AD CS Step by Step Guide: Two Tier PKI Hierarchy Deployment
This step-by-step guide describes the steps needed to set up a basic configuration of Active Directory® Certificate Services (AD CS) in a lab environment. AD CS in Windows Server® 2008 R2 provides customizable services for creating and managing public key certificates used in software security systems employing public key technologies. The purpose of this step-by-step guide is to enable you to create a two-tier public key infrastructure (PKI) hierarchy using Windows Server® 2008 R2 Active Directory Certificate Services (AD CS). This guide contains instructions for installation/configuration of Windows Server 2008 R2 standalone offline root CA and enterprise issuing CA (two-tier PKI hierarchy). You will also learn to complete the configuration of LDAP as well as HTTP CRL Distribution Point (CDP) and Authority Information Access (AIA) locations. Also this guide includes instructions for installation/configuration of Online Responder (OCSP) for revocation checking.
Important - The configuration of the computers and network in this guide was designed to give you hands-on practice in creating a single-tier PKI hierarchy. The design decisions made in this guide were geared toward increasing your hands-on experience and may not reflect a best practices configuration. For best practice information, see Best Practices for Implementing a Microsoft Windows Server 2003 Public Key Infrastructure and PKI Design Brief Overview.
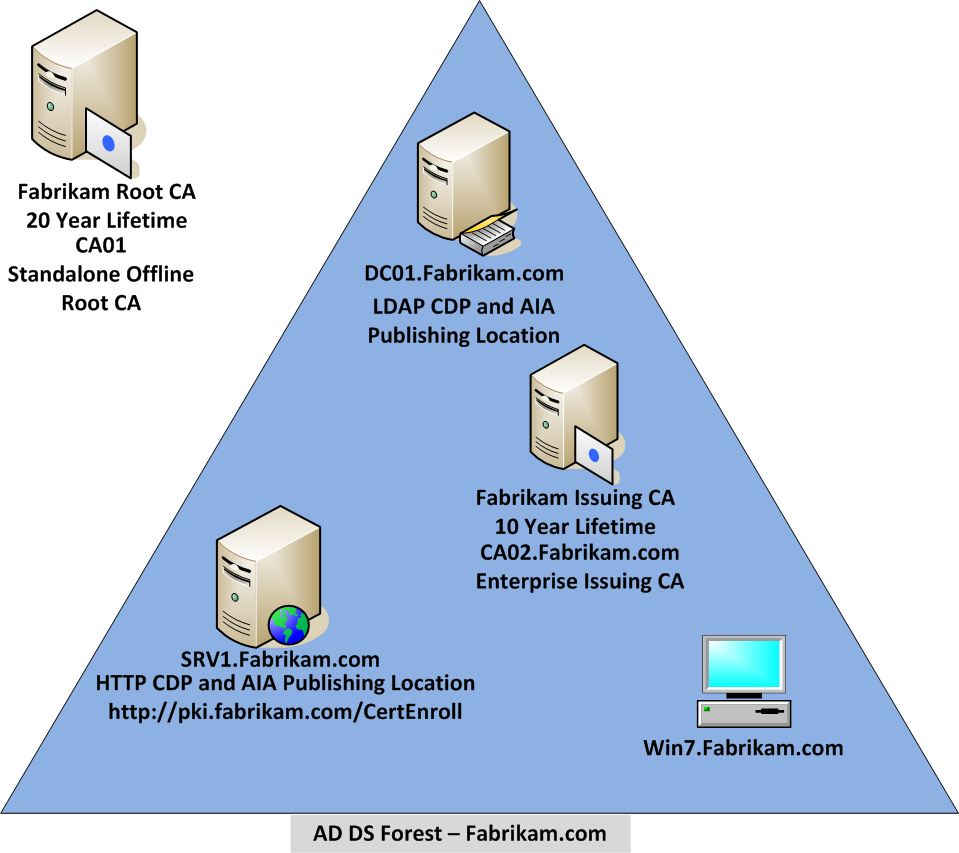
Test Lab Overview
There are five computers involved in this two-tier PKI hierarchy lab. There is one domain controller that is also running Active Directory-integrated Domain Name Service (DNS). This computer will also provide the Lightweight Directory Access Protocol (LDAP) location for the CDP and the AIA point for the PKI configuration. One Standalone Offline Root CA, One Enterprise Issuing CA, and One Web Server (HTTP CDP/AIA) and one Windows 7 Client computer.
| Virtual Machine | Role(s) | OS Type | IP Address | Subnet Mask | Preferred DNS Server |
| DC01.Fabrikam.com | DC & DNS - LDAP CDP/AIA | Windows Server 2008 R2 | 192.168.1.10 | 255.255.255.0 | 192.168.1.10 |
| CA01 | Standalone Offline Root CA | Windows Server 2008 R2 | Not Applicable | Not Applicable | Not Applicable |
| CA02.Fabrikam.com | Enterprise Issuing CA | Windows Server 2008 R2 | 192.168.1.12 | 255.255.255.0 | 192.168.1.10 |
| SRV1.Fabrikam.com | Web Server - HTTP CDP/AIA | Windows Server 2008 R2 Enterprise | 192.168.1.13 | 255.255.255.0 | 192.168.1.10 |
| WIN7.Fabrikam.com | Windows Client Computer | Windows 7 | 192.168.1.14 | 255.255.255.0 | 192.168.1.10 |
Computer Requirements
Make sure that following requirements are met for the computers or virtual machines to be installed for this lab:
- The Windows Server 2008 R2 Enterprise Edition operating system for SRV1 because it will run OCSP. For more information about Windows Server Editions and capabilities, see Active Directory Certificate Services Overview.
- Windows Server 2008 R2 Standard, Enterprise, or Datacenter edition operating system for the rest of the servers.
- Since the computer CA01 will not be connected to a network, you must use have the ability to use removable media (floppy disk or USB drive). One removable media with enough free space to hold a few certificates and certificate revocation lists (about 10 kilobytes). This can be either physical or virtual removable media depending on whether your lab is using physical or virtual computers. For instructions on transferring files using a virtual floppy disk using Microsoft Windows Server™ Hyper-V, see Creating, Using, and Transferring Files using Virtual Floppy Disks.
- Windows 7 Professional, Ultimate, or Enterprise edition because it must be able to join the domain.
- All current service packs and updates applied
- Initial membership: Workgroup
- Network configuration: You may have a custom network configuration for your environment. If so, you can configure that instead and make the appropriate substitutions as needed. In this lab the assumption will be made that you are using the IP address scheme shown in the table.
Major Steps
There are eight major steps in this step-by-step guide as listed below (each includes several sub tasks).
- Install the Active Directory Forest
- Prepare the web server for CDP and AIA publication
- Install the standalone offline root CA
- Perform post installation configuration steps on the standalone offline root CA
- Install Subordinate Issuing CA
- Perform the post installation configuration on the subordinate issuing CA
- Install and configure the online responder
- Verify the PKI hierarchy health
Install the Active Directory Forest
In this Step-by-Step guide, an Active Directory Domain Services (AD DS) forest named Fabrikam.com is used. DC01 functions as the domain controller. The Forest Functional Level is set to Windows Server 2008 R2.
Configure Server Name and Network Settings
To ensure the server is named DC01 and the network settings are configured properly for this lab:
- Log on to DC01 as the local administrator.
- Click Start, type ncpa.cpl and press ENTER.
- In Network Connections, right-click the Local Area Connection and then click Properties.
- If there are more than one Local Area Connection icons in the Network Connections, you want to modify the one that is connected to network segment shared by all the computers that you have installed for this lab.
- Click the Internet Protocol Version 4 (TCP/IPv4) and then click Properties.
- Select the Use the Following IP address. Configure the IP address, Subnet mask, and Default gateway appropriately for your test network.
- IP Address: 192.168.1.10
- Subnet mask: 255.255.255.0
- Default gateway: <optional>
- Select the Use the following DNS server address. Configure the Preferred DNS server for the IP address of your domain controller. Click OK. Click Close.
