Managed identities for Language resources
Managed identities for Azure resources are service principals that create a Microsoft Entra identity and specific permissions for Azure managed resources. Managed identities are a safer way to grant access to storage data and replace the requirement for you to include shared access signature tokens (SAS) with your source and target container URLs.
You can use managed identities to grant access to any resource that supports Microsoft Entra authentication, including your own applications.
To grant access to an Azure resource, assign an Azure role to a managed identity using Azure role-based access control (
Azure RBAC).There's no added cost to use managed identities in Azure.
Important
When using managed identities, don't include a SAS token URL with your HTTP requests—your requests will fail. Using managed identities replaces the requirement for you to include shared access signature tokens (SAS) with your source and target container URLs.
To use managed identities for Language operations, you must create your Language resource in a specific geographic Azure region such as East US. If your Language resource region is set to Global, then you can't use managed identity authentication. You can, however, still use Shared Access Signature tokens (SAS).
Prerequisites
To get started, you need the following resources:
An active Azure account. If you don't have one, you can create a free account.
An single-service Azure AI Language resource created in a regional location.
A brief understanding of Azure role-based access control (
Azure RBAC) using the Azure portal.An Azure Blob Storage account in the same region as your Language resource. You also need to create containers to store and organize your blob data within your storage account.
If your storage account is behind a firewall, you must enable the following configuration:
Go to the Azure portal and sign in to your Azure account.
Select your Storage account.
In the Security + networking group in the left pane, select Networking.
In the Firewalls and virtual networks tab, select Enabled from selected virtual networks and IP addresses.
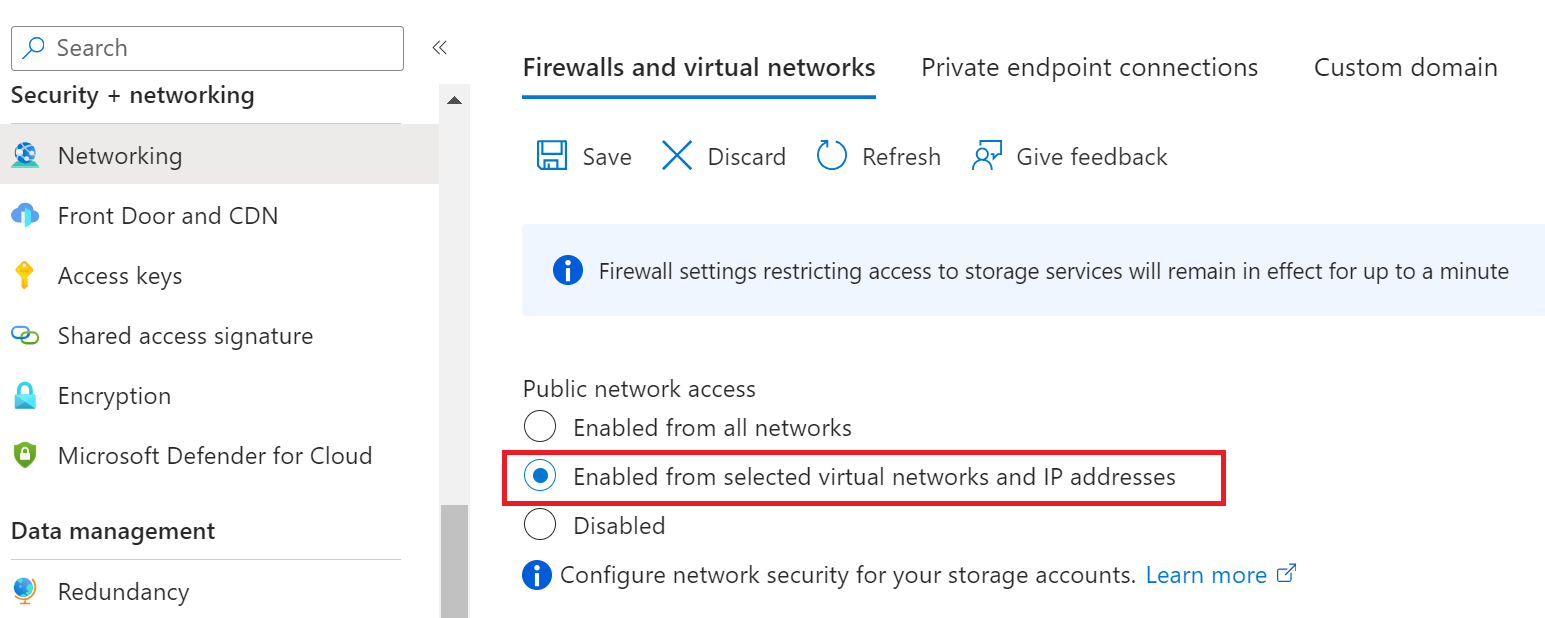
Deselect all check boxes.
