Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Tip
Did you know you can try the features in Microsoft Defender for Office 365 Plan 2 for free? Use the 90-day Defender for Office 365 trial at the Microsoft Defender portal trials hub. Learn about who can sign up and trial terms on Try Microsoft Defender for Office 365.
Microsoft 365 organizations that have Microsoft Defender for Office 365 included in their subscription or purchased as an add-on have the Email entity page. The Email entity page in the Microsoft Defender portal contains highly detailed information about an email message and any related entities.
This article explains the information and actions on the Email entity page.
Permissions and licensing for the Email entity page
To use the Email entity page, you need to be assigned permissions. The permissions and licensing are the same as Threat Explorer (Explorer) and Real-time detections. For more information, see Permissions and licensing for Threat Explorer and Real-time detections.
Where to find the Email entity page
There are no direct links to the Email entity page from the top levels of the Defender portal. Instead, the ![]() Open email entity action is available at the top of the email details flyout in many Defender for Office 365 features. This email details flyout is known as the Email summary panel, and contains a summarized subset of the information on the Email entity page. The email summary panel is identical across Defender for Office 365 features. For more information, see the The Email summary panel section later in this article.
Open email entity action is available at the top of the email details flyout in many Defender for Office 365 features. This email details flyout is known as the Email summary panel, and contains a summarized subset of the information on the Email entity page. The email summary panel is identical across Defender for Office 365 features. For more information, see the The Email summary panel section later in this article.
The Email summary panel with the ![]() Open email entity action is available in the following locations:
Open email entity action is available in the following locations:
From the Advanced hunting page at https://security.microsoft.com/v2/advanced-hunting: In the Results tab of an email-related query, click on the NetworkMessageId value of an entry in the table.
*From the Alerts page at https://security.microsoft.com/alerts: For alerts with the Detection source value MDO or the Product names value Microsoft Defender for Office 365, select the entry by clicking on the Alert name value. In the alert details page that opens, select the message from the Messages list section.
From the Threat protection status report at https://security.microsoft.com/reports/TPSEmailPhishReportATP:
- Select View data by Email > Phish and any of the available Chart breakdown selections. In the details table below the chart, select the entry by clicking anywhere in the row other than the check box next to the first column.
- Select View data by Email > Malware and any of the available Chart breakdown selections. In the details table below the chart, select the entry by clicking anywhere in the row other than the check box next to the first column.
- Select View data by Email > Spam and any of the available Chart breakdown selections. In the details table below the chart, select the entry by clicking anywhere in the row other than the check box next to the first column.
From the Explorer page at https://security.microsoft.com/threatexplorerv3 (Threat Explorer) or from the Real-time detections page at https://security.microsoft.com/realtimereportsv3. Use one of the following methods:
- In Threat Explorer, verify the All email view is selected > verify the Email tab (view) in the details area is selected > click on the Subject value in an entry.
- In Threat Explorer or Real-time detections, select the Malware view > verify the Email tab (view) in the details area is selected > click on the Subject value in an entry.
- In Threat Explorer or Real-time detections, select the Phish view > verify the Email tab (view) in the details area is selected > click on the Subject value in an entry.
From the Incidents page at https://security.microsoft.com/incidents: For incidents with the Product names value Microsoft Defender for Office 365, select the incident by clicking on the Incident name value. In the incident details page that opens, select the Evidence and responses tab (view). In the All evidence tab and the Entity type value Email or the Emails tab, select the entry by clicking anywhere in the row other than the check box.
From the Quarantine page at https://security.microsoft.com/quarantine: Verify the Email tab is selected > select an entry by clicking anywhere in the row other than the check box.
From the Submissions page at https://security.microsoft.com/reportsubmission:
- Select the Emails tab > select an entry by clicking anywhere in the row other than the check box.
- Select the User reported tab > select an entry by clicking anywhere in the row other than the check box.
What's on the Email entity page
The details pane on the left side of the page contains collapsible sections with details about the message. These sections remain constant as long as you're on the page. The available sections are:
Tags section. Shows any user tags (including Priority account) that are assigned to senders or recipients. For more information about user tags, see User tags in Microsoft Defender for Office 365.
