Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Collecting diagnostics in Microsoft Intune is a powerful action that enables IT administrators to gather troubleshooting data from managed devices without interrupting users. This feature is essential for identifying and resolving issues related to device compliance, app performance, or enrollment failures—especially in large or distributed environments where hands-on access to devices is limited. For example, if a Windows device fails during Autopilot provisioning, Intune can automatically collect logs from the device and upload them for review, helping admins pinpoint the root cause quickly. This feature can also be used in bulk across up to 25 devices at once, streamlining diagnostics at scale.
The collect diagnostics action lets you collect and download managed device diagnostics without interrupting the user. Only nonuser locations and file types are accessed.
Prerequisites
Device platform requirements
This action supports the following platforms:
- Android (via app protection)
- iOS/iPadOS (via app protection)
- Windows (corporate-owned)
- Windows Holographic
Roles requirements
To run this action, use an account with at least one of the following roles:
- Help Desk Operator
- School Administrator
- Custom role that includes:
- The permission Remote tasks/Collect diagnostics
- Permissions that provide visibility into and access to managed devices in Intune (for example, Organization/Read, Managed devices/Read)
Network and connectivity requirements
For diagnostics to be able to upload successfully from the client, make sure that the URL for your region isn't blocked on the network:
- Europe:
lgmsapeweu.blob.core.windows.net- Americas:
lgmsapewus2.blob.core.windows.net- East Asia:
lgmsapesea.blob.core.windows.net- Australia:
lgmsapeaus.blob.core.windows.net- India:
lgmsapeind.blob.core.windows.net- Switzerland:
lgmsapeswiss.blob.core.windows.netDevices must be online and able to communicate with the service during diagnostics.
Note
Intune App Protection logs are available to download from the diagnostics tab in the Troubleshooting pane. However, M365 remote application diagnostics are only available to their specific support engineers.
Devices don't have to be managed by MDM (Mobile device management) to have Intune app protection or M365 app diagnostics collected, only managed by an Intune app protection policy.
The data is stored in Microsoft support systems and isn't subject to Intune data management policies or protections. Some applications might collect and store data using systems other than Intune.
How to collect diagnostics from the Intune admin center
Note
Diagnostics can't be collected or downloaded by calling Microsoft Graph directly. Use the Intune admin center to collect and download diagnostics.
The Microsoft 365 remote application diagnostics enables admins to request Intune app protection diagnostics and Microsoft 365 application diagnostics (where applicable).
Admins can find this report in the Microsoft Intune admin center by selecting Troubleshooting + support > Troubleshoot > select a user > Summary > App protection*. This feature is exclusive to applications that are under Intune app protection management. If supported, the application specific logs are gathered and stored within dedicated storage solutions for each application.
Applications with support for M365 application diagnostics:
- Outlook
- Teams
- OneDrive
- Microsoft Edge
- Outlook
- Teams
- OneDrive
- Microsoft Edge
- Microsoft Word
- Microsoft Excel
- Microsoft PowerPoint
- OneNote
- Microsoft 365 (Office)
Requirements to collect diagnostics from an M365 application:
- Sign in to the Microsoft Intune admin center.
- Navigate to Tenant administration > Device diagnostics > Make sure the third setting is enabled.
- Create and deploy an Intune App Protection policy to a user. For more information, see Create and assign app protection policies.
- Confirm the application has been managed by Intune App Protection policy. You can check locally on the device and/or by loading the user into the Intune Troubleshooting Pane and opening the App Protection summary page.
To use the Collect diagnostics action:
- Sign in to the Microsoft Intune admin center
- Navigate to Troubleshooting + support > Troubleshoot > select a user.
- On the Summary page, select App Protection > Checked-in.
- Find the application to collect diagnostics on and use the "..." option to select Collect diagnostics.
- When prompted, select Yes.
To check status of the Collect diagnostics action:
- On the "App Protection" summary, select refresh.
- Find the application you want the status for and select the hyperlink in the Diagnostic Status column.
To download diagnostics:
- Navigate to Troubleshooting + support > Troubleshoot > select a user.
- On the Summary page, select the Diagnostics page and download the diagnostics.
Important
Diagnostic uploads exceeding 50 diagnostics or 4 MB in diagnostic data can't be downloaded directly from the Intune portal. For access to larger diagnostic uploads, reach out to Microsoft Intune support.
Diagnostics take approximately 30 minutes to be delivered from an end user's device. The user might be required to close and reopen the app if prompted for a pin when opening the app for the diagnostics request to prompt.
The collect diagnostics action can also be configured to automatically collect and upload Windows devices logs upon a Windows Autopilot failure on a device. When a Windows Autopilot failure occurs, logs are processed on the failed device and then automatically captured and uploaded to Intune. A device can automatically capture one set of logs per day.
The diagnostic collection is stored for 28 days and then deleted. Each device can have up to 10 collections stored at one time.
Collect diagnostics is also available as a bulk device action that collects diagnostic logs from up to 25 Windows devices at a time.
Note
Microsoft personnel might access device diagnostics to help troubleshooting and resolving incidents.
To use the Collect diagnostics action:
- In the Microsoft Intune admin center, select Devices > All devices.
