Configure federated sign-in for Windows devices
Starting in Windows 11 SE, version 22H2 and Windows 11 Pro Edu/Education, version 22H2 with KB5022913, you can enable your users to sign-in using a federated identity provider (IdP) via a web sign-in experience. Signing in with a federated identity can be a great way to simplify the sign-in process for your users: instead of having to remember a username and password defined in Microsoft Entra ID, they can sign-in using their existing credentials from the IdP. For example, students and educators can use QR code badges to sign-in.
Benefits of federated sign-in
A federated sign-in experience enables students to sign-in in less time, and with less friction. With fewer credentials to remember and a simplified sign-in process, students are more engaged and focused on learning.
There are two Windows features that enable a federated sign-in experience:
- Federated sign-in, which is designed for 1:1 student devices. For an optimal experience, you should not enable federated sign-in on shared devices
- Web sign-in, which provides a similar experience to Federated sign-in, and can be used for shared devices
Important
Federated sign-in and Web sign-in require different configurations, which are explained in this document.
Prerequisites
To enable a federated sign-in experience, the following prerequisites must be met:
A Microsoft Entra tenant, with one or multiple domains federated to a third-party IdP. For more information, see What is federation with Microsoft Entra ID? and Use a SAML 2.0 IdP for Single Sign On
Note
If your organization uses a third-party federation solution, you can configure single sign-on to Microsoft Entra ID if the solution is compatible with Microsoft Entra ID. For questions regarding compatibility, contact your identity provider. If you're an IdP, and would like to validate your solution for interoperability, refer to these guidelines.
- For a step-by-step guide on how to configure Google Workspace as an identity provider for Microsoft Entra ID, see Configure federation between Google Workspace and Microsoft Entra ID
- For a step-by-step guide on how to configure Clever as an identity provider for Microsoft Entra ID, see Setup guide for Badges into Windows and Microsoft Entra ID
Individual IdP accounts created: each user requires an account defined in the third-party IdP platform
Individual Microsoft Entra accounts created: each user requires a matching account defined in Microsoft Entra ID. These accounts are commonly created through automated solutions, for example:
- School Data Sync (SDS)
- Microsoft Entra Connect Sync for environment with on-premises AD DS
- PowerShell scripts that call the Microsoft Graph API
- provisioning tools offered by the IdP
For more information about identity matching, see Identity matching in Microsoft Entra ID.
Licenses assigned to the Microsoft Entra user accounts. It's recommended to assign licenses to a dynamic group: when new users are provisioned in Microsoft Entra ID, the licenses are automatically assigned. For more information, see Assign licenses to users by group membership in Microsoft Entra ID
Enable Federated sign-in or Web sign-in on the Windows devices, depending if the devices are shared or assigned to a single student
To use Federated sign-in or Web sign-in, the devices must have Internet access. These features don't work without it, as the authentication is done over the Internet.
Important
WS-Fed is the only supported federated protocol to join a device to Microsoft Entra ID. If you have a SAML 2.0 IdP, it's recommended to complete the Microsoft Entra join process using one of the following methods:
- Provisioning packages (PPKG)
- Windows Autopilot self-deploying mode
Windows edition and licensing requirements
The following table lists the Windows editions that support Federated sign-in:
| Windows Pro | Windows Enterprise | Windows Pro Education/SE | Windows Education |
|---|---|---|---|
| No | No | Yes | Yes |
Federated sign-in license entitlements are granted by the following licenses:
| Windows Pro Education/SE | Windows Enterprise E3 | Windows Enterprise E5 | Windows Education A3 | Windows Education A5 |
|---|---|---|---|---|
| Yes | No | No | Yes | Yes |
For more information about Windows licensing, see Windows licensing overview.
Federated sign-in is supported on the following Windows editions and versions:
- Windows 11 SE, version 22H2 and later
- Windows 11 Pro Edu/Education, version 22H2 with KB5022913
Web sign-in is supported starting in Windows 11 SE/Pro Edu/Education, version 22H2 with KB5026446.
