Windows Authentication Providers <providers>
Overview
The <providers> collection of the <windowsAuthentication> element defines the list of authentication providers that are used with the Internet Information Services (IIS) 7 Windows authentication module. This list of providers cannot be extended, and by default it contains only two entries:
- Negotiate - This provider will attempt to use Kerberos for authentication if it is available.
- NTLM - This provider will attempt to use Windows NT LAN Manager for authentication.
Compatibility
| Version | Notes |
|---|---|
| IIS 10.0 | The <providers> element was not modified in IIS 10.0. |
| IIS 8.5 | The <providers> element was not modified in IIS 8.5. |
| IIS 8.0 | The <providers> element was not modified in IIS 8.0. |
| IIS 7.5 | The <providers> element was not modified in IIS 7.5. |
| IIS 7.0 | The <providers> element of the <windowsAuthentication> element was introduced in IIS 7.0. |
| IIS 6.0 | The <providers> collection replaces the IIS 6.0 NTAuthenticationProviders metabase property. |
Setup
The default installation of IIS 7 and later does not include the Windows authentication role service. To use Windows authentication on IIS, you must install the role service, disable Anonymous authentication for your Web site or application, and then enable Windows authentication for the site or application.
Note
After you install the role service, IIS 7 commits the following configuration settings to the ApplicationHost.config file.
<windowsAuthentication enabled="false" />
Windows Server 2012 or Windows Server 2012 R2
- On the taskbar, click Server Manager.
- In Server Manager, click the Manage menu, and then click Add Roles and Features.
- In the Add Roles and Features wizard, click Next. Select the installation type and click Next. Select the destination server and click Next.
- On the Server Roles page, expand Web Server (IIS), expand Web Server, expand Security, and then select Windows Authentication. Click Next.
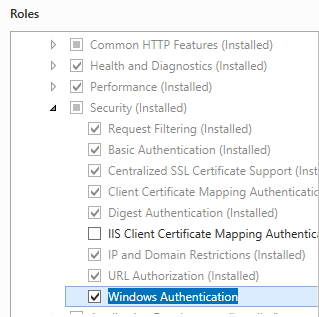
- On the Select features page, click Next.
- On the Confirm installation selections page, click Install.
- On the Results page, click Close.
Windows 8 or Windows 8.1
- On the Start screen, move the pointer all the way to the lower left corner, right-click the Start button, and then click Control Panel.
- In Control Panel, click Programs and Features, and then click Turn Windows features on or off.
- Expand Internet Information Services, expand World Wide Web Services, expand Security, and then select Windows Authentication.
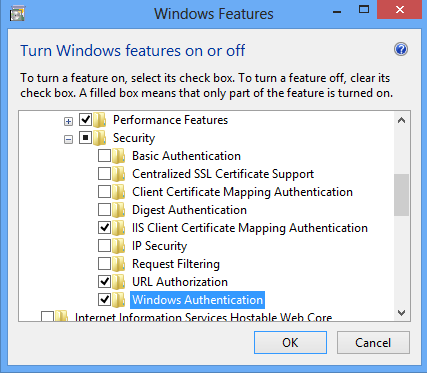
- Click OK.
- Click Close.
Windows Server 2008 or Windows Server 2008 R2
- On the taskbar, click Start, point to Administrative Tools, and then click Server Manager.
- In the Server Manager hierarchy pane, expand Roles, and then click Web Server (IIS).
- In the Web Server (IIS) pane, scroll to the Role Services section, and then click Add Role Services.
- On the Select Role Services page of the Add Role Services Wizard, select Windows Authentication, and then click Next.
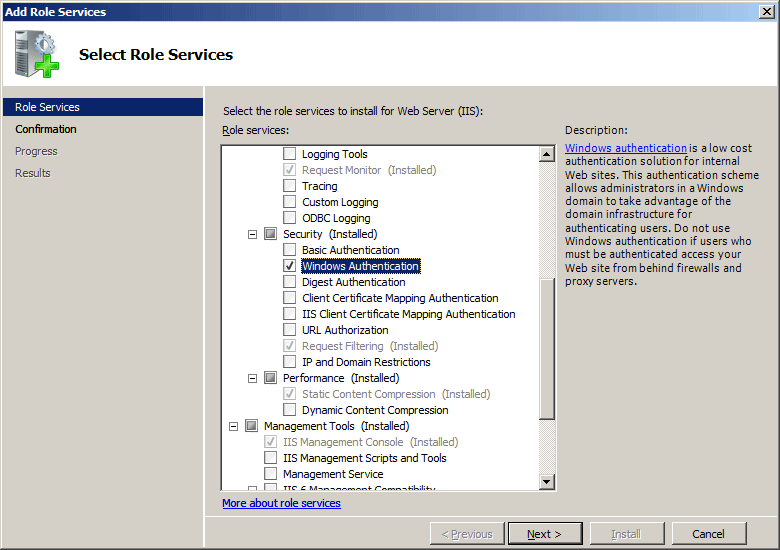
- On the Confirm Installation Selections page, click Install.
