Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Effective May 1, 2025, Azure AD B2C will no longer be available to purchase for new customers. Learn more in our FAQ.
In this tutorial, learn how to integrate Azure Active Directory B2C (Azure AD B2C) with Experian CrossCore, a service that verifies user identification. It does risk analysis based on information provided by the user during sign-up. CrossCore permits users to sign in, or not.
Learn more about Experian solutions, services, etc.
In this tutorial, you can use the following attributes in CrossCore risk analysis:
- IP Address
- Given Name
- Middle Name
- Surname
- Street Address
- City
- State or Province
- Postal Code
- Country or Region
- Phone Number
Prerequisites
To get started, you'll need:
- A Microsoft Entra subscription
- If you don't have one, you can get an Azure free account
- An Azure AD B2C tenant linked to your Azure subscription
Scenario description
The Experian integration includes the following components:
- Azure AD B2C: The authorization server that verifies user credentials, also known as the identity provider (IdP)
- Experian CrossCore: The service takes inputs from the user and verifies their identity
- Custom REST API: This implements the integration between Azure AD B2C and CrossCore
The following architecture diagram shows the implementation.
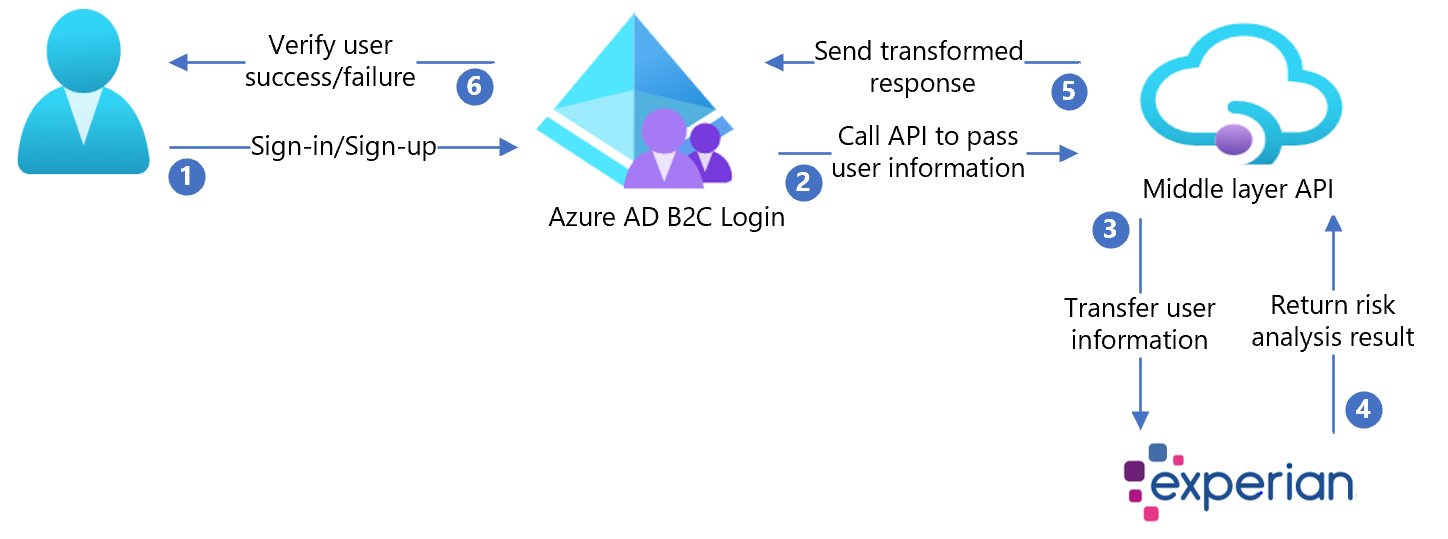
- User arrives at sign-in page, creates a new account, and enters information. Azure AD B2C collects user attributes.
- Azure AD B2C calls the middle-layer API and passes the user attributes.
- Middle-layer API collects user attributes and transforms it into an Experian CrossCore-ready format. Then, sends it to Experian CrossCore.
- Experian consumes the information validates user identification based on risk analysis. Then, it returns the result to the middle-layer API.
- Middle-layer API processes the information and sends relevant information in a JSON format to Azure AD B2C.
