Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Authenticator is used to sign in to any Microsoft Entra account without using a password. Authenticator uses key-based authentication to enable a user credential that's tied to a device, where the device uses a PIN or biometric. Windows Hello for Business uses a similar technology.
Authentication technology can be used on any device platform, including mobile. Authenticator can run on either iOS or Android.
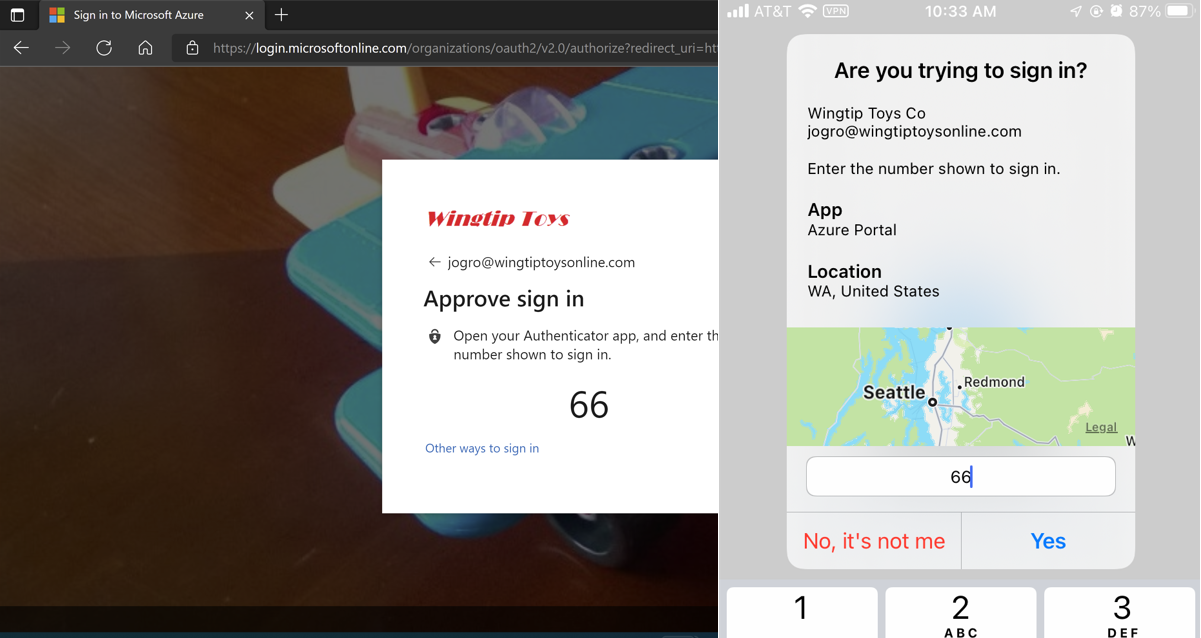
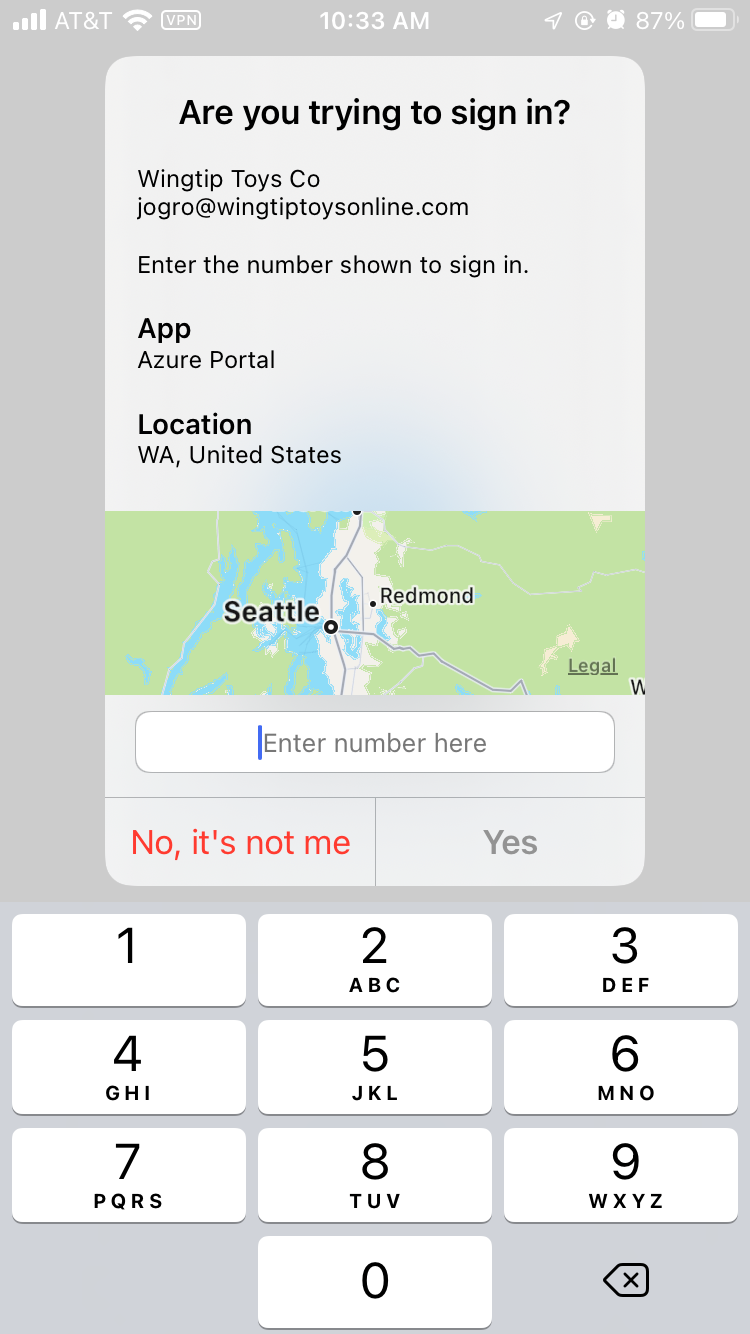
Phone sign-in from Authenticator shows a message that asks the user to tap a number in the app. It doesn't ask for a username or password. To complete the sign-in process in the app, follow these steps:
- In the Authenticator dialog, enter the number shown on the sign-in screen.
- Select Approve.
- Provide your PIN or biometric.
Multiple accounts
You can enable passwordless phone sign-in for multiple accounts in Authenticator on any supported Android or iOS device. Consultants, students, and other users with multiple accounts in Microsoft Entra ID can add each account to Authenticator and use passwordless phone sign-in for all of them from the same device.
The Microsoft Entra accounts can be in the same tenant or different tenants. Guest accounts aren't supported for multiple account sign-ins from one device.
Prerequisites
To use passwordless phone sign-in with Authenticator, you must meet the following prerequisites:
Recommended: Microsoft Entra multifactor authentication (MFA), with push notifications allowed as a verification method. Push notifications to a user smartphone or tablet help the Authenticator app to prevent unauthorized access to accounts and stop fraudulent transactions. The Authenticator app automatically generates codes when set up to do push notifications. A user has a backup sign-in method even if their device doesn't have connectivity.
