Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this article, you'll learn how to set up private access for your Azure App Configuration store, by creating a private endpoint with Azure Private Link. Private endpoints allow access to your App Configuration store using a private IP address from a virtual network.
Prerequisites
- An Azure account with an active subscription. Create an account for free.
- We assume you already have an App Configuration store. If you want to create one, go to create an App Configuration store.
Sign in to Azure
You'll need to sign in to Azure first to access the App Configuration service.
Sign in to the Azure portal at https://portal.azure.com/ with your Azure account.
Create a private endpoint
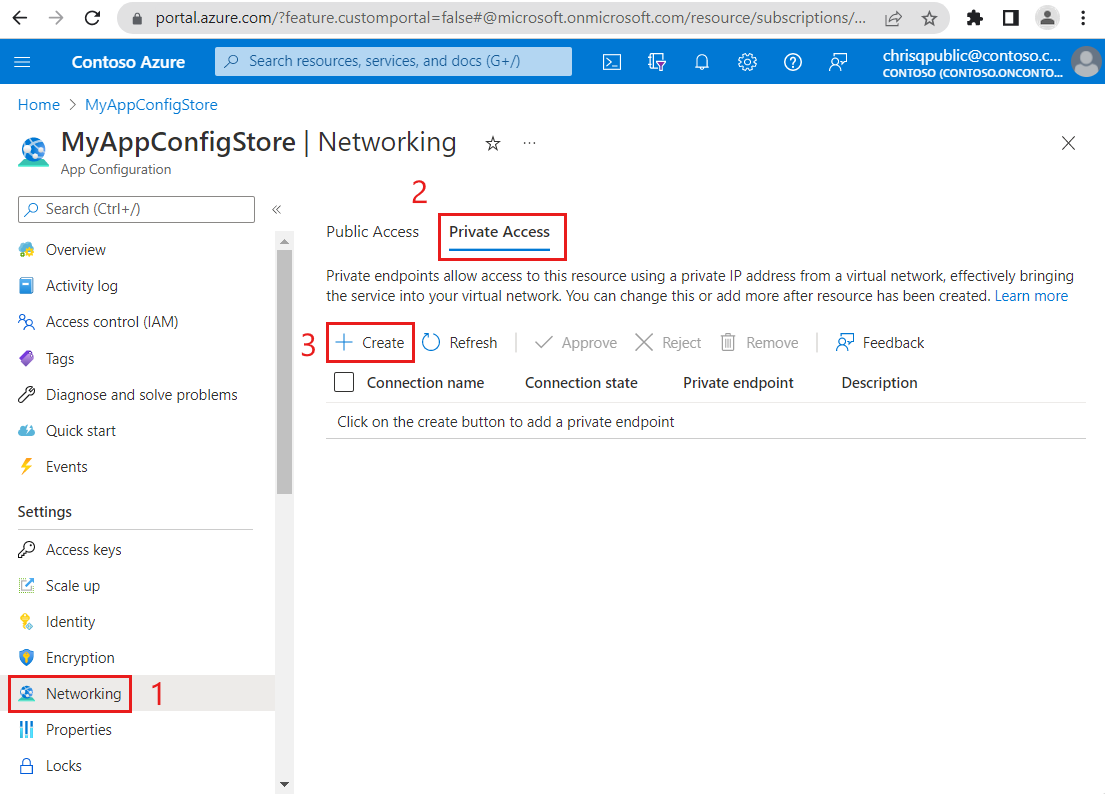
In your App Configuration store, under Settings, select Networking.
Select the Private Access tab and then Create to start setting up a new private endpoint.
