Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Organizations that use an internal or nonintegrated certificate authority (CA) often rely on manual processes to renew Transport Layer Security (TLS) and Secure Sockets Layer (SSL) certificates. Manual renewal can lead to expired certificates that cause service outages, like when a web server certificate expires unnoticed and disrupts customer-facing applications.
Azure Key Vault supports automatic certificate renewal for integrated CAs like DigiCert or GlobalSign, but nonintegrated CAs require a manual approach. This article presents an architecture that automates certificate renewal for nonintegrated CAs by using Key Vault, Azure Event Grid, Azure Automation, and the Key Vault extension. The solution reduces human error, minimizes service interruptions, and enforces principle of least privilege across all identities in the renewal process.
Architecture
This section provides an overview of the underlying architecture that supports this solution.
Download a Visio file of this architecture.
The Azure environment comprises the following platform as a service (PaaS) resources:
A key vault that stores only certificates issued by the same nonintegrated CA
An Event Grid system topic
A storage account queue
An Automation account that exposes a webhook that Event Grid targets
To monitor the process and status of expired and expiring certificates, Log Analytics stores the data, and the workspace presents it in the form of tabular and graphical dashboards.
This scenario assumes that an existing public key infrastructure (PKI) is already in place and consists of a Microsoft Enterprise CA joined to an Active Directory domain. The PKI, the Active Directory domain, and the servers that require certificate renewal can reside on Azure or on‑premises environments.
You don't need to join the virtual machines (VMs) that host certificates to monitor for renewal to Active Directory or to Microsoft Entra ID. You only need to join the CA and the hybrid worker, if it's located on a different VM than the CA, to Active Directory.
The following sections provide details about the automatic renewal process.
Workflow
The following diagram shows the automatic workflow for certificate renewal within the Azure ecosystem.
Download a Visio file of this workflow.
The following workflow corresponds to the previous diagram:
Key Vault configuration: The initial phase of the renewal process entails storing the certificate object in the designated certificates section of the key vault.
We recommend that you use certificate tags to configure custom email notifications by tagging each certificate with the recipient's email address. This approach lets you notify specific admins for each certificate rather than applying the same recipient to all certificates. Use the Recipient tag and set its value to one or more email addresses separated by a comma or semicolon. Tag-based notifications ensure timely alerts when the certificate renewal completes on the internal CA and when the renewed certificate becomes available in Key Vault.
You can use built-in Key Vault certificate notifications in combination with this approach, but they serve a different purpose. Built-in notifications apply globally to all certificates in the key vault and are limited to upcoming certificate expiration alerts. They use the same recipient for all certificates.
Key Vault extension configuration: You must equip the servers that need to use the certificates with the Key Vault extension. The extension is compatible with Windows and Linux systems. It supports Azure infrastructure as a service (IaaS) servers and on-premises or other cloud servers that integrate through Azure Arc. Configure the Key Vault extension to periodically poll Key Vault for any updated certificates. The polling interval is customizable and flexible, so it can align with specific operational requirements.
Note
On some Linux distributions or hardened enterprise images, the Key Vault extension might not be available or supported. In these cases, schedule the script_for_not_supported_ARC_on_Linux_distro script as a recommended fallback. The script periodically checks Key Vault for certificate updates and applies them to the server. It can run on Azure native VMs (IaaS) and on-premises servers integrated with Azure Arc.
Event Grid integration: As a certificate nears expiration, two Event Grid subscriptions intercept this important lifetime event from the key vault.
Event Grid triggers: One Event Grid subscription sends certificate renewal information to a storage account queue. The other subscription triggers the launch of a runbook through the configured webhook in the Automation account. If the runbook fails to renew the certificate, or if the CA is unavailable, a scheduled process retries renewing the runbook from that point until the queue clears. This process makes the solution robust.
To enhance the solution's resiliency, set up a dead-letter location mechanism. It manages potential errors that might occur during message transit from Event Grid to the subscription targets, the storage queue, and the webhook.
Storage account queue: The runbook launches within the CA server configured as an Automation Hybrid Runbook Worker. It receives all messages in the storage account queue that contain the name of the expiring certificate and the key vault that hosts the runbook. The following steps occur for each message in the queue.
Certificate renewal: The script in the runbook connects to Azure to retrieve the certificate's template name that you set up during generation. The template is the configuration component of the CA that defines the attributes and purpose of the certificates that it generates.
