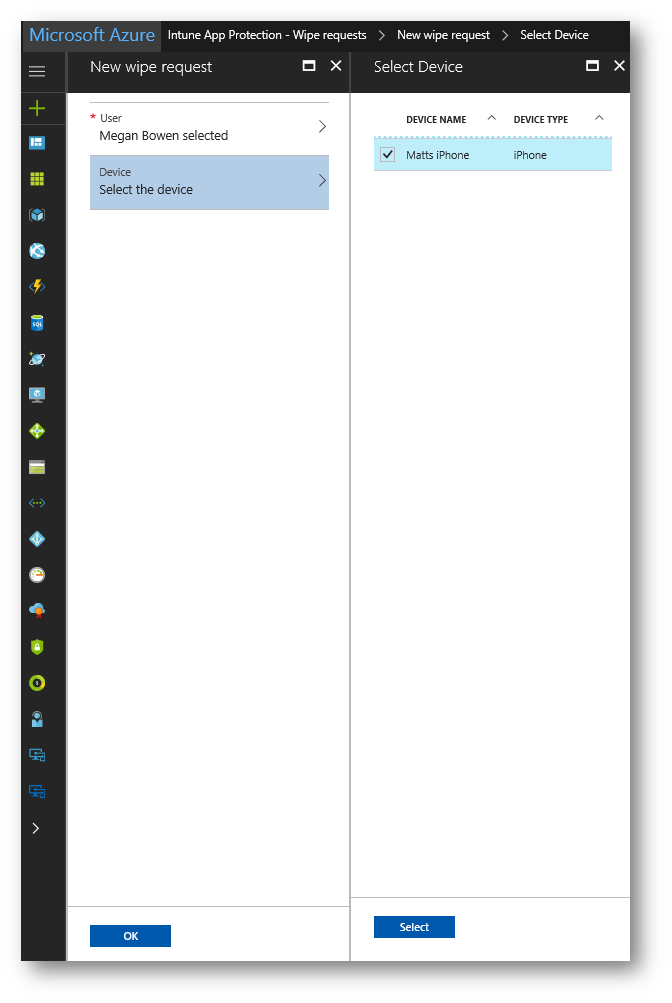
Next on the New wipe request blade click Device. Select the device by placing a check mark next to it then click Select then click OK:
Note: The name of the device is Matts iPhone as I am using my device for this demonstration.
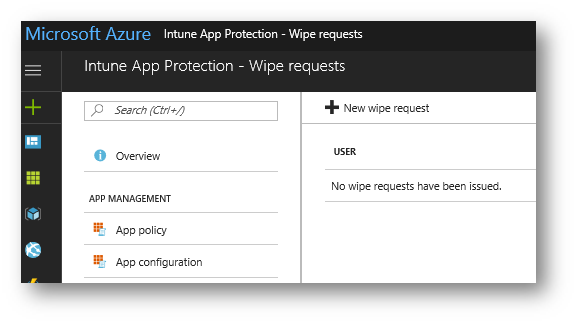
A new wipe request will be created and queued to be sent to the device:
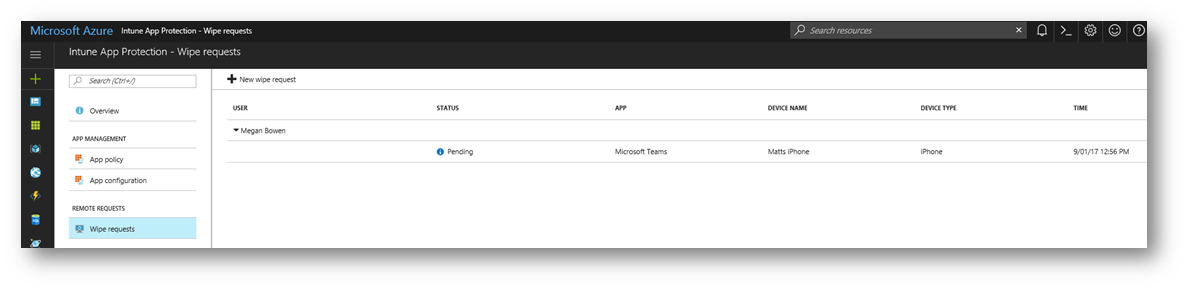
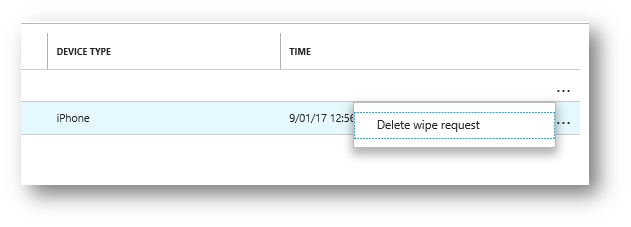
Note: the wipe request can be cancelled by clicking the ellipsis and selecting Delete wipe request:
User experience when wiping data from the Microsoft Teams app:
IMPORTANT:
The user must open the app for the wipe to occur, and the wipe may take up to 30 minutes after the request was sent.
