Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to:
- Microsoft Defender XDR
Important
Some information in this article relates to a prereleased product which may be substantially modified before it's commercially released. Microsoft makes no warranties, expressed or implied, with respect to the information provided here.
Threat analytics is an in-product threat intelligence solution from expert Microsoft security researchers. It helps security teams stay efficient while facing emerging threats, such as:
- Active threat actors and their campaigns
- Popular and new attack techniques
- Critical vulnerabilities
- Common attack surfaces
- Prevalent malware
You can access threat analytics from the upper left-hand side of Microsoft Defender portal's navigation bar, or from a dedicated dashboard card that shows the top threats to your organization, both in terms of known impact and your exposure.
Getting visibility on active or ongoing campaigns and knowing what to do through threat analytics can help equip your security operations team with informed decisions.
With more sophisticated adversaries and new threats emerging frequently and prevalently, it's critical to be able to quickly:
- Identify and react to emerging threats
- Learn if you're currently under attack
- Assess the impact of the threat to your assets
- Review your resilience against or exposure to the threats
- Identify the mitigation, recovery, or prevention actions you can take to stop or contain the threats
Each report provides an analysis of a tracked threat and extensive guidance on how to defend against that threat. It also incorporates data from your network, indicating whether the threat is active and if you have applicable protections in place.
Required roles and permissions
To access Threat analytics in the Defender portal, you need a license for at least one Microsoft Defender XDR product. For more information, see Microsoft Defender XDR prerequisites.
Note
The Microsoft Defender for Endpoint P1 license is an exception to this prerequisite and doesn't grant Threat analytics access.
Microsoft Sentinel SIEM customers have access to certain Threat analytics sections or tabs only. Learn more
The following roles and permissions are also required to access Threat analytics:
- Security data basics (read)—to view threat analytics report, related incidents and alerts, and impacted assets
- Vulnerability management (read) and Exposure Management (read)—to see related exposure data and recommended actions
By default, access to services available in the Defender portal is managed collectively using Microsoft Entra global roles. If you need greater flexibility and control over access to specific product data, and aren't yet using the Microsoft Defender unified role-based access control (RBAC) for centralized permissions management, we recommend creating custom roles for each service. Learn more about creating custom roles
Important
You have visibility to all threat analytics reports even if you have just one of the supported products. However, you need each product and role to see that product's specific incidents, assets, exposure, and recommended actions associated with the threat.