- From the devices list, select a device.
- At the top of the device overview pane, find the row of action icons. Select Collect diagnostics.
- To confirm, select Yes. A pending notification appears on the device's Overview page.
- To check the status of the action, select Monitor > Device diagnostics.
- After the action completes, select ... > Download in the row for the action > Yes.
- The data zip file is added to your download tray and you can save it to your computer.
Diagnostics collection on Windows Autopilot failure
Windows Autopilot diagnostics are automatically captured when devices experience a failure as long as the Windows Autopilot automatic capture diagnostic feature is enabled.
To view the diagnostics collected after a Windows Autopilot failure:
- In the Microsoft Intune admin center, select Devices > All devices.
- From the devices list, select a device.
- At the top of the device overview pane, find the row of action icons. Select Diagnostics > Download.
- The data zip file is added to your download tray and you can save it to your computer.
Data collected
While there's no intent to collect personal data, diagnostics might include user identifiable information such as user or device name.
If you install KB5011543 on Windows 10 or KB5011563 on Windows 11, the format of the zip file is simpler including:
- A flattened structure where the logs collected are named to match the data collected
- When multiple files are collected, a folder is created.
This following list is the same order as the diagnostic zip. Each collection contains the following data:
| Registry key |
|---|
HKLM\SOFTWARE\Microsoft\CloudManagedUpdate |
HKLM\SOFTWARE\Microsoft\EPMAgent |
HKLM\SOFTWARE\Microsoft\PolicyManager\current\device\DeviceHealthMonitoring |
HKLM\SOFTWARE\Microsoft\IntuneManagementExtension |
HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot |
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI |
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings |
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
HKLM\SOFTWARE\Microsoft\DeviceInventory |
HKLM\SOFTWARE\Policies\Microsoft\Cryptography\Configuration\SSL |
HKLM\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall |
HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL |
HKLM\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\Mdm |
HKLM\SYSTEM\Setup\SetupDiag\Results |
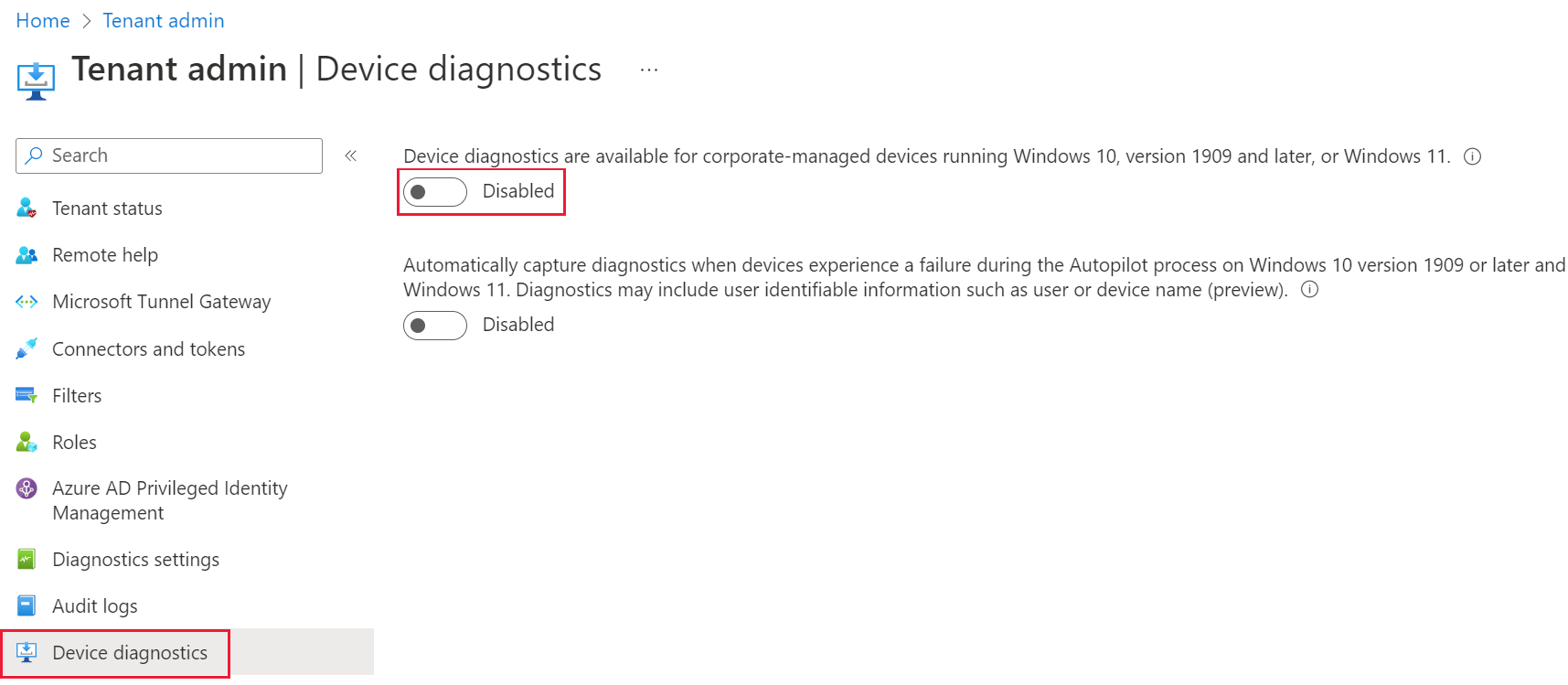
Disable device diagnostics
The collect diagnostics action is enabled by default. You can disable the Collect diagnostics action for all devices by following these steps:
Sign in to the Microsoft Intune admin center
Navigate to Tenant administration > Device diagnostics.
