Deploy STIG-compliant Windows Virtual Machines (Preview)
Microsoft Azure Security Technical Implementation Guides (STIGs) solution templates help you accelerate your DoD STIG compliance by delivering an automated solution to deploy virtual machines and apply STIGs through the Azure portal.
This quickstart shows how to deploy a STIG-compliant Windows virtual machine (Preview) on Azure or Azure Government using the corresponding portal.
Prerequisites
- Azure or Azure Government subscription
- Storage account
- If desired, must be in the same resource group/region as the VM
- Required if you plan to store Log Analytics diagnostics
- Log Analytics workspace (required if you plan to store diagnostic logs)
Sign in to Azure
Sign in at the Azure portal or Azure Government portal depending on your subscription.
Create a STIG-compliant virtual machine
Select Create a resource.
Type Azure STIG Templates for Windows in the search bar and press enter.
Select Azure STIG Templates for Windows from the search results and then Create.
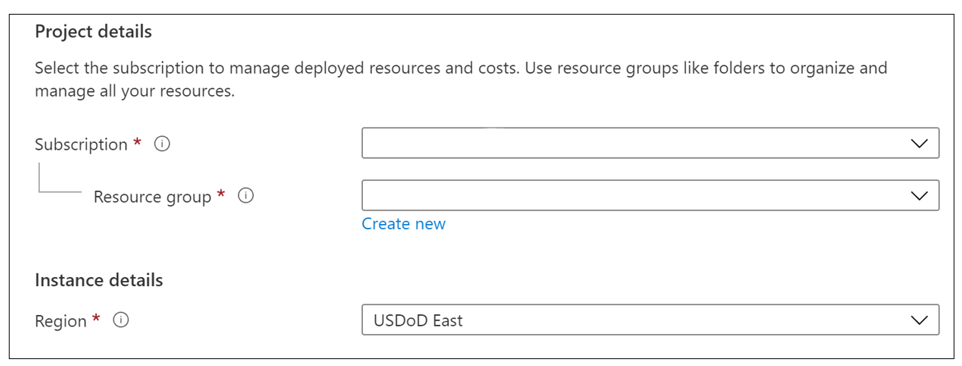
In the Basics tab, under Project details:
a. Select an existing Subscription.
b. Create a new Resource group or enter an existing resource group.
c. Select your Region.
Important
Make sure to choose an empty resource group or create a new one.
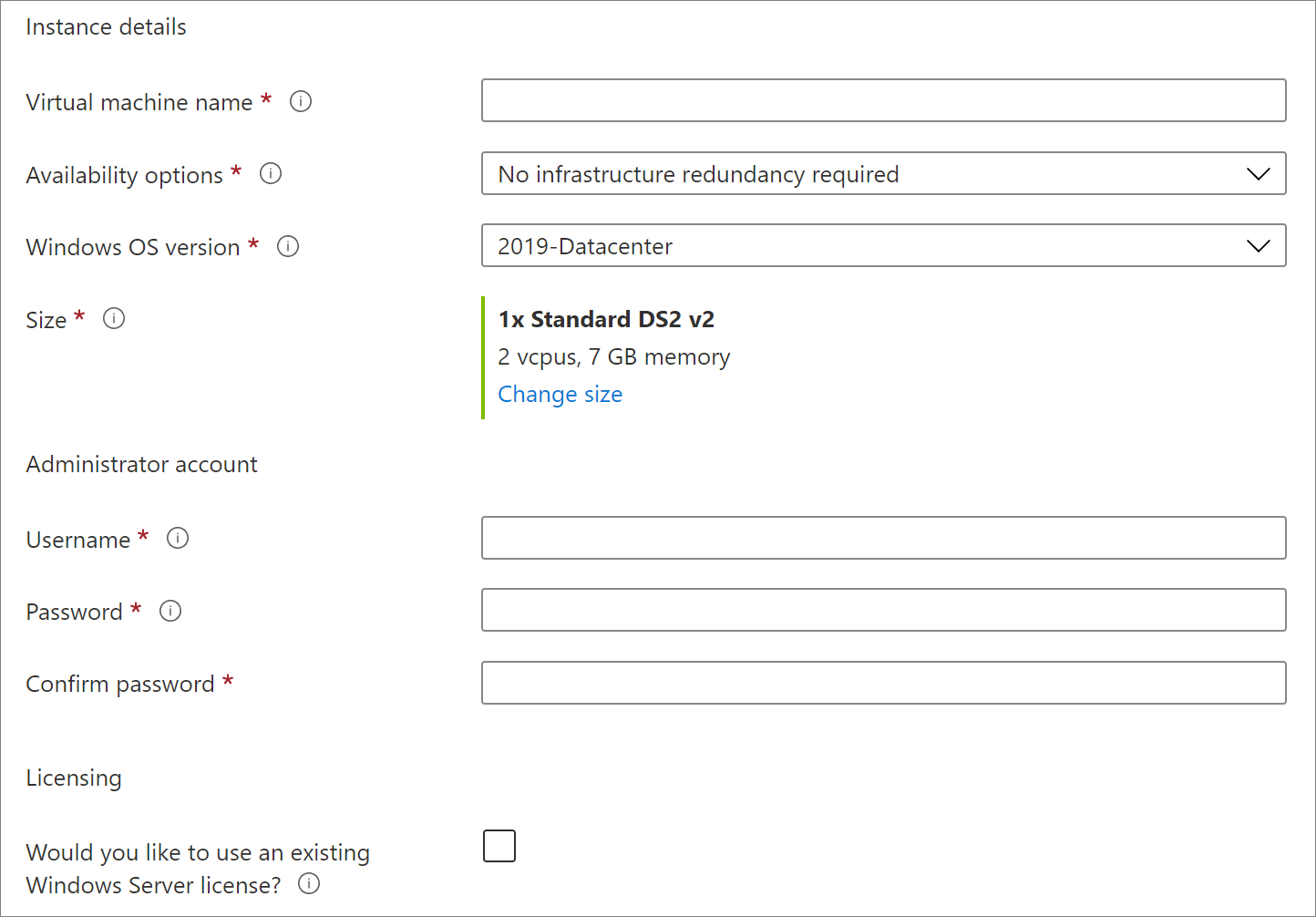
Under Instance details, enter all required information:
a. Enter the VM name.
b. Select the Availability options. To learn about availability sets, see Availability sets overview.
c. Select the Windows OS version.
d. Select the instance Size.
e. Enter the administrator account Username.
f. Enter the administrator account Password.
g. Confirm Password.
h. Check if using an existing Windows Server license.
Under Disk:
a. Select the OS disk type.
b. Select the Encryption type.

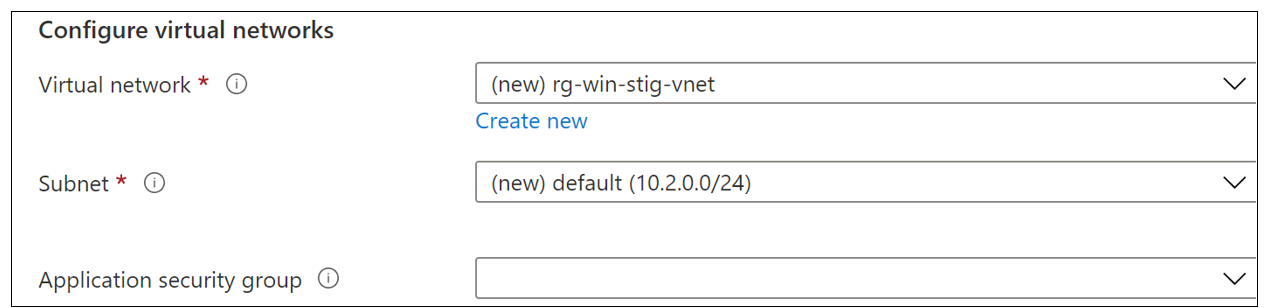
Under Networking:
a. Select the Virtual Network. Either use existing virtual network or select Create new (note RDP inbound is disallowed).
b. Select Subnet.
c. Application security group (optional).
