Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
This feature is in preview. The Azure Preview Supplemental Terms include additional legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability. This premium Azure Policy capability is offered at no extra cost for customers with Microsoft Defender for Cloud's enhanced security features enabled. For other users, charges might apply in the future.
When you investigate security recommendations in Microsoft Defender for Cloud, you review the list of affected resources. Occasionally, you find a resource that shouldn't be in the list, or you find a recommendation that appears in a scope where it doesn't belong. For example, Defender for Cloud might not track a remediation process, or a recommendation might not apply to a specific subscription. Your organization might decide to accept the risks related to the specific resource or recommendation.
In such cases, create an exemption rule to:
Exempt a resource to remove it from the list of unhealthy resources and from secure score impact. Defender for Cloud lists the resource as Not applicable and shows the reason as Exempted with the justification that you select.
Exempt a subscription or management group to prevent the recommendation from affecting your secure score or appearing for that scope. The exemption applies to existing resources and to resources that you create later. Defender for Cloud marks the recommendation with the justification that you select for that scope.
For each scope, create an exemption rule to:
Mark a specific recommendation as Mitigated or Risk accepted for one or more subscriptions, or for a management group.
Mark one or more resources as Mitigated or Risk accepted for a specific recommendation.
Resource exemption is limited to 5,000 resources per subscription. If you add more than 5,000 exemptions per subscription, you might experience load issues on the exemption page.
Prerequisites
Defender for Cloud exemption relies on the Microsoft Cloud Security Benchmark (MCSB) initiative. MCSB must be assigned on the subscription before you create exemptions.
Important
Without MCSB assigned:
- Some portal features might not work as expected.
- Resources might not appear in compliance views.
- Exemption options might occasionally be unavailable.
You can create exemptions for recommendations that belong to the default MCSB initiative or to other built-in regulatory standards. Some recommendations in MCSB don't support exemptions. You can find a list of these recommendations in the exemptions FAQ.
Permissions:
To create exemptions, you need the following permissions:
- Owner or Security Admin on the scope where you create the exemption.
- To create a rule, you need permissions to edit policies in Azure Policy. Learn more.
- You must have exemption permission on all initiative assignments at the target scope. If multiple initiatives contain a recommendation, you must create the exemption with permissions across all of them. A missing permission on even one initiative can cause the exemption to fail.
You need the following RBAC actions:
| Action | Description |
|---|---|
Microsoft.Authorization/policyExemptions/write |
Create an exemption |
Microsoft.Authorization/policyExemptions/delete |
Delete an exemption |
Microsoft.Authorization/policyExemptions/read |
View an exemption |
Microsoft.Authorization/policyAssignments/exempt/action |
Perform an exemption operation on a linked scope |
Note
If any of these actions are missing, the Exempt button might be hidden. Custom roles offer limited support for exemption operations.
To manage exemptions, use one of the following built-in roles:
- Security Admin (recommended)
- Owner
- Contributor (at the subscription level)
- Resource Policy Contributor
Subscription-level permissions don't inherit upward to management groups. If the policy assignment is at the management group level, you need the role assigned at that level.
To manage exemptions for specific resources, you need the required RBAC actions at the resource or resource group level. Subscription-scoped role assignments might not provide sufficient access to create or delete exemptions on individual resources. Verify that your role assignment covers the scope of the resource you want to exempt.
When you create an exemption at the management group level, ensure the Microsoft Azure Security Resource Provider has the necessary permissions by assigning it the Reader role on that management group. Grant this role the same way that you grant user permissions.
Limitations:
You don't create exemptions for custom recommendations.
Preview recommendations might not support exemptions. Check whether the recommendation shows a Preview tag.
Some recommendations in MCSB don't support exemptions. You can find a list of these recommendations in the exemptions FAQ.
If you disable a recommendation, you also exempt all of its subrecommendations.
KQL-based recommendations use standard assignments and don't use Azure Policy exemption events in the Activity Logs. To determine whether a recommendation is KQL-based or policy-based, open the recommendation in the portal and check the Assessment key field. KQL-based recommendations show a standard assessment key format and don't have an associated Azure Policy definition link. Policy-based recommendations display a direct link to the underlying policy definition.
When you create an exemption from the Defender for Cloud portal, Defender for Cloud identifies all initiatives that contain the recommendation and creates the exemption across all of them automatically. If you create the exemption through the Azure Policy API instead, you must create a separate exemption for each initiative manually. For more information, see the exemptions FAQ.
When you assign a new initiative that contains a recommendation with an existing exemption, the exemption doesn't carry over to the new initiative. Create a new exemption for the recommendation under the newly assigned initiative.
Tip
If you run into issues after you create an exemption, see Review and manage recommendation exemptions for guidance on:
Define an exemption
We recommend creating exemptions in the Defender for Cloud portal. Exemptions created through the Azure Policy API might not fully integrate with Defender for Cloud and can cause unexpected results, such as exemptions that don't propagate correctly across all relevant initiatives. If you need to use the API, see Azure Policy exemption structure.
