Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
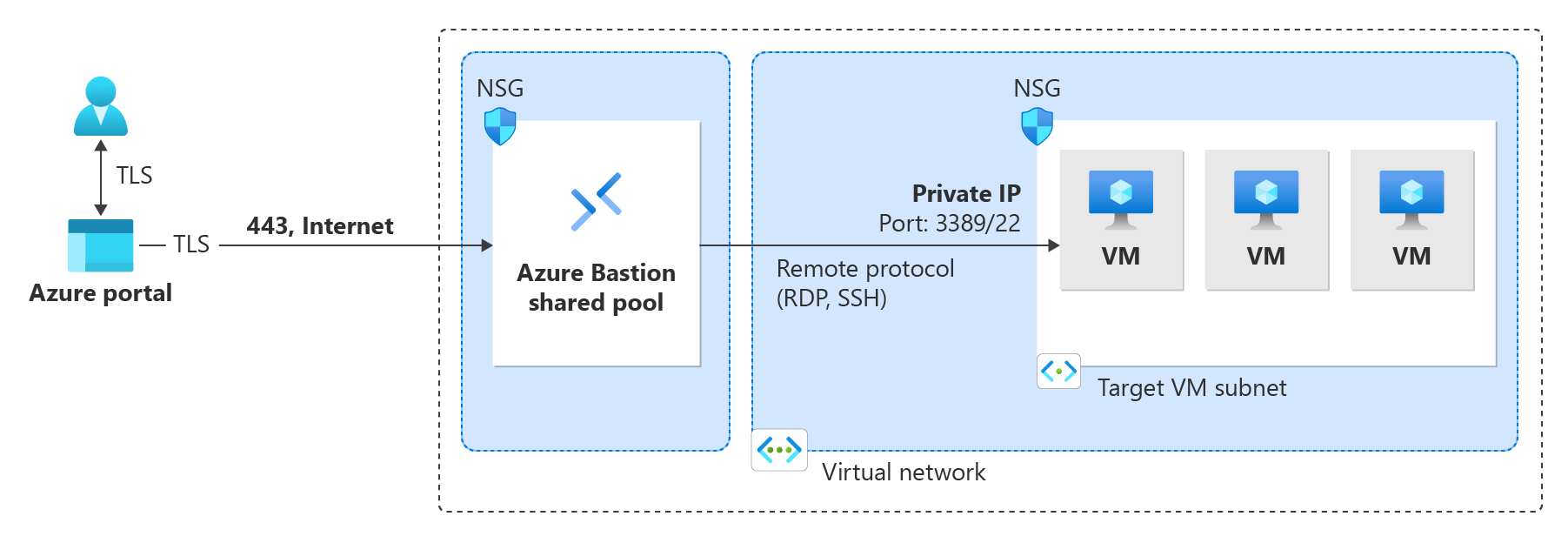
In this quickstart, you learn how to deploy Azure Bastion to your virtual network from the Azure portal. You can deploy Bastion with default settings for a quick setup, configure custom settings to specify the SKU and scaling options, or use the free Developer SKU for basic connectivity. After you deploy Bastion, you can use SSH or RDP to connect to virtual machines (VMs) in the virtual network via Bastion by using the private IP addresses of the VMs. The VMs that you connect to don't need a public IP address, client software, an agent, or a special configuration. For more information about Bastion, see What is Azure Bastion?
The steps in this article help you:
- Deploy Bastion to your virtual network by using the Azure portal.
- Connect to your VM via the portal by using SSH or RDP connectivity and the VM's private IP address.
- Remove your VM's public IP address if you don't need it for anything else.
Important
Hourly pricing starts from the moment that Bastion is deployed, regardless of outbound data usage. For more information, see Pricing and SKUs. If you're deploying Bastion as part of a tutorial or test, we recommend that you delete this resource after you finish using it.
Prerequisites
To complete this quickstart, you need these resources:
An Azure subscription. If you don't already have one, you can activate your MSDN subscriber benefits or sign up for a free account.
A virtual network to which you'll deploy Bastion.
A virtual machine in the virtual network. This VM isn't part of the Bastion configuration and doesn't become a bastion host. You connect to this VM later in the exercise. If you don't have a VM, create one by using Quickstart: Create a Windows VM or Quickstart: Create a Linux VM.
Required VM roles:
- Reader role on the virtual machine
- Reader role on the network adapter (NIC) with the private IP of the virtual machine
Required VM inbound ports:
- For Windows VMs: RDP (3389)
- For Linux VMs: SSH (22)
For Developer SKU only: The VM must be in a region that supports Bastion Developer.
Note
The use of Azure Bastion with Azure Private DNS zones is supported. However, there are restrictions. For more information, see the Azure Bastion FAQ.
Deploy Bastion
To deploy Bastion, sign in to the Azure portal and go to your VM or virtual network.
Select the tab for the deployment method you want to use:
- Default settings: Quick one-click deployment with Standard SKU.
- Custom settings: Full control over SKU, scaling, availability zones, and other features.
- Developer SKU (free): No-cost option with basic features for dev/test. Uses shared pool architecture. Limited to select regions.
Note
Dedicated deployments (Default and Custom settings) take approximately 10 minutes to complete. Developer SKU deploys in seconds.
When you deploy Bastion using the Deploy Bastion option, Bastion deploys automatically with the Standard SKU and default settings based on your virtual network. You can configure additional settings or upgrade the SKU after deployment completes.
The following diagram shows the dedicated deployment architecture used by the Default settings options.
Default values:
To deploy Bastion with default settings:
- Go to your virtual network (or VM). In the left pane, select Connect > Bastion.
- In the Bastion pane, select Deploy Bastion.
- Bastion deploys automatically with default settings. The deployment process takes about 10 minutes to complete.
Remove VM public IP address
When you connect to a VM by using Azure Bastion, you don't need a public IP address for your VM. If you aren't using the public IP address for anything else, you can dissociate it from your VM:
Go to your virtual machine. On the Overview page, click the Public IP address to open the Public IP address page.
On the Public IP address page, go to Overview. You can view the resource that this IP address is Associated to. Select Dissociate at the top of the pane.
Select Yes to dissociate the IP address from the VM network interface. After you dissociate the public IP address from the network interface, verify that it's no longer listed under Associated to.
After you dissociate the IP address, you can delete the public IP address resource. On the Public IP address pane for the VM, at the top of the Overview page, select Delete.
Select Yes to delete the public IP address.
Clean up resources
When you finish using the virtual network and the virtual machines, delete the resource group and all of the resources that it contains:
Enter the name of your resource group in the Search box at the top of the portal, and then select it from the search results.
Select Delete resource group.
Enter your resource group for TYPE THE RESOURCE GROUP NAME, and then select Delete.
Next steps
In this quickstart, you deployed Bastion to your virtual network. Next, you can connect to a virtual machine securely via Bastion, configure more features, and work with VM connections.
- Connect to a Windows VM: RDP | SSH
- Connect to a Linux VM: SSH | RDP
- Connect from a native client: Windows | Linux/SSH
- Connect to a scale set
- VM connections and features
- Azure Bastion configuration settings
- Bastion SKU comparison
- IP-based connections