- Azure AD B2C receives information from middle-layer API. With a failure, an error message appears. With success, the user is authenticated and written into the directory.
Onboard with Experian
- Create an Experian account. To get started, go to Experian and scroll to the bottom for the contact form.
- When an account is created, you receive information for API configuration. The following sections continue the process.
Configure Azure AD B2C with Experian
Deploy the API
- Deploy the partner-integration to an Azure service: Go to /CrossCoreIntegrationApi.sln.
- Publish the code from Visual Studio.
Note
Use the deployed service URL to configure Microsoft Entra ID with the required settings.
Deploy the client certificate
The Experian API call is protected by a client certificate, provided by Experian.
- Follow the instructions in Private client certificate.
- Upload the certificate to the Azure App service.
The sample policy has two steps:
- Upload the certificate.
- Set the
WEBSITE_LOAD_ROOT_CERTIFICATESkey with the thumbprint of the certificate.
Configure the API
Application settings can be configured in the App service in Azure. Use this method to configure settings without checking them into a repository.
Provide the following application settings to the REST API:
| Application settings | Source | Notes |
|---|---|---|
| CrossCoreConfig:TenantId | Experian account configuration | N/A |
| CrossCoreConfig:OrgCode | Experian account configuration | N/A |
| CrossCore:ApiEndpoint | Experian account configuration | N/A |
| CrossCore:ClientReference | Experian account configuration | N/A |
| CrossCore:ModelCode | Experian account configuration | N/A |
| CrossCore:OrgCode | Experian account configuration | N/A |
| CrossCore:SignatureKey | Experian account configuration | N/A |
| CrossCore:TenantId | Experian account configuration | N/A |
| CrossCore:CertificateThumbprint | Experian certificate | N/A |
| BasicAuth:ApiUsername | Define a username for the API | Used in the ExtId configuration |
| BasicAuth:ApiPassword | Define a password for the API | Used in the ExtId configuration |
Create API policy keys
Refer to Custom policy starter pack to create two policy keys, one each for:
- API username
- API password you defined for HTTP basic authentication
Note
Later, you will need the keys for configuring the policies.
Replace the configuration values
In the partner-integration custom policies, find the following placeholders and replace with the corresponding values from your instance
| Placeholder | Replace with value | Example |
|---|---|---|
| {your_tenant_name} | Your tenant short name | "yourtenant" from yourtenant.onmicrosoft.com |
| {your_trustframeworkbase_policy} | Azure AD B2C name of your TrustFrameworkBase policy | B2C_1A_experian_TrustFrameworkBase |
| {your_tenant_IdentityExperienceFramework_appid} | App ID of the IdentityExperienceFramework app configured in your Azure AD B2C tenant | 00001111-aaaa-2222-bbbb-3333cccc4444 |
| {your_tenant_ ProxyIdentityExperienceFramework_appid} | App ID of the ProxyIdentityExperienceFramework app configured in your Azure AD B2C tenant | 00001111-aaaa-2222-bbbb-3333cccc4444 |
| {your_tenant_extensions_appid} | App ID of your tenant storage application | 00001111-aaaa-2222-bbbb-3333cccc4444 |
| {your_tenant_extensions_app_objectid} | Object ID of your tenant storage application | aaaaaaaa-0000-1111-2222-bbbbbbbbbbbb |
| {your_api_username_key_name} | Username key name, made in Create API policy keys | B2C_1A_RestApiUsername |
| {your_api_password_key_name} | Password key name, made in Create API policy keys | B2C_1A_RestApiPassword |
| {your_app_service_URL} | App service URL you set up | https://yourapp.azurewebsites.net |
Configure the Azure AD B2C policy
Refer to Custom policy starter pack for instructions to set up your Azure AD B2C tenant and configure policies.
Note
This sample policy is based on Active Directory B2C custom policy starterpack/LocalAccounts.
Tip
We recommend that customers add consent notification in the attribute collection page. Notify users that information goes to third-party services for identity verification.
Test the user flow
- Open the Azure AD B2C tenant and under Policies select User flows.
- Select your previously created User Flow.
- Select Run user flow.
- Application: the registered app (example is JWT).
- Reply URL: redirect URL.
- Select Run user flow.
- Complete sign-up flow and create an account.
- Sign out.
- Complete sign-in flow.
- Select continue
- CrossCore puzzle appears.