- Preferred DNS Server: 192.168.1.10
- Click Start, type sysdm.cpl and press ENTER. Click Change.
- In Computer name, type DC01 and then click OK.
- When prompted that you need to restart the computer, click OK. Click Close. Click Restart Now.
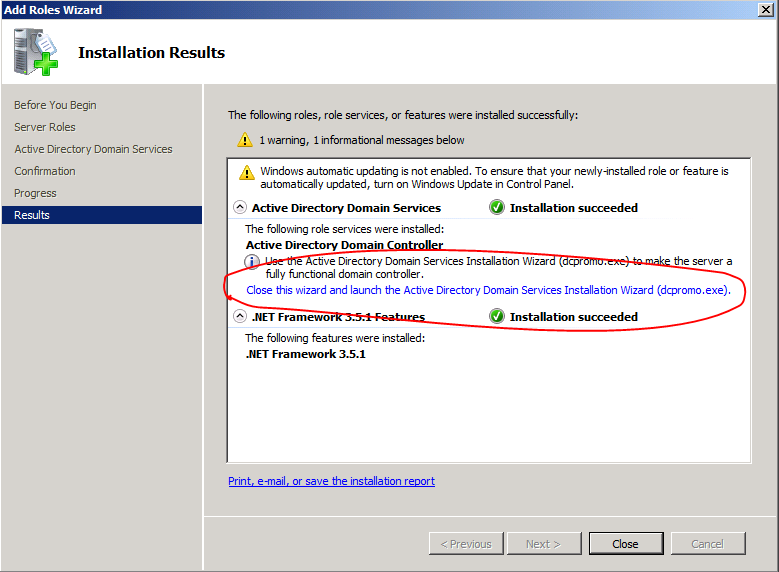
Install a new forest by using Server Manager
To install the Fabrikam.com forest:
- Log onto DC01 as DC01\Administrator.
- Open Server Manager. To do so, you can click the Server Manager icon in the toolbar or click Start, click Administrative Tools, and then click Server Manager.
- In the console tree, right-click Roles and then click Add Roles.
- On the Before You Begin page, click Next.
- On the Select Server Roles page, select Active Directory Domain Services. Click Next.
- If prompted by the Add Roles Wizard, click Add Required Features and then click Next.
- On the Active Directory Domain Services page, click Next.
- On the Confirm Installation Selections page, click Install.
- On the Installation Results page, click the Close this wizard and launch the Active Directory Domain Services Installation Wizard (dcpromo.exe) link (in blue).
- On the Welcome to the Active Directory Domain Services Installation Wizard page, click Next.
- The Use advanced mode installation check box could be used to get additional installation options. However, you will not do so in this lab.
- On the Operating System Compatibility page, click Next.
- On the Choose a Deployment Configuration page, select Create a new domain in a new forest, and then click Next.
- On the Name the Forest Root Domain page, in FQDN of the forest root domain, type fabrikam.com, and then click Next.
- On the Set Forest Functional Level page, in the Forest functional level drop down menu, select Windows Server 2008 R2 and then click Next.
- On the Additional Domain Controller Options page, click Next.
- DNS server is selected by default so that your forest DNS infrastructure can be created during AD DS installation. In our scenario we are going to use Active Directory–integrated DNS so we have selected to install DNS.
- If you do not have static IP address assigned to your network adapter, a warning message appears advising you to set static addresses.
- The wizard displays a message indicating that it cannot create a delegation for the DNS server, this is normal when creating a new forest and root domain. Click Yes to continue.
- On the Location for Database, Log Files, and SYSVOL page, click Next.
- On the Directory Services Restore Mode Administrator Password page, type and confirm the restore mode password, and then click Next. This password must be used to start AD DS in Directory Service Restore Mode for tasks that must be performed offline.
- On the Summary page, review your selections and click Next to install Active Directory Domain Services.
- Select the Reboot on completion check box to have the server restart automatically after Active Directory installation is completed.
- If you are using Active Directory-integrated DNS, the IP address for the Preferred DNS server for the first domain controller in the forest is automatically set to the loopback address of 127.0.0.1. This helps assure that the IP address of the first domain controller will be resolved in DNS even if the static IP address of the server is changed. If you prefer to configure actual IP address of the DNS sever rather than loopback address, then replace it with 192.168.1.10 after the restart.
Install the Group Policy Management Console
In some installations of Windows Server 2008 R2, the Group Policy Management console is added automatically. In other installations, it is not. If your installation does not automatically include the Group Policy Management tools upon AD DS installation, then you can add them using the following procedure:
- Log onto DC01.Fabrikam.com as Fabrikam\Administrator.
- Open Server Manager.
- In the console tree, click Features. In the Features pane, click Add Features.
- In the Add Feature Wizard dialog box, select Group Policy Management from the list of available features.
- Click Install.
- Close Server Manager when the installation completes.
Prepare HTTP Web Server for CDP and AIA Publication
Join SRV1 to the domain
- Log on to SRV1 as the local administrator.
- Click Start, type ncpa.cpl and press ENTER.
- In Network Connections, right-click the Local Area Connection and then click Properties.
- If there are more than one Local Area Connection icons in the Network Connections, you want to modify the one that is connected to network segment shared by all the computers that you have installed for this lab.
- Click the Internet Protocol Version 4 (TCP/IPv4) and then click Properties.
- Select the Use the Following IP address. Configure the IP address, Subnet mask, and Default gateway appropriately for your test network.
- IP Address: 192.168.1.13
- Subnet mask: 255.255.255.0
- Default gateway: <optional>
- Select the Use the following DNS server address. Configure the Preferred DNS server for the IP address of your domain controller. Click OK. Click Close.
- Preferred DNS Server: 192.168.1.10
- Click Start, type sysdm.cpl and press ENTER. Click Change.
- In Computer name, type SRV1 and then click OK.
- When prompted that you need to restart the computer, click OK. Click Close. Click Restart Now.
- After SRV1 restarts, log on as a local administrator.
- Click Start, type sysdm.cpl and press ENTER. Click Change.
- In Member of, select Domain, and then type fabrikam.com. Click OK.
- In Windows Security, enter the User name and password for the domain administrator account. Click OK.
- You should be welcomed to the Fabrikam domain. Click OK.
- When prompted that a restart is required, click OK. Click Close. Click Restart Now.
Install Web Server (IIS) Role
- Log on to SRV1.Fabrikam.com as Fabrikam\Administrator. (Ensure that you switch user to log on as Fabrikam\Administrator)
- Open Server Manager.
- Right-click on Roles and then select Add Roles.
- On the Before You Begin page select Next.
- On the Select Server Roles page select Web Server (IIS) and then click Next.
- On Web Server (IIS) page, click Next.
- Leave the defaults on Select Role Services page and then click Next.
- On Confirm Installation Selections page, click Next.
- On the Installation Results page, click Close.
Create CertEnroll Folder and grant Share & NTFS Permissions to Cert Publishers group
- Log onto SRV1.Fabrikam.com as Fabrikam\Administrator.
- Click Start and select Computer to open Windows Explorer and then go to C: drive.
- Create folder called CertEnroll at the root of C: drive.
- Right-click on CertEnroll folder and select Properties.
- On CertEnroll Properties page select Sharing tab to configure share permissions.
- Click on Advanced Sharing option and then select Share this folder.
- Click on Permissions and then click Add.
- On Select Users or Groups page, in the Enter the object names to select, type Fabrikam\Cert Publishers and then click OK.
- On Permissions for CertEnroll dialog box, select Cert Publishers group and then in the Allow column select Change permission. Click OK twice to go back to CertEnroll Properties page.
- Select Security tab and click Edit to configure NTFS permissions.
- On Permissions for CertEnroll page click Add.
- On Select Users or Groups page, under the Enter the object names to select, enter Fabrikam\Cert Publishers and then click OK.
- On Permissions for CertEnroll page highlight Cert Publishers group and then under the Allow column select Modify permission. Click OK.
- On CertEnroll Properties page, click OK.
Create CertEnroll Virtual Directory in IIS
- Ensure you are logged on to SRV1.Fabrikam.com as Fabrikam\Administrator.