Configure a federated sign-in experience
You can configure a federated sign-in experience for student assigned (1:1) devices or student shared devices:
- When federated sign-in is configured for student assigned (1:1) devices, you use a Windows feature called Federated sign-in. The first user who signs in to the device with a federated identity becomes the primary user. The primary user is always displayed in the bottom left corner of the sign-in screen
- When federated sign-in is configured for student shared devices, you use a Windows feature called Web sign-in. With Web sign-in there's no primary user, and the sign-in screen displays, by default, the last user who signed in to the device
The configuration is different for each scenario, and is described in the following sections.
Configure Federated sign-in for student assigned (1:1) devices
Review the following instructions to configure your devices using either Microsoft Intune or a provisioning package (PPKG).
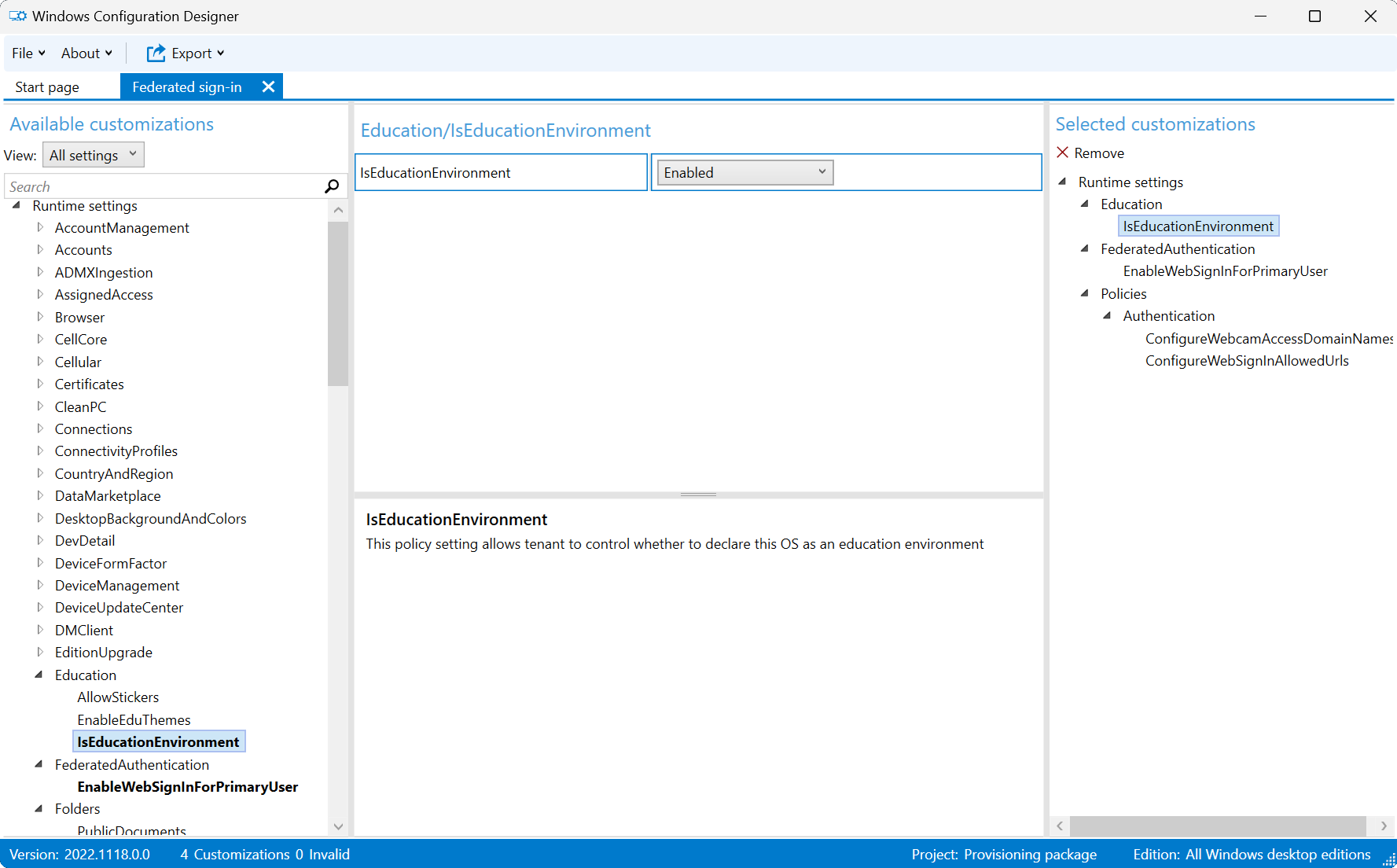
To configure devices with Microsoft Intune, create a Settings catalog policy and use the following settings:
| Category | Setting name | Value |
|---|---|---|
| Education | Is Education Environment | Enabled |
| Federated Authentication | Enable Web Sign In For Primary User | Enabled |
| Authentication | Configure Web Sign In Allowed Urls | Enter the list of domains, with each URL in a separate row. For example: - samlidp.clever.com- clever.com- mobile-redirector.clever.com |
| Authentication | Configure Webcam Access Domain Names | This setting is optional, and it should be configured if you need to use the webcam during the sign-in process. Specify the list of domains that are allowed to use the webcam during the sign-in process, separated by a semicolon. For example: clever.com |
Assign the policy to a group that contains as members the devices or users that you want to configure.
Alternatively, you can configure devices using a custom policy with the following settings:
| Setting |
|---|
OMA-URI: ./Vendor/MSFT/Policy/Config/Education/IsEducationEnvironmentData type: int Value: 1 |
OMA-URI: ./Vendor/MSFT/Policy/Config/FederatedAuthentication/EnableWebSignInForPrimaryUserData type: int Value: 1 |
OMA-URI: ./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebSignInAllowedUrlsData type: String Value: Semicolon separated list of domains, for example: samlidp.clever.com;clever.com;mobile-redirector.clever.com |
