Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
You can deploy local apps to Azure App Service by using local Git deployment or FTP/S deployment. This article explains how to create and manage deployment credentials for local Git or FTP/S deployment.
Deployment credentials are different from your Azure subscription credentials. App Service supports two types of credentials for secure local app deployment: user-scope and app-scope credentials.
User-scope or user-level credentials provide one set of deployment credentials for a user's entire Azure account. A user who is granted app access via role-based access control (RBAC) or coadministrator permissions can use their user-level credentials as long as they have those permissions.
You can use your user-scope credentials to deploy any app to App Service via local Git or FTP/S in any subscription that your Azure account has permission to access. You don't share these credentials with any other Azure users. You can reset your user-scope credentials anytime.
App-scope or application-level credentials are one set of credentials per app that can be used to deploy that app only. These credentials are generated automatically for each app at creation and can't be configured manually, but the password can be reset anytime.
A user must have at least Contributor level permissions on an app, including the built-in Website Contributor role, to be granted access to app-level credentials via RBAC. Reader role can't publish and can't access these credentials.
Prerequisites
To set, reset, access, or use deployment credentials, you must have Contributor-level permissions on the App Service app.
Basic authentication requirement
To publish App Service apps via local Git or FTP/S, you must enable basic authentication. SCM Basic Auth Publishing Credentials and FTP Basic Auth Publishing Credentials must both be set to On on the app's Configuration page in the Azure portal.
Basic authentication is less secure than other authentication methods and is disabled by default for new apps. If basic authentication is disabled, you can't view or set deployment credentials in the app's Deployment Center or use these credentials for publishing. For more information, see Disable basic authentication in Azure App Service deployments.
Set user-scope credentials
For FTP/S deployment, you need both a user name and a password. Local Git deployment requires only a user name. The user name must be unique within Azure.
For local Git deployment, the user name can't contain the @ character.
For FTP/S deployment:
The user name must follow the format
<app-name>\<user-name>. Since user-scope credentials are linked to the user and not to the app, this format directs the sign-in action to the correct FTP/S endpoint for the app.The password must be at least eight characters and contain capital letters, lowercase letters, numbers, and symbols. The Azure portal doesn't show the user-scope password, and the JSON output shows it as
null. If you lose or forget your password, you can reset your credentials to get a new one.
You can configure user-scope credentials by using Azure CLI or the Azure portal.
To create user-scope credentials using Azure CLI, run the az webapp deployment user set command, replacing <username> and <password> with values you select.
az webapp deployment user set --user-name <username> --password <password>
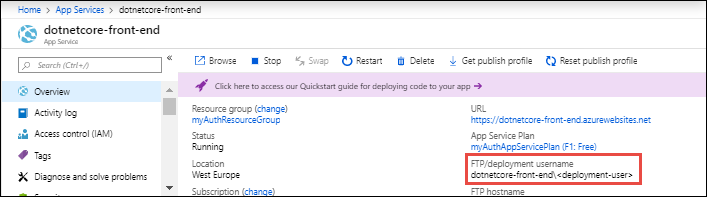
After you set user-scope credentials, you can see your deployment user name on your app's Overview page in the Azure portal. If local Git deployment is configured, the label is Git/Deployment username. Otherwise, the label is FTP/Deployment username.
Get application-scope credentials
The application-scope credentials are automatically created at app creation. The FTP/S app-scope user name always follows the format app-name\$app-name. The local Git app-scope user name uses the format $app-name.
Note
When you use git remote add in shells that use the dollar sign for variable interpolation, such as Bash, you must use \$ to escape any dollar signs in the username or password to avoid authentication errors.
You can get your app-scope credentials by using Azure CLI, Azure PowerShell, or the Azure portal.
In Azure CLI, get the application-scope credentials by using the az webapp deployment list-publishing-profiles command. For example:
az webapp deployment list-publishing-profiles --resource-group myResourceGroup --name myApp
For local Git deployment, you can also use the az webapp deployment list-publishing-credentials command. The following example returns a Git remote URI that has the application-scope credentials for the app already embedded.
az webapp deployment list-publishing-credentials --resource-group myResourceGroup --name myApp --query scmUri
The returned Git remote URI doesn't have /<app-name>.git at the end. If you use the URI to add a remote, append /<app-name>.git to the URI to avoid an error 22 with git-http-push.
Reset credentials
You can use Azure CLI, Azure PowerShell, or the Azure portal to reset your application-scope deployment credentials and get a new password. The app-scope user names retain their autogenerated values.
In Azure CLI and the Azure portal, you can also reset your user-scope credentials by creating new ones. This action affects all the apps in your account that use the user-scope credentials.
When you reset your deployment credentials, any external integrations and automation via the publishing profile stop working and must be reconfigured with the new values.
In Azure CLI, reset the application-scope password by using the az resource invoke-action command with the newpassword action.
az resource invoke-action --action newpassword --resource-group <group-name> --name <app-name> --resource-type Microsoft.Web/sites
Reset the user-scope credentials by rerunning the az webapp deployment user set command to create new user name and password values.
az webapp deployment user set --user-name <new-username> --password <new-password>