- Click Start, Administrative Tools and then select Internet Information Services (IIS) Manager.
- On the Connections, expand SRV1 and then expand Sites.
- Right-click on Default Web Site and select Add Virtual Directory.
- On Add Virtual Directory page, in Alias, type CertEnroll. In Physical path, type C:\Certenroll, and then click OK.
- In the Connections pane, under the Default Web Site, ensure the CertEnroll virtual directory is selected.
- In the CertEnroll Home pane, double-click on Directory Browsing.
- In Actions pane click Enable.
Enable Double Escaping on IIS Server
Allowing double escaping makes it possible for the web server to host Delta CRLs. For more information, see KB Article 942076- Error message when you visit a Web site that is hosted on IIS 7.0: "HTTP Error 404.11 – URL_DOUBLE_ESCAPED" 
Ensure you are logged on to SRV1.Fabrikam.com as Fabrikam\Administrator.
Open a Command Prompt. To do so, click Start, click Run, and then type cmd. Click OK.
Then type cd %windir%\system32\inetsrv\ and press ENTER.
Type following command and press Enter.
Appcmd set config "Default Web Site" /section:system.webServer/Security/requestFiltering -allowDoubleEscaping:True
Restart IIS service. To do so, type iisreset and press ENTER.
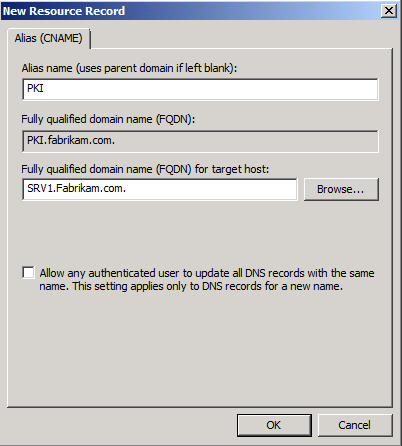
Create CNAME (pki.fabrikam.com) in DNS
- Ensure that you are logged on to DC01.Fabrikam.com as Fabrikam\Administrator.
- Open the DNS Console. You can do so by clicking Start, click Run, and then type dnsmgmt.msc. Click OK.
- Expand Forward Lookup Zones, select and then right-click Fabrikam.com zone. Click New Alias (CNAME).
- In Alias name (uses parent domain if left blank), type PKI. In the Fully qualified domain name (FQDN) for target host field, type SRV1.Fabrikam.com. and then click OK.
Note - Include the terminating “.” in the FQDN in the previous step. In a production environment this alias can resolve to a load balancer which distributes requests to any number of web servers that contain the CA certificates and CRLs.
Install the Standalone Offline Root CA
The standalone offline root CA should not be installed in the domain. As a matter of fact, it should not even be connected to a network at all.
Create a CAPolicy.inf for the standalone offline root CA
To create a CAPolicy.inf for the standalone offline root CA:
Log onto CA01 as CA01\Administrator.
Click Start, click Run and then type notepad C:\Windows\CAPolicy.inf and press ENTER.
When prompted to create new file, click Yes.
Type in following as contents of the file.
[Version]
Signature="$Windows NT$"
[Certsrv_Server]
RenewalKeyLength=2048 ; recommended 4096
RenewalValidityPeriod=Years
RenewalValidityPeriodUnits=20
AlternateSignatureAlgorithm=0
Notes:
- AlternateSignatureAlgorithm=1 is not compatible with Windows XP and Windows Server 2003 certificate client computers. In addition most 3rd party applications do not recognize alternate signature format.
- Windows Server 2008 R2 CAPolicy.inf Syntax - The CAPolicy.inf contains various settings that are used when installing the Active Directory Certification Service (AD CS) or when renewing the CA certificate. The CAPolicy.inf file is not required to install ADCS with the default settings, but in many cases the default settings are insufficient. The CAPolicy.inf can be used to configure CAs in these more complicated deployments.
- Any entries in CAPolicy.inf file that are misspelled will be ignored.
5. Click File and Save to save the CAPolicy.inf file under C:\Windows directory.
Warning: Be sure to save the CAPolicy.inf with the .inf extension. If you do not specifically type .inf at the end of the file name and select the options as described, the file will be saved as a text file and will not be used during CA installation.
6. Close Notepad.
Installing the Standalone Offline Root CA
To install the standalone offline root CA:
- Log onto CA01 as CA01\Administrator.
- Click Start, click Administrative Tools, and then click Server Manager.
- Right-click on Roles and then click Add Roles.
- On the Before You Begin page click Next.
- On the Select Server Roles page select Active Directory Certificate Services, and then click Next.
- On the Introduction to Active Directory Certificate Services page, click Next.
- On the Select Role Services page, ensure that Certification Authority is selected, and then Next.
- On the Specify Setup Type page, ensure that Standalone is selected, and then click Next.
- Note: Enterprise option is grayed out as CA01 server is not joined to Active Directory domain.
- On the Specify CA Type page, ensure that Root CA is selected, and then click Next.
- On the Set Up Private Key page, ensure that Create a new private key is selected, and then click Next.
- Leave the defaults on the Configure Cryptography for CA page, and then click Next.
- Important: In a production environment, you would set the CSP, Hash Algorithm, and Key length to meet application compatibility requirements.
- On Configure CA Name page, under Common name for this CA, clear the existing entry and type Fabrikam Root CA. Click Next.
- Note: A Distinguished Name Suffix is optional for a root CA. This will be configured in a later step.
- On Set Validity Period page, under Select validity period for the certificate generated for this CA, clear the existing entry and then type 20. Leave the selection box set to Years. Click Next.
- Keep the default settings on the Configure Certificate Database page, and then click Next.
- On the Confirm Installation Selections page, review the settings, and then click Install.
- Review the information on the Installation Results page to verify that the installation is successful and then click Close.
Perform Post Installation Configuration for Root CA
- Ensure that you are logged on to CA01 as CA01\Administrator.
- Open a command prompt. To do so, you can click Start, click Run, type cmd and then click OK.
- To define Active Directory Configuration Partition Distinguished Name, run the following command from an administrative command prompt:
- Certutil -setreg CA\DSConfigDN "CN=Configuration,DC=Fabrikam,DC=com"
- To define CRL Period Units and CRL Period, run the following commands from an administrative command prompt:
- Certutil -setreg CA\CRLPeriodUnits 52
- Certutil -setreg CA\CRLPeriod "Weeks"
- Certutil -setreg CA\CRLDeltaPeriodUnits 0
- To define CRL Overlap Period Units and CRL Overlap Period, run the following commands from an administrative command prompt:
- Certutil -setreg CA\CRLOverlapPeriodUnits 12
- Certutil -setreg CA\CRLOverlapPeriod "Hours"
- To define Validity Period Units for all issued certificates by this CA, type following command and then press Enter. In this lab, the Enterprise Issuing CA should receive a 10 year lifetime for its CA certificate. To configure this, run the following commands from an administrative command prompt:
- Certutil -setreg CA\ValidityPeriodUnits 10
- Certutil -setreg CA\ValidityPeriod "Years"
Additional information
- CRLPeriodUnits - You can use this setting to specify the number of days, weeks, months, or years, that a CRL will be valid.
- CRLPeriod - You can use this setting to specify whether the validity period of a CRL will be defined in days, weeks, months, or years.
- CRLOverlapPeriodUnits - You use this setting to specify the number of days, weeks, months, or years that CRLs can overlap. When a large number of certificates are revoked, such as during an employee layoff, the delta CRL size might increase significantly because of the large number of entries, and almost all clients will refer to the older base CRL. You can reduce the size of the overlap period to speed the propagation process for the new base CRL and help minimize the size of delta CRLs.
- CRLOverlapPeriod - This setting specifies whether the overlap period for CRLs will be defined in days, weeks, months, or years.
- The overlap period for CRLs is the amount of time at the end of a published CRLs lifetime that a client can use to obtain a new CRL before the old CRL is considered unusable. The default setting for this value is 10% of the CRL lifetime. Because some environments may require longer periods to replicate a CRL, this setting can be configured manually.
