Sign in
Use the Connect-MgGraph command to sign in to your tenant.
Connect-MgGraph -Scopes "RoleManagement.ReadWrite.Directory"
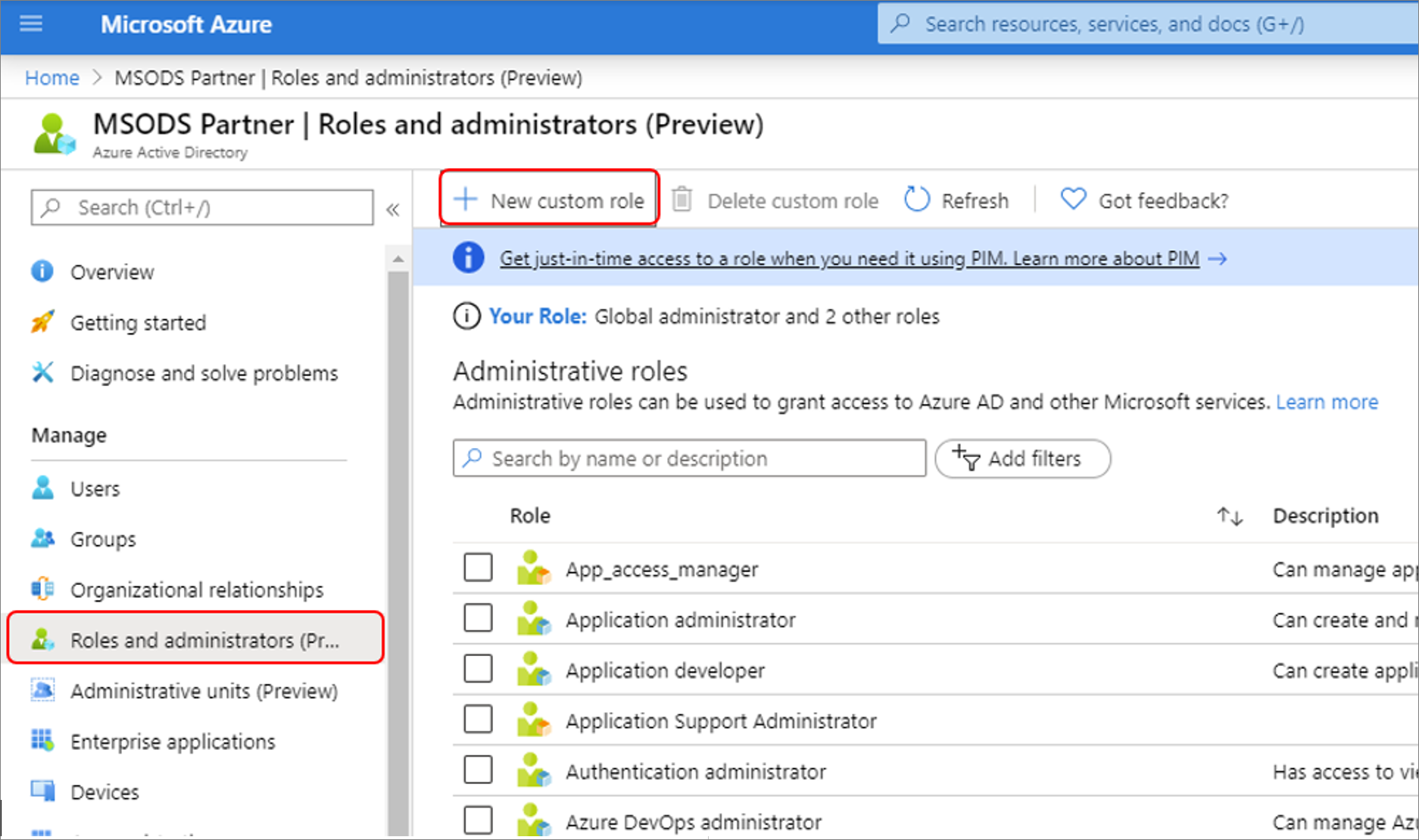
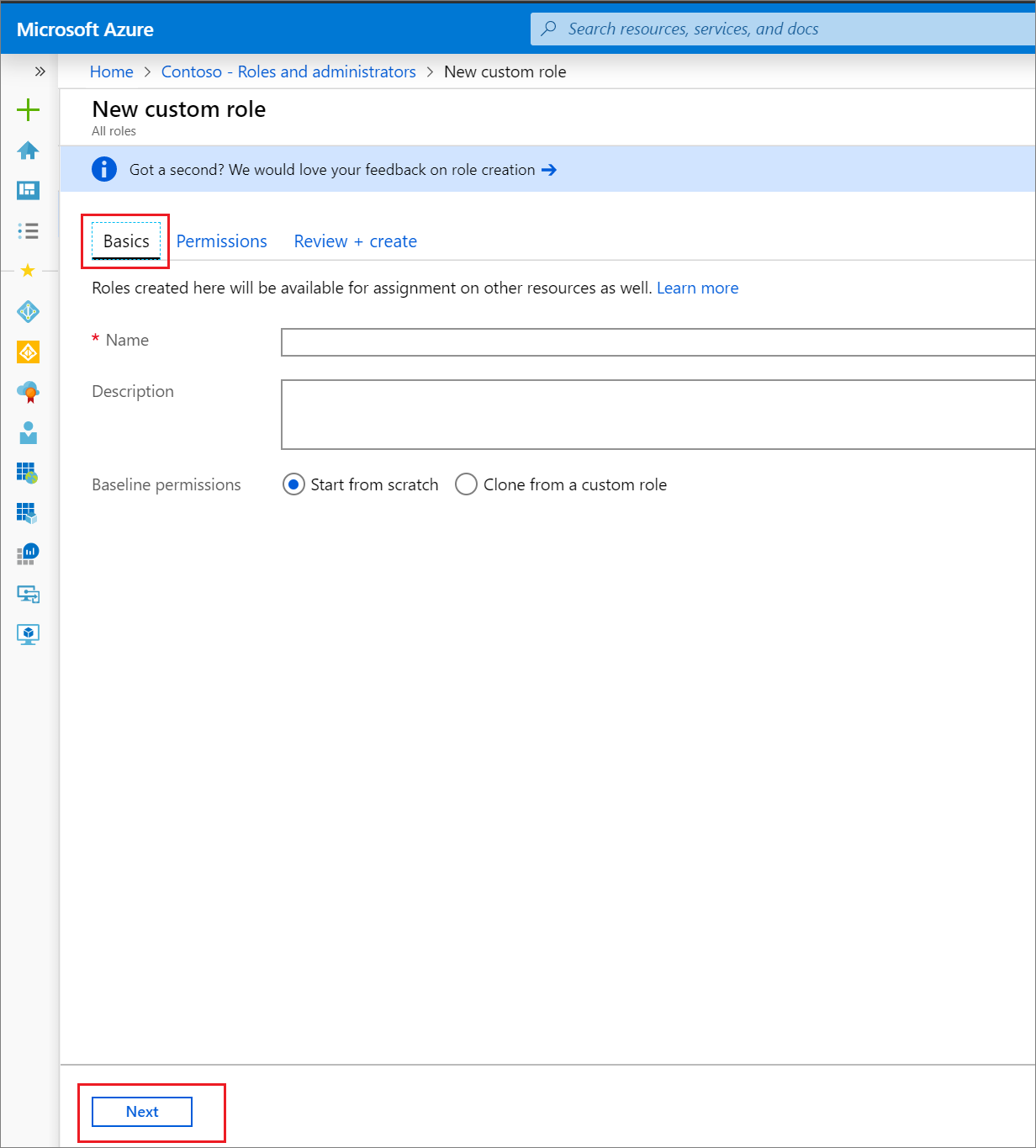
Create the custom role
Create a new role using the following PowerShell script:
# Basic role information
$displayName = "Application Support Administrator"
$description = "Can manage basic aspects of application registrations."
$templateId = (New-Guid).Guid
# Set of permissions to grant
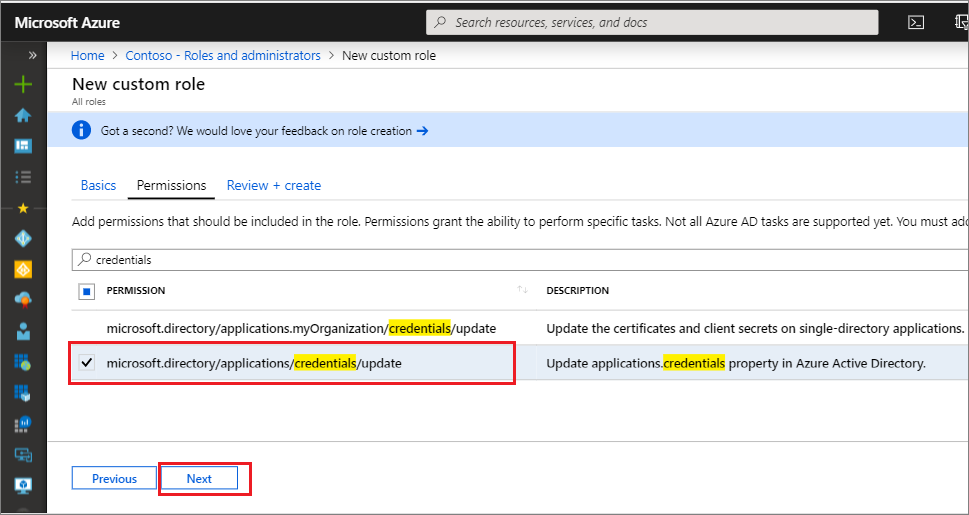
$allowedResourceAction =
@(
