Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Note
Azure Active Directory is now Microsoft Entra ID. Learn more
Starting with the Dynamics GP October 2020 release, you will have the ability to use Multi-Factor Authentication for e-mail functionality. This new feature relies on a Microsoft Entra ID App Registration. In this first section we will go over how to perform the Azure side the of the configuration.
Register the app
First, you'll need to have an administrator who can log into the Azure Portal.
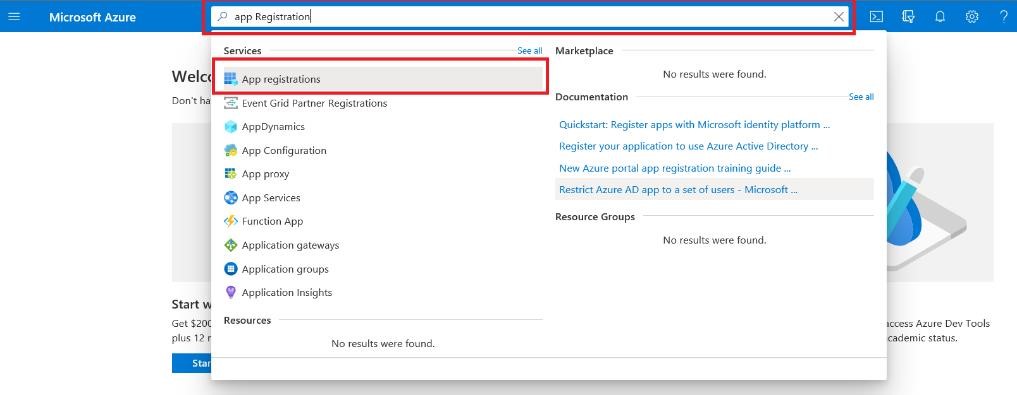
In the search box, type App Registration and select that option:
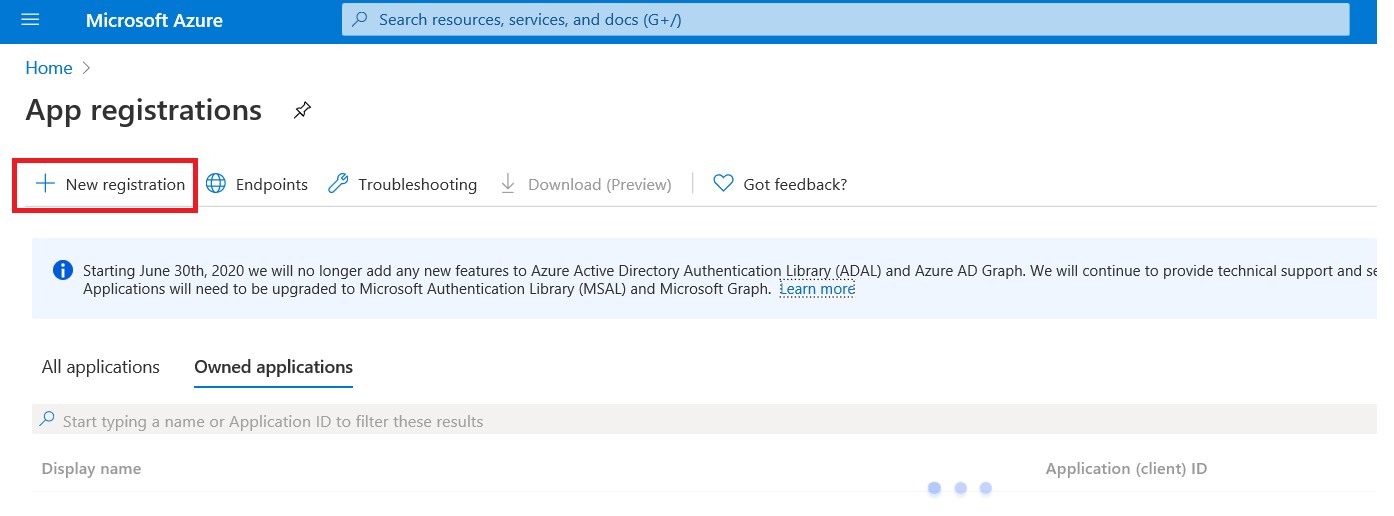
Click on New Registration as shown in the below screenshot:
You will then choose settings for your new application.