Fill out the form with the following information:
Parameter Description Example Subscription Select an Azure subscription. Your private endpoint must be in the same subscription as your virtual network. You'll select a virtual network later in this how-to guide. MyAzureSubscription Resource group Select a resource group or create a new one. MyResourceGroup Name Enter a unique name for the new private endpoint for your App Configuration store. When using the Azure portal, the private endpoint connection name will be the same as the private endpoint name. App Configuration stores must have unique private endpoint connection names. MyPrivateEndpoint Network Interface Name This field is completed automatically. Optionally edit the name of the network interface. MyPrivateEndpoint-nic Region Select a region. Your private endpoint must be in the same region as your virtual network. Central US 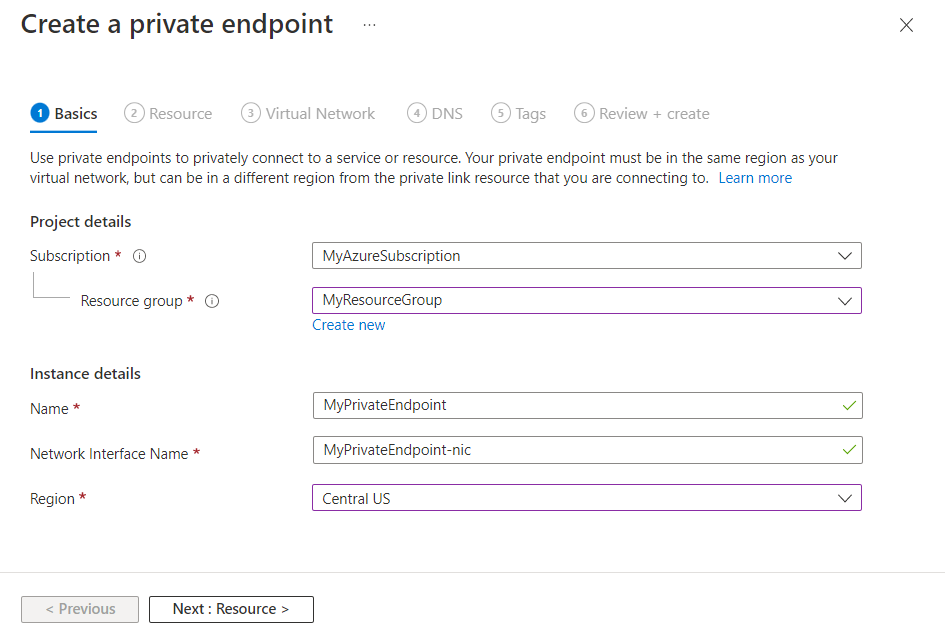
Select Next : Resource >. Private Link offers options to create private endpoints for different types of Azure resources, such as SQL servers, Azure storage accounts or App Configuration stores. The current App Configuration store is automatically filled in the Resource field as that is the resource the private endpoint is connecting to.
The resource type Microsoft.AppConfiguration/configurationStores and the target subresource configurationStores indicate that you're creating an endpoint for an App Configuration store.
The name of your configuration store is listed under Resource.

Select Next : Virtual Network >.
Select an existing Virtual network to deploy the private endpoint to. If you don't have a virtual network, create a virtual network.
Select a Subnet from the list.
Leave the box Enable network policies for all private endpoints in this subnet checked.
Under Private IP configuration, select the option to allocate IP addresses dynamically. For more information, refer to Private IP addresses.
Optionally, you can select or create an Application security group. Application security groups allow you to group virtual machines and define network security policies based on those groups.

Select Next : DNS > to configure a DNS record. If you don't want to make changes to the default settings, you can move forward to the next tab.
For Integrate with private DNS zone, select Yes to integrate your private endpoint with a private DNS zone. You may also use your own DNS servers or create DNS records using the host files on your virtual machines.
A subscription and resource group for your private DNS zone are preselected. You can change them optionally.