OMA-URI: ./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebCamAccessDomainNames** Data type: String Value: This setting is optional, and it should be configured if you need to use the webcam during the sign-in process. Specify the list of domains that are allowed to use the webcam during the sign-in process, separated by a semicolon. For example: clever.com |
Configure Web sign-in for student shared devices
Review the following instructions to configure your shared devices using either Microsoft Intune or a provisioning package (PPKG).
To configure devices with Microsoft Intune, create a Settings catalog policy and use the following settings:
| Category | Setting name | Value |
|---|---|---|
| Education | Is Education Environment | Enabled |
| SharedPC | Enable Shared PC Mode With OneDrive Sync | True |
| Authentication | Enable Web Sign In | Enabled |
| Authentication | Configure Web Sign In Allowed Urls | Enter the list of domains, with each URL in a separate row. For example: - samlidp.clever.com- clever.com- mobile-redirector.clever.com |
| Authentication | Configure Webcam Access Domain Names | This setting is optional, and it should be configured if you need to use the webcam during the sign-in process. Specify the list of domains that are allowed to use the webcam during the sign-in process, separated by a semicolon. For example: clever.com |
Assign the policy to a group that contains as members the devices or users that you want to configure.
Alternatively, you can configure devices using a custom policy with the following settings:
| Setting |
|---|
OMA-URI: ./Vendor/MSFT/Policy/Config/Education/IsEducationEnvironmentData type: int Value: 1 |
OMA-URI: ./Vendor/MSFT/SharedPC/EnableSharedPCModeWithOneDriveSyncData type: Boolean Value: True |
OMA-URI: ./Vendor/MSFT/Policy/Config/Authentication/EnableWebSignInData type: Integer Value: 1 |
OMA-URI: ./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebSignInAllowedUrlsData type: String Value: Semicolon separated list of domains, for example: samlidp.clever.com;clever.com;mobile-redirector.clever.com |
OMA-URI: ./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebCamAccessDomainNamesData type: String Value: This setting is optional, and it should be configured if you need to use the webcam during the sign-in process. Specify the list of domains that are allowed to use the webcam during the sign-in process, separated by a semicolon. For example: clever.com |
How to use federated sign-in
Once the devices are configured, a new sign-in experience becomes available.