After the script interfaces with Key Vault, it initiates a certificate renewal request. This request triggers Key Vault to generate a certificate signing request (CSR) and applies the same template that generated the original certificate. This process ensures that the renewed certificate aligns with the predefined security policies. For more information about security in the authentication and authorization process, see Security.
The script downloads the CSR and submits it to the CA.
The CA generates a new x509 certificate based on the correct template and sends it back to the script. This step ensures that the renewed certificate aligns with the predefined security policies.
Certificate merging and Key Vault update: The script merges the renewed certificate back into the key vault. This step finalizes the update process and removes the message from the queue. Throughout the entire process, the private key of the certificate is never extracted from the key vault.
Monitoring and email notification: All logs related to operations that run across various Azure components, including the Automation account, Key Vault, the storage account queue, and Event Grid, should be sent to the Azure Monitor Logs workspace. After the certificate merges into the key vault, the script sends an email message to administrators to notify them of the outcome.
Certificate retrieval: The Key Vault extension on the server plays an important role during this phase. It automatically downloads the latest version of the certificate from the key vault into the local store of the server that uses the certificate. You can configure multiple servers with the Key Vault extension to retrieve the same certificate from the key vault, including wildcard or with multiple Subject Alternative Name (SAN) certificates.
For Linux distributions in which you can't install the Key Vault extension, schedule the script_for_not_supported_ARC_on_Linux_distro script to achieve the same functionality as the extension.
Components
This solution uses various components to handle automatic certificate renewal on Azure. The following sections describe each component and its specific purpose.
Key Vault extension
The Key Vault extension is a tool installed on servers that provides automatic refresh of certificates stored in an Azure key vault. In this architecture, you must install the Key Vault extension on servers that require automatic certificate renewal. For more information about installation procedures for various servers, see the following articles:
- Key Vault extension for Windows
- Key Vault extension for Linux
- Key Vault extension for Azure Arc-enabled servers
Note
The following scripts are samples that you can run from Azure Cloud Shell to configure the Key Vault extension:
The Key Vault extension configuration parameters include:
Key Vault Name: The key vault that contains the certificate for renewal.
Certificate Name: The name of the certificate to renew.
Certificate Store, Name, and Location: The certificate store where the certificate is stored. On Windows servers, the default value for Name is
Myand Location isLocalMachine, which is the personal certificate store of the computer. On Linux servers, you can specify a file system path, assuming that the default value isAzureKeyVault, which is the certificate store for Key Vault.linkOnRenewal: A flag that indicates whether the certificate should be linked to the server on renewal. If the flag is set to
trueon Windows machines, it copies the new certificate in the store and links it to the old certificate, which effectively rebinds the certificate. The default value isfalse, which means that an explicit binding is required.pollingIntervalInS: The polling interval for the Key Vault extension to check for certificate updates. The default value is
3600seconds (1 hour).authenticationSetting: The authentication setting for the Key Vault extension. For Azure servers, you can omit this setting so that the extension uses the VM's system-assigned managed identity to authenticate to the key vault. For on-premises servers, if you specify the setting
msiEndpoint = "http://localhost:40342/metadata/identity", the extension uses the service principal associated with the computer object created during Azure Arc onboarding.
Note
Specify the Key Vault extension parameters only during the initial setup. This approach ensures that the parameters remain unchanged throughout the renewal process.
Automation account
An Automation account is a cloud-based service that automates tasks via runbooks. In this architecture, it handles the certificate renewal process. You need to configure the account with a runbook by using the PowerShell script.
You also need to create a Hybrid Worker Group. Associate the Hybrid Worker Group with a Windows Server member of the same Active Directory domain of the CA, ideally the CA itself, for launching runbooks.
The runbook must have an associated webhook initiated from the Hybrid Runbook Worker. Configure the webhook URL in the event subscription of the Event Grid system topic.
Storage account queue
The storage account queue is a message queue within Azure Storage. In this architecture, it stores the messages that contain the name of the certificate being renewed and the key vault that contains the certificate. Configure the storage account queue in the event subscription of the Event Grid system topic. The queue handles decoupling the script from the certificate expiration notification event. It supports persisting the event within a queue message. This approach helps ensure that the renewal process for certificates is repeated through scheduled jobs even if problems occur during the script's run.