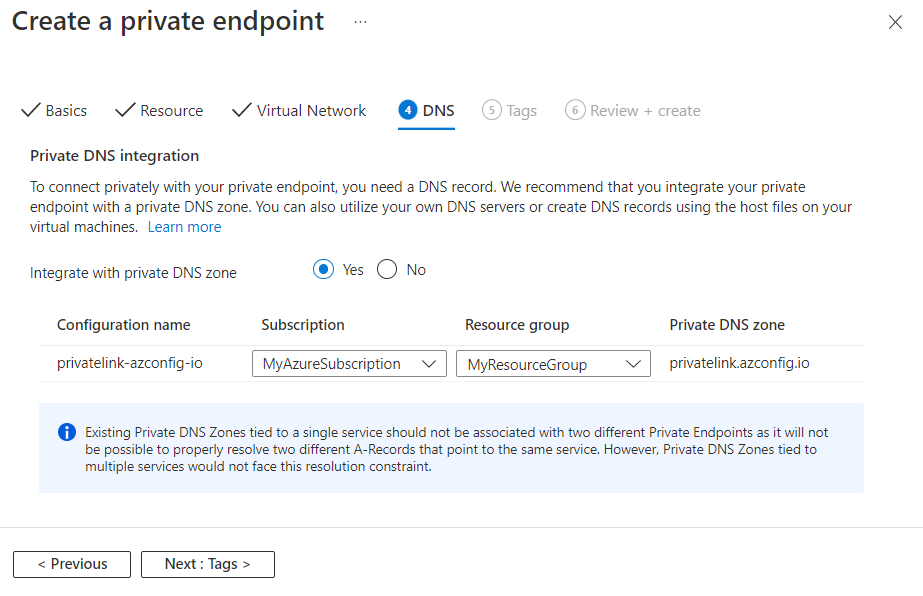
To learn more about DNS configuration, go to Name resolution for resources in Azure virtual networks and DNS configuration for Private Endpoints.
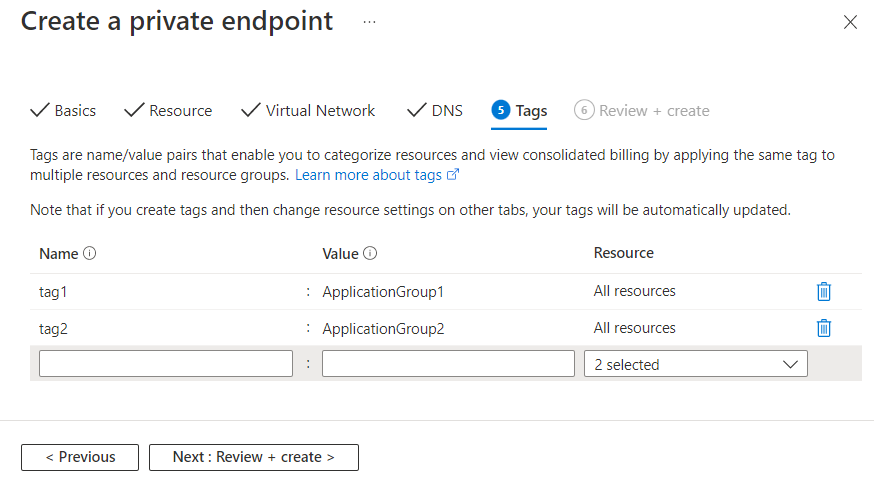
Select Next : Tags > and optionally create tags. Tags are name/value pairs that enable you to categorize resources and view consolidated billing by applying the same tag to multiple resources and resource groups.
Select Next : Review + create > to review information about your App Configuration store, private endpoint, virtual network and DNS. You can also select Download a template for automation to reuse JSON data from this form later.