Change the control under Device diagnostics are available for corporate-managed devices running Windows 10, version 1909 and later, or Windows 11. to Disabled.
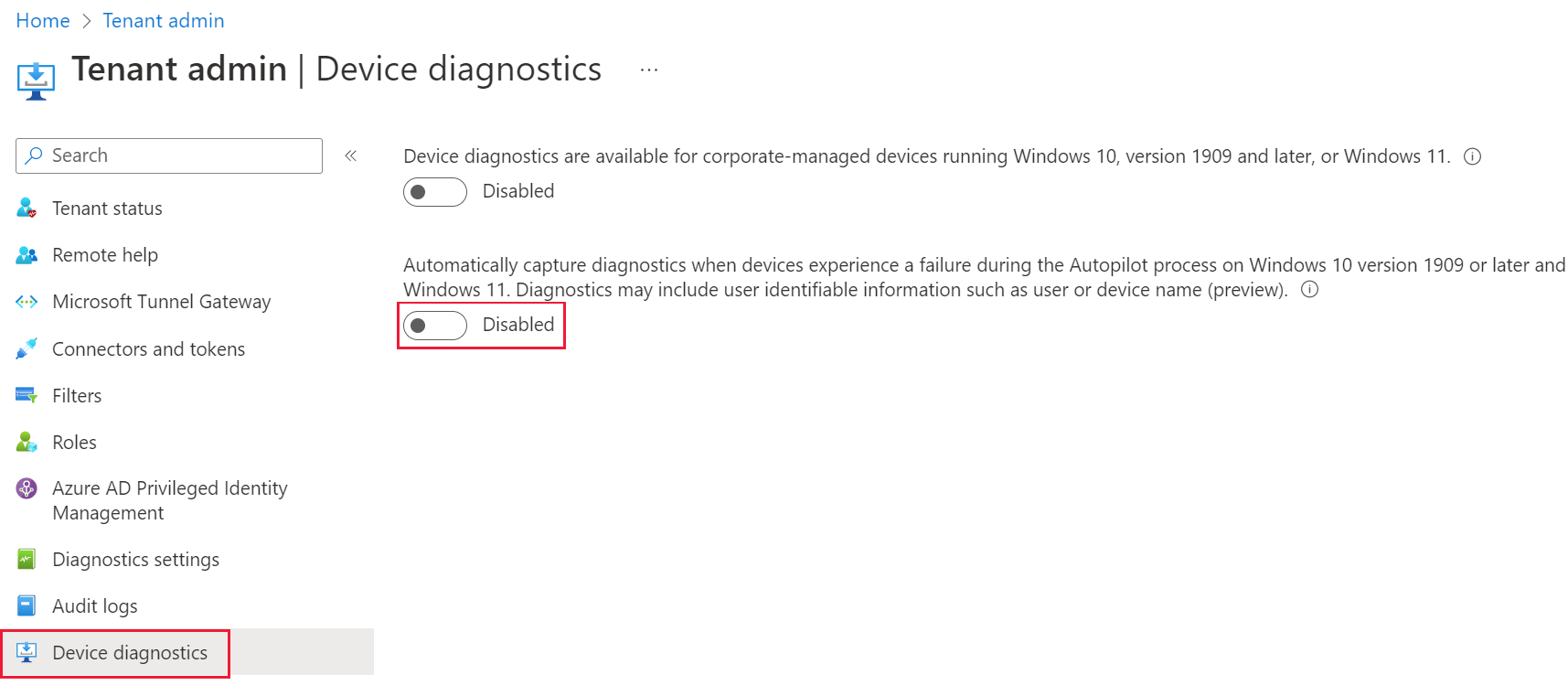
Disable Windows Autopilot automatic collection of diagnostics
Windows Autopilot automatic diagnostic capture is enabled by default. You can disable Windows Autopilot automatic diagnostic capture by following these steps:
Sign in to the Microsoft Intune admin center
Navigate to Tenant administration > Device diagnostics.
Change the control under Automatically capture diagnostics when devices experience a failure during the Autopilot process on Windows 10 version 1909 or later and Windows 11. Diagnostics may include user identifiable information such as user or device name (preview). to Disabled.
Known issues with device diagnostics
Currently there are the two main issues that could cause device diagnostics to fail:
- A time-out could occur on devices without patches KB4601315 or KB4601319. These patches contain a fix to the DiagnosticLog CSP that prevents time out during upload. After the update installs, make sure to reboot your device.
- The device wasn't able to receive the device action within a 24-hour window. If the device is offline or turned off, it could cause a failure.