- ValidityPeriodUnits - You can use this setting to define the number of days, weeks, months, or years that a certificate issued by the CA will be valid. The validity period for a certificate cannot be greater than the validity period of the CA that issued the certificate. The default value depends on the type of certificate.
- ValidityPeriod - You can use this setting to specify whether the validity period of certificates issued by the CA will be defined in days, weeks, months, or years. The default value depends on the type of certificate.
Enable Auditing on the Root CA
CA auditing depends on system Audit Object Access to be enabled. The following instructions describe how to use Local Security Policy to enable object access auditing.
Click Start, click Administrative Tools, and then select Local Security Policy.
Expand Local Policies and then select Audit Policy.
Double click Audit Object Access and then select Success and Failure then click OK.
Close Local Security Policy editor.
Enable auditing for the CA by selecting which group of events to audit in the Certificate Authority MMC snap-in or by configuring AuditFilter registry key setting. To configure Auditing for all CA related events, run the following command from an administrative command prompt:
Certutil -setreg CA\AuditFilter 127
Additional Information
- CA\AudtiFilter 127 enables all forms of auditing. You can enable use this setting to enable specific or all auditing events for CA.
- You cannot use a domain Group Policy for this case because the offline root CA is not joined to the domain.
- TechNet articles
Configure the AIA and CDP
There are multiple different methods for configuring the Authority Information Access (AIA) and certificate revocation list distribution point (CDP) locations. You can use the user interface (in the Properties of the CA object), certutil, or directly edit the registry. The AIA is used to point to the public key for the certification authority (CA). The CDP is where the certificate revocation list is maintained, which allows client computers to determine if a certificate has been revoked. In this lab there will be three locations for the AIA and four locations for the CDP.
Configure the AIA
Using a certutil command is a quick and common method for configuring the AIA. When you run the following certutil command, you will be configuring a static file system location, a lightweight directory access path (LDAP) location, and http location for the AIA. The certutil command to set the AIA modifies the registry, so ensure that you run the command from an command prompt run as Administrator. Run the following command:
certutil -setreg CA\CACertPublicationURLs "1:C:\Windows\system32\CertSrv\CertEnroll\1_%3%4.crt\n2:ldap:///CN=%7,CN=AIA,CN=Public Key Services,CN=Services,%6%11\n2:http://pki.fabrikam.com/CertEnroll/%1_%3%4.crt"****
After you have run that command, run the following command to confirm your settings:
certutil -getreg CA\CACertPublicationURLs
If you look in the registry, under the following path: HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\CertSvc\Configuration\Fabrikam Root CA, you can confirm the CACertPublicationURLs by opening that REG_MULTI_SZ value. You should see the following:
1:C:\Windows\system32\CertSrv\CertEnroll\1_%3%4.crt
2:ldap:///CN=%7,CN=AIA,CN=Public Key Services,CN=Services,%6%11
2:http://pki.fabrikam.com/CertEnroll/%1_%3%4.crt
You can also see this in the the CA (certsrv) console. To open the console, click Start, click Administrative Tools, and then click Certification Authority. In the navigation pane, expand the Certificate Authority (Local). Right-click Fabrikam Root CA and then click Properties. On the Extensions tab, under Select extension, click Authority Information Access (AIA) and you will see the graphical representation of the AIA settings.
Additional Information
- CACertPublicationURLs - This setting identifies the URL of the authority information access (AIA) point where a client can find a CA certificate. Because the authority information access point is the location of the certificate that was used to sign the certificate.
- Each number value listed above preceding each URL means specific configuration setting. You can find more information about these values at AIA Publishing Properties.
- These settings can be configured from the Extensions tab in the Certificate Authority manager as well.
- The HTTP path to pki.fabrikam.com is being used as an alias (CNAME configured earlier), which provides flexibility for load balancing scenarios.
Configure the CDP
Clients will use the CDP to locate the CRL for the certificates issued by the CA. This allows certificate clients to ensure that the certificates have not been revoked. You can also configure the CDP with the user interface, certutil, and registry. Using a certutil command is a quick and common method for configuring the CDP. When you run the following certutil command, you will be configuring a static file system location, an LDAP location, an http location, and a file system location.
Note: The file system location that you will be setting will allow the CRL to be copied over the network to the web server (SRV1), which is why we earlier allowed the Cert Publishers group access to the share and folder. All CAs are members of the Cert Publishers group, so we effectively allowed all CAs to copy to the CertEnroll folder on SRV1. Some administrators decide to configure a separate group of specific computers for that purpose or even grant permissions to the CAs individually.
The certutil command to set the CDP modifies the registry, so ensure that you run the command from an command prompt run as Administrator. Run the following command:
certutil -setreg CA\CRLPublicationURLs "1:C:\Windows\system32\CertSrv\CertEnroll\3%8%9.crl\n10:ldap:///CN=%7%8,CN=%2,CN=CDP,CN=Public Key Services,CN=Services,%6%10\n2:http://pki.fabrikam.com/CertEnroll/%3%8%9.crl"
After you run that command, run the following certutil command to verify your settings:
certutil -getreg CA\CRLPublicationURLs
In the registry location: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration\Fabrikam Root CA you can open the REG_MULTI_SZ valueand see the configuration of these values:
1:C:\Windows\system32\CertSrv\CertEnroll\3%8%9.crl
10:ldap:///CN=%7%8,CN=%2,CN=CDP,CN=Public Key Services,CN=Services,%6%10
2:http://pki.fabrikam.com/CertEnroll/%3%8%9.crl
Additional Information
- CRLPublicationURLs - This setting identifies CRL distribution points where a client can find the CRL that is related to a certificate. The CRL distribution point of a root CA should be empty. For intermediate and issuing CAs, you use t he Certification Authority snap-in to define CRL distribution points. These values are then stored in the registry.
- Each number value listed above preceding each URL means specific configuration setting. You can find more information about these values at CRL Publishing Properties.
- TechNet Article - CRL Distribution Point Replacement Token

You can also see this in the the CA (certsrv) console. To open the console, click Start, click Administrative Tools, and then click Certification Authority. In the navigation pane, ensure that Certificate Authority (Local) is expanded. Right-click Fabrikam Root CA and then click Properties. On the Extensions tab, under Select extension, click CRL Distribution Point (CDP) and you will see the graphical representation of the CDP settings.
At an administrative command prompt, run the following commands to restart Active Directory Certificate Services and to publish the CRL.
Restart-Service certsvc
certutil -crl
Install Enterprise Issuing CA
Enterprise CAs must be joined to the domain. Before you install the Enterprise Issuing CA (CA02), you must first join the server to the domain. Then you can install the Certification Authority role service on the server.
Join CA02 to the domain
To join CA02 to the domain:
- Log on to CA02 as the local administrator.
- Click Start, type ncpa.cpl and press ENTER.
- In Network Connections, right-click the Local Area Connection and then click Properties.
- If there are more than one Local Area Connection icons in the Network Connections, you want to modify the one that is connected to network segment shared by all the computers that you have installed for this lab.
- Click the Internet Protocol Version 4 (TCP/IPv4) and then click Properties.
- Select the Use the Following IP address. Configure the IP address, Subnet mask, and Default gateway appropriately for your test network.
- IP Address: 192.168.1.12
- Subnet mask: 255.255.255.0
- Default gateway: <optional>
- Select the Use the following DNS server address. Configure the Preferred DNS server for the IP address of your domain controller. Click OK. Click Close.
- Preferred DNS Server: 192.168.1.10
- Click Start, type sysdm.cpl and press ENTER. Click Change.
- In Computer name, type CA02 and then click OK.
- When prompted that you need to restart the computer, click OK. Click Close. Click Restart Now.
- After CA02 restarts, log on as a local administrator.
- Click Start, type sysdm.cpl and press ENTER. Click Change.
- In Member of, select Domain, and then type fabrikam.com. Click OK.
- In Windows Security, enter the User name and password for the domain administrator account. Click OK.