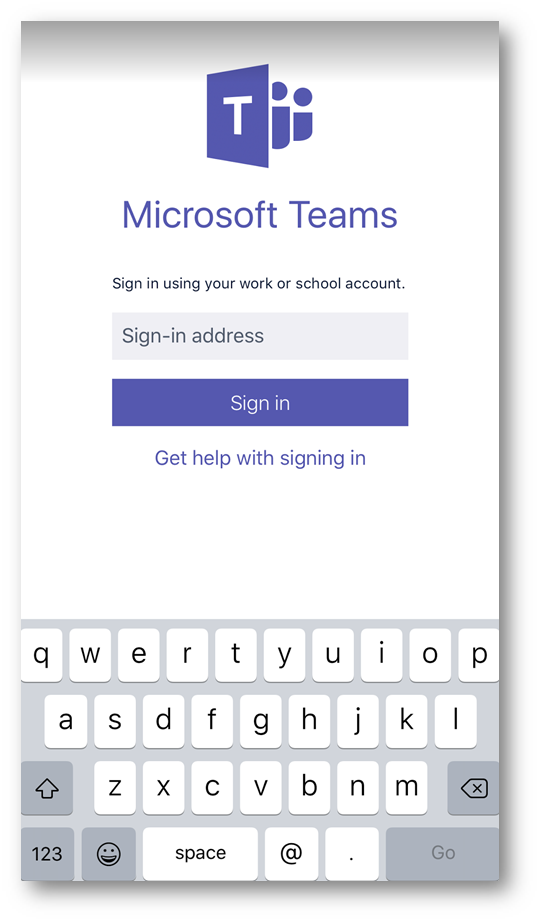
Launching the Microsoft Teams app after the wipe request has been sent, I will be prompted with a message indicating the app has been wiped. Tap OK to proceed:
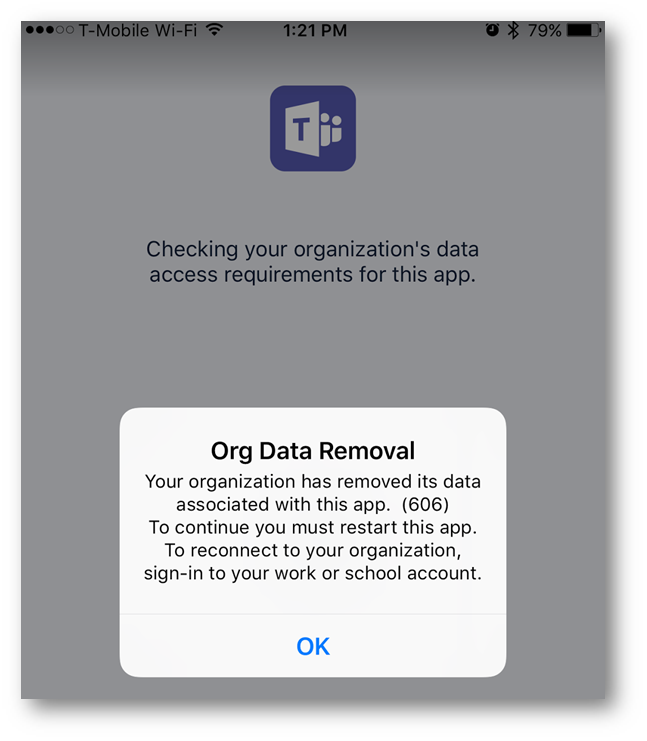
I will be returned to the home screen. After re-launching Microsoft Teams app, I will be asked to sign-in. At this point, the app has been returned to its default out of the box state:
Back in the Azure portal, notice the wipe request is now marked as Complete:
Conclusion: The Microsoft Teams app can be managed by the organization and the data within that app can be protected through MAM policy such as preventing users from copying data out of the app and pasting into a non-managed app, etc. What questions, comments, feedback or input do you have? Let me know down below in the comments.
MAM for other Microsoft mobile applications
If you are curious about MAM for other Microsoft apps such as Outlook, OneDrive, etc the process is identical to the above to configure MAM for those apps. In addition, the user experience within the app when MAM is applied, and the wipe experience, is also identical.