Hybrid Runbook Worker
The Hybrid Runbook Worker is a feature of Automation that you use to run runbooks on machines located in a datacenter. In this architecture, it runs the certificate renewal runbook. Install the Hybrid Runbook Worker by using the Azure Hybrid Worker extension method, which is the supported mode for a new installation. You create the worker and associate it with a Windows Server member in the same Active Directory domain of the CA, ideally the CA itself.
Key Vault
Key Vault is the secure repository for certificates. In this architecture, it stores certificates issued only by the same nonintegrated CA. Under the event section of the key vault, associate the Event Grid system topic with the webhook of the Automation account and a subscription.
Event Grid
Event Grid is an event-routing service. In this architecture, it handles event-driven communication within Azure. Configure Event Grid by setting up the system topic and event subscription to monitor relevant events. Relevant events include certificate expiration alerts, actions triggered within the automation workflow, and messages posted in the storage account queue. Configure the Event Grid system topic by using the following parameters:
Source: The name of the key vault that contains the certificates.
Source Type: The type of the source. For example, the source type for this solution is
Azure Key Vault.Event Type: The event type to monitor. For example, the event type for this solution is
Microsoft.KeyVault.CertificateNearExpiry. This event triggers when a certificate is near expiration.Subscription for Webhook:
Subscription Name: The name of the event subscription.
Endpoint Type: The type of endpoint to use. For example, the endpoint type for this solution is
Webhook.Endpoint: The URL of the webhook associated with the Automation account runbook. For more information, see Automation account.
Subscription for StorageQueue:
Subscription Name: The name of the event subscription.
Endpoint Type: The type of endpoint to use. For example, the endpoint type for this solution is
StorageQueue.Endpoint: The storage account queue.
Log Analytics workspace and Azure workbook
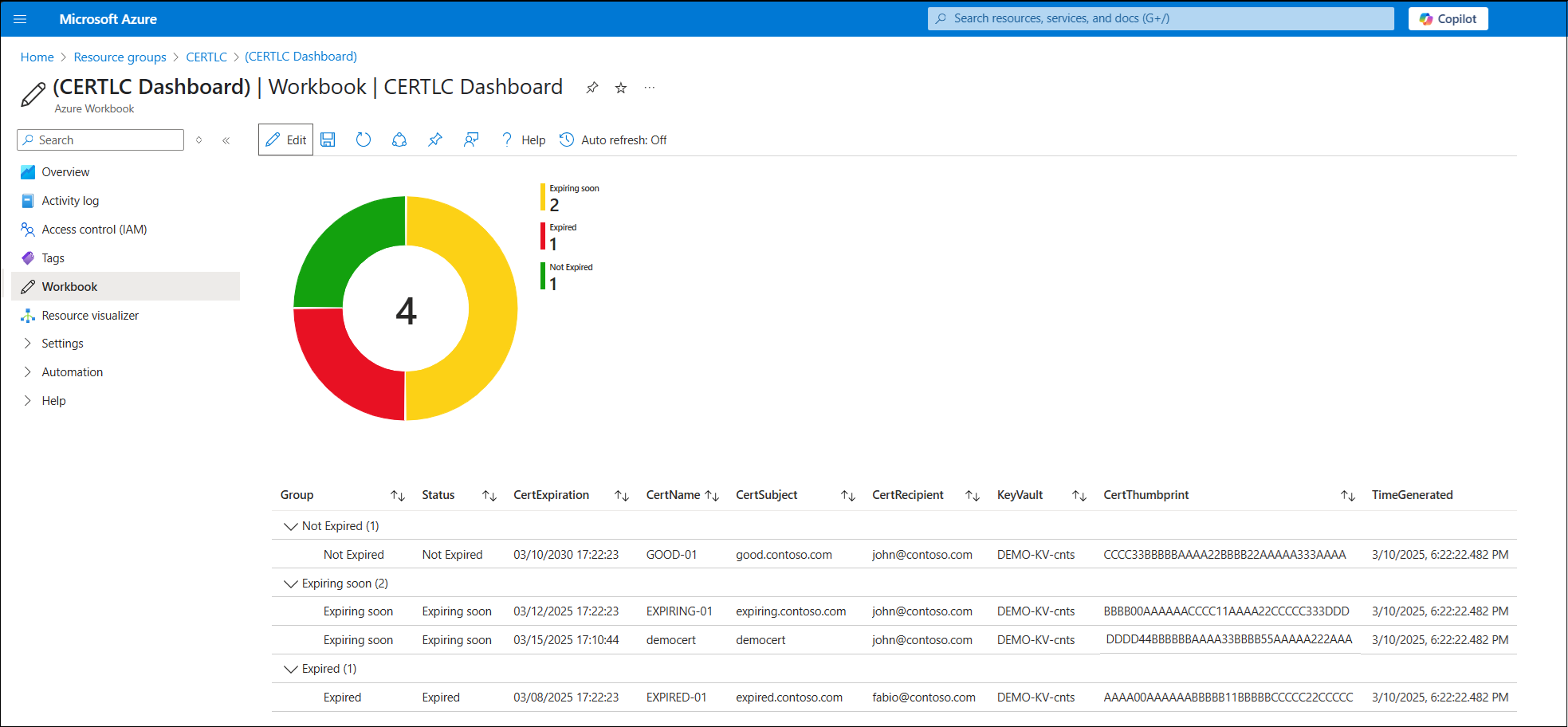
Log Analytics workspaces and Azure workbooks are Azure resources that collect, aggregate, and analyze data. In this architecture, they enhance monitoring and visualization of certificate statuses stored in Key Vault. These components are crucial for maintaining visibility into certificate health:
Log Analytics workspace: Collects and stores data about certificate states. It identifies expired certificates, certificates that expire soon, and valid certificates.