As users enter their username, they're redirected to the identity provider sign-in page. Once the Idp authenticates the users, they're signed-in. In the following animation, you can observe how the first sign-in process works for a student assigned (1:1) device:
Important
For student assigned (1:1) devices, once the policy is enabled, the first user who sign-in to the device will also set the disambiguation page to the identity provider domain on the device. This means that the device will be defaulting to that IdP. The user can exit the Federated sign-in flow by pressing Ctrl+Alt+Delete to get back to the standard Windows sign-in screen. The behavior is different for student shared devices, where the disambiguation page is always shown, unless preferred Microsoft Entra tenant name is configured.
Important considerations
Known issues affecting student assigned (1:1) devices
Federated sign-in for student assigned (1:1) devices doesn't work with the following settings enabled:
- EnableSharedPCMode or EnableSharedPCModeWithOneDriveSync, which are part of the SharedPC CSP
- Interactive logon: do not display last signed in, which is a security policy part of the Policy CSP
- Take a Test in kiosk mode, since it uses the security policy above
Known issues affecting student shared devices
The following issues are known to affect student shared devices:
- Non-federated users can't sign-in to the devices, including local accounts
- Take a Test in kiosk mode, since it uses a local guest account to sign in
Account management
For student shared devices, it's recommended to configure the account management policies to automatically delete the user profiles after a certain period of inactivity or disk levels. For more information, see Set up a shared or guest Windows device.
Preferred Microsoft Entra tenant name
To improve the user experience, you can configure the preferred Microsoft Entra tenant name feature.
When using preferred Microsoft Entra tenant name, the users bypass the disambiguation page and are redirected to the identity provider sign-in page. This configuration can be especially useful for student shared devices, where the disambiguation page is always shown.
For more information about preferred tenant name, see Authentication CSP - PreferredAadTenantDomainName.