- Enter a display name for the application (e.g. GPMFAApp)
- For Supported account types prior to the Fall 2023 (18.6) release, you were limited to the second option (Account in any organizational directory (Any Microsoft Entra ID account – Multitenant)). If you are on 18.6 or later, you can also use the (Account in this organizational directory only (%domain% only - Single tenant)) option. Choosing the wrong option can lead to an Unknown Error when using MFA in Dynamics GP.
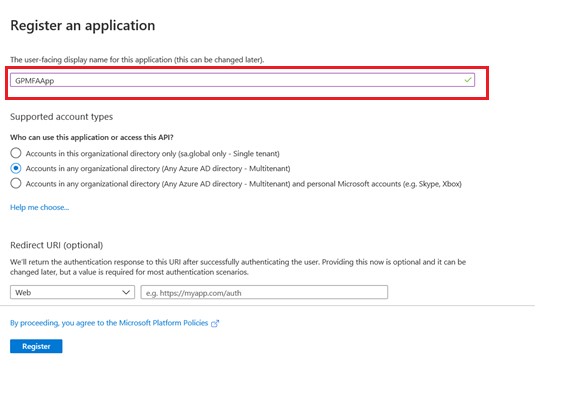
Click on Register button.
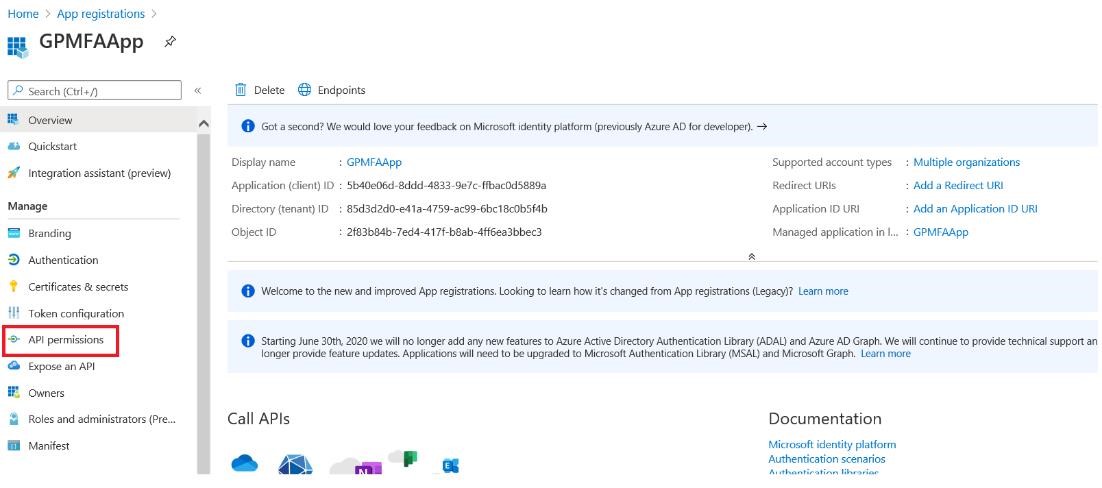
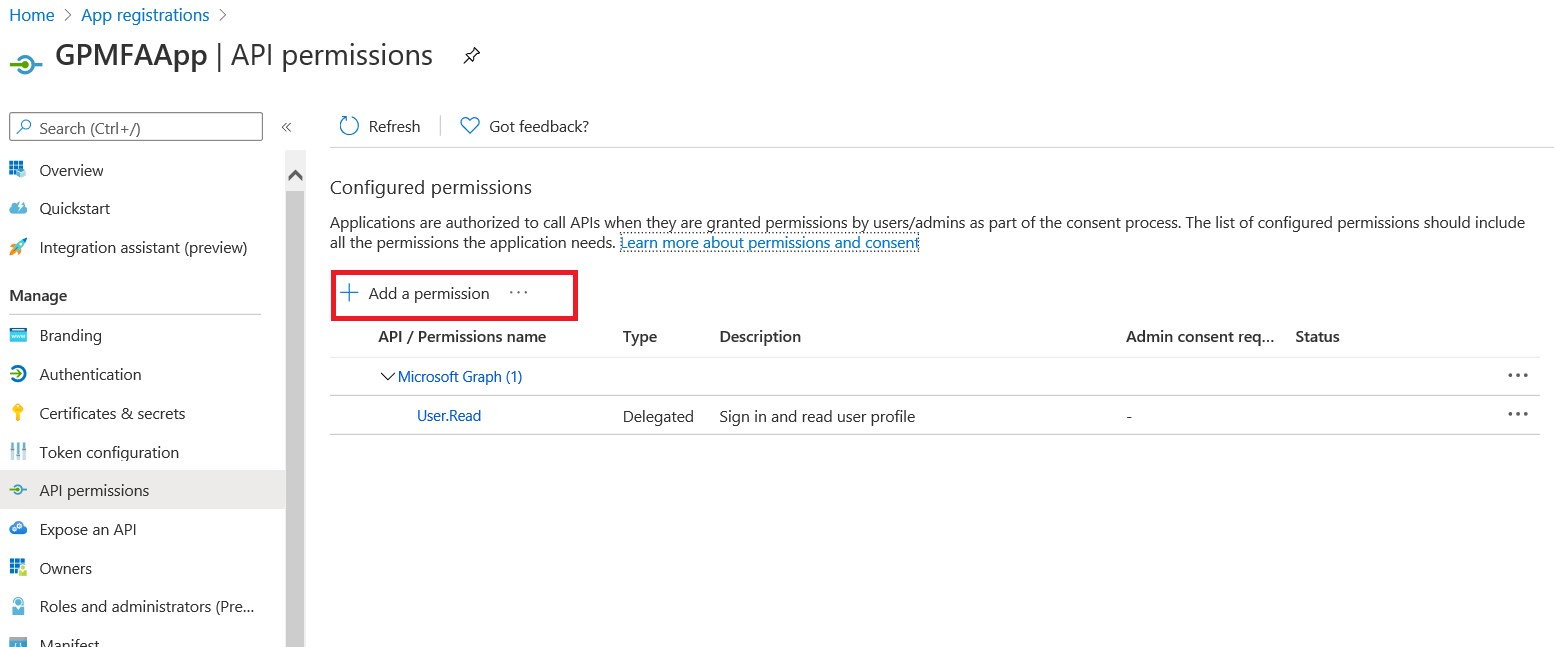
Click on API Permission on the left side panel as shown in the screenshot.
Click on Add permission button.
Microsoft Graph – By default, Microsoft Graph application will have read permission for the user profile. To allow a Graph application to send an email, we need to add some specific permissions.
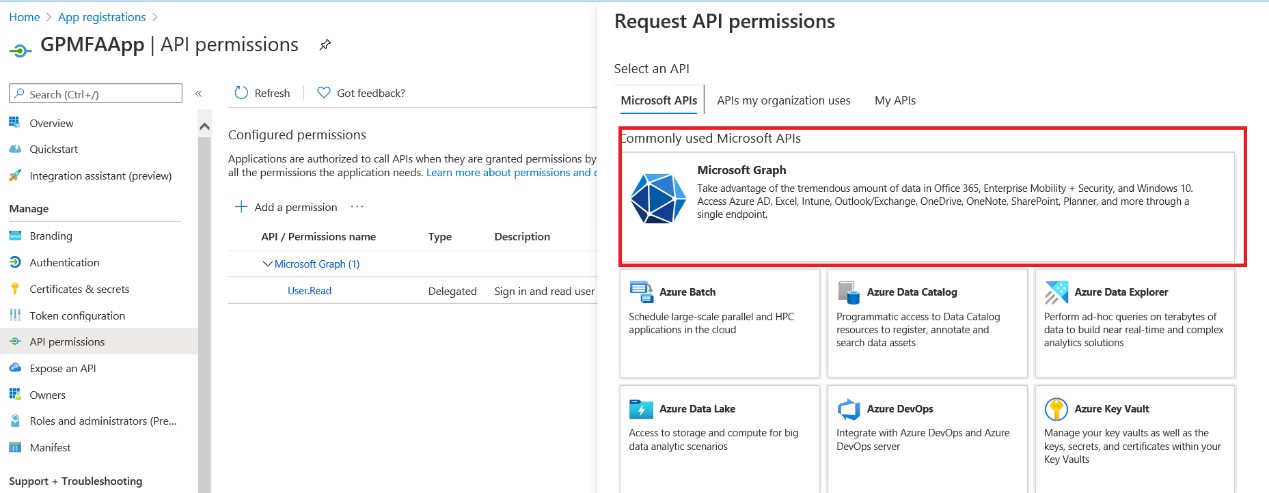
Click on "Delegated permissions".