- You should be welcomed to the Fabrikam domain. Click OK.
- When prompted that a restart is required, click OK. Click Close. Click Restart Now.
Create CAPolicy.inf for Enterprise Root CA
Log onto CA02.Fabrikam.com as Fabrikam\Administrator. (Ensure that you switch user to log on as Fabrikam\Administrator)
Click Start, select Run and then type notepad C:\Windows\CAPolicy.inf and press ENTER.
When prompted to create new file, click Yes.
Type in following as content of the file.
[Version]
Signature="$Windows NT$"
[PolicyStatementExtension]
Policies=InternalPolicy
[InternalPolicy]
OID= 1.2.3.4.1455.67.89.5
URL=http://pki.fabrikam.com/cps.txt
[Certsrv_Server]
RenewalKeyLength=2048
RenewalValidityPeriod=Years
RenewalValidityPeriodUnits=10
LoadDefaultTemplates=0
AlternateSignatureAlgorithm=0
Click File and Save to save the CAPolicy.inf file under C:\Windows directory.
** Important**: Ensure that the CAPolicy.inf is saved as an .inf file. The file will not be used if it is saved with any other file extension.
Close Notepad.
Notes
- Any entries in CAPolicy.inf file that are misspelled will be ignored.
- AlternateSignatureAlgorithm=1 is not compatible with Windows XP and Windows Server 2003 certificate clients.
- Windows Server 2008 R2 CAPolicy.inf Syntax - The CAPolicy.inf contains various settings that are used when installing the Active Directory Certification Service (ADCS) or when renewing the CA certificate. The CAPolicy.inf file is not required to install AD CS with the default settings, but in many cases the default settings are insufficient. The CAPolicy.inf can be used to configure CAs in these more complicated deployments.
- The OID shown in the example is the Microsoft OID. Individual organizations should obtain their own OIDs. For more information about OIDs, see Obtaining a Root OID from an ISO Name Registration Authority.
Publish the Root CA Certificate and CRL
To publish the root CA certificate and certificate revocation list (CRL):
- Ensure you are logged on to CA02.Fabrikam.com as Fabrikam\Administrator.
- Copy Root CA Certificate (CA01_Fabrikam Root CA.crt) and Root CA CRL (Fabrikam Root CA.crl) files from C:\Windows\System32\CertSrv\CertEnroll directory on CA01 server to removable media.
- Note: CA01 is configured as standalone offline CA without network connectivity. You must use removable media to transfer the files from CA01 to CA02.fabrikam.com. For instructions on transferring files using a virtual floppy disk using Microsoft Windows Server™ Hyper-V, see Creating, Using, and Transferring Files using Virtual Floppy Disks.
- For example, if you were copying the files to a floppy disk using drive letter A:, you would run the following command:
- copy C:\Windows\System32\CertSrv\CertEnroll\.cr* A:\
- On CA02, to publish Fabrikam Root CA Certificate and CRL in Active Directory, run the following commands at an administrative command prompt. Ensure that you substitute the correct drive letter of your removable media (for A:) in the commands that follow:
- certutil -f -dspublish "A:\CA01_Fabrikam Root CA.crt" RootCA
- certutil -f -dspublish "A:\Fabrikam Root CA.crl" CA01
- To publish Fabrikam Root CA Certificate and CRL to http://pki.fabrikam.com/CertEnroll, copy Fabrikam Root CA Certificate and CRL to \srv1.Fabrikam.com\C$\CertEnroll directory. Run the following commands from an administrative command prompt. Ensure that you substitute the correct drive letter of your removable media (for A:) in the commands that follow:
- copy "A:\CA01_Fabrikam Root CA.crt" \SRV1.Fabrikam.com\C$\CertEnroll\
- copy "A:\Fabrikam Root CA.crl" \SRV1.Fabrikam.com\C$\CertEnroll\
- To add Fabrikam Root CA Certificate and CRL in CA02.Fabrikam.com local store, run the following command from an administrative command prompt. Ensure that you substitute the correct drive letter of your removable media (for A:) in the commands that follow:
- certutil -addstore -f root "CA01_Fabrikam Root CA.crt"
- certutil -addstore -f root "Fabrikam Root CA.crl"
Additional information
- TechNet Library: Appendix A: Directory Objects
- TechNet Library: Certutil Syntax
Install Subordinate Issuing CA
To install the subordinate issuing CA on CA02.fabrikam.com:
Ensure that you are logged on to CA02.fabrikam.com as Fabrikam\Administrator.
Open Server Manager.
Right-click Roles and then select Add Roles.
On the Before You Begin page select Next.
On the Select Server Roles page select Active Directory Certificate Services and then click Next.
On the Introduction to Active Directory Certificate Services page, click Next.
On the Select Role Services page, select Certification Authority and Certification Authority Web Enrollment. If you see the Add Roles Wizard, click Add Required Role Services. Click Next.
On the Add role services and features required for Certificate Authority Web Enrollment page, click Add Required Role Services and then click Next.
On the Specify Setup Type page, ensure that Enterprise is selected, and then click Next.
- Note: Enterprise option will be greyed out if you are not logged on as Enterprise Admin or do not have local administrator permission.
On the Specify CA Type page, select Subordinate CA, and then click Next.
On the Set Up Private Key page, ensure that Create a new private key is selected, and then click Next.
Leave the defaults on the Configure Cryptography for CA page, then click Next.
- Important: When installing in a production environment, the CSP, Hash Algorithm and Key length selected must support application compatibility requirements.
On Configure CA Name page, clear the existing entry for Common name for this CA box, and enter Fabrikam Issuing CA, then select Next.
- Note - Distinguished Name Suffix is automatically populated and should not be modified.
On the Request certificate from a parent CA page, select Save a certificate request to file and manually send it later to a parent CA option then click Next.
Leave the defaults on the Configure Certificate Database page, and then click Next.
On the Web Server (IIS) page, click Next.
Leave the defaults on the Select Role Services page and then click Next.
On the Confirm Installation Selections page, click Install.
Review the information on the Installation Results page to verify that the installation is successful and then click Close.
- The following warning message is expected: "The Active Directory Certificate Services installation is incomplete. To complete the installation, use the request file "C:\CA02.fabrikam.com_Fabrikam Issuing CA.req" to obtain a certificate from the parent CA. Then, use the Certification Authority snap-in to install the certificate. To complete this procedure, right-click the node with the name of the CA, and then click Install CA Certificate. The operation completed successfully. 0x0 (WIN32: 0)."
Copy C:\CA02.fabrikam.com_Fabrikam Issuing CA.req to your removable media. For example, if you want to copy to a floppy disk drive using the drive letter A:, you would run the following command from a command prompt:
- copy "C:\CA02.fabrikam.com_Fabrikam Issuing CA.req" A:\
Submit the Request and Issue Fabrikam Issuing CA Certificate
To submit the certificate request and issue the requested certificate:
- Ensure that you are logged on to CA01 as CA01\Administrator. Place the removable media with the certificate request into CA01.
- On CA01, open an administrative command prompt. Then, submit the request using the following command (assuming that A:\ is your removable media drive letter):
- certreq -submit "A:\CA02.fabrikam.com_Fabrikam Issuing CA.req"
- Note: Pay attention to the RequestID number that is displayed after you submit the request. You will use this number when retrieving the certificate.
- In the Certification Authority List dialog box, ensure that Fabrikam Root CA is selected and then click OK.
- Open the Certification Authority console. To do so, click Start, click Administrative Tools, click Certification Authority.
- In the certsrv [Certification Authority (Local)] dialog box, in the console tree, expand Fabrikam Root CA.
- Click Pending Requests. In the details pane, right-click the request you just submitted, click All Tasks, and then click Issue.
- Return to the administrative command prompt to accept the issued certificate by running the following command. Ensure that you substitute the appropriate drive letter of your removable media for A: as well as the correct RequestID for 2:
- certreq -retrieve 2 "A:\CA02.fabrikam.com_Fabrikam Issuing CA.crt"
- In the Certification Authority List dialog box, ensure that Fabrikam Root CA is selected and then click OK.