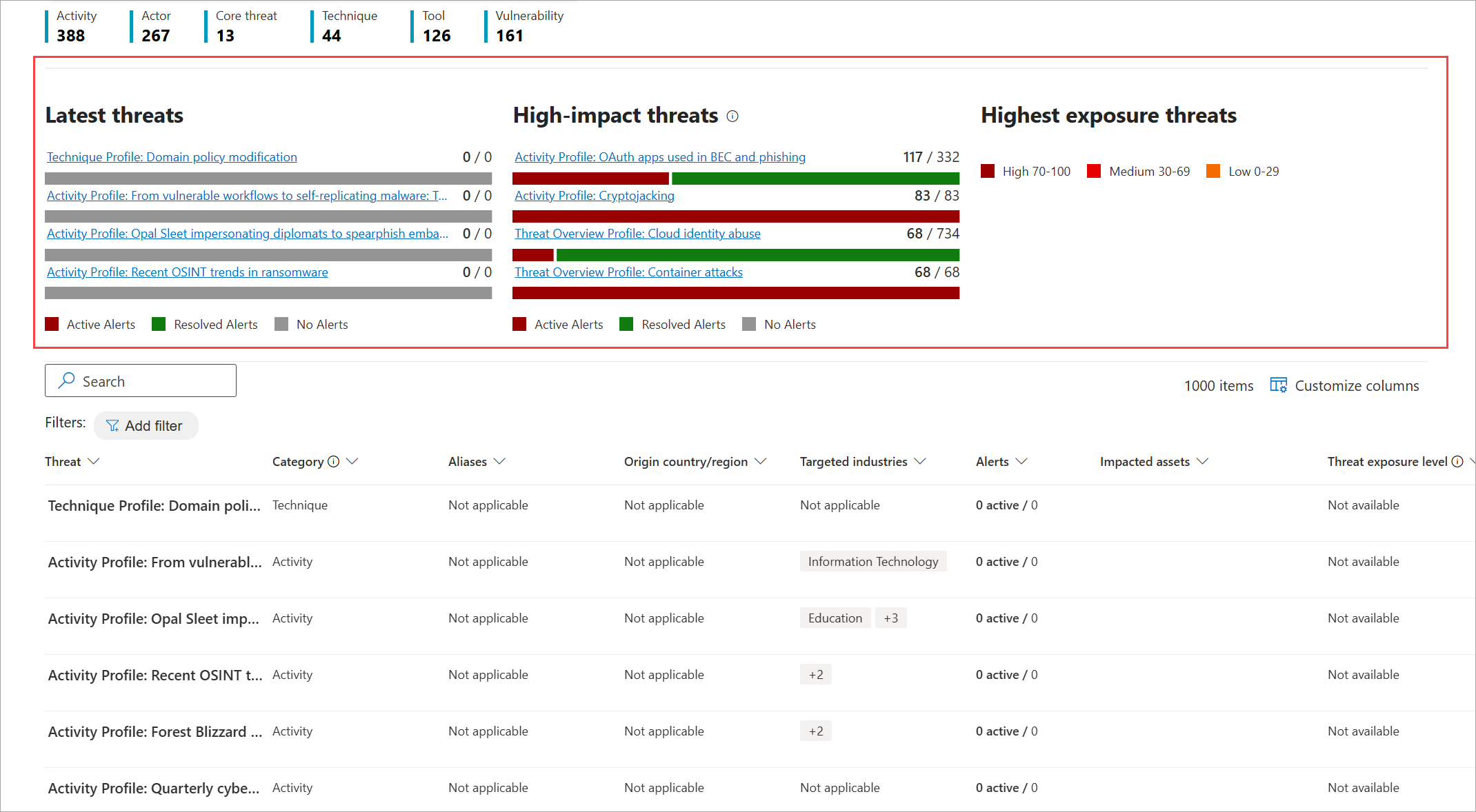
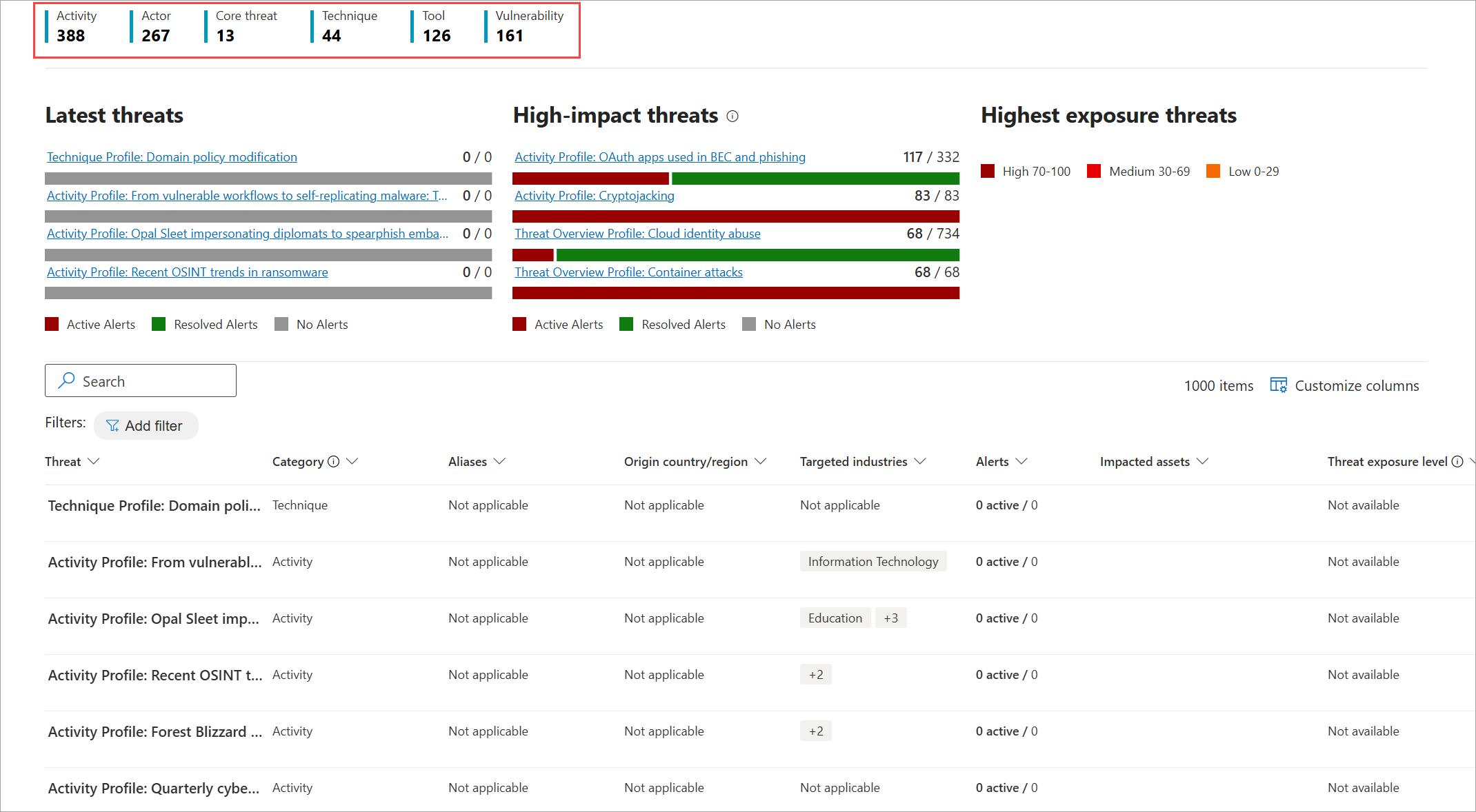
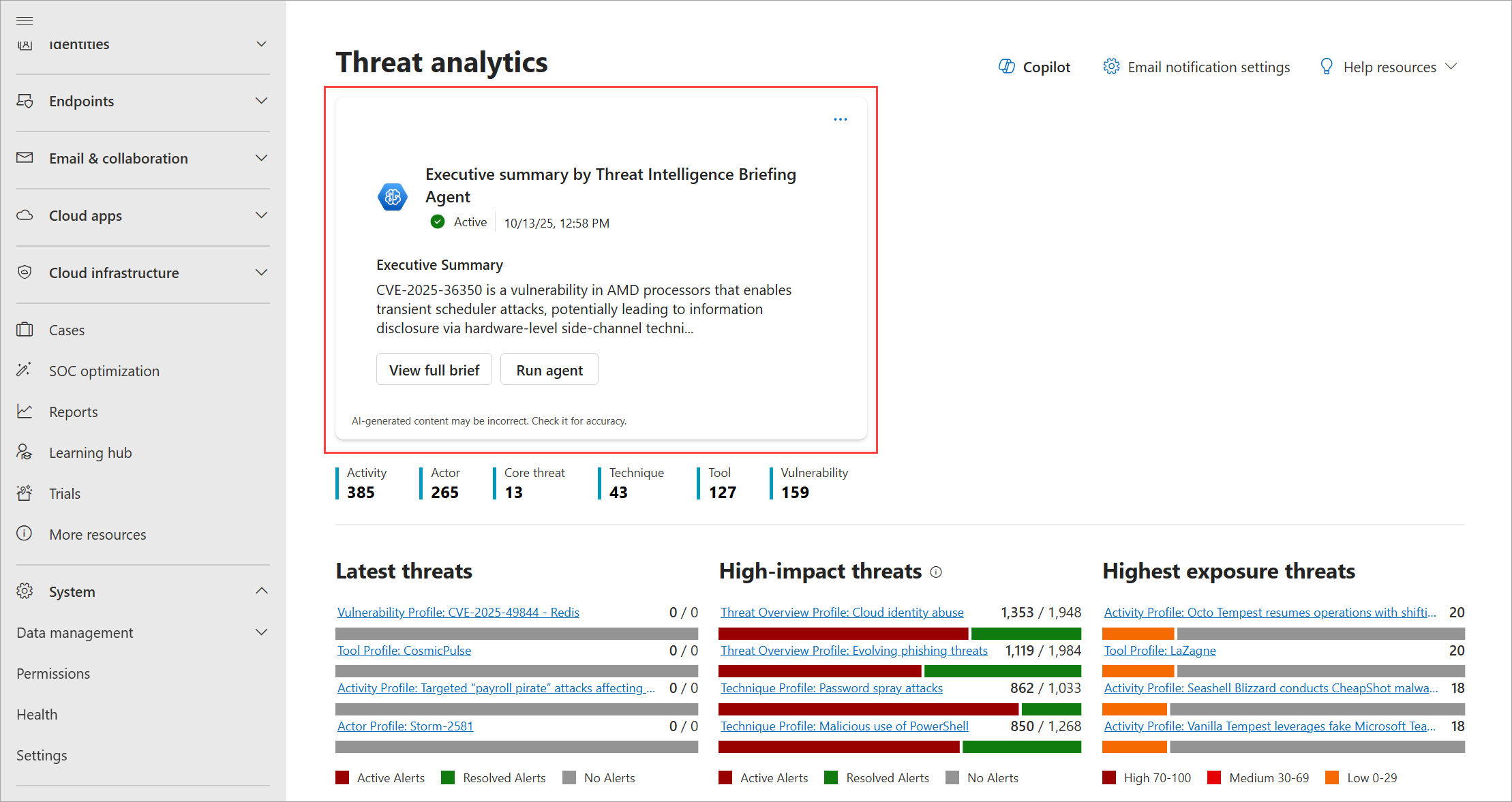
View the threat analytics dashboard
The threat analytics dashboard (security.microsoft.com/threatanalytics3) highlights the reports that are most relevant to your organization. It summarizes the threats in the following sections:
- Latest threats—lists the most recently published or updated threat reports, along with the number of active and resolved alerts.
- High-impact threats—lists the threats that have the highest impact to your organization. This section lists threats with the highest number of active and resolved alerts first.
- Highest exposure threats—lists threats to which your organization has the highest exposure. Your exposure level to a threat is calculated using two pieces of information: how severe the vulnerabilities associated with the threat are, and how many devices in your organization could be exploited by those vulnerabilities.
Select a threat from the dashboard to view the report for that threat. You can also select the Search field to key in a keyword that's related to the threat analytics report that you'd like to read.
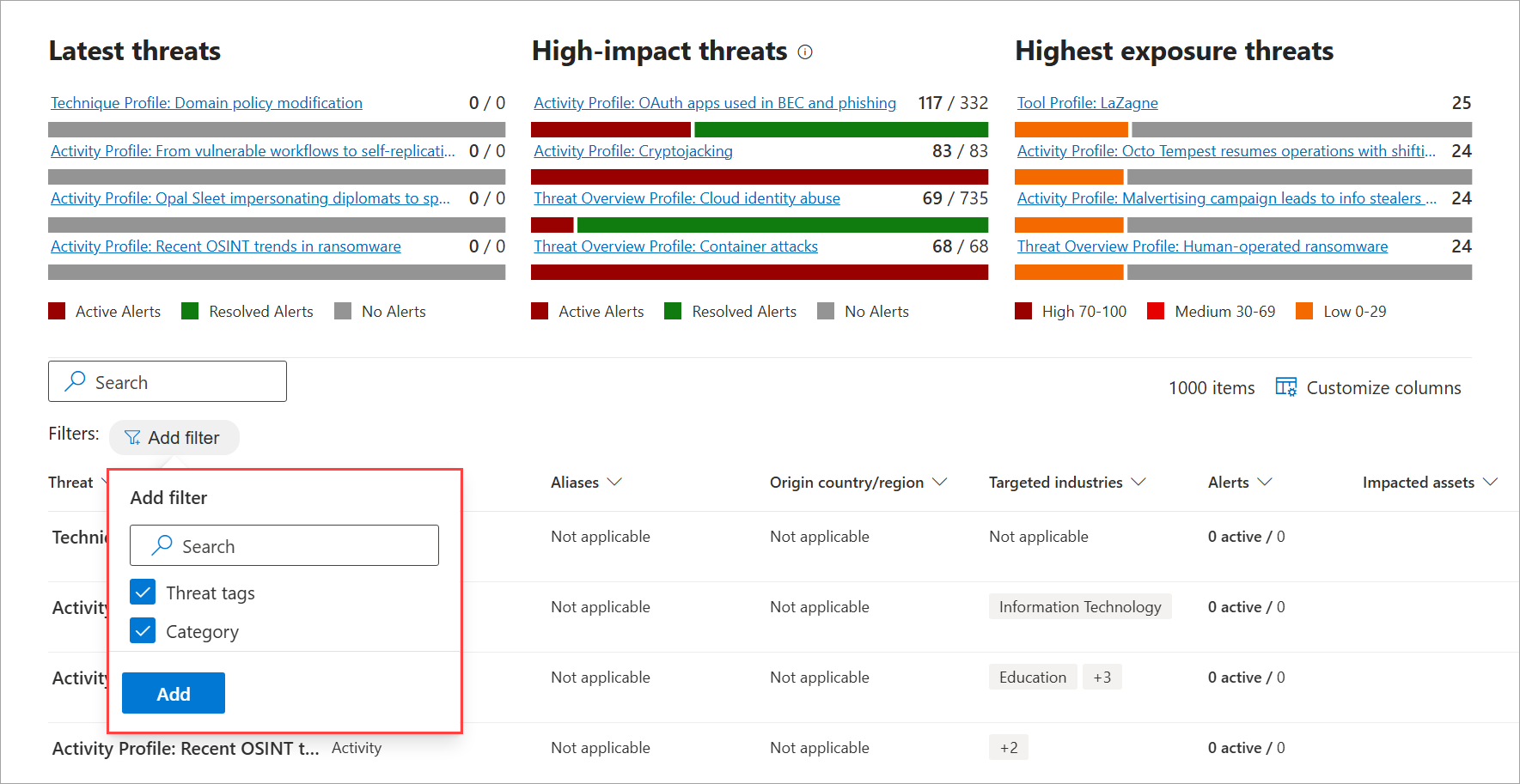
View reports by category
You can filter the threat report list and view the most relevant reports according to the following options:
Threat tags—assist you in viewing the most relevant reports according to a specific threat category. For example, the Ransomware tag includes all reports related to ransomware.