The device must be registered with each tenant where it's used to sign in. For example, the following device must be registered with Contoso and Wingtip Toys to allow all accounts to sign in:
- balas@contoso.com
- balas@wingtiptoys.com and bsandhu@wingtiptoys
To use passwordless authentication in Microsoft Entra ID, first enable the combined registration experience, and then enable users for the passwordless method.
Enable passwordless phone sign-in authentication methods
Microsoft Entra ID lets Authentication Policy Administrators choose which authentication methods can be used to sign in. You can enable Microsoft Authenticator in the Authentication methods policy to manage both the traditional push MFA method and the passwordless authentication method.
After Microsoft Authenticator is enabled as an authentication method, users can go to Security info to register Authenticator as a way to sign in. Microsoft Authenticator is listed as a method on Security info. For example, Microsoft Authenticator-Passwordless or Microsoft Authenticator-MFA Push appears, depending on what's enabled and registered.
To enable the authentication method for passwordless phone sign-in, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Authentication Policy Administrator.
- Browse to Entra ID > Authentication methods > Policies.
Each group is enabled by default to use Any mode. Any mode allows group members to sign in with either a push notification or passwordless phone sign-in.
Note
If you see an error when you try to save, it might be because of the number of users or groups being added. As a workaround, replace the users and groups that you're trying to add with a single group in the same operation. Then select Save again.