Detection details section:
Original Threats
Original delivery location:
- Deleted Items folder
- Dropped
- Delivered failed
- Inbox folder
- Junk Email folder
- External
- Quarantine
- Unknown
Latest Threats
Latest delivery location: The location of the message after system actions on the message (for example, ZAP), or admin actions on the message (for example, Move to Deleted Items). User actions on the message (for example, deleting or archiving the message) aren't shown, so this value doesn't guarantee the current location of the message.
Tip
There are scenarios where Original delivery location/Latest delivery location and/or Delivery action have the value Unknown. For example:
- The message was delivered (Delivery action is Delivered), but an Inbox rule moved the message to a default folder other than the Inbox or Junk Email folder (for example, the Draft or Archive folder).
- ZAP attempted to move the message after delivery, but the message wasn't found (for example, the user moved or deleted the message).
Detection technology:
- Advanced filter: Phishing signals based on machine learning.
- Campaign: Messages identified as part of a campaign.
- File detonation: Safe Attachments detected a malicious attachment during detonation analysis.
- File detonation reputation: File attachments previously detected by Safe Attachments detonations in other Microsoft 365 organizations.
- File reputation: The message contains a file that was previously identified as malicious in other Microsoft 365 organizations.
- Fingerprint matching: The message closely resembles a previous detected malicious message.
- General filter: Phishing signals based on analyst rules.
- Impersonation brand: Sender impersonation of well-known brands.
- Impersonation domain: Impersonation of sender domains that you own or specified for protection in anti-phishing policies.
- Impersonation user: Impersonation of protected senders that you specified in anti-phishing policies or learned through mailbox intelligence.
- LLM content analysis: Analysis by Microsoft's purpose-built large language models to detect harmful email.
- Mail bombing: A distributed denial of service (DDoS) attack that typically subscribes recipients to a large number of legitimate newsletters and services. The resulting volume of incoming email within minutes intends to overwhelm the recipient's mailbox and email security systems, and acts as a precursor to malware, ransomware, or data exfiltration.
- Mailbox intelligence impersonation: Impersonation detections from mailbox intelligence in anti-phishing policies.
- Mixed analysis detection: Multiple filters contributed to the message verdict.
- Spoof DMARC: The message failed DMARC authentication.
- Spoof external domain: Sender email address spoofing using a domain that's external to your organization.
- Spoof intra-org: Sender email address spoofing using a domain that's internal to your organization.
- URL detonation: Safe Links detected a malicious URL in the message during detonation analysis.
- URL detonation reputation: URLs previously detected by Safe Links detonations in other Microsoft 365 organizations.
- URL malicious reputation: The message contains a URL that was previously identified as malicious in other Microsoft 365 organizations.
Delivery action:
- Delivered
- Junked
- Blocked
Primary Override : Source
- Values for Primary override:
- Allowed by organization policy
- Allowed by user policy
- Blocked by organization policy
- Blocked by user policy
- None
- Values for Primary override source:
- 3rd Party Filter
- Admin initiated time travel (ZAP)
- Antimalware policy block by file type
- Antispam policy settings
- Connection policy
- Exchange transport rule
- Exclusive mode (User override)
- Filtering skipped due to on-prem organization
- IP region filter from policy
- Language filter from policy
- Phishing Simulation
- Quarantine release
- SecOps Mailbox
- Sender address list (Admin Override)
- Sender address list (User override)
- Sender domain list (Admin Override)
- Sender domain list (User override)
- Tenant Allow/Block List file block
- Tenant Allow/Block List sender email address block
- Tenant Allow/Block List spoof block
- Tenant Allow/Block List URL block
- Trusted contact list (User override)
- Trusted domain (User override)
- Trusted recipient (User override)
- Trusted senders only (User override)
- Values for Primary override:
Email details section:
- Directionality:
- Inbound
- Intra-irg
- Outbound
- Recipient (To)*
- Sender*
- Time received
- Internet Message ID*: Available in the Message-ID header field in the message header. An example value is
<08f1e0f6806a47b4ac103961109ae6ef@server.domain>(note the angle brackets). - Network Message ID*: A GUID value that's available in the X-MS-Exchange-Organization-Network-Message-Id header field in the message header.
- Cluster ID
- Language
* The
 Copy to clipboard action is available to copy the value.
