Events
Take the Microsoft Learn AI Skills Challenge
Sep 24, 11 PM - Nov 1, 11 PM
Elevate your skills in Microsoft Fabric and earn a digital badge by November 1.
Register nowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
APPLIES TO:
NoSQL
MongoDB
Cassandra
Gremlin
Table
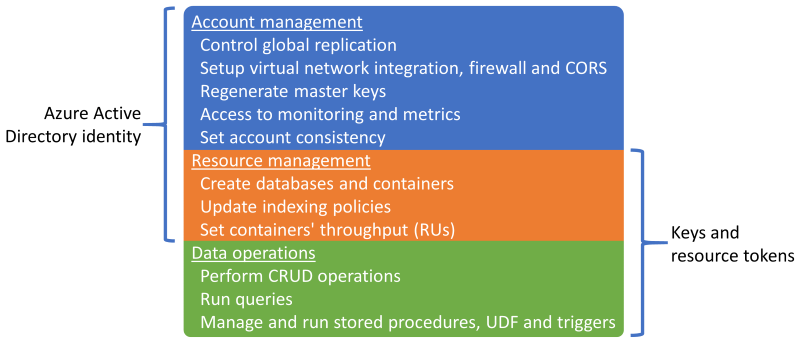
In Azure Cosmos DB, there are two ways to authenticate your interactions with the database service:
Each authentication method gives access to different sets of operations, with some overlap:
In some scenarios, you may want to restrict some users of your organization to perform data operations (that is CRUD requests and queries) only. This is typically the case for developers who don't need to create or delete resources, or change the provisioned throughput of the containers they are working on.
You can restrict the access by applying the following steps:
The next sections of this article show how to perform these steps.
Note
In order to execute the commands in the next sections, you need to install Azure PowerShell Module 3.0.0 or later, as well as the Azure Owner Role on the subscription that you are trying to modify.
In the PowerShell scripts in the next sections, substitute the following placeholders with values specific to your environment:
$MySubscriptionId - The subscription ID that contains the Azure Cosmos DB account where you want to limit the permissions. For example: e5c8766a-eeb0-40e8-af56-0eb142ebf78e.$MyResourceGroupName - The resource group containing the Azure Cosmos DB account. For example: myresourcegroup.$MyAzureCosmosDBAccountName - The name of your Azure Cosmos DB account. For example: mycosmosdbsaccount.$MyUserName - The login (username@domain) of the user for whom you want to limit access. For example: cosmosdbuser@contoso.com.Azure PowerShell commands require you to login and select the subscription to execute the commands:
Login-AzAccount
Select-AzSubscription $MySubscriptionId
The following script creates a Microsoft Entra role assignment with "Key Only" access for Azure Cosmos DB accounts. The role is based on Azure custom roles and Granular actions for Azure Cosmos DB. These roles and actions are part of the Microsoft.DocumentDB Microsoft Entra namespace.
First, create a JSON document named AzureCosmosKeyOnlyAccess.json with the following content:
{
"Name": "Azure Cosmos DB Key Only Access Custom Role",
"Id": "00000000-0000-0000-0000-0000000000",
"IsCustom": true,
"Description": "This role restricts the user to read the account keys only.",
"Actions":
[
"Microsoft.DocumentDB/databaseAccounts/listKeys/action"
],
"NotActions": [],
"DataActions": [],
"NotDataActions": [],
"AssignableScopes":
[
"/subscriptions/$MySubscriptionId"
]
}
Run the following commands to create the Role assignment and assign it to the user:
New-AzRoleDefinition -InputFile "AzureCosmosKeyOnlyAccess.json"
New-AzRoleAssignment -SignInName $MyUserName -RoleDefinitionName "Azure Cosmos DB Key Only Access Custom Role" -ResourceGroupName $MyResourceGroupName -ResourceName $MyAzureCosmosDBAccountName -ResourceType "Microsoft.DocumentDb/databaseAccounts"
The following commands remove the ability to use keys to:
$cdba = Get-AzResource -ResourceType "Microsoft.DocumentDb/databaseAccounts" -ApiVersion "2015-04-08" -ResourceGroupName $MyResourceGroupName -ResourceName $MyAzureCosmosDBAccountName
$cdba.Properties.disableKeyBasedMetadataWriteAccess="True"
$cdba | Set-AzResource -Force
Events
Take the Microsoft Learn AI Skills Challenge
Sep 24, 11 PM - Nov 1, 11 PM
Elevate your skills in Microsoft Fabric and earn a digital badge by November 1.
Register nowTraining
Module
Implement security in Azure Cosmos DB for NoSQL - Training
We will learn the different security models that Azure Cosmos DB uses.
Certification
Microsoft Certified: Azure Cosmos DB Developer Specialty - Certifications
Write efficient queries, create indexing policies, manage, and provision resources in the SQL API and SDK with Microsoft Azure Cosmos DB.