Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article helps you understand and improve the security of your Business Central installation regardless of where it's hosted. It includes guidance and recommended practices related to authentication, authorization, and auditing. It also touches on data encryption and secure development practices that can be applied to any Business Central environment.
Business Central uses a layered approach to application security, as outlined in the following diagram.
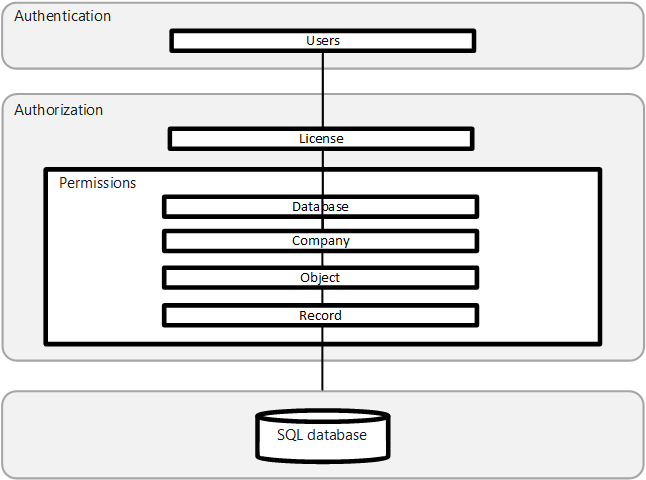
Authentication
Before users can sign in to the Business Central application, they must be authenticated as a valid user in the system. Business Central (on-premises) supports several authentication methods, such as Windows and Microsoft Entra ID. Business Central online deployments use Microsoft Entra ID only. Learn more in the following articles:
Managing Users and Permissions
Audit user administration events in Microsoft Purview
Set up Business Central Access with Microsoft 365 Licenses
Authentication and Credential Types (on-premises only)
Set up Multifactor Authentication (MFA)
The authentication method configured for Business Central Server is also used to access web services. Learn more in Web Services Authentication.
Authorization
After a user is authenticated, authorization determines which areas the user can access. For example, it determines the pages and reports a user can open and the permissions they have on associated data. Learn more in the following articles:
User Permissions in the Application
Audit permission administration events in Microsoft Purview
Analyzing Permission Changes Trace Telemetry
Removing Elements from the User Interface According to Permissions
Analyzing Authorization Telemetry
Using OAuth to Authorize Business Central Web Services
Note
After successful authentication, Business Central allows a user in only if they exist in the environment and have permission to the company or data they're trying to access. In other words, being a licensed in Microsoft Entra ID isn't enough—the user must also be set up inside Business Central with appropriate access.
Data encryption
You can encrypt data on the Business Central server by generating new encryption keys—or importing existing ones—that you enable on the Business Central server instance that connects to the database. Learn more in Encrypting Data in Dynamics 365 Business Central.
Security development lifecycle
The Microsoft Security Development Lifecycle (SDL) is a software development process that helps developers build more secure software. SDL addresses security compliance requirements while reducing development cost. Learn more in Security Development Lifecycle.
Auditing data fields
For a comprehensive audit trail of data changes, Business Central offers a change log feature. When the change log is enabled enabled for specific tables/fields, it records every insertion, modification, or deletion (including the old and new values, user, and timestamp).
This information is useful for compliance and investigations. However, be mindful of performance. Enable it only on the records that truly need detailed tracking. For instance, avoid logging every change on large ledger entry tables, because these changes are append-only by nature.
Learn more about the change log in Audit changes.
Tip
Instead of the change log, you can use Business Central's analysis mode on any list page. Add the system fields (Created/Modified date and user) to the list (they can be hidden), then turn on analysis mode. With these fields present, the analysis mode (and Copilot) can help summarize recent changes to the data in that list—giving you a lightweight audit view.
Sensitive field monitoring with email alerts
Admins can set up monitoring of specific fields in Business Central, letting you flag fields as sensitive. If these fields are changed, the system can send an email alert to designated recipients and emit telemetry about the change. For example, you might monitor the bank account number field on a vendor card. This way, any change triggers an immediate alert, helping you quickly catch potential fraud attempts.
Tip
Sensitive field monitoring has significantly less performance impact than the change log feature, making it a recommended alternative. Use it to track critical fields without the overhead of logging every change across entire tables.
Learn more in Monitor sensitive fields and Analyzing field monitoring telemetry.
Related information
Security and Protection
Security Tips for Business Users
Online Security
on-premises Security