Copy to clipboard action is available to copy the value.- Directionality:
The tabs (views) along the top of the page allows you to investigate email efficiently. These views are described in the following subsections.
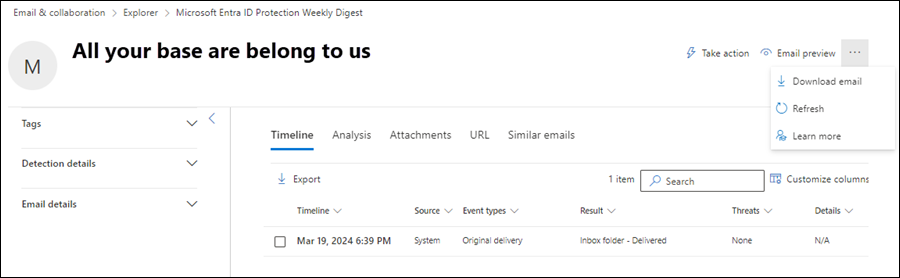
Timeline view
The Timeline view shows the delivery and post-delivery events that happened to the message.
The following message event information is available in the view. Select a column header to sort by that column. To add or remove columns, select ![]() Customize columns. By default, all available columns are selected.
Customize columns. By default, all available columns are selected.
- Timeline (date/time of the event)
- Source: For example: System, **Admin, or User.
- Event types
- Result
- Threats
- Details
If nothing happened to the message after delivery, the message is likely to have only one row in the Timeline view with the Event types value Original delivery. For example:
- The Result value is Inbox folder - Delivered.
- The Result value is Junk email folder - Delivered to Junk
- The Result value is Quarantine - Blocked.
Subsequent actions to the message by users, admins, or Microsoft 365 add more rows to the view. For example:
- The Event types value is ZAP and the Result value is Message moved to Quarantine by ZAP.
- The Event types value is Quarantine Release and the Result value is Message was successfully released from Quarantine.
Use the ![]() Search box to find information on the page. Type text in the box and then press the ENTER key.
Search box to find information on the page. Type text in the box and then press the ENTER key.
Use ![]() Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Analysis view
The Analysis view contains information that helps you analyze the message in depth. The following information is available in this view:
Threat detection details section: Information about threats detected in the message:
- Threat classification: AI determination of the threat. For more information, see Threat classification in Microsoft Defender for Office 365.
- Threats: The primary threat is indicated by
 Primary threat.
Primary threat. - Confidence level: Values are High, Medium, or Low.
- Priority account protection: Values are Yes or No. For more information, see Configure and review priority account protection in Microsoft Defender for Office 365.
Email detection details section: Information about protection features or overrides that affected the message:
All Overrides: All organization or user settings that had the possibility to alter the intended delivery location of the message. For example, if the message matched a mail flow rule and a block entry in the Tenant Allow/Block List, both settings are listed here. The Primary Override : Source property value identifies the setting that affected the delivery of the message.
Primary Override : Source: Shows the organization or user setting that altered the intended delivery location of the message (allowed instead of blocked, or blocked instead of allowed). For example:
- A mail flow rule blocked the message.
- An entry in the user's Safe Senders list allowed the message.
Exchange transport rules (mail flow rules): If mail flow rules affected the message, the rule names and GUID vales are shown. Actions taken on messages by mail flow rules occur before spam and phishing verdicts.
The
 Copy to clipboard action is available to copy the rule GUID. For more information about mail flow rules, see Mail flow rules (transport rules) in Exchange Online.
Copy to clipboard action is available to copy the rule GUID. For more information about mail flow rules, see Mail flow rules (transport rules) in Exchange Online.The Go to Exchange admin center link opens the Rules page in the new Exchange admin center at https://admin.exchange.microsoft.com/#/transportrules.
Connector: If the message was delivered through an Inbound connector, the connector name is shown. For more information about connectors, see Configure mail flow using connectors in Exchange Online.
Bulk complaint level (BCL): A higher BCL value indicates the message is more likely to be spam. For more information, see Bulk complaint level (BCL).
Policy: If a policy type is listed here (for example, Spam), select Configure
 to open the related policy page (for example, the Anti-spam policies page at https://security.microsoft.com/antispam).
to open the related policy page (for example, the Anti-spam policies page at https://security.microsoft.com/antispam).Policy action
Alert ID: Select the Alert ID value to open the details page for the alert (as if you found and selected the alert from the Alerts page at https://security.microsoft.com/alerts). The
 Copy to clipboard action is also available to copy the Alert ID value.
Copy to clipboard action is also available to copy the Alert ID value.Policy type
Client type: Shows the type of client that sent the message (for example, REST)
Email size
Data loss prevention rules
Sender-Recipient details section: Details about the message sender and some recipient information:
- Sender display name
- Sender address*
- Sender IP
- Sender domain name*
- Domain creation date: A recently created domain and other message signals can identify the message as suspicious.
- Domain owner
- Sender MAIL FROM address*
- Sender MAIL FROM domain name*
- Return-Path
- Return-Path domain
- Location
- Recipient domain*
- To: Shows the first 5,000 characters of any email addresses in the To field of the message.
- Cc: Shows the first 5,000 characters of any email addresses in the Cc field of the message.
- Distribution list: Shows the distribution group (distribution list) if the recipient received the email as a member of the list. The top level distribution group is shown for nested distribution groups.
- Forwarding: Indicates whether the message was automatically forwarded to an external email address. The forwarding user and the forwarding type are shown (mail flow rules, Inbox rules, or SMTP forwarding).
* The
 Copy to clipboard action is available to copy the value.
Copy to clipboard action is available to copy the value.Authentication section: Details about email authentication results:
- Domain-based Message Authentication (DMARC)
Pass: The DMARC check for the message passed.Fail: The DMARC check for the message failed.BestGuessPass: The DMARC TXT record for the domain doesn't exist. If it existed, the DMARC check for the message would pass.- None: Indicates that no DMARC TXT record exists for the sending domain in DNS.
- DomainKeys identified mail (DKIM): Values are:
Pass: The DKIM check for the message passed.Fail (reason): The DKIM check for the message failed. For example, the message wasn't DKIM signed or the DKIM signature wasn't verified.None: The message wasn't DKIM signed. This result might or might not indicate that the domain has a DKIM record, or that the DKIM record doesn't evaluate to a result. This result only indicates that this message wasn't signed.
- Sender Policy Framework (SPF): Values are:
Pass (IP address): The SPF check found the message source is valid for the domain.Fail (IP address): The SPF check found the message source isn't valid for the domain, and the enforcement rule in the SPF record is-all(hard fail).SoftFail (reason): The SPF check found the message source isn't valid for the domain, and the enforcement rule in the SPF record is~all(soft fail).Neutral: The SPF check found the message source isn't valid for the domain, and the enforcement rule in the SPF record is?all(neutral).None: The domain doesn't have an SPF record, or the SPF record doesn't evaluate to a result.TempError: The SPF check encountered a temporary error (for example, a DNS error). The same check later might succeed.PermError: The SPF check encountered a permanent error. For example, the domain has a badly formatted SPF record.
- Composite authentication: SPF, DKIM, DMARC, and other information determine if the message sender (the From address) is authentic. For more information, see Composite authentication.
Tip
For more information about email authentication results and how to correct failures, see Security Operations guide for email authentication in Microsoft 365.
- Domain-based Message Authentication (DMARC)
Related entities section: Information about attachments and URLs in the message:
- Entity: Selecting Attachments or URLs takes you to the Attachments view or the URL view of the Email entity page for the message.
- Total count
- Threats found: The values are Yes or No.
Message details area:
- Plain-text email header tab: Contains the entire message header in plain text. Select
 Copy message header to copy the message header. Select
Copy message header to copy the message header. Select  Microsoft Message Header Analyzer to open the Message Header Analyzer at https://mha.azurewebsites.net/pages/mha.html. Paste the copied message header into the page, and then select Analyze headers for details about the message headers and values.
Microsoft Message Header Analyzer to open the Message Header Analyzer at https://mha.azurewebsites.net/pages/mha.html. Paste the copied message header into the page, and then select Analyze headers for details about the message headers and values. - To tab: Shows the first 5,000 characters of any email addresses in the To field of the message.
- Cc tab: Shows the first 5,000 characters of any email addresses in the Cc field of the message.