- On the Results page, click Close.
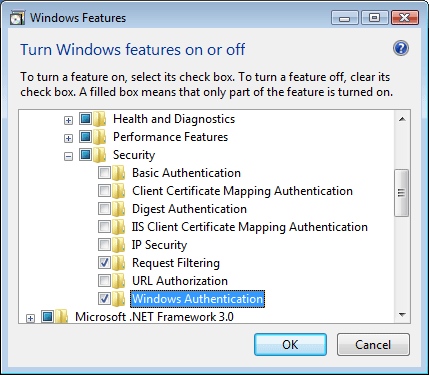
Windows Vista or Windows 7
- On the taskbar, click Start, and then click Control Panel.
- In Control Panel, click Programs and Features, and then click Turn Windows Features on or off.
- Expand Internet Information Services, then World Wide Web Services, then Security.
- Select Windows Authentication, and then click OK.
How To
There is no user interface for Windows authentication providers for IIS 7. For examples of how to modify the list of Windows authentication providers programmatically, see the Code Samples section of this document.
Configuration
Attributes
None.
Child Elements
| Element | Description |
|---|---|
add |
Optional element. Adds a security provider to the collection of providers. Windows authentication requires at least one provider. |
remove |
Optional element. Removes a reference to a security provider from the providers collection. |
clear |
Optional element. Removes all references to providers from the provider collection. |
Configuration Sample
The following default <windowsAuthentication> element is configured at the root ApplicationHost.config file in IIS 7.0, and disables Windows authentication by default. It also defines the two Windows authentication providers for IIS 7.0.
<windowsAuthentication enabled="false">
<providers>
<add value="Negotiate" />
<add value="NTLM" />
</providers>
</windowsAuthentication>
The following example enables Windows authentication and disables Anonymous authentication for a Web site named Contoso.
<location path="Contoso">
<system.webServer>
<security>
<authentication>
<anonymousAuthentication enabled="false" />
<windowsAuthentication enabled="true" />
</authentication>
</security>
</system.webServer>
</location>
Sample Code
The following code examples will enable Windows authentication and remove the Negotiate provider for a site named Contoso.
AppCmd.exe
appcmd.exe set config "Contoso" -section:system.webServer/security/authentication/windowsAuthentication /enabled:"True" /commit:apphost
appcmd.exe set config "Contoso" -section:system.webServer/security/authentication/windowsAuthentication /-"providers.[value='Negotiate']" /commit:apphost
Note
You must be sure to set the commit parameter to apphost when you use AppCmd.exe to configure these settings. This commits the configuration settings to the appropriate location section in the ApplicationHost.config file.
C#
using System;
using System.Text;
using Microsoft.Web.Administration;
internal static class Sample
{
private static void Main()
{
using (ServerManager serverManager = new ServerManager())
{
Configuration config = serverManager.GetApplicationHostConfiguration();
ConfigurationSection windowsAuthenticationSection = config.GetSection("system.webServer/security/authentication/windowsAuthentication", "Contoso");
windowsAuthenticationSection["enabled"] = true;
ConfigurationElementCollection providersCollection = windowsAuthenticationSection.GetCollection("providers");
ConfigurationElement addElement = FindElement(providersCollection, "add", "value", @"Negotiate");
if (addElement == null) throw new InvalidOperationException("Element not found!");
providersCollection.Remove(addElement);
serverManager.CommitChanges();
}
}
private static ConfigurationElement FindElement(ConfigurationElementCollection collection, string elementTagName, params string[] keyValues)
{
foreach (ConfigurationElement element in collection)
{
if (String.Equals(element.ElementTagName, elementTagName, StringComparison.OrdinalIgnoreCase))
{
bool matches = true;
for (int i = 0; i < keyValues.Length; i += 2)
{
object o = element.GetAttributeValue(keyValues[i]);
string value = null;
if (o != null)
{
value = o.ToString();
}
if (!String.Equals(value, keyValues[i + 1], StringComparison.OrdinalIgnoreCase))
{
matches = false;
break;
}
}
if (matches)
{
return element;
}
}
}
return null;
}
}
VB.NET
Imports System
Imports System.Text
Imports Microsoft.Web.Administration
Module Sample
Sub Main()
Dim serverManager As ServerManager = New ServerManager
Dim config As Configuration = serverManager.GetApplicationHostConfiguration
Dim windowsAuthenticationSection As ConfigurationSection = config.GetSection("system.webServer/security/authentication/windowsAuthentication", "Contoso")
windowsAuthenticationSection("enabled") = True
Dim providersCollection As ConfigurationElementCollection = windowsAuthenticationSection.GetCollection("providers")
Dim addElement As ConfigurationElement = FindElement(providersCollection, "add", "value", "Negotiate")
If (addElement Is Nothing) Then
Throw New InvalidOperationException("Element not found!")