Make sure Microsoft network routing is selected.
Under the Resource instances section, select Microsoft.CognitiveServices/accounts as the resource type and select your Language resource as the instance name.
Make certain that the Allow Azure services on the trusted services list to access this storage account box is checked. For more information about managing exceptions, see Configure Azure Storage firewalls and virtual networks.
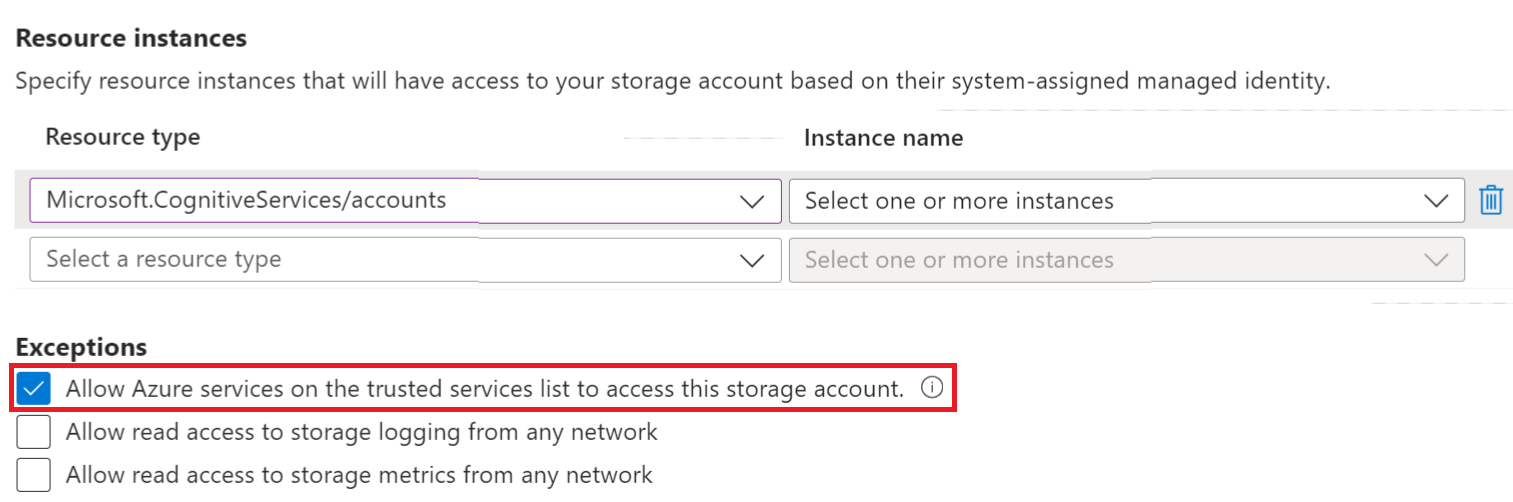
Select Save.
Note
It may take up to 5 minutes for the network changes to propagate.
Although network access is now permitted, your Language resource is still unable to access the data in your Storage account. You need to create a managed identity for and assign a specific access role to your Language resource.
Managed identity assignments
There are two types of managed identities: system-assigned and user-assigned. Currently, Document Translation supports system-assigned managed identity:
A system-assigned managed identity is enabled directly on a service instance. It isn't enabled by default; you must go to your resource and update the identity setting.
The system-assigned managed identity is tied to your resource throughout its lifecycle. If you delete your resource, the managed identity is deleted as well.
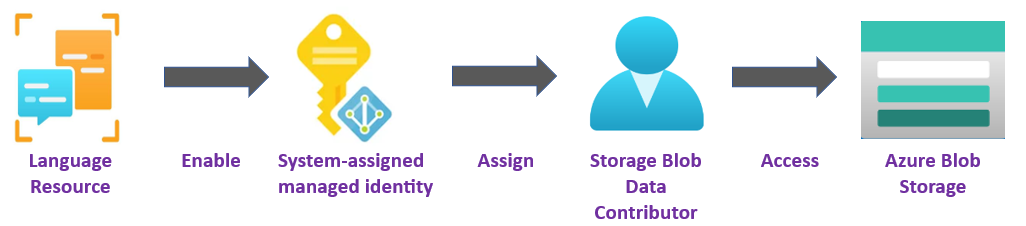
In the following steps, we enable a system-assigned managed identity and grant your Language resource limited access to your Azure Blob Storage account.
Enable a system-assigned managed identity
You must grant the Language resource access to your storage account before it can create, read, or delete blobs. Once you enabled the Language resource with a system-assigned managed identity, you can use Azure role-based access control (Azure RBAC), to give Language features access to your Azure storage containers.
