Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Screenshots
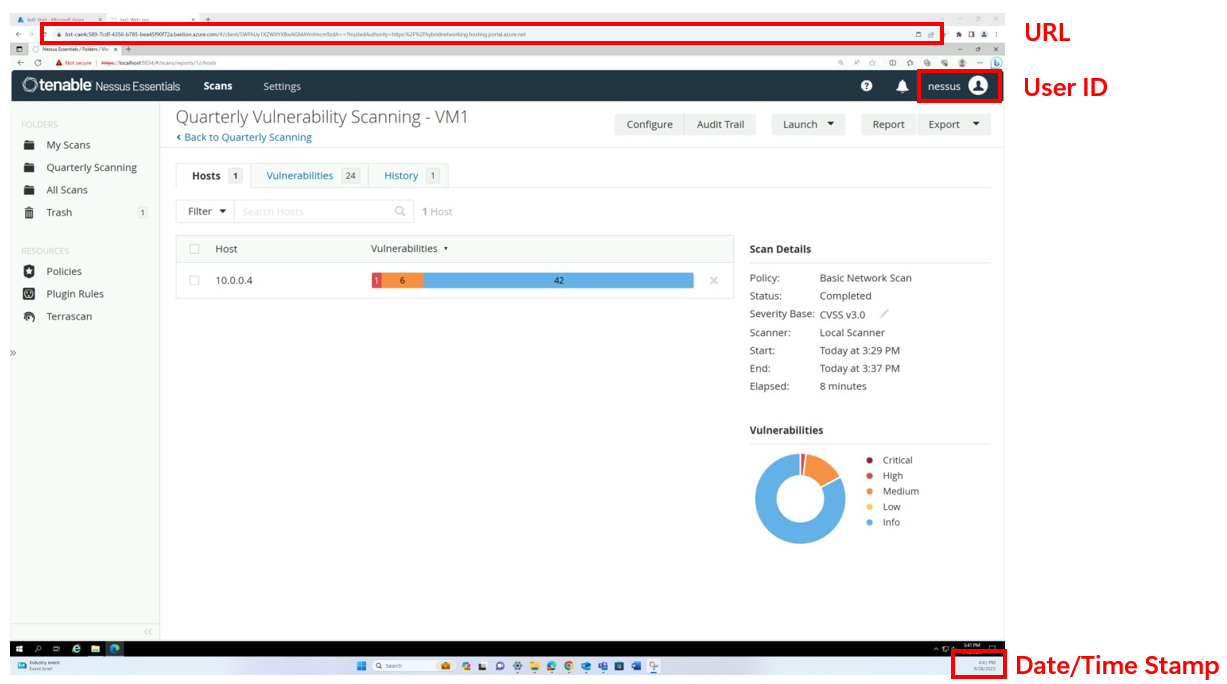
Screenshots should be complete images of your system, showing the date and time stamp, URLs, and evidence of logged-in user ID when relevant.
Policy documents
The entire policy document must be submitted when providing evidence. Per industry best practices polices should undergo an annual review to ensure they are up to date. All policies should include version controls, dates, and approvals.

Sub-controls
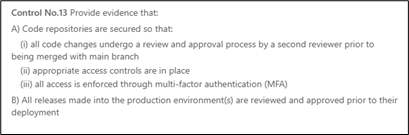
Many of the controls include sub-controls that must be satisfied. You are required to upload evidence for each of these sub-controls.
File submission
Screenshots should be provided as word/PDF documents with a detailed description of purpose and context. This will help simplify the certification review process, making sure the control shown is correctly assessed against the control’s purpose.

Please refer to the sample evidence guide for comprehensive instructions on aligning your documentation with the criteria for potential evidence.