Monitoring Public IP addresses
When you have critical applications and business processes relying on Azure resources, you want to monitor those resources for their availability, performance, and operation.
This article describes the monitoring data generated by Public IP Address. Public IP Addresses use Azure Monitor. If you are unfamiliar with the features of Azure Monitor common to all Azure services that use it, read Monitoring Azure resources with Azure Monitor.
Public IP Addresses insights
Some services in Azure have a special focused pre-built monitoring dashboard in the Azure portal that provides a starting point for monitoring your service. These special dashboards are called "insights".
Public IP Address insights provides:
Traffic data
DDoS information
Monitoring data
Public IP Addresses collect the same kinds of monitoring data as other Azure resources that are described in Monitoring data from Azure resources.
See Monitoring Public IP Addresses data reference for detailed information on the metrics and logs metrics created by Public IP Addresses.
Collection and routing
Platform metrics and the Activity log are collected and stored automatically, but can be routed to other locations by using a diagnostic setting.
Resource Logs are not collected and stored until you create a diagnostic setting and route them to one or more locations.
For general guidance, see Create diagnostic setting to collect platform logs and metrics in Azure for the process for creating a diagnostic setting using the Azure portal, CLI, or PowerShell. When you create a diagnostic setting, you specify which categories of logs to collect. The categories for Public IP Addresses are listed in Monitoring Public IP Addresses data reference.
Creating a diagnostic setting
You can create a diagnostic setting by using the Azure portal, PowerShell, or the Azure CLI.
Portal
Sign-in to the Azure Portal.
In the search box at the top of the portal, enter Public IP addresses. Select Public IP addresses in the search results.
Select your the public IP address that you want to enable the setting for. For this example, myPublicIP is used.
In the Monitoring section of your public IP address, select Diagnostic settings.
Select +Add diagnostic setting.
Enter or select the following information in Diagnostic setting.
Setting Value Diagnostic setting name Enter a name for the diagnostic setting. Logs Categories Select DDoSProtectionNotifications, DDoSMitigationFlowLogs, and DDoSMitigationReports. Metrics Select AllMetrics. Select the Destination details. Some of the destination options are:
Send to Log Analytics workspace
- Select the Subscription and Log Analytics workspace.
Archive to a storage account
- Select the Subscription and Storage account.
Stream to an event hub
- Select the Subscription, Event hub namespace, Event hub name (optional), and Event hub policy name.
Send to a partner solution
- Select the Subscription and Destination.
Select Save.
PowerShell
Sign in to Azure PowerShell:
Connect-AzAccount
Log analytics workspace
To send resource logs to a Log Analytics workspace, enter these commands. In this example, myResourceGroup, myLogAnalyticsWorkspace and myPublicIP are used for the resource values. Replace these values with yours.
## Place the public IP in a variable. ##
$ippara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'myPublicIP'
}
$ip = Get-AzPublicIPAddress @ippara
## Place the workspace in a variable. ##
$wspara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'myLogAnalyticsWorkspace'
}
$ws = Get-AzOperationalInsightsWorkspace @wspara
## Enable the diagnostic setting. ##
$diag = @{
ResourceId = $ip.id
Name = 'myDiagnosticSetting'
Enabled = $true
WorkspaceId = $ws.ResourceId
}
Set-AzDiagnosticSetting @diag
Storage account
To send resource logs to a storage account, enter these commands. In this example, myResourceGroup, mystorageaccount8675 and myPublicIP are used for the resource values. Replace these values with yours.
## Place the public IP in a variable. ##
$ippara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'myPublicIP'
}
$lb = Get-AzPublicIPAddress @ippara
## Place the storage account in a variable. ##
$storpara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'mystorageaccount8675'
}
$storage = Get-AzStorageAccount @storpara
## Enable the diagnostic setting. ##
$diag = @{
ResourceId = $ip.id
Name = 'myDiagnosticSetting'
StorageAccountId = $storage.id
Enabled = $true
}
Set-AzDiagnosticSetting @diag
Event hub
To send resource logs to an event hub namespace, enter these commands. In this example, myResourceGroup, myeventhub8675 and myPublicIP are used for the resource values. Replace these values with yours.
## Place the public IP in a variable. ##
$ippara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'myPublicIP'
}
$lb = Get-AzPublicIPAddress @ippara
## Place the event hub in a variable. ##
$hubpara = @{
ResourceGroupName = 'myResourceGroup'
Name = 'myeventhub8675'
}
$eventhub = Get-AzEventHubNamespace @hubpara
## Place the event hub authorization rule in a variable. ##
$hubrule = @{
ResourceGroupName = 'myResourceGroup'
Namespace = 'myeventhub8675'
}
$eventhubrule = Get-AzEventHubAuthorizationRule @hubrule
## Enable the diagnostic setting. ##
$diag = @{
ResourceId = $ip.id
Name = 'myDiagnosticSetting'
EventHubName = $eventhub.Name
EventHubAuthorizationRuleId = $eventhubrule.Id
Enabled = $true
}
Set-AzDiagnosticSetting @diag
Azure CLI
Sign in to Azure CLI:
az login
Log analytics workspace
To send resource logs to a Log Analytics workspace, enter these commands. In this example, myResourceGroup, myLogAnalyticsWorkspace and myPublicIP are used for the resource values. Replace these values with yours.
