Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Error:
Address Sanitizer Error: Stack buffer overflow
Remarks
A stack buffer overflow can happen many ways in C or C++. We provide several examples for this category of error that you can catch by a simple recompile.
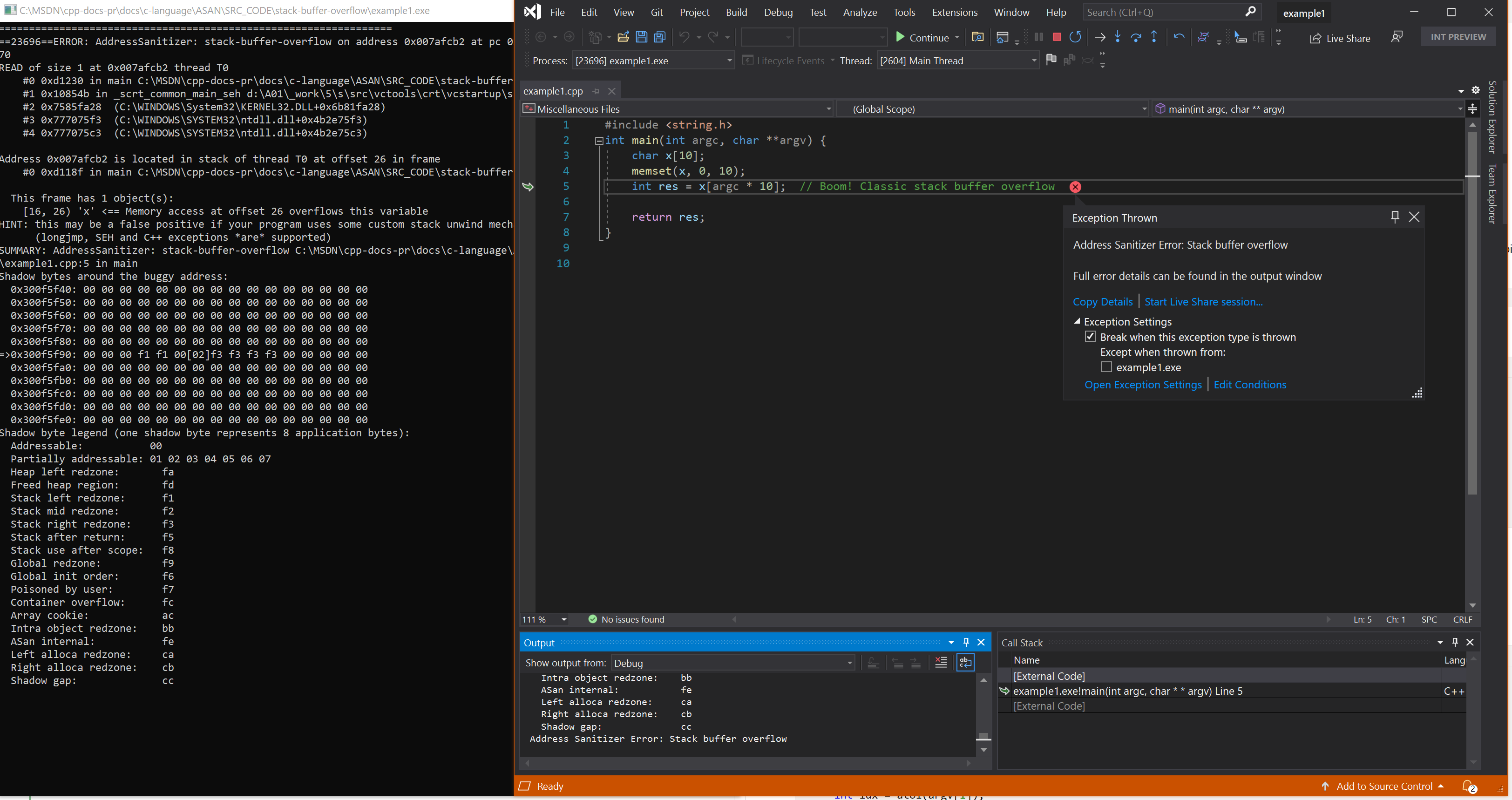
Example - stack buffer overflow
// example1.cpp
// stack-buffer-overflow error
#include <string.h>
int main(int argc, char **argv) {
char x[10];
memset(x, 0, 10);
int res = x[argc * 10]; // Boom! Classic stack buffer overflow
return res;
}
To build and test this example, run these commands in a Visual Studio 2019 version 16.9 or later developer command prompt:
cl example1.cpp /fsanitize=address /Zi
devenv /debugexe example1.exe
Resulting error
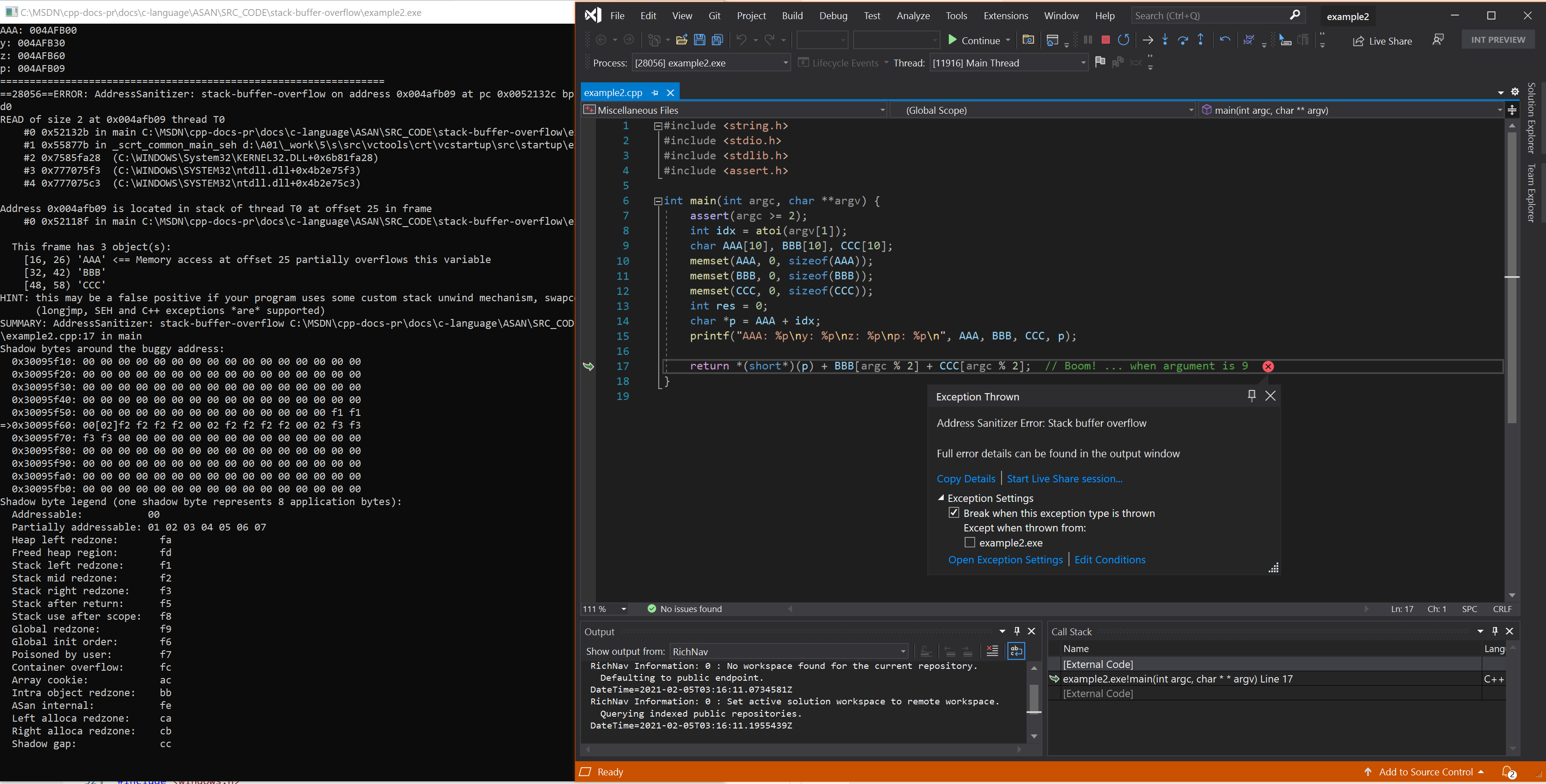
Example - Stack buffer math
// example2.cpp
// stack-buffer-overflow error
#include <string.h>
#include <stdio.h>
#include <stdlib.h>
#include <assert.h>
int main(int argc, char **argv) {
assert(argc >= 2);
int idx = atoi(argv[1]);
char AAA[10], BBB[10], CCC[10];
memset(AAA, 0, sizeof(AAA));
memset(BBB, 0, sizeof(BBB));
memset(CCC, 0, sizeof(CCC));
int res = 0;
char *p = AAA + idx;
printf("AAA: %p\ny: %p\nz: %p\np: %p\n", AAA, BBB, CCC, p);
return *(short*)(p) + BBB[argc % 2] + CCC[argc % 2]; // Boom! ... when argument is 9
}
To build and test this example, run these commands in a Visual Studio 2019 version 16.9 or later developer command prompt:
cl example2.cpp /fsanitize=address /Zi
devenv /debugexe example2.exe 9
Resulting error - Stack buffer math
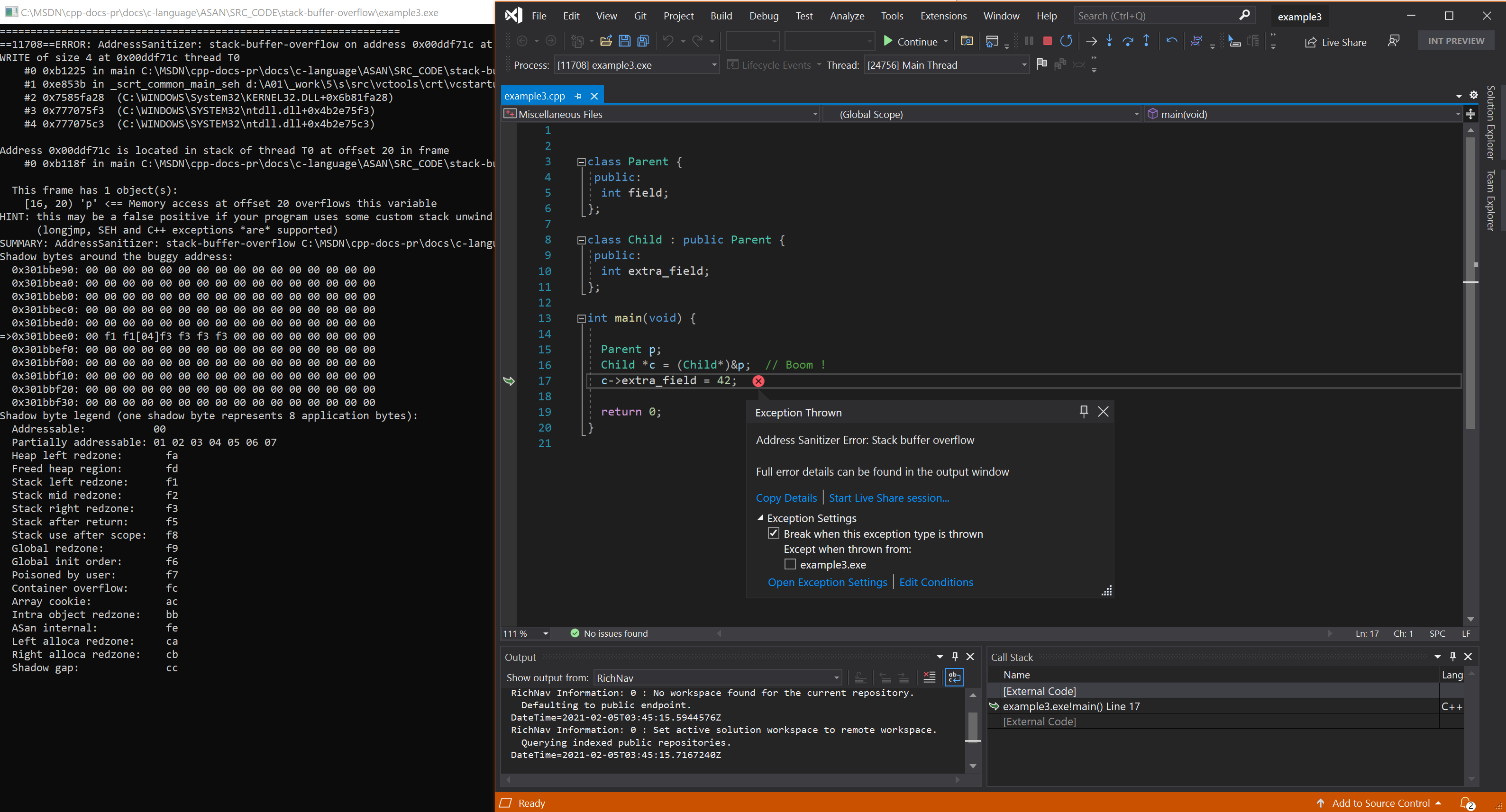
Example - improper down cast on stack
// example3.cpp
// stack-buffer-overflow error
class Parent {
public:
int field;
};
class Child : public Parent {
public:
volatile int extra_field;
};
int main(void) {
Parent p;
Child *c = (Child*)&p;
c->extra_field = 42; // Boom !
return (c->extra_field == 42);
}
To build and test this example, run these commands in a Visual Studio 2019 version 16.9 or later developer command prompt:
cl example3.cpp /fsanitize=address /Zi
devenv /debugexe example3.exe
Resulting error - improper down cast on stack
See also
AddressSanitizer overview
AddressSanitizer known issues
AddressSanitizer build and language reference
AddressSanitizer runtime reference
AddressSanitizer shadow bytes
AddressSanitizer cloud or distributed testing
AddressSanitizer debugger integration
AddressSanitizer error examples