Azure workbook: Retrieves data from the Log Analytics workspace and presents it in a dashboard with visual representations, such as pie charts and detailed tables. It categorizes certificates into Not Expired (green), Expiring Soon (yellow), and Expired (red).
The following components retrieve and present certificate information in the workbook:
Data ingestion runbook execution: A runbook runs directly from Azure, without requiring the context of a Hybrid Worker. The runbook retrieves certificate data from the key vault and sends it to a custom table defined in the Log Analytics workspace. The runbook runs on a scheduled cadence.
Workbook visualization: A workbook queries the data from the custom table and displays it in both a pie chart and a detailed table. It highlights certificates based on their expiration status.
By integrating these extra components, your solution builds a more comprehensive approach to certificate life cycle management.
Alternatives
This solution uses an Automation account to orchestrate the certificate renewal process. It also uses Hybrid Runbook Worker to provide the flexibility to integrate with a CA on-premises or in other clouds.
An alternative approach is to use Azure Logic Apps. The main difference between the two approaches is that the Automation account is a PaaS solution, and Logic Apps is a software as a service (SaaS) solution.
Logic Apps is a fully managed service, so you don't need to manage the underlying infrastructure. It can also integrate with external connectors. This capability expands the range of notification options, such as engagement with Microsoft Teams or Microsoft 365.
Logic Apps doesn't have a feature similar to Hybrid Runbook Worker, which results in less flexible integration with the CA, so an Automation account is the preferred approach.
Scenario details
Every organization requires secure and efficient management of their certificate life cycle. Failing to update a certificate before expiration can lead to service interruptions and incur significant costs for the business.
Enterprises typically operate complex IT infrastructures that involve multiple teams who are responsible for the certificate life cycle. The manual nature of the certificate renewal process often introduces errors and consumes valuable time.
This solution addresses these challenges by automating certificate renewal issued by Microsoft Certificate Service. The service is widely used for various server applications, such as web servers and SQL servers, and for encryption, nonrepudiation, signing purposes, and ensuring timely updates and secure certificate storage within Key Vault. The service's compatibility with Azure servers and on-premises servers supports flexible deployment.
Potential use cases
This solution caters to organizations across various industries that:
Use Microsoft Certificate Service for server certificate generation.
Require automation in the certificate renewal process to accelerate operations and minimize errors, which helps avoid business loss and service-level agreement (SLA) violations.
Require secure certificate storage in repositories like Key Vault.
This architecture serves as a foundational deployment approach across application landing zone subscriptions.
Note
You can extend the same life cycle pattern to Azure App Service, Azure Application Gateway, and Kubernetes workloads that integrate with Key Vault.
Considerations
These considerations implement the pillars of the Azure Well-Architected Framework, which is a set of guiding tenets that you can use to improve the quality of a workload. For more information, see Well-Architected Framework.
Security
Security provides assurances against deliberate attacks and the misuse of your valuable data and systems. For more information, see Design review checklist for Security.
Key Vault securely stores certificates as encrypted secrets protected by Azure role-based access control (Azure RBAC).