Go to the Azure portal and sign in to your Azure account.
Select your Language resource.
In the Resource Management group in the left pane, select Identity. If your resource was created in the global region, the Identity tab isn't visible. You can still use Shared Access Signature tokens (SAS) for authentication.
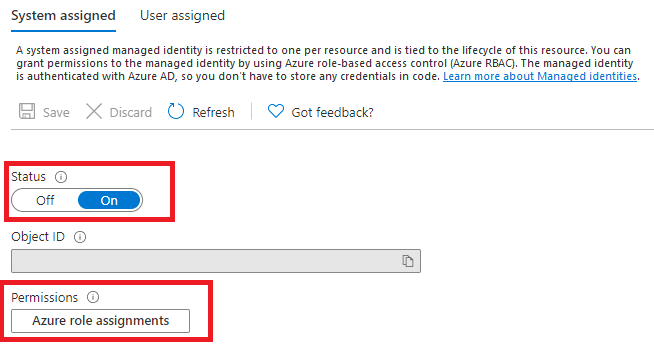
Within the System assigned tab, turn on the Status toggle.
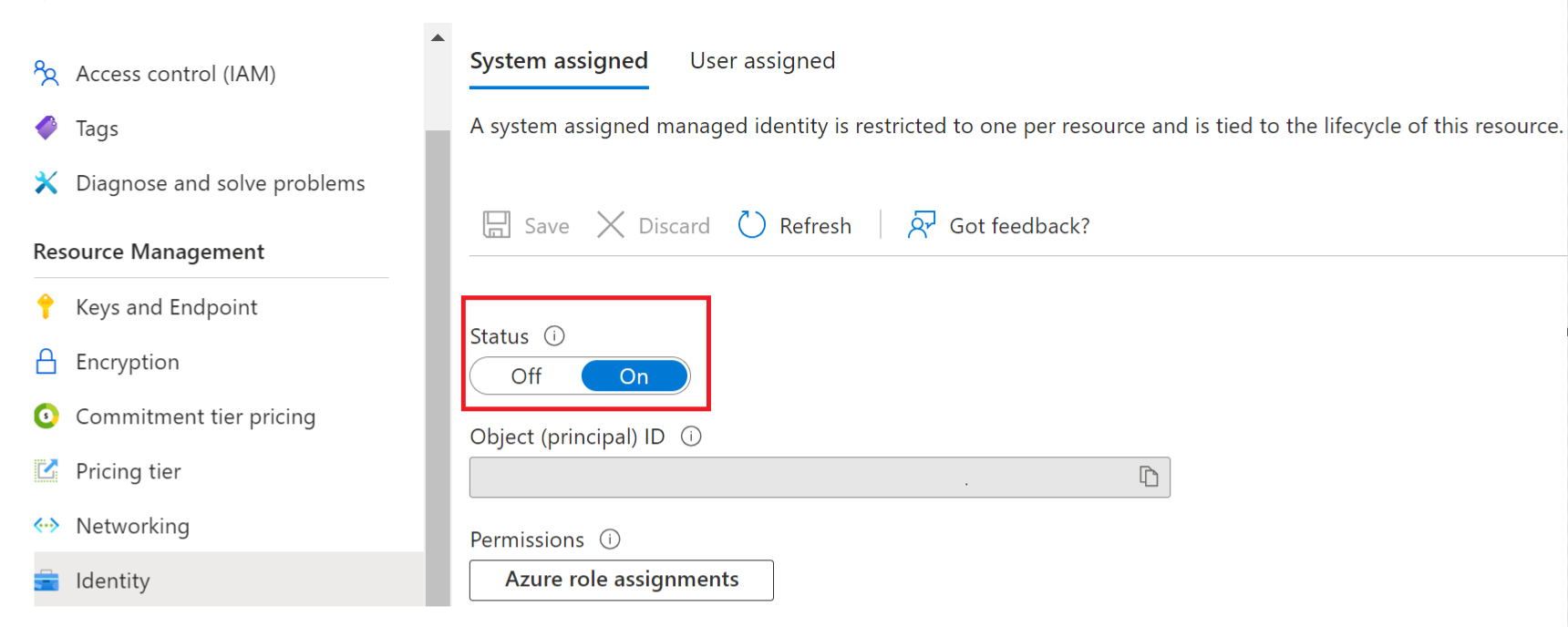
Important
User assigned managed identities don't meet the requirements for the batch processing storage account scenario. Be sure to enable system assigned managed identity.
Select Save.
Grant storage account access for your Language resource
Important
To assign a system-assigned managed identity role, you need Microsoft.Authorization/roleAssignments/write permissions, such as Owner or User Access Administrator at the storage scope for the storage resource.