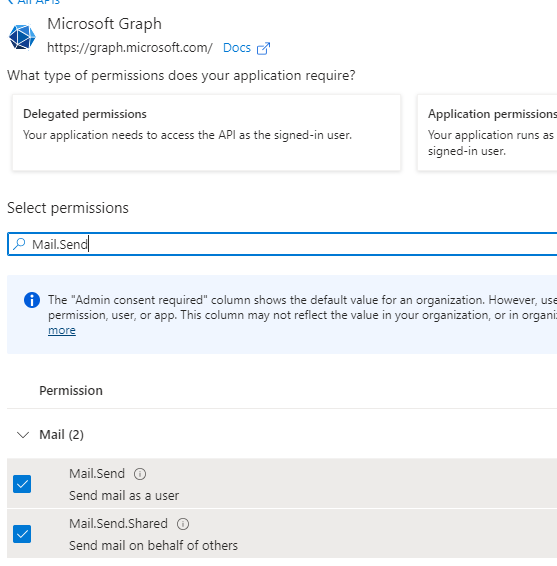
Search for "Mail.Send" in the Select permission search box.
Mark the "Mail.Send" and "Mail.Send.Shared" checkboxes and click on Add permissions.
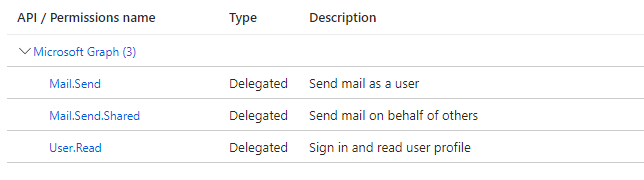
Mail.Send and Mail.Send.Shared permissions will be added under Microsoft Graph.
Click on "Authentication" on the left panel under Manage option.
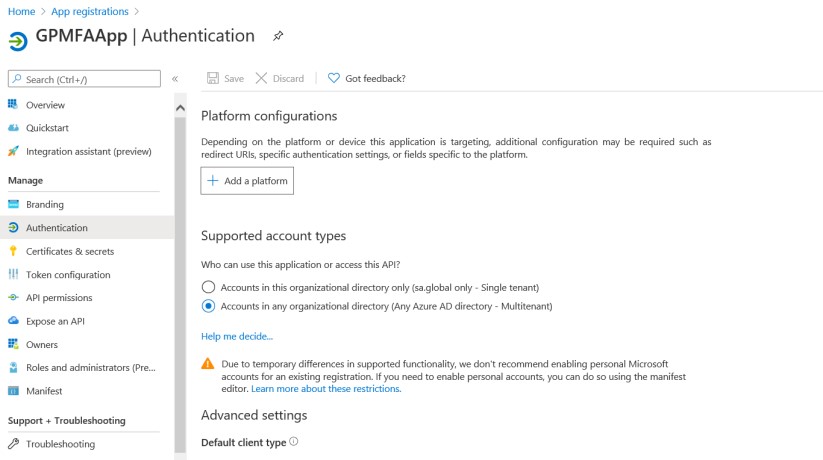
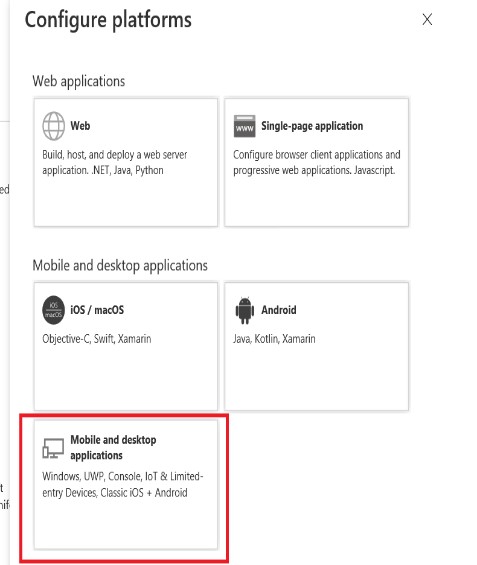
Click on "+Add Platform" and select "Mobile and desktop applications".