The Microsoft Threat Intelligence team adds threat tags to each threat report. The following threat tags are currently available:
- Ransomware
- Phishing
- Activity group
- Vulnerability
Category—assists you in viewing the most relevant reports according to a specific report type. For example, the Actor category includes all threat actor profiles. Learn more about the different analyst report types
These filters assist you in efficiently reviewing the threat report list. For example, you can view all threat reports related to the ransomware category, or threat reports that involve vulnerabilities.
Categories are presented at the top of the threat analytics page. Counters show the number of available reports under each category.
To add report filter types in your dashboard, select Filters, choose from the list, and select Add.
To set the types of reports you want in the list based on the available filters, select a filter type (for example, Threat tags), choose from the list, and select Apply.
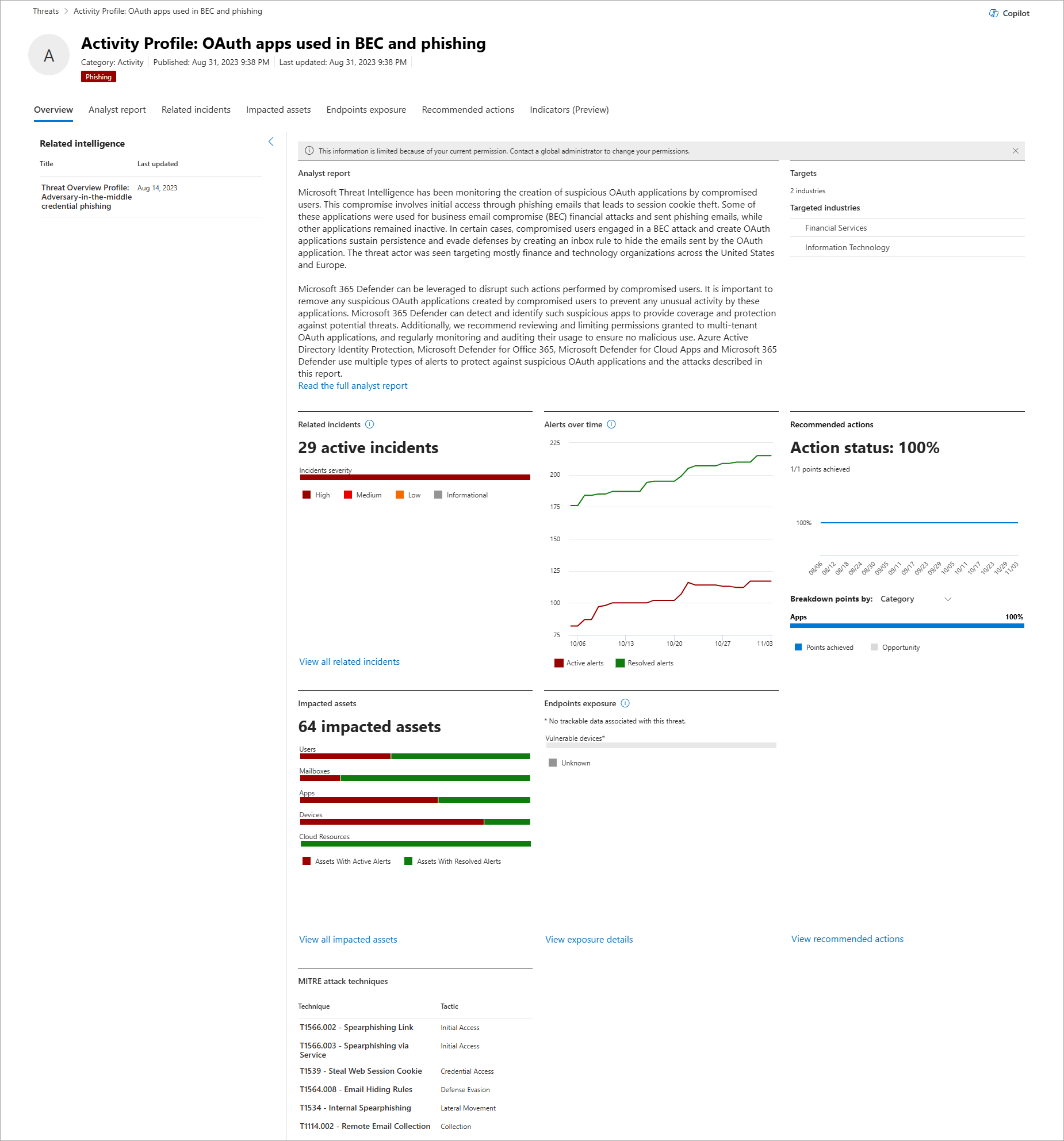
View a threat analytics report
Each threat analytics report provides information in several sections:
- Overview
- Analyst report
- Related incidents
- Impacted assets
- Endpoints exposure
- Recommended actions
- Indicators (preview)
Overview: Quickly understand the threat, assess its impact, and review defenses
The Overview section provides a preview of the detailed analyst report. It also provides charts that highlight the impact of the threat to your organization, and your exposure through misconfigured and unpatched devices.