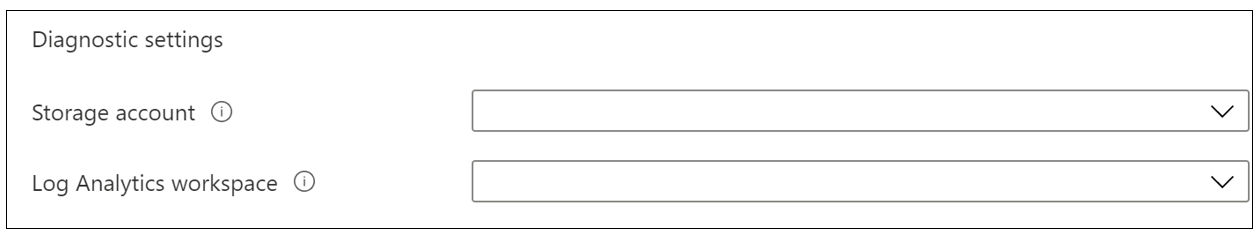
Under Management:
a. For Diagnostic settings select Storage account (optional, required to store diagnostic logs).
b. Enter Log Analytics workspace (optional, required to store log analytics).
Select Review + create to review summary of all selections.
Once the validation check is successful select Create.
Once the creation process is started, the Deployment process page will be displayed:
a. Deployment Overview tab displays the deployment process including any errors that may occur. Once deployment is complete, this tab provides information on the deployment and provides the opportunity to download the deployment details.
b. Inputs tab provides a list of the inputs to the deployment.
c. Outputs tab provides information on any deployment outputs.
d. Template tab provides downloadable access to the JSON scripts used in the template.
The deployed virtual machine can be found in the resource group used for the deployment. Since inbound RDP is disallowed, Azure Bastion must be used to connect to the VM.
High availability and resiliency
Our solution template creates a single instance virtual machine using premium or standard operating system disk, which supports SLA for Virtual Machines.
We recommend you deploy multiple instances of virtual machines configured behind Azure Load Balancer and/or Azure Traffic Manager for higher availability and resiliency.
Business continuity and disaster recovery (BCDR)
As an organization you need to adopt a business continuity and disaster recovery (BCDR) strategy that keeps your data safe, and your apps and workloads online, when planned and unplanned outages occur.
Azure Site Recovery helps ensure business continuity by keeping business apps and workloads running during outages. Site Recovery replicates workloads running on physical and virtual machines from a primary site to a secondary location. When an outage occurs at your primary site, you fail over to secondary location, and access apps from there. After the primary location is running again, you can fail back to it.
Site Recovery can manage replication for:
- Azure VMs replicating between Azure regions.
- On-premises VMs, Azure Stack VMs, and physical servers.
To learn more about backup and restore options for virtual machines in Azure, continue to Overview of backup options for VMs.