Enter the value "urn:ietf:wg:oauth:2.0:oob" in the Custom Redirect URIs text box as shown in the screen shot. This uri will redirect to the original application.
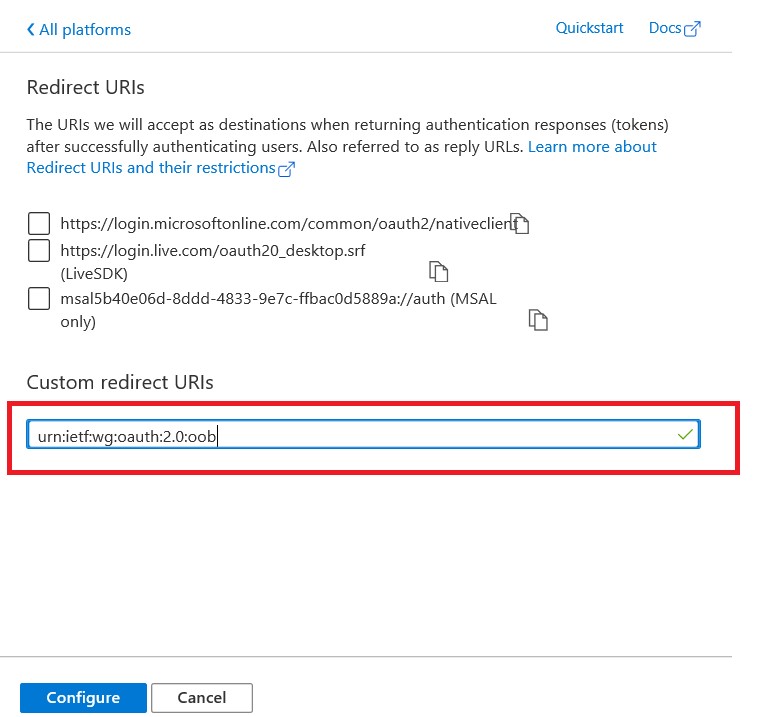
Click on Configure button
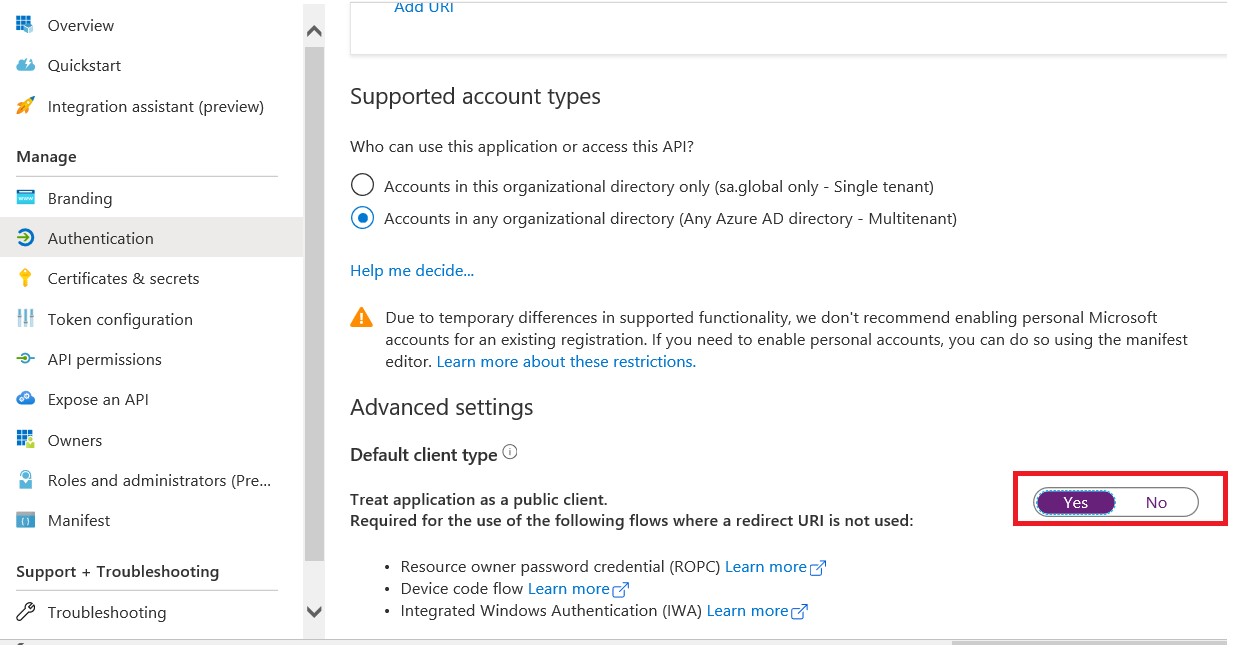
Save the changes for the application.