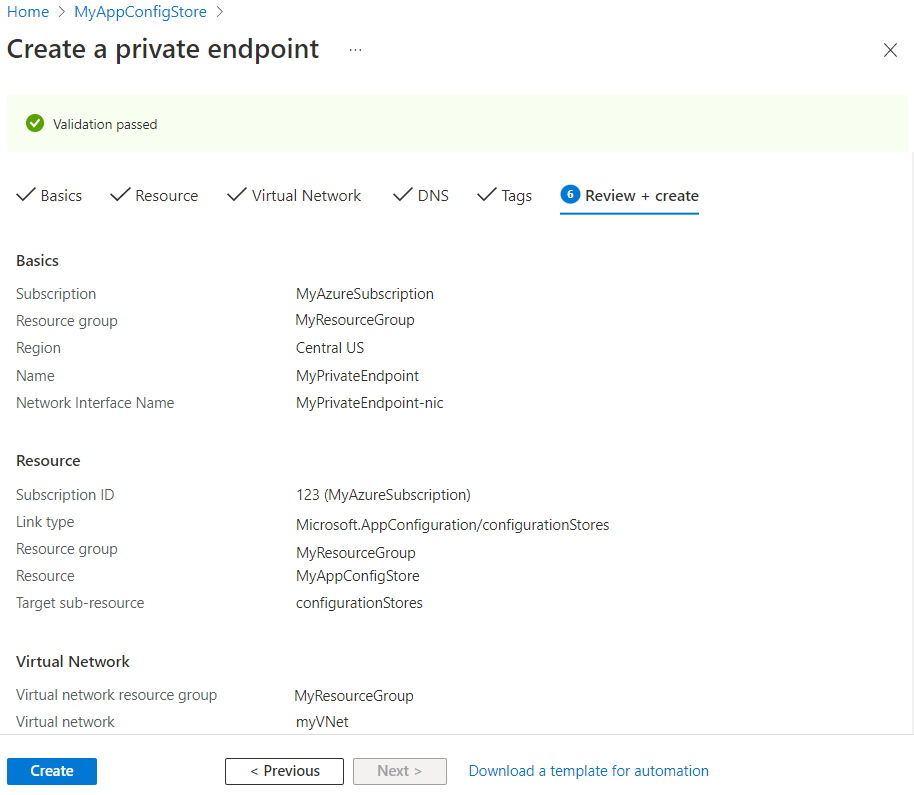
Select Create.
Once deployment is complete, you'll get a notification that your endpoint has been created. If it's auto-approved, you can start accessing your app configuration store privately, else you'll have to wait for approval.
Manage private link connection
Go to Networking > Private Access in your App Configuration store to access the private endpoints linked to your App Configuration store.
Check the connection state of your private link connection. When you create a private endpoint, the connection must be approved. If the resource for which you're creating a private endpoint is in your directory and you have sufficient permissions, the connection request will be auto-approved. Otherwise, you must wait for the owner of that resource to approve your connection request. For more information about the connection approval models, go to Manage Azure Private Endpoints.
To manually approve, reject or remove a connection, select the checkbox next to the endpoint you want to edit and select an action item from the top menu.
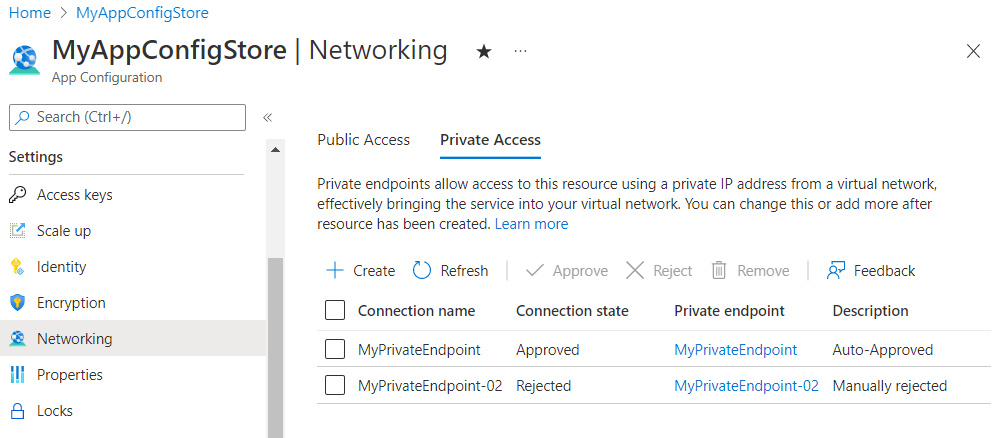
Select the name of the private endpoint to open the private endpoint resource and access more information or to edit the private endpoint.
If you have issues with a private endpoint, check the following guide: Troubleshoot Azure Private Endpoint connectivity problems.