End If
providersCollection.Remove(addElement)
serverManager.CommitChanges()
End Sub
Private Function FindElement(ByVal collection As ConfigurationElementCollection, ByVal elementTagName As String, ByVal ParamArray keyValues() As String) As ConfigurationElement
For Each element As ConfigurationElement In collection
If String.Equals(element.ElementTagName, elementTagName, StringComparison.OrdinalIgnoreCase) Then
Dim matches As Boolean = True
Dim i As Integer
For i = 0 To keyValues.Length - 1 Step 2
Dim o As Object = element.GetAttributeValue(keyValues(i))
Dim value As String = Nothing
If (Not (o) Is Nothing) Then
value = o.ToString
End If
If Not String.Equals(value, keyValues((i + 1)), StringComparison.OrdinalIgnoreCase) Then
matches = False
Exit For
End If
Next
If matches Then
Return element
End If
End If
Next
Return Nothing
End Function
End Module
JavaScript
var adminManager = new ActiveXObject('Microsoft.ApplicationHost.WritableAdminManager');
adminManager.CommitPath = "MACHINE/WEBROOT/APPHOST";
var windowsAuthenticationSection = adminManager.GetAdminSection("system.webServer/security/authentication/windowsAuthentication", "MACHINE/WEBROOT/APPHOST/Contoso");
windowsAuthenticationSection.Properties.Item("enabled").Value = true;
var providersCollection = windowsAuthenticationSection.ChildElements.Item("providers").Collection;
var addElementPos = FindElement(providersCollection, "add", ["value", "Negotiate"]);
if (addElementPos == -1) throw "Element not found!";
providersCollection.DeleteElement(addElementPos);
adminManager.CommitChanges();
function FindElement(collection, elementTagName, valuesToMatch) {
for (var i = 0; i < collection.Count; i++) {
var element = collection.Item(i);
if (element.Name == elementTagName) {
var matches = true;
for (var iVal = 0; iVal < valuesToMatch.length; iVal += 2) {
var property = element.GetPropertyByName(valuesToMatch[iVal]);
var value = property.Value;
if (value != null) {
value = value.toString();
}
if (value != valuesToMatch[iVal + 1]) {
matches = false;
break;
}
}
if (matches) {
return i;
}
}
}
return -1;
}
VBScript
Set adminManager = WScript.CreateObject("Microsoft.ApplicationHost.WritableAdminManager")
adminManager.CommitPath = "MACHINE/WEBROOT/APPHOST"
Set windowsAuthenticationSection = adminManager.GetAdminSection("system.webServer/security/authentication/windowsAuthentication", "MACHINE/WEBROOT/APPHOST/Contoso")
windowsAuthenticationSection.Properties.Item("enabled").Value = True
Set providersCollection = windowsAuthenticationSection.ChildElements.Item("providers").Collection
addElementPos = FindElement(providersCollection, "add", Array("value", "Negotiate"))
If (addElementPos = -1) Then
WScript.Echo "Element not found!"
WScript.Quit
End If
providersCollection.DeleteElement(addElementPos)
adminManager.CommitChanges()
Function FindElement(collection, elementTagName, valuesToMatch)
For i = 0 To CInt(collection.Count) - 1
Set element = collection.Item(i)
If element.Name = elementTagName Then
matches = True
For iVal = 0 To UBound(valuesToMatch) Step 2
Set property = element.GetPropertyByName(valuesToMatch(iVal))
value = property.Value
If Not IsNull(value) Then
value = CStr(value)
End If
If Not value = CStr(valuesToMatch(iVal + 1)) Then
matches = False
Exit For
End If
Next
If matches Then
Exit For
End If
End If
Next
If matches Then
FindElement = i
Else
FindElement = -1
End If
End Function
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for