Understand the threat and its tactics, techniques, and procedures
Each report includes the following details about a threat, whenever applicable or available, providing you a quick glance of what the threat is and how it might impact your organization:
- Aliases—lists the publicly disclosed names given by other security vendors to the threat
- Origin—shows the country or region the threat originated from
- Related intelligence—lists other threat analytics reports that are relevant or related to the threat
- Targets—lists the countries or regions and industries targeted by the threat
- MITRE attack techniques—lists the threat’s observed tactics, techniques, and procedures (TTPs) according to the MITRE ATT&CK framework
Assess impact on your organization
Each report includes charts designed to provide information about the organizational impact of a threat:
- Related incidents—provides an overview of the impact of the tracked threat to your organization with the following data:
- Number of active alerts and the number of active incidents they're associated with
- Severity of active incidents
- Alerts over time—shows the number of related Active and Resolved alerts over time. The number of resolved alerts indicates how quickly your organization responds to alerts associated with a threat. Ideally, the chart should show alerts resolved within a few days.
- Impacted assets—shows the number of distinct assets that currently have at least one active alert associated with the tracked threat. Alerts are triggered for mailboxes that receive threat emails. Review both org- and user-level policies for overrides that cause the delivery of threat emails.
Review security resilience and posture
Each report includes charts that provide an overview of how resilient your organization is against a given threat:
- Recommended actions—shows the Action status percentage, or the number of points you've achieved to improve your security posture. Perform the recommended actions to help address the threat. You can view the breakdown of points by Category or Status.
- Endpoints exposure—shows the number of vulnerable devices. Apply security updates or patches to address vulnerabilities exploited by the threat.
Analyst report: Get expert insight from Microsoft security researchers
In the Analyst report section, you can read through the detailed expert write-up. Most reports provide detailed descriptions of attack chains, including tactics and techniques mapped to the MITRE ATT&CK framework, exhaustive lists of recommendations, and powerful threat hunting guidance.
Learn more about the analyst report
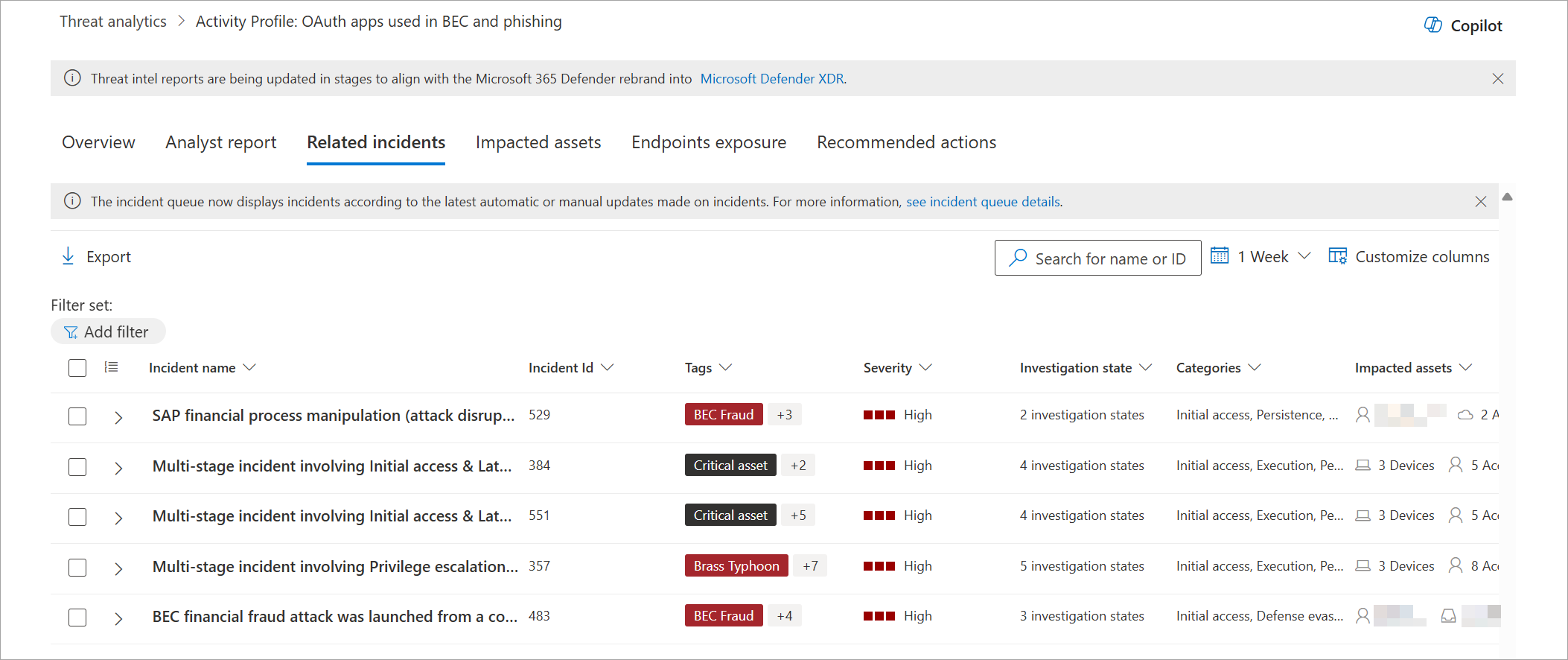
Related incidents: View and manage related incidents
The Related incidents tab provides the list of all incidents related to the tracked threat. You can assign incidents or manage alerts linked to each incident.
Note
Incidents and alerts associated with the threat come from Microsoft Defender for Endpoint, Microsoft Defender for Identity, Microsoft Defender for Office 365, Microsoft Defender for Cloud Apps, and Microsoft Defender for Cloud.