User registration
Users register for the passwordless authentication method of Microsoft Entra ID. Users who already registered the Authenticator app for MFA can skip to the next section and enable phone sign-in.
Direct phone sign-in registration
Users can register for passwordless phone sign-in directly within the Authenticator app without the need to first register Authenticator with their account, all while never accruing a password. Here's how:
- Acquire a Temporary Access Pass from your admin or organization.
- Download and install the Authenticator app on your mobile device.
- Open Authenticator and select Add account, and then select Work or school account.
- Select Sign in.
- Follow the instructions to sign in with your account by using the Temporary Access Pass provided by your admin or organization.
- After sign-in, continue following the extra steps to set up phone sign-in.
Guided registration with My Sign-Ins
Note
Users can register Authenticator via combined registration only if the Authenticator authentication mode is set to Any or Push.
To register the Authenticator app, follow these steps:
- Browse to Security info.
- Sign in, and then select Add method > Authenticator app > Add to add Authenticator.
- Follow the instructions to install and configure the Authenticator app on your device.
- Select Done to finish the Authenticator configuration.
Enable phone sign-in
After users register for the Authenticator app, they need to enable phone sign-in:
- In Microsoft Authenticator, select the account registered.
- Select Set up Passwordless sign-in requests.
- Follow the instructions in the app to finish registering the account for passwordless phone sign-in.
An organization can direct its users to sign in with their phones, without using a password. For further assistance configuring Authenticator and enabling phone sign-in, see Sign in to your accounts by using the Authenticator app.
Note
If a policy restricts the user from using phone sign-in, the user can't enable it within Authenticator.
Sign in with a passwordless credential
A user can start using passwordless sign-in after all the following actions are completed:
- An admin enabled the user's tenant.
- The user added Authenticator as a sign-in method.
To start the phone sign-in process for the first time, follow these steps:
- Enter your name on the Sign-in pane.
- Select Next.
- If necessary, select Other ways to sign in.
- Select Approve a request on my Authenticator app.
A number then appears. The app prompts the user to authenticate by entering the appropriate number instead of by entering a password.
After the user uses passwordless phone sign-in, the app continues to guide the user through this method. The user also sees the option to choose another method.
Temporary Access Pass
If the tenant administrator enabled self-service password reset for users to set up passwordless sign-in with the Authenticator app for the first time by using a Temporary Access Pass, follow these steps:
- Open a browser on a mobile device or desktop, and go to Security info.
- Register the Authenticator app as your sign-in method. This action links your account to the app.
- Return to your mobile device and activate passwordless sign-in through the Authenticator app.
Management
We recommend the Authentication methods policy as the best way to manage Authenticator. Authentication Policy Administrators can edit this policy to enable or disable Authenticator. Admins can include or exclude specific users and groups from using it.
Admins can also configure parameters to better control how Authenticator is used. For example, they can add a location or the app name to the sign-in request so that users have greater context before they approve.
Known issues
The following known issues exist.
Not seeing the option for passwordless phone sign-in
In one scenario, a user might have an unanswered passwordless phone sign-in verification that's pending. If the user attempts to sign in again, the user sees only the option to enter a password.
To resolve this scenario, follow these steps:
- Open Authenticator.
- Respond to any notification prompts.
Then continue to use passwordless phone sign-in.
AuthenticatorAppSignInPolicy not supported
The legacy policy AuthenticatorAppSignInPolicy isn't supported with Authenticator. To enable users for push notifications or passwordless phone sign-in with the Authenticator app, use the Authentication Methods policy.
Federated accounts
After a user enables any passwordless credential, the Microsoft Entra sign-in process stops using login\_hint. The process no longer accelerates the user toward a federated sign-in location.
This logic generally prevents a user in a hybrid tenant from being directed to Active Directory Federation Services for sign-in verification. The option to select Use your password instead is still available.
On-premises users
Admins can enable users for MFA through an on-premises identity provider. Users can still create and use a single passwordless phone sign-in credential.
If a user attempts to upgrade multiple installations (5+) of Authenticator with the passwordless phone sign-in credential, this change might result in an error.
Related content
To learn about Microsoft Entra authentication and passwordless methods, see the following articles: