Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
As an educational institution, you can sign up for a free trial of Microsoft 365 Education and complete an eligibility verification wizard to purchase subscriptions at academic prices.
Creating a Microsoft Entra tenant
When you sign up for a paid or trial subscription of Microsoft 365 Education, a Microsoft Entra tenant is created as part of the underlying Office 365 services. Likewise, a Microsoft Entra tenant is created when you sign up for Azure.
Customers must own a paid Microsoft license plan to create an additional Microsoft Entra tenant.
Important
When creating a Microsoft Entra tenant, you must specify a logical region that will determine the location of the data center. This must be chosen very carefully because it cannot be changed after creation.
For more information, see the Microsoft 365 Education deployment guide.
What is a Microsoft Entra tenant?
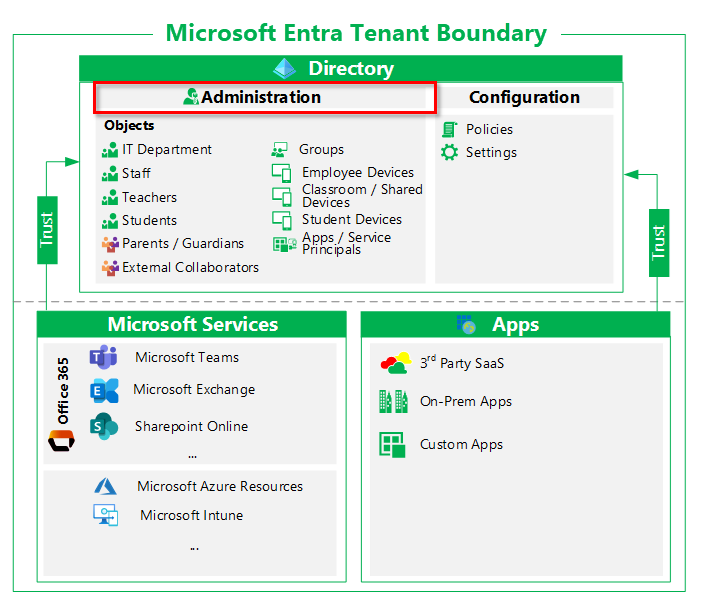
A Microsoft Entra tenant provides identity and access management (IAM) capabilities to applications and resources used by your organization. An identity is a directory object that can be authenticated and authorized for access to a resource. Identity objects exist for human identities such as students and teachers, and non-human identities like classroom and student devices, applications, and service principles.
The Microsoft Entra tenant is an identity security boundary that is under the control of your organization’s IT department. Within this security boundary, administration of objects (such as user objects) and configuration of tenant-wide settings are controlled by your IT administrators.
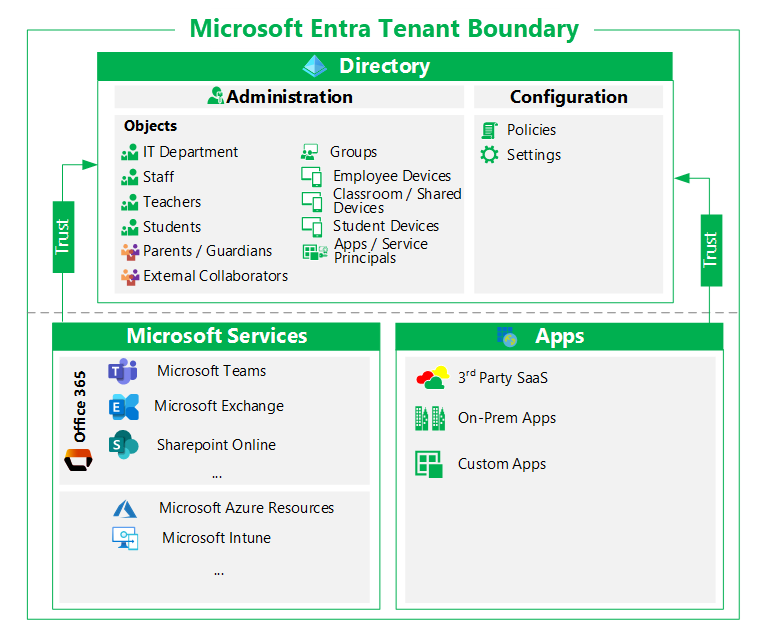
Resources in a tenant
Microsoft Entra ID is used to grant objects representing identities access to resources like applications and their underlying Azure resources, which might include databases, and Learning management Systems (LMS).
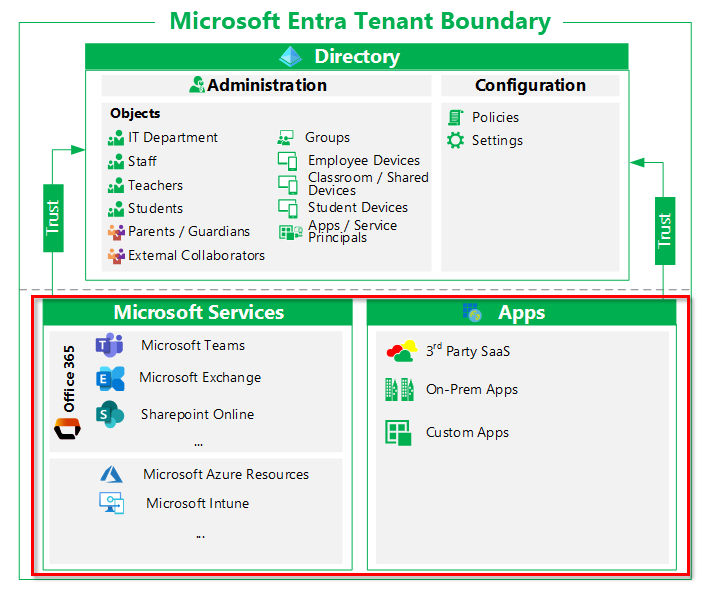
Access to apps that use Microsoft Entra ID
Identities can be granted access to many types of applications, including but not limited to:
Microsoft productivity services such as Exchange Online, Microsoft Teams, and SharePoint Online
Microsoft IT services such as Azure Sentinel, Microsoft Intune, and Microsoft Defender ATP
Microsoft Developer tools such as Azure DevOps
Third-party applications such as Learning Management Systems (LMS)
On-premises applications integrated with hybrid access capabilities such as Microsoft Entra application proxy
Custom in-house developed applications
Applications that use Microsoft Entra ID require directory objects to be configured and managed in the trusted Microsoft Entra tenant. Examples of directory objects include application registrations, service principals, groups, and schema attribute extensions.
While some applications can have multiple instances per tenant, for example a test instance and a production instance, some Microsoft Services such as Exchange Online can only have one instance per tenant.
Access to Directory Objects
Identities, resources, and their relationships are represented in a Microsoft Entra tenant as directory objects. Examples of directory objects include users, groups, service principals, and app registrations.
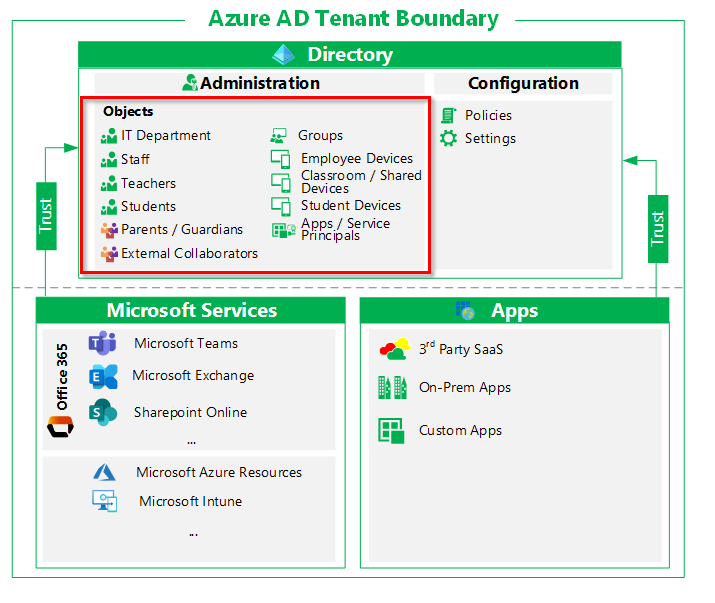
When objects are in a Microsoft Entra tenant, the following occurs:
Visibility. Identities can discover or enumerate resources, users, groups, and access usage reporting and audit logs if they have the right permissions. For example, a member of the directory can discover users in the directory with default user permissions.
Applications can affect objects. Applications can manipulate directory objects through Microsoft Graph as part of their business logic. Typical examples include reading or setting user attributes, updating user’s calendar, and sending emails on behalf of the user. Consent is necessary to allow applications to affect the tenant. Administrators can consent for all users. For more information, see Permissions and consent in the Microsoft identity platform.
Note
Use caution when using application permissions. For example, with Exchange Online, you should scope application permissions to specific mailboxes and permissions.
Throttling and service limits. Runtime behavior of a resource might trigger throttling to prevent overuse or service degradation. Throttling can occur at the application, tenant, or entire service level. Most commonly it occurs when an application has a large number of requests within or across tenants.
Every tenant has a total object limit. By default, a tenant is limited to 50,000 total objects. After a custom domain is added, the limit increases to 300,000. You can increase this object limit further by contacting the EDU Customer Success Team team. We recommended that a single Microsoft Entra tenant not exceed 1 million users, which usually equates to approximately 3 million total objects. For more information about service limits in Microsoft Entra ID, see Microsoft Entra service limits and restrictions.