Impacted assets: Get list of impacted devices, users, mailboxes, apps, and cloud resources
The Impacted assets tab shows the assets impacted by the threat over time. It displays:
- Assets affected by active alerts
- Assets affected by resolved alerts
- All assets, or the total number of assets affected by active and resolved alerts
Assets are divided into the following categories:
- Devices
- Users
- Mailboxes
- Apps
- Cloud resources
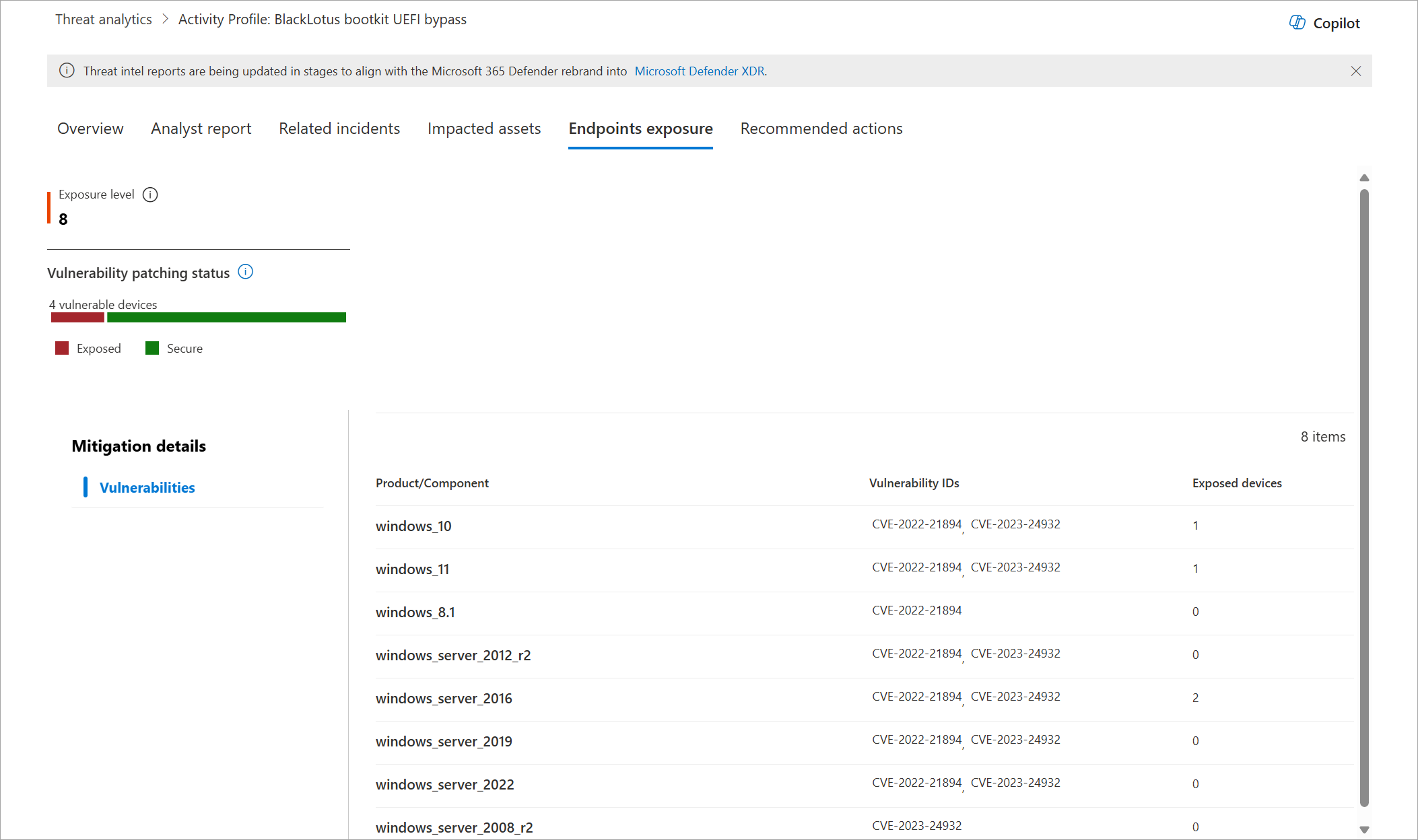
Endpoints exposure: Know the deployment status of security updates
The Endpoints exposure section provides your organization's Exposure level to the threat. The exposure level is calculated based on the severity of the vulnerabilities and misconfigurations that the threat exploits, and the number of devices with these weaknesses.
This section also provides the deployment status of supported software security updates for vulnerabilities found on onboarded devices. It incorporates data from Microsoft Defender Vulnerability Management, which also provides detailed drill-down information from various links in the report.