- Plain-text email header tab: Contains the entire message header in plain text. Select
Attachments view
The Attachments view shows information about all file attachments in the message, and the scanning results of those attachments.
The following attachment information is available in this view. Select a column header to sort by that column. To add or remove columns, select ![]() Customize columns. By default, all available columns are selected.
Customize columns. By default, all available columns are selected.
- Attachment filename: If you click on the filename value
- File type
- File size
- File extension
- Threat
- Malware family
- Attachment SHA256: The
 Copy to clipboard action is available to copy the SHA256 value.
Copy to clipboard action is available to copy the SHA256 value. - Details
Use the ![]() Search box to find information on the page. Type text in the box and then press the ENTER key.
Search box to find information on the page. Type text in the box and then press the ENTER key.
Use ![]() Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Attachment details
If you select an entry in the Attachments view by clicking on the Attachment filename value, a details flyout opens that contains the following information:
- Deep analysis tab: Information is available on this tab if Safe Attachments scanned (detonated) the attachment and it is identified as malicious through detonation. You can identify these messages in Threat Explorer using the following methods:
Detection technology query filter with the value File detonation.
Detonation available indicator in the Details column.
The detonation count shown in the Email Summary Panel.
Detonation chain section: Safe Attachments detonation of a single file can trigger multiple detonations. The detonation chain tracks the path of detonations, including the original malicious file that caused the verdict, and all other files affected by the detonation. These attached files might not be directly present in the email. But, including the analysis is important to determining why the file was found to be malicious.
If no detonation chain information is available, the value No detonation tree is shown. Otherwise, you can select
 Export to download the detonation chain information to a CSV file. The default filename is Detonation chain.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Detonation chain(1).csv). The CSV file contains the following information:
Export to download the detonation chain information to a CSV file. The default filename is Detonation chain.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Detonation chain(1).csv). The CSV file contains the following information:- Top: The top level file.
- Level1: The next level file.
- Level2: The next level file.
- and so on.
The detonation chain and the CSV file might show just the top level item if none of the linked entities were found to be problematic or were detonated.
Summary section: If no detonation summary information is available, the value No detonation summary is shown. Otherwise, the following detonation summary information is available:
- Analysis time
- Verdict: The verdict on the attachment itself.
- More info: The file size in bytes.
- Indicators of compromise
Screenshots section: Show any screenshots that were captured during detonation. No screenshots are captured for container files like ZIP or RAR that contain other files.
If no detonation screenshots are available, the value No screenshots to display is shown. Otherwise, select the link to view the screenshot.
Behavior details section: Shows the exact events that took place during detonation, and problematic or benign observations that contain URLs, IPs, domains, and files found during detonation. There might not be any behavior details for container files like ZIP or RAR that contain other files.
If no behavior details information is available, the value No detonation behaviors is shown. Otherwise, you can select
 Export to download the behavioral details information to a CSV file. The default filename is Behavior details.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Behavior details(1).csv). The CSV file contains the following information:
Export to download the behavioral details information to a CSV file. The default filename is Behavior details.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Behavior details(1).csv). The CSV file contains the following information:- Time
- Behavior
- Behavior property
- Process (PID)
- Operation
- Target
- Details
- Result
- File info tab: The File details section contains the following information:
- File name
- SHA256
- File size (in bytes)
When you're finished in the file details flyout, select ![]() Close.
Close.
Block attachments from the Attachments view
If you select an entry in the Attachments view by selecting the check box next to the filename, the ![]() Block action is available. This action adds the file as a block entry in the Tenant Allow/Block List. Selecting Block starts the Take action wizard:
Block action is available. This action adds the file as a block entry in the Tenant Allow/Block List. Selecting Block starts the Take action wizard:
On the Choose actions page, configure one of following settings in the Block file section:
- Never expire on: The default value
 .
. - Never expire off: Slide the toggle to off
 and then select a date in the Remove on box.
and then select a date in the Remove on box.
When you're finished on the Choose actions page, select Next.
- Never expire on: The default value
On the Choose target entities page, verify the file that you want to block is selected, and then select Next.
On the Review and submit page, configure the following settings:
- Remediation name: Enter a unique name to track the status in the Action center.
- Description: Enter an optional description.
When you're finished on the Review and submit page, select Submit.
URL view
The URL view shows information about all original or rewritten URLs in the message, along with the scanning results for each URL.
The following attachment information is available in this view. Select a column header to sort by that column. To add or remove columns, select ![]() Customize columns. By default, all available columns are selected.
Customize columns. By default, all available columns are selected.
- URL
- Threat
- Source
- Details
Use the ![]() Search box to find information on the page. Type text in the box and then press the ENTER key.
Search box to find information on the page. Type text in the box and then press the ENTER key.
Use ![]() Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
URL details
If you select an entry in the URL view by clicking on the URL value, a details flyout opens that contains the following information:
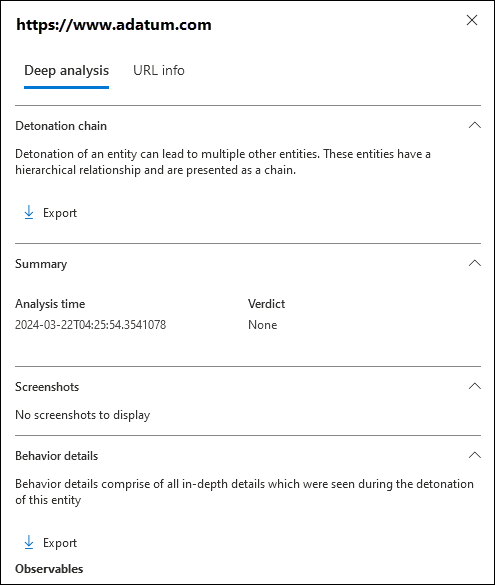
- Deep analysis tab: Information is available on this tab if Safe Links scanned (detonated) the URL and it is identified as malicious through detonation. You can identify these messages in Threat Explorer using the following methods:
Detection technology query filter with the value URL detonation.
Detonation available indicator in the Details column.
The detonation count shown in the Email Summary Panel.
Detonation chain section: Safe Links detonation of a single URL can trigger multiple detonations. The detonation chain tracks the path of detonations, including the original malicious URL that caused the verdict, and all other URLs affected by the detonation. These URLs might not be directly present in the email. But, including the analysis is important to determining why the URL was found to be malicious.
If no detonation chain information is available, the value No detonation tree is shown. Otherwise, you can select
 Export to download the detonation chain information to a CSV file. The default filename is Detonation chain.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Detonation chain(1).csv). The CSV file contains the following information:
Export to download the detonation chain information to a CSV file. The default filename is Detonation chain.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Detonation chain(1).csv). The CSV file contains the following information:- Top: The top level file.
- Level1: The next level file.
- Level2: The next level file.
- and so on.
The detonation chain and the CSV file might show just the top level item if none of the linked entities were found to be problematic or were detonated.
Summary section: If no detonation summary information is available, the value No detonation summary is shown. Otherwise, the following detonation summary information is available:
- Analysis time
- Verdict: The verdict on the URL itself.
Screenshots section: Show any screenshots that were captured during detonation. No screenshots are captured if the URL opens into a link that directly downloads a file. However, you see the downloaded file in the detonation chain.
If no detonation screenshots are available, the value No screenshots to display is shown. Otherwise, select the link to view the screenshot.
Behavior details section: Shows the exact events that took place during detonation, and problematic or benign observations that contain URLs, IPs, domains, and files found during detonation.
If no behavior details information is available, the value No detonation behaviors is shown. Otherwise, you can select
 Export to download the behavioral details information to a CSV file. The default filename is Behavior details.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Behavior details(1).csv). The CSV file contains the following information:
Export to download the behavioral details information to a CSV file. The default filename is Behavior details.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, Behavior details(1).csv). The CSV file contains the following information:- Time
- Behavior
- Behavior property
- Process (PID)
- Operation
- Target
- Details
- Result
- URL info tab: The URL details section contains the following information:
- URL
- Threat
When you're finished in the file details flyout, select ![]() Close.
Close.
Block URLs from the URL view
If you select an entry in the URL view by selecting the check box next to the filename, the ![]() Block action is available. This action adds the URL as a block entry in the Tenant Allow/Block List. Selecting Block starts the Take action wizard:
Block action is available. This action adds the URL as a block entry in the Tenant Allow/Block List. Selecting Block starts the Take action wizard:
On the Choose actions page, configure one of following settings in the Block URL section:
- Never expire on: The default value
 .
. - Never expire off: Slide the toggle to off
 and then select a date in the Remove on box.
and then select a date in the Remove on box.
When you're finished on the Choose actions page, select Next.
- Never expire on: The default value
On the Choose target entities page, verify the URL that you want to block is selected, and then select Next.
On the Review and submit page, configure the following settings:
- Remediation name: Enter a unique name to track the status in the Action center.
- Description: Enter an optional description.
When you're finished on the Review and submit page, select Submit.
Similar emails view
The Similar emails view shows other email messages that have the same message body fingerprint as this message. Matching criteria in other messages doesn't apply for this view (for example, file attachment fingerprints).
The following attachment information is available in this view. Select a column header to sort by that column. To add or remove columns, select ![]() Customize columns. By default, all available columns are selected.
Customize columns. By default, all available columns are selected.
- Date
- Subject
- Recipient
- Sender
- Sender IP
- Override
- Delivery action
- Delivery location
Use ![]() Filter to filter the entries by Start date and End date.
Filter to filter the entries by Start date and End date.
Use the ![]() Search box to find information on the page. Type text in the box and then press the ENTER key.
Search box to find information on the page. Type text in the box and then press the ENTER key.
Use ![]() Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
Export to export the data in the view to a CSV file. The default filename is - Microsoft Defender.csv and the default location is the Downloads folder. If a file with that name already exists, the filename is appended with a number (for example, - Microsoft Defender(1).csv).
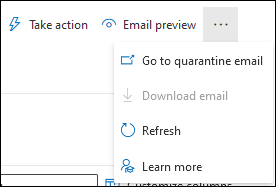
Actions on the Email entity page
The following actions are available at the top of the Email entity page:
 Take action: For information, see Threat hunting: The Take action wizard.
Take action: For information, see Threat hunting: The Take action wizard. Email preview¹ ²
Email preview¹ ² More options:
More options:
 Go to quarantined email: Available only if the message was quarantined. Selecting this action opens the Email tab on the Quarantine page at https://security.microsoft.com/quarantine, filtered by the unique Message ID value of the message. For more information, see View quarantined email.
Go to quarantined email: Available only if the message was quarantined. Selecting this action opens the Email tab on the Quarantine page at https://security.microsoft.com/quarantine, filtered by the unique Message ID value of the message. For more information, see View quarantined email. Download email¹ ²
Download email¹ ²Tip
Download email isn't available for messages that were quarantined. Instead, download a password protected copy of the message from quarantine.
Email preview and Download email actions are available in Audit Logs and CloudAppEvents table of Advanced Hunting (Record type 38) for auditing and reporting.
¹ The Email preview and Download email actions require the Preview role. You can assign this role in the following locations:
- Microsoft Defender XDR Unified role based access control (RBAC) (If Email & collaboration > Defender for Office 365 permissions is
 Active. Affects the Defender portal only, not PowerShell): Security operations/Raw data (email & collaboration)/Email & collaboration content (read).
Active. Affects the Defender portal only, not PowerShell): Security operations/Raw data (email & collaboration)/Email & collaboration content (read). - Email & collaboration permissions in the Microsoft Defender portal: Membership in the Data Investigator or eDiscovery Manager role groups. Or, you can create a new role group with the Preview role assigned, and add the users to the custom role group.
² You can preview or download email messages that are available in cloud mailboxes. Examples of when messages are no longer available in mailboxes include:
- The message was dropped before delivery or delivery failed.
- The message was hard deleted.
- The message has a delivery location of On-prem/External.
- ZAP moved the message to quarantine.