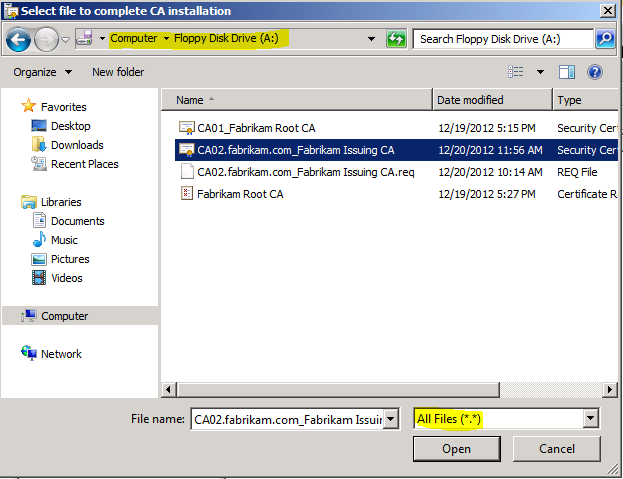
Install the Fabrikam Issuing CA Certificate on CA02
To install the certificate and start the Certification Authority service on CA02:
- Ensure that you are logged on to CA02.fabrikam.com as Fabrikam\Administrator. Place the removable media with the issued certificate for CA02.fabrikam.com into CA02.
- Open the Certification Authority console.
- In the Certification Authority console tree, right-click Fabrikam Issuing CA, and then click Install CA Certificate.
- In the Select file to complete CA installation, navigate to your removable media. Ensure that you are displaying All Files (*.*) and click the CA02.fabrikam.com_Fabrikam Issuing CA certificate. Click Open.
- In the console tree, right-click Fabrikam Issuing CA, click All Tasks, and then click Start Service.
- In the console tree, expand Fabrikam Issuing CA and then click Certificate Templates. Notice there are no certificates shown in the details pane. This is because the CAPolicy.inf specified not to install the default templates in the line LoadDefaultTemplates=0.
Perform Post Installation Configuration Tasks on the Subordinate Issuing CA
There are multiple settings to configure to complete the installation of the issuing CA. These are similar to the tasks that were needed to complete the configuration of the root CA.
Configure Certificate Revocation and CA Certificate Validity Periods
To configure certificate revocation and CA certificate validity periods:
- Ensure that you are logged on to CA02.fabrikam.com as Fabrikam\Administrator.
- Configure the CRL and Delta CRL settings by running the following command from an administrative command prompt:
- Certutil -setreg CA\CRLPeriodUnits 1
- Certutil -setreg CA\CRLPeriod "Weeks"
- Certutil -setreg CA\CRLDeltaPeriodUnits 1
- Certutil -setreg CA\CRLDeltaPeriod "Days"
- Define CRL overlap settings by running the following command from an administrative command prompt:
- Certutil -setreg CA\CRLOverlapPeriodUnits 12
- Certutil -setreg CA\CRLOverlapPeriod "Hours"
- The default setting for Validity Period is 2 years in registry. Adjust this setting accordingly to meet your needs of entity certificate’s lifetime issued from Fabrikam Issuing CA. It is recommended that you do not configure validity periods that are longer than half of total lifetime of Fabrikam Issuing CA certificate, which was issued to be valid for 10 years. To limit issued certificates to 5 years, run the following commands from an administrative command prompt:
- Certutil -setreg CA\ValidityPeriodUnits 5
- Certutil -setreg CA\ValidityPeriod "Years"
Additional information
- CRLPeriodUnits - You can use this setting to specify the number of days, weeks, months, or years, that a CRL will be valid.
- CRLPeriod - You can use this setting to specify whether the validity period of a CRL will be defined in days, weeks, months, or years.
- CRLDeltaPeriodUnits - You use this setting to specify the number of days, weeks, months, or years that delta CRLs can be valid. If a CA is to be offline, you should disable delta CRL publication.
- CRLDeltaPeriod - You use this setting to specify whether delta CRL lifetimes will be defined in days, weeks, months, or years. The delta CRL publication interval setting is similar to the CRL publication interval setting. If a CA is to be offline, you should disable delta CRL publication.
- The use of delta CRLs needs to be based on a need to publish revocation knowledge quickly while minimizing bandwidth consumption issues that can result with base CRL usage only. CRLPeriodUnits and CRLDeltaPeriodUnits settings should not be less than Active Directory convergence time if you are planning to publish CRLs to Active Directory.
- CRLOverlapPeriodUnits - You use this setting to specify the number of days, weeks, months, or years that CRLs can overlap. When a large number of certificates are revoked, such as during an employee layoff, the delta CRL size might increase significantly because of the large number of entries, and almost all clients will refer to the older base CRL. You can reduce the size of the overlap period to speed the propagation process for the new base CRL and help minimize the size of delta CRLs.
- CRLOverlapPeriod - This setting specifies whether the overlap period for CRLs will be defined in days, weeks, months, or years.
- The overlap period for CRLs is the amount of time at the end of a published CRLs lifetime that a client can use to obtain a new CRL before the old CRL is considered unusable. The default setting for this value is 10% of the CRL lifetime. Because some environments may require longer periods to replicate a CRL, this setting can be configured manually.
- ValidityPeriodUnits - You can use this setting to define the number of days, weeks, months, or years that a certificate issued by the CA will be valid. The validity period for a certificate cannot be greater than the validity period of the CA that issued the certificate. The default value depends on the type of certificate.
- ValidityPeriod - You can use this setting to specify whether the validity period of certificates issued by the CA will be defined in days, weeks, months, or years. The default value depends on the type of certificate.
- When Enterprise Issuing CA receives the certificate enrollment request from end entity it takes into account number of factors while determining lifetime as listed in the following:
- Remaining lifetime of CA Certificate. The CA will not issue certificates that are valid past the CA’s own lifetime.
- The validity period specified in the Certificate Template.
- The value specified of the following registry keys:
- ValidityPeriod
- ValidityPeriodUnits
- The certificate issued will be configured with the validity period that is the shortest of these items.
Enable Auditing on the Issuing CA
CA auditing depends on system Audit Object Access to be enabled. The following instructions describe how to use Local Security Policy to enable object access auditing.
Click Start, click Administrative Tools, and then select Local Security Policy.
Expand Local Policies and then select Audit Policy.
Double click Audit Object Access and then select Success and Failure then click OK.
Close Local Security Policy editor.
Enable auditing for the CA by selecting which group of events to audit in the Certificate Authority MMC snap-in or by configuring AuditFilter registry key setting. To configure Auditing for all CA related events, run the following command from an administrative command prompt:
Certutil -setreg CA\AuditFilter 127
Additional Information
- CA\AudtiFilter 127 enables all forms of auditing. You can enable use this setting to enable specific or all auditing events for CA.
- You could have used a domain Group Policy in this case because the enterprise issuing CA is joined to the domain.
- TechNet articles
Configure the AIA and CDP
There are multiple different methods for configuring the Authority Information Access (AIA) and certificate revocation list distribution point (CDP) locations. You can use the user interface (in the Properties of the CA object), certutil, or directly edit the registry. The AIA is used to point to the public key for the certification authority (CA). The CDP is where the certificate revocation list is maintained, which allows client computers to determine if a certificate has been revoked. In this lab there will be three locations for the AIA and four locations for the CDP.