Go to the Azure portal and sign in to your Azure account.
Select your Language resource.
In the Resource Management group in the left pane, select Identity.
Under Permissions select Azure role assignments:
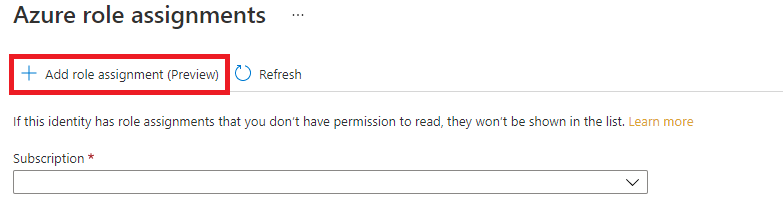
On the Azure role assignments page that opened, choose your subscription from the drop-down menu then select + Add role assignment.
Next, assign a Storage Blob Data Contributor role to your Language service resource. The Storage Blob Data Contributor role gives Language (represented by the system-assigned managed identity) read, write, and delete access to the blob container and data. In the Add role assignment pop-up window, complete the fields as follows and select Save:
Field Value Scope Storage. Subscription The subscription associated with your storage resource. Resource The name of your storage resource. Role Storage Blob Data Contributor. 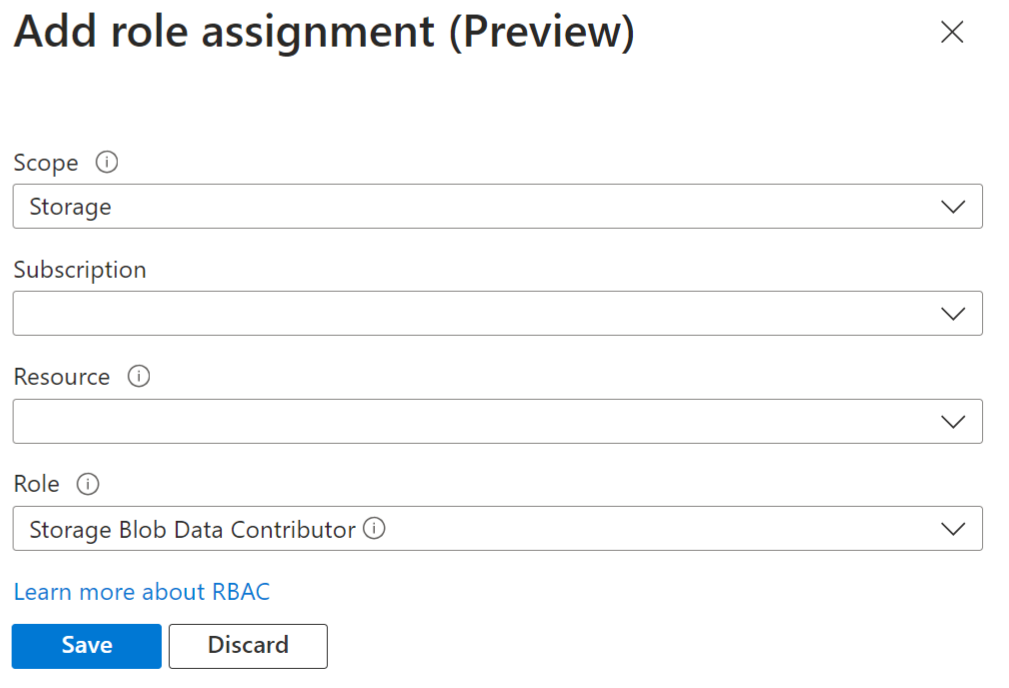
After the Added Role assignment confirmation message appears, refresh the page to see the added role assignment.
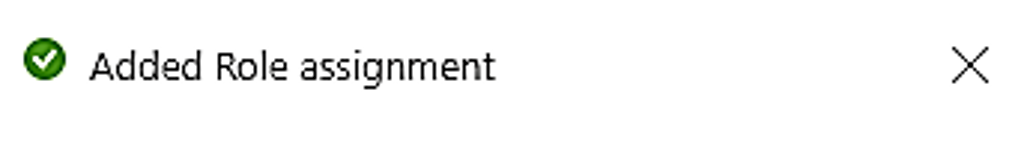
If you don't see the new role assignment right away, wait and try refreshing the page again. When you assign or remove role assignments, it can take up to 30 minutes for changes to take effect.
HTTP requests
A native document Language service operation request is submitted to your Language service endpoint via a POST request.
With managed identity and
Azure RBAC, you no longer need to include SAS URLs.If successful, the POST method returns a
202 Acceptedresponse code and the service creates a request.The processed documents appear in your target container.
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for