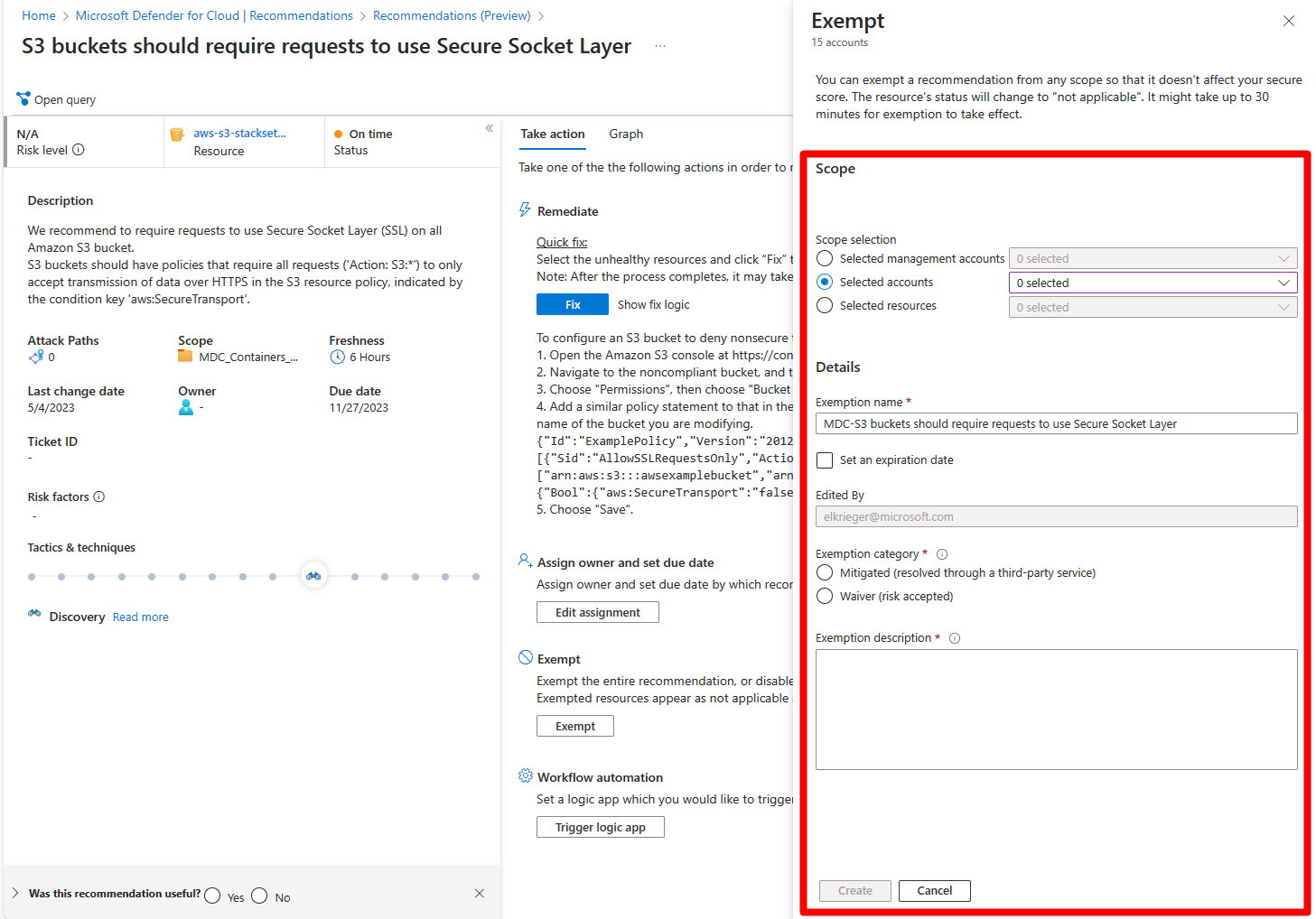
To create an exemption rule:
Sign in to the Azure portal.
Go to Defender for Cloud > Recommendations.
Select a recommendation.
Select Exempt.
Select the scope for the exemption.
- If you select a management group, Defender for Cloud exempts the recommendation from all subscriptions in that group.
- If you create this rule to exempt one or more resources from the recommendation, choose Selected resources and select the relevant resources from the list.
Enter a name.
(Optional) set an expiration date.
Select the category for the exemption:
- Resolved through third-party service (mitigated) – if you use a non-Microsoft service for remediation that Defender for Cloud doesn't track.
Note
When you exempt a resource as mitigated, it counts as healthy. You don't gain points for the remediation, but Defender for Cloud doesn't deduct points for leaving it unhealthy, so exempted resources don't lower your score.
- Risk accepted (waiver) – if you decide to accept the risk of not mitigating this recommendation.
Enter a description.
Select Create.
After you create the exemption
An exemption can take up to 24 hours to take effect because Defender for Cloud evaluates resources every 12-24 hours. After the exemption takes effect:
The recommendation or resources don't affect your secure score.
If you exempt specific resources, Defender for Cloud lists them in the Not applicable tab of the recommendation details page.
If you exempt a recommendation, Defender for Cloud hides it by default on the Recommendations page. This behavior happens because the default Recommendation status filter excludes Not applicable recommendations. The same behavior occurs if you exempt all recommendations in a security control.
Understand how the exemption type affects the recommendation status
The exemption type that you select determines how the exemption affects the recommendation and secure score:
- Mitigated exemptions: Exempt resources count as healthy. Secure score increases.
- Waiver exemptions: Exempt resources are excluded from the secure score calculation. Resources don't count toward secure score but might still appear in recommendations.
Note
Preview recommendations have no impact on secure score regardless of exemption status.
Verify that the exemption is working
If the recommendation still shows resources as unhealthy after 24 hours, see Resolve an exemption that doesn't update the recommendation status for detailed steps.