Configure the AIA
Using a certutil command is a quick and common method for configuring the AIA. When you run the following certutil command, you will be configuring a static file system location, a lightweight directory access path (LDAP) location, and http location for the AIA. The certutil command to set the AIA modifies the registry, so ensure that you run the command from an command prompt run as Administrator. Run the following command:
certutil -setreg CA\CACertPublicationURLs "1:C:\Windows\system32\CertSrv\CertEnroll\1_%3%4.crt\n2:ldap:///CN=%7,CN=AIA,CN=Public Key Services,CN=Services,%6%11\n2:http://pki.fabrikam.com/CertEnroll/%1_%3%4.crt"****
After you have run that command, run the following command to confirm your settings:
certutil -getreg CA\CACertPublicationURLs
If you look in the registry, under the following path: HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\CertSvc\Configuration\Fabrikam Issuing CA, you can confirm the CACertPublicationURLs by opening that REG_MULTI_SZ value. You should see the following:
1:C:\Windows\system32\CertSrv\CertEnroll\1_%3%4.crt
2:ldap:///CN=%7,CN=AIA,CN=Public Key Services,CN=Services,%6%11
2:http://pki.fabrikam.com/CertEnroll/%1_%3%4.crt
You can also see this in the the CA (certsrv) console. To open the console, click Start, click Administrative Tools, and then click Certification Authority. In the navigation pane, expand the Certificate Authority (Local). Right-clickFabrikam Root CA and then click Properties. On the Extensions tab, under Select extension, click Authority Information Access (AIA) and you will see the graphical representation of the AIA settings.
From an administrative command prompt, run the following command to copy the Fabrikam Issuing CA certificate to the http AIA location:
copy "c:\Windows\System32\certsrv\certenroll\CA02.fabrikam.com_Fabrikam Issuing CA.crt" \srv1.fabrikam.com\c$\certenroll\
Additional Information
- CACertPublicationURLs - This setting identifies the URL of the authority information access (AIA) point where a client can find a CA certificate. Because the authority information access point is the location of the certificate that was used to sign the certificate.
- Each number value listed above preceding each URL means specific configuration setting. You can find more information about these values at AIA Publishing Properties.
- These settings can be configured from the Extensions tab in the Certificate Authority manager as well.
- The HTTP path to pki.fabrikam.com is being used as an alias (CNAME configured earlier), which provides flexibility for load balancing scenarios.
Configure the CDP
Clients will use the CDP to locate the CRL and delta CRLs for the certificates issued by the CA. This allows certificate clients to ensure that the certificates have not been revoked. You can also configure the CDP with the user interface, certutil, and registry. Using a certutil command is a quick and common method for configuring the CDP. When you run the following certutil command, you will be configuring a static file system location, an LDAP location, an http location, and a file system location.
Note: The file system location that you will be setting will allow the CRL to be copied over the network to the web server (SRV1), which is why we earlier allowed the Cert Publishers group access to the share and folder. All CAs are members of the Cert Publishers group, so we effectively allowed all CAs to copy to the CertEnroll folder on SRV1. Some administrators decide to configure a separate group of specific computers for that purpose or even grant permissions to the CAs individually.
The certutil command to set the CDP modifies the registry, so ensure that you run the command from an command prompt run as Administrator. Run the following command:
certutil -setreg CA\CRLPublicationURLs "65:C:\Windows\system32\CertSrv\CertEnroll\3%8%9.crl\n79:ldap:///CN=%7%8,CN=%2,CN=CDP,CN=Public Key Services,CN=Services,%6%10\n6:http://pki.fabrikam.com/CertEnroll/%3%8%9.crl\n65:\srv1.fabrikam.com\CertEnroll\3%8%9.crl"
After you run that command, run the following certutil command to verify your settings:
certutil -getreg CA\CRLPublicationURLs
In the registry location:HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration\Fabrikam Issuing CA you can open the REG_MULTI_SZ value and see the configuration of these values:
65:C:\Windows\system32\CertSrv\CertEnroll\3%8%9.crl
79:ldap:///CN=%7%8,CN=%2,CN=CDP,CN=Public Key Services,CN=Services,%6%10
6:http://pki.fabrikam.com/CertEnroll/%3%8%9.crl
65:file://\srv1.fabrikam.com\CertEnroll\3%8%9.crl
Additional Information
- CRLPublicationURLs - This setting identifies CRL distribution points where a client can find the CRL that is related to a certificate. The CRL distribution point of a root CA should be empty. For intermediate and issuing CAs, you use t he Certification Authority snap-in to define CRL distribution points. These values are then stored in the registry.
- Each number value listed above preceding each URL means specific configuration setting. You can find more information about these values at CRL Publishing Properties.
- TechNet Article - CRL Distribution Point Replacement Token
You can also see this in the the CA (certsrv) console. To open the console, click Start, click Administrative Tools, and then click Certification Authority. In the navigation pane, ensure that Certificate Authority (Local) is expanded. Right-click Fabrikam Root CA and then click Properties. On the Extensions tab, under Select extension, click CRL Distribution Point (CDP) and you will see the graphical representation of the CDP settings.
At an administrative command prompt, run the following commands to restart Active Directory Certificate Services and to publish the CRL.
net stop certsvc && net start certsvc
certutil -crl
Install and Configure the Online Responder Role Service
The use of Online Responders that distribute OCSP responses, along with the use of CRLs, is one of two common methods for conveying information about the validity of certificates. Unlike CRLs, which are distributed periodically and contain information about all certificates that have been revoked or suspended, an Online Responder receives and responds only to requests from clients for information about the status of a single certificate. The amount of data retrieved per request remains constant regardless of the number of revoked certificate.
Install the Online Responder Role Service on SRV1
To install the Online Responder role service on SRV1:
- Ensure that you are logged on to SRV1.Fabrikam.com as Fabrikam\Administrator.
- Open Server Manager.
- Right click on Roles, and then click Add Roles.
- On the Before You Begin page, then select Next.
- On the Select Server Roles page, select Active Directory Certificate Services and then click Next.
- On Introduction to Active Directory Certificate Services page, click Next.
- On the Select Role Services page, clear the Certification Authority, and then select Online Responder. Click Next.
- Note: You do not want to install a Certification Authority on SRV1.Fabrikam.com, so you are clearing that checkbox.
- If the Add role services and features required for Online Responder page appears, click Add Required Role Services and then click Next. Then, on the Web Server (IIS), click Next.
- On the Confirm Installation Selections page, click Install. Click Close when the installation is complete.
Add the OCSP URL to the Fabrikam Issuing CA
To add the OCSP URL to the Fabrikam Issuing CA:
Ensure that you are logged on to CA02.fabrikam.com as Fabrikam\Administrator
In the Certification Authority console, in the console tree, right-click Fabrikam Issuing CA, and then click Properties.
On the Extensions tab, under Select extension, select Authority Information Access (AIA), and then click Add.
In Location, type http://srv1.fabrikam.com/ocsp and then click OK.
Select Include in the online certificate status protocol (OCSP) extension.
- Note: A common misconfiguration is to select both checkboxes in the Extensions tab, which is incorrect. Ensure that Include in the online certificate status protocol (OCSP) extension checkbox is the only one selected.
Click OK. When prompted by the Certification Authority dialog box to restart Active Directory Certificate Services, click Yes.
Important: The Fabrikam Issuing CA will now include http://srv1.fabrikam.com/ocsp URL as part of Authority Information Access (AIA) extension in all newly issued certificates issued or renewed or re-enrolled certificates. However, certificates enrolled from Fabrikam Issuing CA prior to this change will not have this URL.
Configure and Publish the OCSP Response Signing Certificate on the Fabrikam Issuing CA
To configure the OCSP response signing certificate:
- On CA02.fabrikam.com, ensure that you are logged on as Fabrikam\Administrator.
- In the Certification Authority console, ensure that the Fabrikam Issuing CA is expanded in the console tree.
- Right-click on Certificate Templates and then click Manage. Certificate Templates opens and displays the certificate templates stored in Active Directory.
- In the details pane (middle pane) right-click OCSP Response Signing and then click Properties.
- On the Security tab click Add. Click Object Types.
- In the Object Types dialog box, select Computers and then click OK.
- In Enter the object names to select, type SRV1 and then click Check Names. Click OK.
- Ensure that SRV1 is selected and in the Allow column, ensure that the Read and Enroll permissions are selected. Click OK.
- Close Certificate Templates MMC console.
- In certsrv console, right-click Certificate Templates, then select New and then select Certificate Template to Issue.
- In the Enable Certificate Templates dialog box, click OCSP Response Signing and the click OK.
Configure Revocation Configuration on the Online Responder
To configure the revocation configuration:
- On SRV1.Fabrikam.com, ensure that you are logged on as Fabrikam\Administrator.