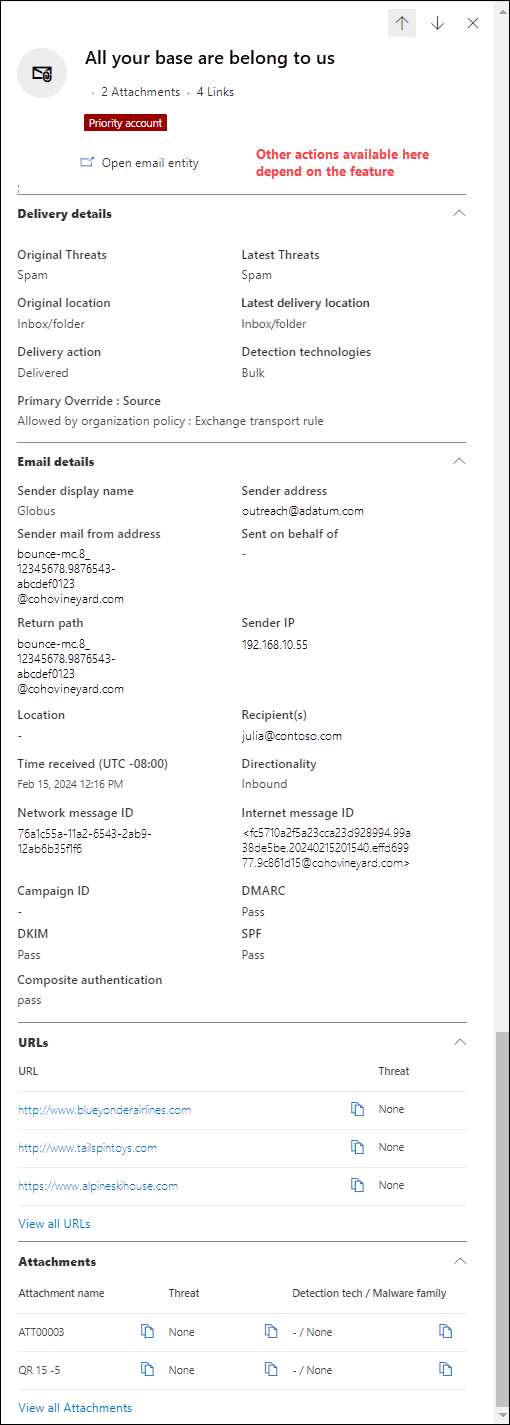
The Email summary panel
The Email summary panel is the email details flyout that's available in many features in the default email protections for cloud mailboxes and in Defender for Office 365. The Email summary panel contains standardized summary information about the email message taken from the full details that are available on the Email entity page in Defender for Office 365.
Where to find the Email summary panel is described in the Where to find the Email entity page section earlier in this article. The rest of this section describes the information that's available on the Email summary panel across all features.
Tip
The Email summary panel is available from the Action center page at https://security.microsoft.com/action-center/ on the Pending or History tabs. Select an action with the Entity type value Email by clicking anywhere in the row other than the check box or the Investigation ID value. The details flyout that opens is the Email summary panel, but ![]() Open email entity isn't available at the top of the flyout.
Open email entity isn't available at the top of the flyout.
The following message information is available at the top of the Email summary panel:
- The title of the flyout is the message Subject value.
- The number of attachments and links in the message (not present in all features).
- Any user tags that are assigned to the recipients of the message (including the Priority account tag). For more information, see User tags in Microsoft Defender for Office 365
- The actions that are available at the top of the flyout depend on where you opened the Email summary panel. The available actions are described in the individual feature articles.
Tip
To see details about other messages without leaving the Email summary panel of the current message, use  Previous item and Next item at the top of the flyout.
Previous item and Next item at the top of the flyout.
The following sections are available on the Email summary panel for all features (it doesn't matter where you opened the Email summary panel from):
Delivery details section:
- Original threats
- Latest threats
- Original location
- Latest delivery location
- Delivery action
- Detection technologies
- Primary override : Source
- Threat classification
Email details section:
- Sender display name
- Sender address
- Sender email from address
- Sent on behalf of
- Return path
- Sender IP
- Location
- Recipient(s)
- Time received
- Directionality
- Network message ID
- Internet message ID
- Campaign ID
- DMARC
- DKIM
- SPF
- Composite authentication
URLs section: Details about any URLs in the message:
- URL
- Threat status
If the message has more than three URLs, select View all URLs to see all of them.
Attachments section: Details about any file attachments in the message:
- Attachment name
- Threat
- Detection tech / Malware family
If the message has more than three attachments, select View all attachments to see all of them.