Note
Multi-Factor (Modern Auth) Authentication is supported in Web Client with 18.5 release or later. Refer to Web Client setup with Modern Auth
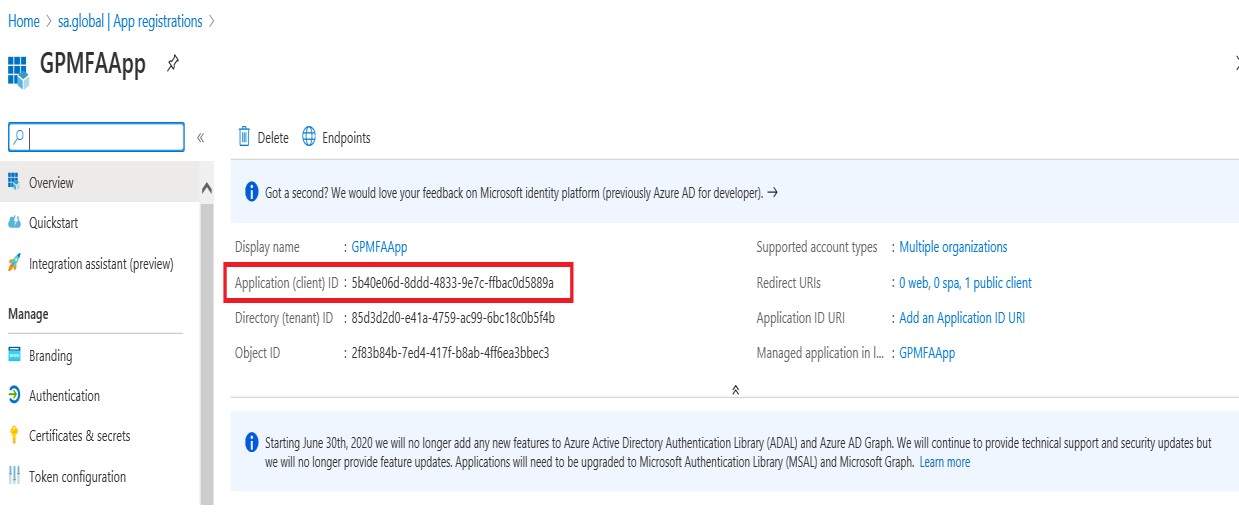
Click on Overview on the left side pane. The Application (client) ID will be used in the Microsoft Dynamics GP client.
From the setup that was done in Azure, now launch Microsoft Dynamics GP 18.3 or later and go to Tools, Select Setup, choose Company and click Company E-mail Setup. Enter the Application (Client) ID into this Desktop Properties section of this window.
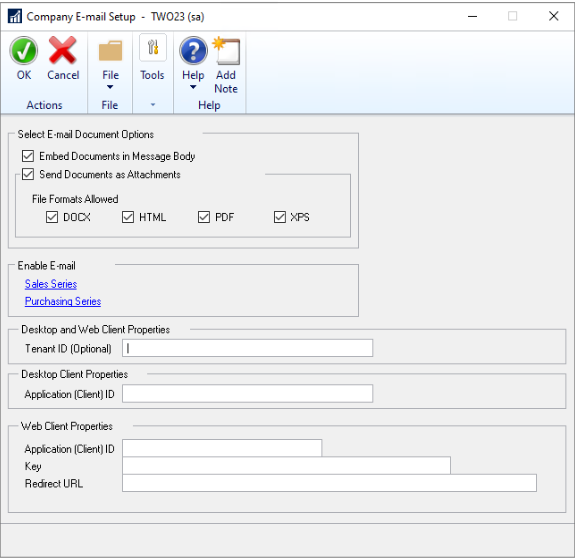
If you're using a Single tenant app registration you will also need to pull the Directory (Tenant) ID from the aboeve Overview window and enter that into the Tenant ID field.
Note
There is a new column (MSGraphClientID) added to the company table SY04900, syEmailSetupOptions.