Tip
In environments that have strict compliance requirements, such as NIS2 or public-sector regulations, consider evaluating Azure Key Vault Premium for HSM-backed key protection if you need to keep the certificate renewal workflow that this article describes.
Throughout the certificate renewal process, the following components use identities:
The system account of the Hybrid Runbook Worker, which operates under the VM's account
The Key Vault extension, which uses the managed identity associated with the VM
The Automation account, which uses its designated managed identity
Least privilege is rigorously enforced across all identities engaged in the certificate renewal procedure.
The system account of the Hybrid Runbook Worker server must have the right to enroll certificates on one or more certificate templates that generate new certificates.
On the key vault that contains the certificates, the Automation account identity must have the Key Vault Certificate Officer role. Additionally, servers that require certificate access must have Get and List permissions within the Key Vault certificate store.
On the storage account queue, the Automation account identity must have the Storage Queue Data Contributor, Reader and Data Access, and Reader roles.
In scenarios in which the Key Vault extension deploys on an Azure VM, authentication occurs via the VM's managed identity. However, when the extension deploys on an Azure Arc-enabled server, a service principal handles authentication. You must assign the Key Vault secret user role within the key vault that stores the certificate to both the managed identity and the service principal. You must use a secret role because the certificate is stored in the key vault as a secret.
Cost Optimization
Cost Optimization focuses on ways to reduce unnecessary expenses and improve operational efficiencies. For more information, see Design review checklist for Cost Optimization.
This solution uses Azure PaaS solutions that operate under a pay-as-you-go framework to optimize cost. Expenses depend on the number of certificates that need renewal and the number of servers equipped with the Key Vault extension, which results in low overhead.
Expenses that result from the Key Vault extension and the Hybrid Runbook Worker depend on your installation choices and polling intervals. The cost of Event Grid corresponds to the volume of events that Key Vault generates. The cost of the Automation account correlates with the number of runbooks that you use.
The cost of Key Vault depends on various factors, including Standard or Premium SKUs, the quantity of stored certificates, and the frequency of operations conducted on the certificates.
Similar considerations for Key Vault configuration apply to the storage account. In this scenario, a Standard SKU with locally redundant storage replication is sufficient for the storage account. Generally, the cost of the storage account queue is minimal.
To estimate the cost of implementing this solution, use the Azure pricing calculator. Input the services described in this article.
Operational Excellence
Operational Excellence covers the operations processes that deploy an application and keep it running in production. For more information, see Design review checklist for Operational Excellence.
The automatic certificate renewal procedure securely stores certificates by applying standardized processes across all certificates within the key vault.
Integration with Event Grid triggers supplementary actions, such as notifying Microsoft Teams or Microsoft 365 and streamlining the renewal process. This integration significantly reduces certificate renewal time and mitigates the potential for errors that might lead to business disruptions and SLA violations.
Integration with Azure Monitor, Microsoft Sentinel, Microsoft Security Copilot, and Microsoft Defender for Cloud facilitates continuous monitoring of the certificate renewal process. It supports anomaly detection and ensures that robust security measures are maintained. Defender for Cloud contributes primarily through posture management and alert correlation rather than direct certificate renewal event handling.
Deploy this scenario
Select the following button to deploy the environment described in this article. The deployment takes about two minutes to complete and creates a key vault, an Event Grid system topic configured with the two subscriptions, a storage account that contains the CERTLC queue, and an Automation account that contains the runbook and the webhook linked to Event Grid.
For more information about the parameters that you need for the deployment, see the code sample portal.
Important
You can deploy a full lab environment to demonstrate the entire automatic certificate renewal workflow. Use the code sample to deploy the following resources:
Active Directory Domain Services (AD DS) within a domain controller VM.
Active Directory Certificate Services (AD CS) within a CA VM, joined to the domain, configured with a template, WebServerShort, for enrolling the certificates to renew.
A Windows Simple Mail Transfer Protocol (SMTP) server installed on the same VM as the CA for sending email notifications. MailViewer also installs to verify the email notifications sent.
The Key Vault extension installed on the domain controller VM for retrieving the renewed certificates from the Key Vault extension.
Contributors
Microsoft maintains this article. The following contributors wrote this article.
Principal authors:
- Fabio Masciotra | Senior Cloud Solution Architect
- Angelo Mazzucchi | Principal Consultant
To see nonpublic LinkedIn profiles, sign in to LinkedIn.