ipid=$(az network public-ip show \
--name myPublicIP \
--resource-group myResourceGroup \
--query id \
--output tsv)
wsid=$(az monitor log-analytics workspace show \
--resource-group myResourceGroup \
--workspace-name myLogAnalyticsWorkspace \
--query id \
--output tsv)
az monitor diagnostic-settings create \
--name myDiagnosticSetting \
--resource $ipid \
--logs '[{"category": "DDoSProtectionNotifications","enabled": true},{"category": "DDoSMitigationFlowLogs","enabled": true},{"category": "DDoSMitigationReports","enabled": true}]' \
--metrics '[{"category": "AllMetrics","enabled": true}]' \
--workspace $wsid
Storage account
To send resource logs to a storage account, enter these commands. In this example, myResourceGroup, mystorageaccount8675 and myPublicIP are used for the resource values. Replace these values with yours.
ipid=$(az network public-ip show \
--name myPublicIP \
--resource-group myResourceGroup \
--query id \
--output tsv)
storid=$(az storage account show \
--name mystorageaccount8675 \
--resource-group myResourceGroup \
--query id \
--output tsv)
az monitor diagnostic-settings create \
--name myDiagnosticSetting \
--resource $ipid \
--logs '[{"category": "DDoSProtectionNotifications","enabled": true},{"category": "DDoSMitigationFlowLogs","enabled": true},{"category": "DDoSMitigationReports","enabled": true}]' \
--metrics '[{"category": "AllMetrics","enabled": true}]' \
--storage-account $storid
Event hub
To send resource logs to an event hub namespace, enter these commands. In this example, myResourceGroup, myeventhub8675 and myPublicIP are used for the resource values. Replace these values with yours.
ipid=$(az network public-ip show \
--name myPublicIP \
--resource-group myResourceGroup \
--query id \
--output tsv)
az monitor diagnostic-settings create \
--name myDiagnosticSetting \
--resource $ipid \
--event-hub myeventhub8675 \
--event-hub-rule RootManageSharedAccessKey \
--logs '[{"category": "DDoSProtectionNotifications","enabled": true},{"category": "DDoSMitigationFlowLogs","enabled": true},{"category": "DDoSMitigationReports","enabled": true}]' \
--metrics '[{"category": "AllMetrics","enabled": true}]'
The metrics and logs you can collect are discussed in the following sections.
Analyzing metrics
You can analyze metrics for Public IP Addresses with metrics from other Azure services using metrics explorer by opening Metrics from the Azure Monitor menu. See Analyze metrics with Azure Monitor metrics explorer for details on using this tool.
For a list of the platform metrics collected for Public IP Address, see Monitoring Public IP Addresses data reference .
For reference, you can see a list of all resource metrics supported in Azure Monitor.
Analyzing logs
Data in Azure Monitor Logs is stored in tables where each table has its own set of unique properties.
All resource logs in Azure Monitor have the same fields followed by service-specific fields. The common schema is outlined in Azure Monitor resource log schema.
The Activity log is a type of platform log in Azure that provides insight into subscription-level events. You can view it independently or route it to Azure Monitor Logs, where you can do much more complex queries using Log Analytics.
For a list of the types of resource logs collected for Public IP addresses, see Monitoring Public IP Addresses data reference.
For a list of the tables used by Azure Monitor Logs and queryable by Log Analytics, see Monitoring Public IP Addresses data reference.
Sample Kusto queries
Important
When you select Logs from the Public IP menu, Log Analytics is opened with the query scope set to the current Public IP address. This means that log queries will only include data from that resource. If you want to run a query that includes data from other resources or data from other Azure services, select Logs from the Azure Monitor menu. See Log query scope and time range in Azure Monitor Log Analytics for details.
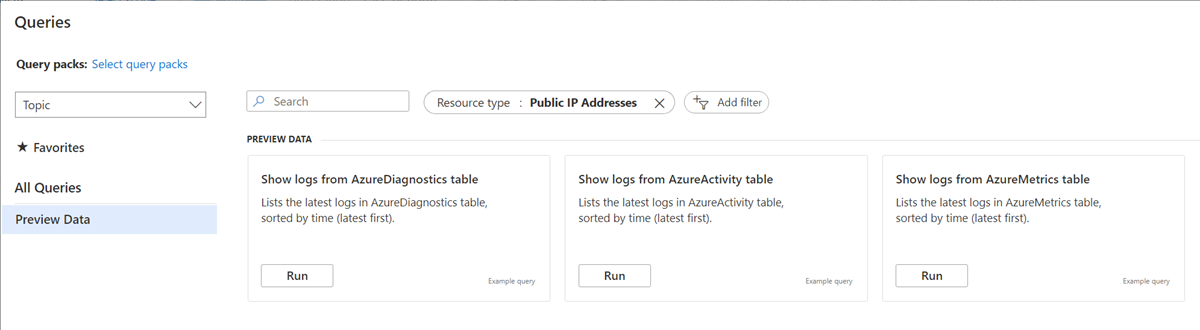
For a list of common queries for Public IP addresses, see the Log Analytics queries interface.
The following is an example of the built in queries for Public IP addresses that are found within the Long Analytics queries interface in the Azure portal.
Alerts
Azure Monitor alerts proactively notify you when important conditions are found in your monitoring data. They allow you to identify and address issues in your system before your customers notice them. You can set alerts on metrics, logs, and the activity log. Different types of alerts have benefits and drawbacks.
The following table lists common and recommended alert rules for Public IP addresses.
| Alert type | Condition | Description |
|---|---|---|
| Under DDoS attack or not | GreaterThan 0. 1 is currently under attack. 0 indicates normal activity |
As part of Azure's edge protection, public IP addresses are monitored for DDoS attacks. An alert will allow you to be notified if your public IP address is affected. |
Next steps
See Monitoring Public IP Addresses data reference for a reference of the metrics, logs, and other important values created by Public IP Address.
See Monitoring Azure resources with Azure Monitor for details on monitoring Azure resources.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for