Clean up resources
When no longer needed, you can delete the resource group, virtual machine, and all related resources.
Select the resource group for the virtual machine, then select Delete. Confirm the name of the resource group to finish deleting the resources.
Support
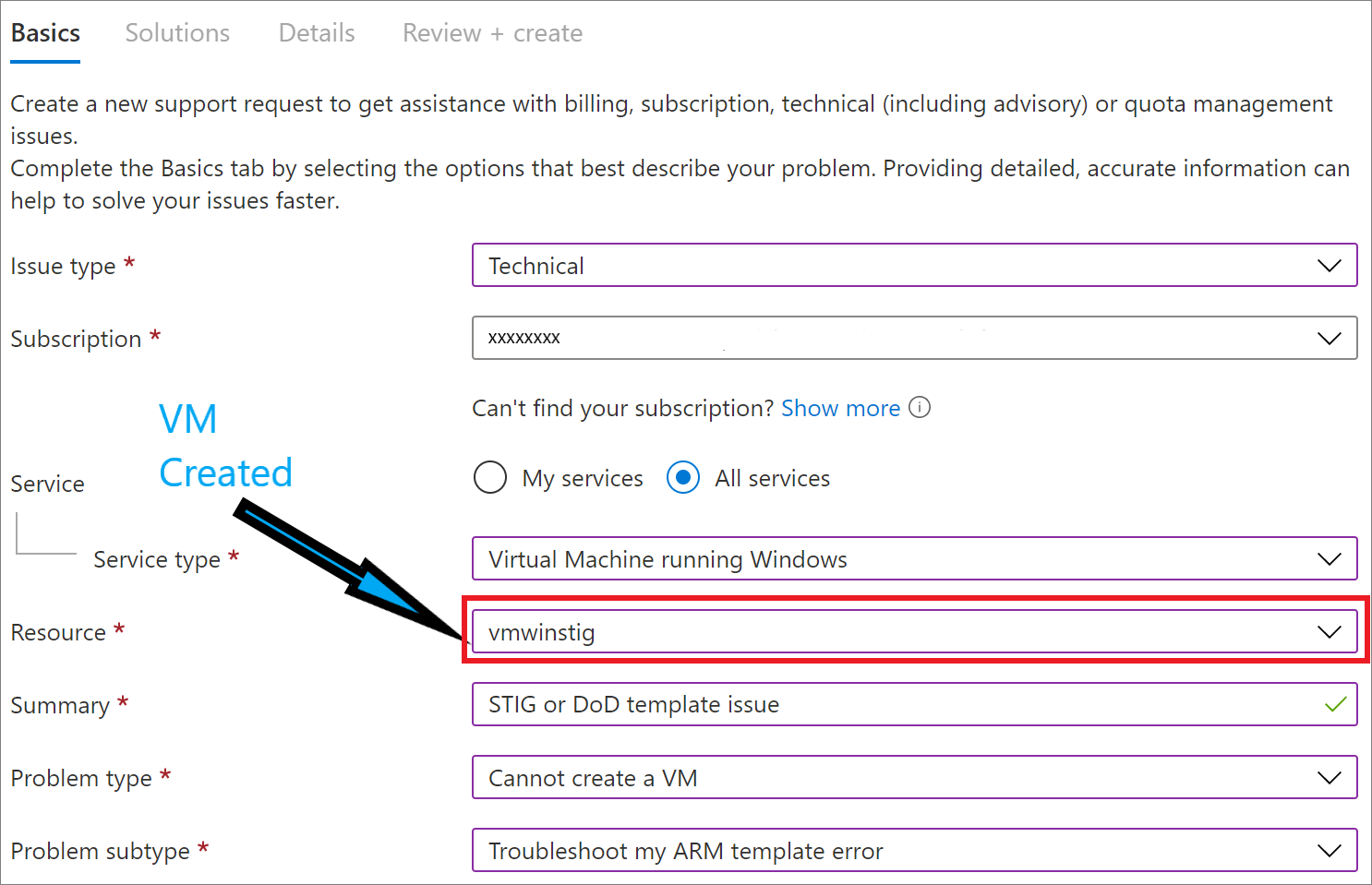
Contact Azure support to get assistance with issues related to STIG solution templates. You can create and manage support requests in the Azure portal. For more information see, Create an Azure support request. Use the following support paths when creating a ticket:
Azure -> Virtual Machine running Windows -> Cannot create a VM -> Troubleshoot my ARM template error
Frequently asked questions
When will STIG-compliant VMs reach general availability (GA)?
The Azure STIG-compliant VM offering is expected to remain in Preview instead of reaching GA because of the release cadence for DISA STIGs. Every quarter, the offering is upgraded with latest guidance, and this process is expected to continue in the future. See previous section for support options that most customers require for production workloads, including creating support tickets.
Can Azure Update Management be used with STIG images?
Yes, Update Management in Azure Automation supports STIG images.
What STIG settings are being applied by the template?
For more information, see Deploy Azure Virtual Machine (Windows) and apply STIG.
Next steps
This quickstart showed you how to deploy a STIG-compliant Windows virtual machine (Preview) on Azure or Azure Government. For more information about creating virtual machines in:
- Azure, see Quickstart: Create a Windows virtual machine in the Azure portal.
- Azure Government, see Tutorial: Create virtual machines.
To learn more about Azure services, continue to the Azure documentation.
For more information about Azure Government, see the following resources:
- Azure Government overview
- Compare Azure Government and global Azure
- Azure Government security
- Azure Government compliance
- Azure Government services by audit scope
- Azure Government DoD overview
- FedRAMP – Azure compliance
- DoD Impact Level 5 – Azure compliance
- Isolation guidelines for Impact Level 5 workloads
- Secure Azure Computing Architecture
- Security Technical Implementation Guides (STIGs)
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for