Password vaulting for single sign-on with application proxy
Microsoft Entra application proxy helps you improve productivity by publishing on-premises applications so that remote employees can securely access them. In the Microsoft Entra admin center, you can also set up single sign-on (SSO) to these apps. Your users only need to authenticate with Microsoft Entra ID, and they can access your enterprise application without having to sign in again.
Application proxy supports several single sign-on modes. Password-based sign-on is intended for applications that use a username and password combination for authentication. Microsoft Entra ID stores the sign-in information and automatically provides it to the application when your users access it remotely.
Prerequisites
This article requires that an app is published and tested with application proxy. To learn more, see Publish applications using Microsoft Entra application proxy.
Set up password vaulting for your application
Sign in to the Microsoft Entra admin center as at least an Application Administrator.
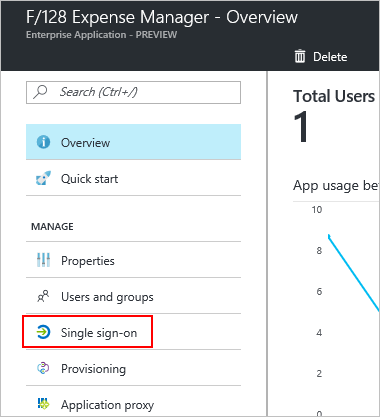
Browse to Identity > Applications > Enterprise applications > All applications.
From the list, select the app that you want to set up with SSO.
Select application proxy.
Change the Pre Authentication type to Passthrough and select Save. Later you can switch back to Microsoft Entra ID type again.
Select Single sign-on.
For the SSO mode, choose Password-based Sign-on.
For the Sign-on URL, enter the URL for the page where users enter their username and password to sign in to your app outside of the corporate network. The page could be the External URL that you created when you published the app through application proxy.
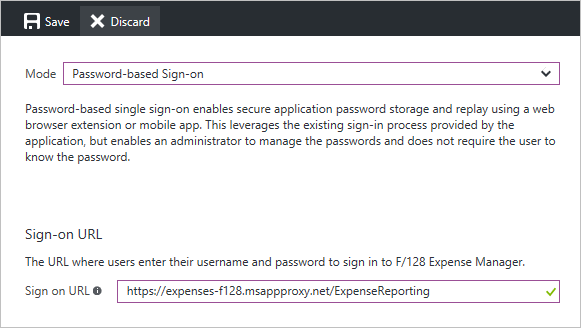
Select Save.
Select application proxy.
Change the Pre Authentication type to Microsoft Entra ID and select Save.
Select Users and Groups.
Assign users to the application, select Add user.
If you want to predefine credentials for a user, check the box in front of the user name and select Update credentials.
Browse to Identity > Applications > App registrations > All applications.
From the list, select the app that you configured with Password SSO.
Select Branding.
Update the Home page URL with the Sign on URL from the password SSO page and select Save.
Test your app
Go to the My Apps portal. Sign in with your credentials (or the credentials for a test account that you set up with access). Once signed in successfully, select the icon of the app. Opening the My Apps portal might trigger the installation of the My Apps Secure Sign-in browser extension. If credentials are predefined, the authentication to the app should happen automatically, otherwise you must specify the user name or password for the first time.
Next steps
- Read about other ways to implement Single sign-on
- Learn about Security considerations for accessing apps remotely with Microsoft Entra application proxy