Identity matching in Microsoft Entra ID
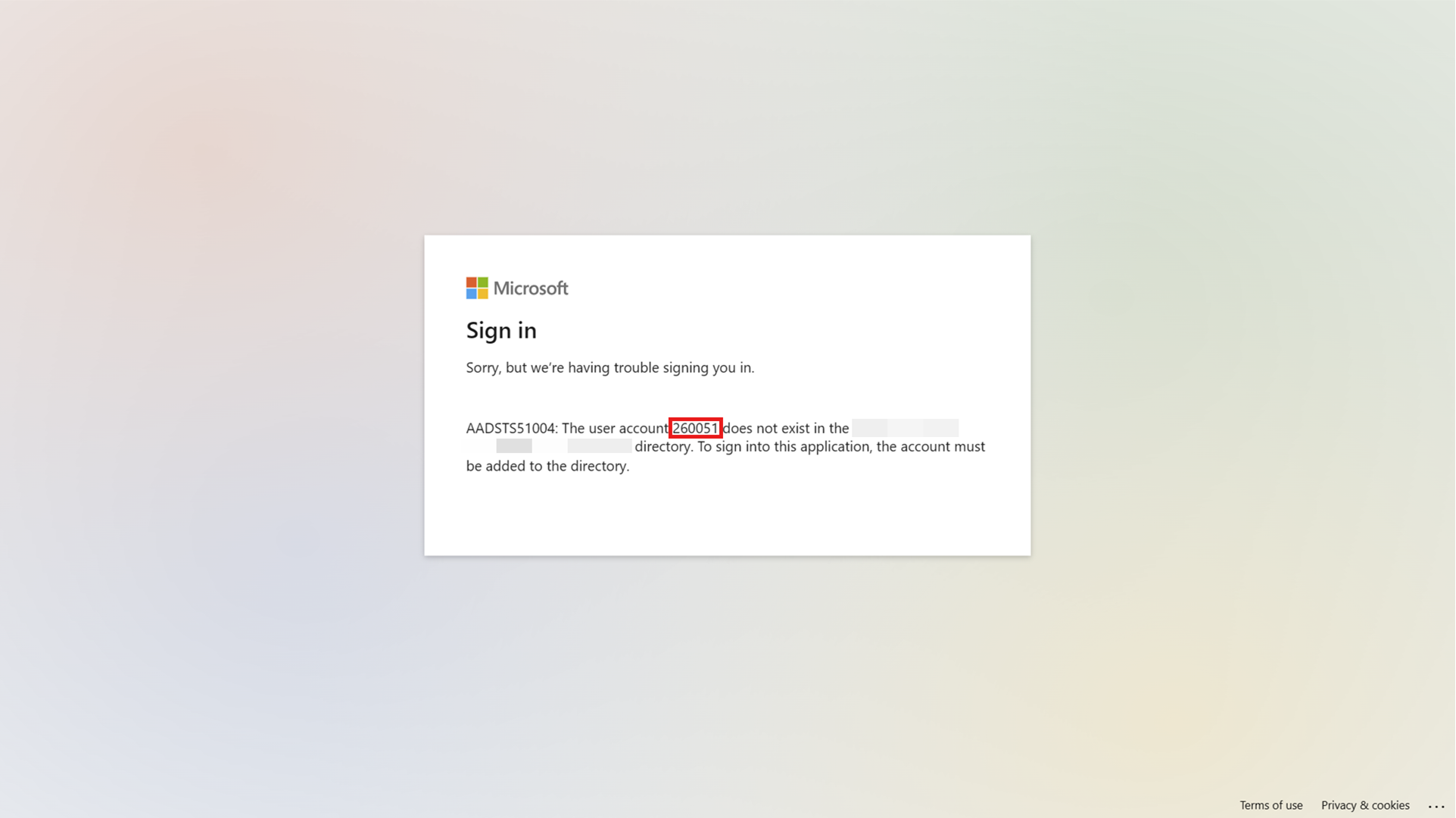
When a Microsoft Entra user is federated, the user's identity from the IdP must match an existing user object in Microsoft Entra ID. After the token sent by the IdP is validated, Microsoft Entra ID searches for a matching user object in the tenant by using an attribute called ImmutableId.
Note
The ImmutableId is a string value that must be unique for each user in the tenant, and it shouldn't change over time. For example, the ImmutableId could be the student ID or SIS ID. The ImmutableId value should be based on the federation setup and configuration with your IdP, so confirm with your IdP before setting it.
If the matching object is found, the user is signed-in. Otherwise, the user is presented with an error message. The following picture shows that a user with the ImmutableId 260051 can't be found:
Important
The ImmutableId matching is case-sensitive.
The ImmutableId is typically configured when the user is created in Microsoft Entra ID, but it can also be updated later.
In a scenario where a user is federated and you want to change the ImmutableId, you must:
- Convert the federated user to a cloud-only user (update the UPN to a non-federated domain)
- Update the ImmutableId
- Convert the user back to a federated user
Here's a PowerShell example to update the ImmutableId for a federated user:
Set-ExecutionPolicy -ExecutionPolicy RemoteSigned -Scope CurrentUser -Force
Install-Module Microsoft.Graph -Scope CurrentUser
Import-Module Microsoft.Graph
Connect-MgGraph -Scopes 'User.Read.All', 'User.ReadWrite.All'
#1. Convert the user from federated to cloud-only
Update-MgUser -UserId alton@example.com -UserPrincipalName alton@example.onmicrosoft.com
#2. Convert the user back to federated, while setting the immutableId
Update-MgUser -UserId alton@example.onmicrosoft.com -UserPrincipalName alton@example.com -OnPremisesImmutableId '260051'
Troubleshooting
- The user can exit the federated sign-in flow by pressing Ctrl+Alt+Delete to get back to the standard Windows sign-in screen
- Select the Other User button, and the standard username/password credentials are available to log into the device