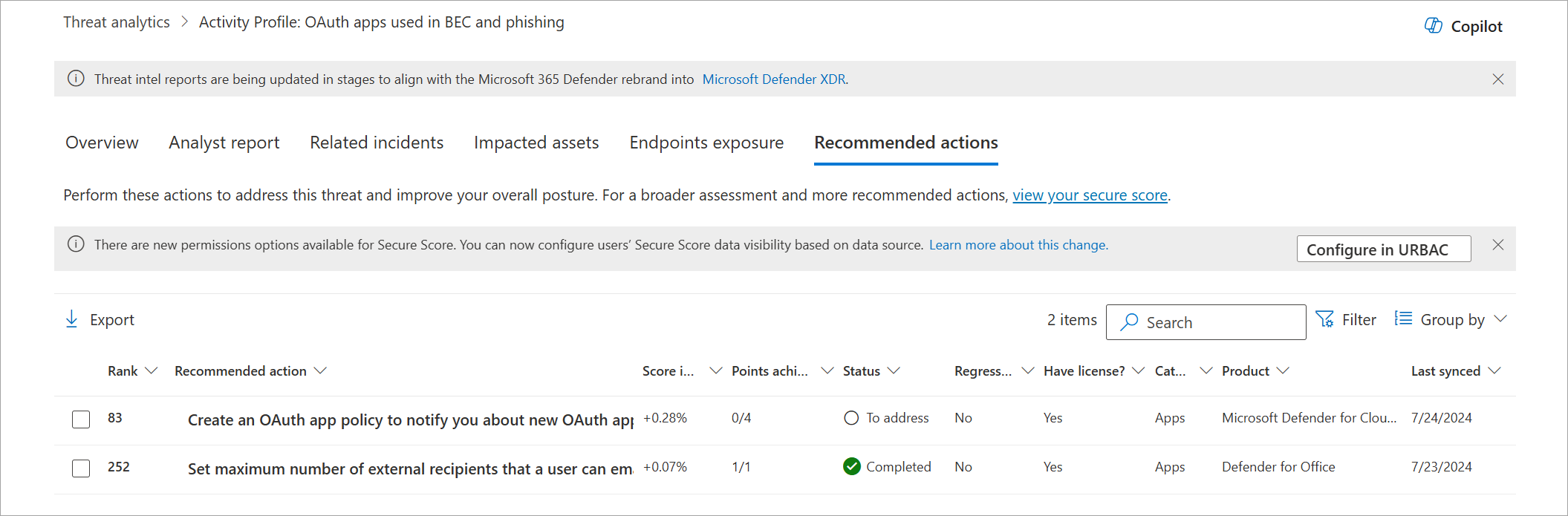
Recommended actions: Review list of mitigations and the status of your devices
In the Recommended actions tab, review the list of specific actionable recommendations that can help you increase your organizational resilience against the threat. The list of tracked mitigations includes supported security configurations, such as:
- Cloud-delivered protection
- Potentially unwanted application (PUA) protection
- Real-time protection
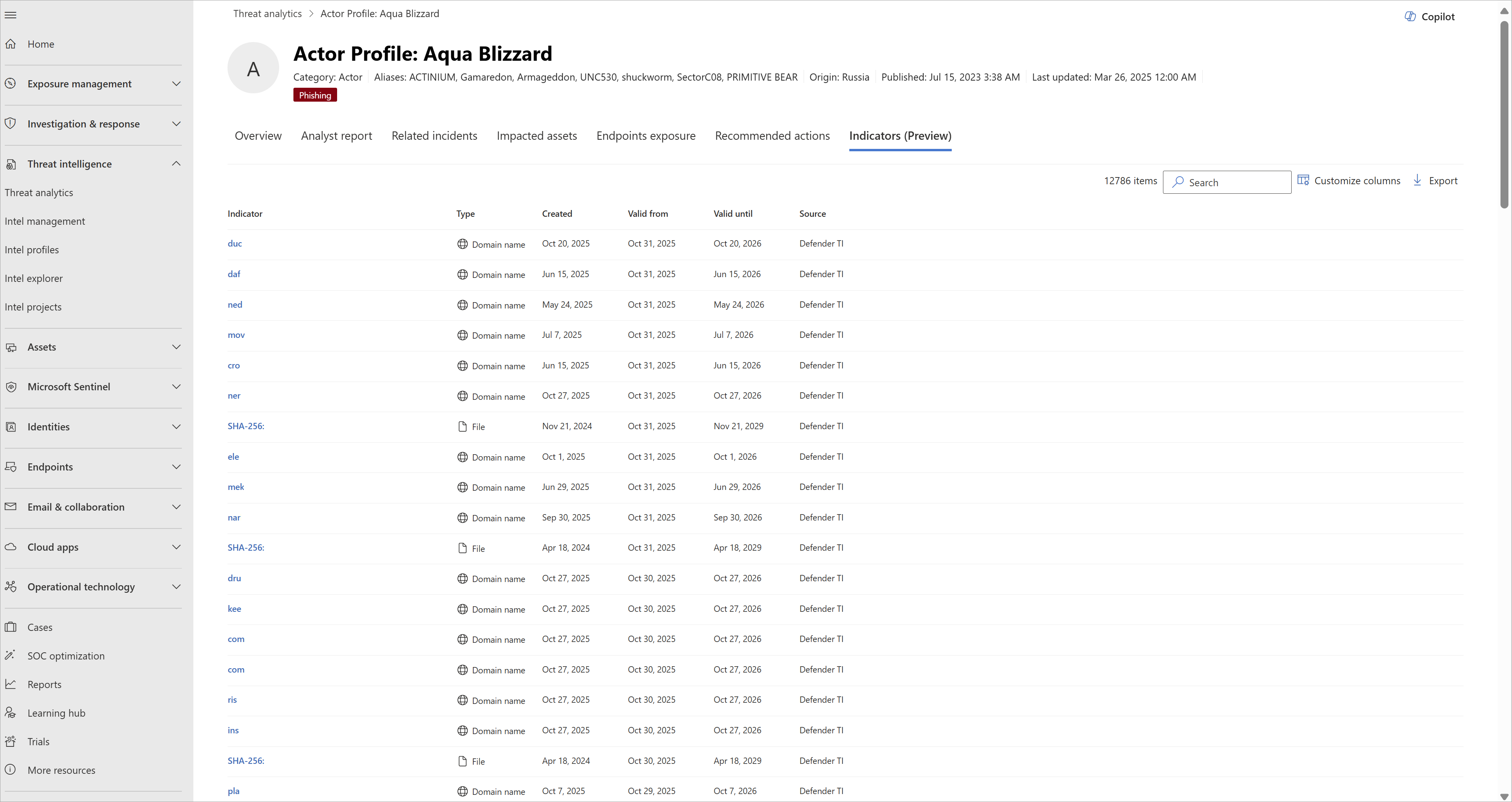
Indicators: View specific infrastructure and evidence behind the threat (preview)
The Indicators tab provides a list of all indicators of compromise (IOCs) associated with the threat. Microsoft researchers update these IOCs in real time as they find new evidence related to the threat. This information helps your security operations center (SOC) and threat intelligence analysts with remediation and proactive hunting. The list also retains expired IOCs, so you can investigate past threats and understand their impact in your environment.
Important
Only verified customers can access the information in the Indicators tab. If you don't have access to this information, you need to verify your tenant. Learn more about getting access to IOCs
Stay updated with the latest reports and threat intelligence
Threat analytics leverages and integrates various Microsoft Defender and Microsoft Security Copilot features to keep you and your SOC team updated whenever a new report or new piece of threat intelligence relevant to your environment becomes available.
Set up the Threat Intelligence Briefing Agent
Set up the Threat Intelligence Briefing Agent to get timely, relevant threat intelligence reports with detailed technical analysis based on the latest threat actor activity and both internal and external vulnerability exposure. The agent correlates Microsoft threat data and customer signals to add critical context to threat information in a matter of minutes, saving analyst teams hours or even days spent on intelligence gathering and correlation.
Once deployed, the Threat Intelligence Briefing Agent appears as a banner at the top of the Threat analytics page.
Learn more about the Threat Intelligence Briefing Agent
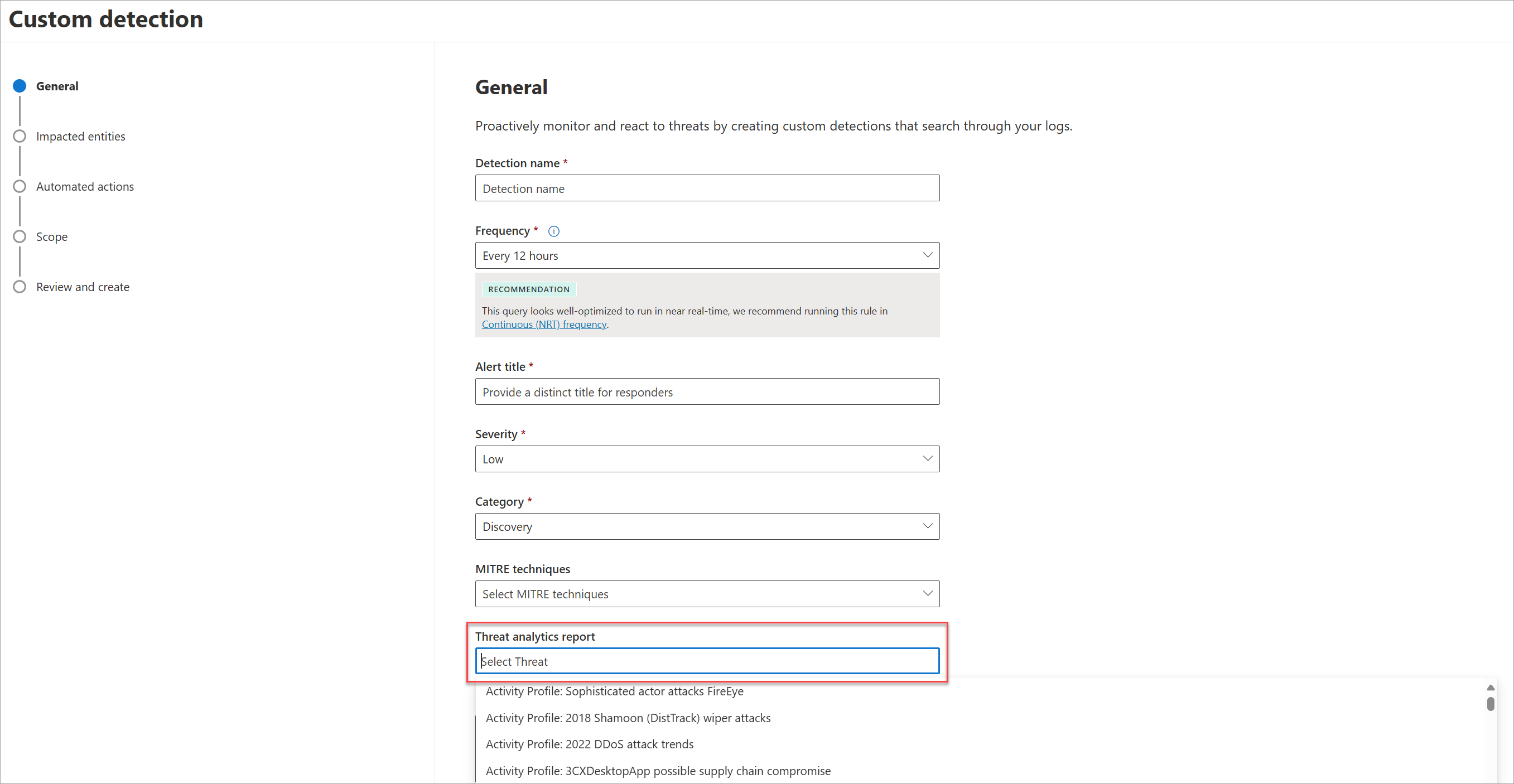
Set up custom detections and link them to Threat analytics reports
Set up custom detection rules and link them to Threat analytics reports. If these rules get triggered and an alert generates an incident, the report shows up in that incident and the incident appears under the Related incidents tab, just like any other Microsoft-defined detection.
Learn more about creating and managing custom detections rules
Set up email notifications for report updates
Set up email notifications that send you updates on Threat analytics reports. To create email notifications, follow the steps in get email notifications for Threat analytics updates in Microsoft Defender XDR.
Other report details and limitations
When you review the threat analytics data, consider the following factors:
- The checklist in the Recommended actions tab only displays recommendations tracked in Microsoft Secure Score. Check the Analyst report tab for more recommended actions that aren't tracked in Secure Score.
- The recommended actions don't guarantee complete resilience and only reflect the best possible actions needed to improve it.
- Antivirus-related statistics are based on Microsoft Defender Antivirus settings.
- The Misconfigured devices column in the main Threat analytics page shows the number of devices affected by a threat when the threat's related recommended actions aren't turned on. However, if Microsoft researchers don't link any recommended actions, the Misconfigured devices column shows the status Not available.
- The Vulnerable devices column in the main Threat analytics page shows the number of devices running software that are vulnerable to any of the vulnerabilities linked to the threat. However, if Microsoft researchers don't link any vulnerabilities, the Vulnerable devices column shows the status Not available.
See also
- Proactively find threats with advanced hunting
- Understand the analyst report section
- Assess and resolve security weaknesses and exposures
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.