"microsoft.directory/applications/basic/update",
"microsoft.directory/applications/credentials/update"
)
$rolePermissions = @(@{AllowedResourceActions= $allowedResourceAction})
# Create new custom admin role
$customAdmin = New-MgRoleManagementDirectoryRoleDefinition -RolePermissions $rolePermissions -DisplayName $displayName -IsEnabled -Description $description -TemplateId $templateId
Assign the custom role using PowerShell
Assign the role using the below PowerShell script:
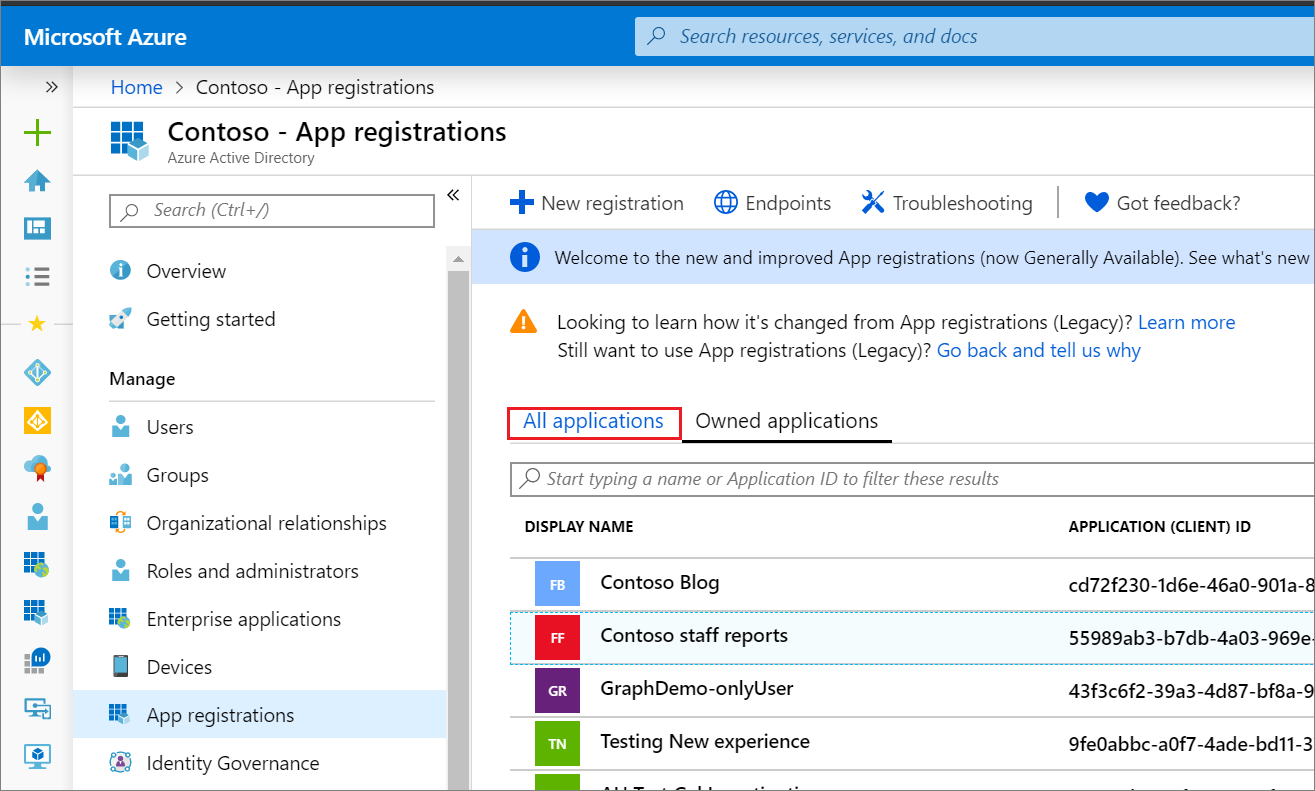
# Get the user and role definition you want to link
$user = Get-MgUser -Filter "userPrincipalName eq 'cburl@f128.info'"
$roleDefinition = Get-MgRoleManagementDirectoryRoleDefinition -Filter "DisplayName eq 'Application Support Administrator'"
# Get app registration and construct resource scope for assignment.
$appRegistration = Get-MgApplication -Filter "Displayname eq 'POSTMAN'"
$resourceScope = '/' + $appRegistration.objectId
# Create a scoped role assignment
$roleAssignment = New-MgRoleManagementDirectoryRoleAssignment -DirectoryScopeId $resourcescope -RoleDefinitionId $roledefinition.Id -PrincipalId $user.Id