- Open Server Manager.
- In the console tree, expand Roles, expand Active Directory Certificate Services, and then expand Online Responder.
- Right-click Revocation Configuration and then click Add Revocation Configuration.
- On the Getting Started with Adding a Revocation Configuration page click Next.
- In Name, enter Fabrikam Issuing CA, and then click Next.
- On the Select CA Certificate Location page ensure that Select a certificate for an Existing enterprise CA is selected, then click Next.
- On the Choose CA Certificates page, ensure that Browse CA certificates published in Active Directory is selected, and then click Browse.
- On the Select Certification Authority dialog box, ensure that Fabrikam Issuing CA is selected, and then click OK. Click Next.
- Leave the defaults on the Select Signing Certificate page, and then click Next.
- On the Revocation Provider page, click Provider.
- Review the choices listed for OCSP Responder to down CRLs in the form of LDAP and HTTP locations.
- Note: Depending on your needs you could select either the LDAP or HTTP as your primary location for OCSP Responder to download CRLs. You can change order for LDAP and HTTP URLs using Move Up or Move Down button. Leave the defaults as they appear.
- Clear the Refresh CRLs based on their validity periods. In the Update CRLs at this refresh interval (min) box, type 15, and then click OK. Click Finish.
- Note: Modifying this setting to download CRLs at a faster rate than the CRLs normal expiration makes it possible for the OCSP responder to rapidly download new CRLs rather than use the last downloaded CRLs normal expiration date. Production needs may differ from the value chosen here.
- In the Certification Authority console, expand Array Configuration and then click SRV1.
- Review Revocation Configuration Status in the middle pane to ensure there is a signing certificate present and the status reports as OK. The provider is successfully using the current configuration.
Configure Group Policy to Provide the OCSP URL for the Fabrikam Issuing CA
This configuration would only be needed to allow existing certificate holders to take advantage of a new OCSP responder without having to re-enroll new certificates with the required OCSP URL added in them.
- Ensure you are logged on to DC01.Fabrikam.com as Fabrikam\Administrator.
- Open an administrative command prompt and run the following commands:.
- cd\
- certutil -config "ca02.fabrikam.com\Fabrikam Issuing CA" -ca.cert fabrikamissuingca.cer
- Click Start, click Run, and then type gpmc.msc. Press ENTER.
- Expand Forest, expand Domains, expand Fabrikam.com, and then expand Group Policy Objects.
- Right click Default Domain Policy, then click Edit.
- Under Computer Configuration, expand Policies, expand Windows Settings, expand Security Settings, and then expand Public Key Policies.
- Right-click Intermediate Certification Authorities, and then click Import.
- On the Welcome to Certificate Import Wizard page, click Next.
- In File name, type C:\fabrikamissuingca.cer, and then click Next.
- On the Certificate Store page, click Next.
- On the Completing the Certificate Import Wizard, click Finish, and then click OK.
- In the console tree, select Intermediate Certification Authorities.
- In the details pane, right-click Fabrikam Issuing CA certificate, then click Properties.
- On the OCSP tab, in Add URL enter http://srv1.fabrikam.com/ocsp, and then click Add URL. Click OK.
- Close the Group Policy Management Editor and then close Group Policy Management console.
Join Win7 to the domain
- Log on to WIN7 as the local administrator.
- Click Start, type ncpa.cpl and press ENTER.
- In Network Connections, right-click the Local Area Connection and then click Properties.
- If there are more than one Local Area Connection icons in the Network Connections, you want to modify the one that is connected to network segment shared by all the computers that you have installed for this lab.
- Click the Internet Protocol Version 4 (TCP/IPv4) and then click Properties.
- Select the Use the Following IP address. Configure the IP address, Subnet mask, and Default gateway appropriately for your test network.
- IP Address: 192.168.1.14
- Subnet mask: 255.255.255.0
- Default gateway: <optional>
- Select the Use the following DNS server address. Configure the Preferred DNS server as the IP address of your domain controller. Click OK. Click Close.
- Preferred DNS Server: 192.168.1.10.
- Click Start, type sysdm.cpl and press ENTER. Click Change. (Ensure the computer name is already set to WIN7 - otherwise change it)
- In Member of, select Domain, and then type fabrikam.com. Click OK.
- In Windows Security, enter the User name and password for the domain administrator account. Click OK.
- You should be welcomed to the Fabrikam domain. Click OK.
- When prompted that a restart is required, click OK. Click Close. Click Restart Now.
Verify the PKI Hierarchy Health
In this section you will use a few different methods and tools to verify your PKI Hierarchy health:
Check PKI Health with Enterprise PKI
To use the Enterprise PKI console to check PKI health:
- On CA02.Fabrikam.com, ensure that you are logged on as Fabrikam\Administrator.
- Open Server Manager.
- In the console tree, under Roles and Active Directory Certificate Services, click Enterprise PKI.
- Alternatively, you can run Enterprise PKI by running PKIView.msc from an administrative command prompt.
- Right click Enterprise PKI and then click Manage AD Containers.
- On the NTAuthCertificates tab, verify the Fabrikam Issuing CA certificate appears with a status of OK.
- On the AIA Container tab, verify both the Fabrikam Root CA and the Fabrikam Issuing CA certificates are present with a status of OK.
- On CDP Container tab, verify Fabrikam Root CA base CRL, Fabrikam Issuing CA base, and the Delta CRLs are present with a status of OK.
- On Certification Authorities Container, verify Fabrikam Root CA certificate is present with a status of OK.
- On Enrollment Services Container, verify Fabrikam Issuing CA certificate is present with a status of OK.
Configure Certificate Distribution on the Fabrikam Issuing CA
To publish a certificate for computers in the enterprise:
- On CA02.fabrikam.com, ensure that you are logged on as Fabrikam\Administrator.
- In the Certification Authority console, ensure that Fabrikam Issuing CA is expanded.
- Right-click Certificate Templates, select New and select Certificate Template to Issue.
- On the Enable Certificate Templates dialog box, click Workstation Authentication, page and then click OK.
Obtain a Certificate Using WIN7 and Verify PKI Health
To obtain a certificate for WIN7 and verify PKI health:
- Log into Win7.Fabrikam.com as Fabrikam\Administrator. (Ensure that you switch user to log on as Fabrikam\Administrator)
- Click Start, type mmc and then press ENTER.
- Click File, and then click Add/Remove Snap-in.
- Click Certificates, then click Add. Select Computer Account, and then click Finish. Click OK.
- Expand Certificates, right click Personal, click All Tasks, and then click Request New Certificate.
- On the Before you begin page, click Next.
- On the Select Certificate Enrollment Policy page, click Next.
- Select Workstation Authentication, click Enroll. When the certificate is enrolled, click Finish.
- In the console tree, expand Personal, click Certificates. In the details pane, right click the win7.fabrikam.com certificate, click All Tasks, and then click Export.
- On the the Welcome to Certificate Export Wizard page, click Next.
- On the Export Private Key, click Next. (No, do not export the private key is selected by default).
- On the Export File Format page, click Next. [DER encoded binary X.509 (.CER) is the default selection].
- On the File to Export page, type C:\win7, and then click Next.
- On the Completing the Certificate Export Wizard page, click then Finish, and then click OK.
- Open a command prompt and run the following commands: (To open a command prompt, click Start, type cmd, and then press ENTER)
- cd\
- certutil -URL C:\win7.cer
- In the URL Retrieval Tool, perform the following steps, in the Retrieve section:
- Select OCSP (from AIA) option and then click Retrieve. Confirm that it shows status as Verified.
- Select CRLs (from CDP) option and then click Retrieve. Confirm that it shows status as Verified.
- Select Certs (from AIA) option and then click Retrieve. Confirm that it shows status as Verified.
- Click Exit to close URL Retrieval Tool.
- From command prompt run following command to thoroughly verify certificate chain retrieval and revocation status.
- certutil -verify -urlfetch c:\win7.cer
- Review the output and make sure all the chain retrieval and revocation status successfully verified.