Configuration in a tenant
Policies and settings in Microsoft Entra ID impact resources in the Microsoft Entra tenant through targeted, or tenant-wide configurations. 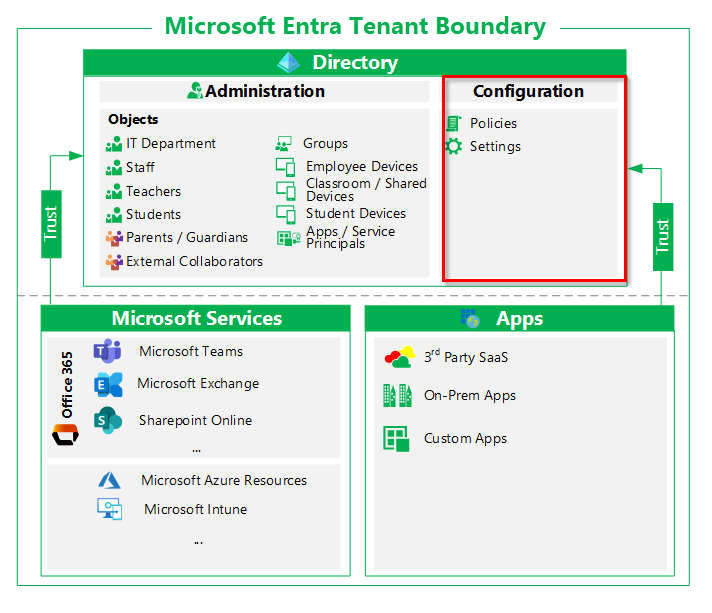
Examples of tenant-wide policies and settings include:
External identities. Global administrators for the tenant identify and control the external identities that can be provisioned in the tenant.
Whether to allow external identities in the tenant
From which domain(s) external identities can be added
Whether users can invite users from other tenants
Named Locations. Global administrators can create named locations, which can then be used to:
Block sign in from specific locations.
Trigger conditional access policies such as MFA.
Allowed authentication methods. Global administrators set the authentication methods allowed for the tenant.
Self-service options. Global Administrators set self-service options such as self-service password reset and create Office 365 groups at the tenant level.
The implementation of some tenant-wide configurations can be scoped as long as they don't get overridden by global administration policies. For example:
If the tenant is configured to allow external identities, a resource administrator can still exclude those identities from accessing a resource.
If the tenant is configured to allow personal device registration, a resource administrator can exclude those devices from accessing specific resources.
If named locations are configured, a resource administrator can configure policies either allowing or excluding access from those locations.
Administration in a tenant
Administration includes the management of identity objects and scoped implementation of tenant-wide configurations. Objects include users, groups, and devices, and service principles. You can scope the effects of tenant-wide configurations for authentication, authorization, self-serve options, and so on.
Tenant-wide administrators, or global admins, can:
Grant access to any resource to any user
Assign resource roles to any user
Assign lower-scoped admin roles to any user
Administration of directory objects
Administrators manage how identity objects can access resources, and under what circumstances. They also can disable, delete, or modify directory objects based on their privileges. Identity objects include:
Organizational identities, such as the following, are represented by user objects:
Administrators
Organizational users
Organizational developers
Test users **
External identities represent users from outside the organization such as:
Partners or other educational institutions that are provisioned with accounts local to the organization environment
Partners or other educational institutions that are provisioned via Azure B2B collaboration
Groups are represented by objects such as:
Security groups
Office 365 groups
Devices are represented by objects such as:
Microsoft Entra hybrid joined devices (on-premises computers synchronized from on-premises Active Directory)
Microsoft Entra joined devices
Microsoft Entra registered mobile devices used by employees to access their workplace applications.
Note
In a hybrid environment, identities are typically synchronized from the on-premises Active Directory environment using Microsoft Entra Connect.
Administration of identity services
Administrators with appropriate permissions can manage how tenant-wide policies are implemented at the level of resource groups, security groups, or applications. When considering administration of resources, keep the following in mind. Each can be a reason to keep resources together, or to isolate them.
An identity assigned an Authentication Administrator role can require non-administrators to reregister for MFA or FIDO authentication.
A Conditional Access (CA) Administrator can create CA policies that require users signing-in to specific apps to do so only from organization-owned devices. They can also scope configurations. For example, even if external identities are allowed in the tenant, they can exclude those identities from accessing a resource.
A Cloud Application Administrator can consent to application permissions on behalf of all users.
A Global Administrator can take control of a subscription.
Licensing
Microsoft paid cloud services, such as Office 365, require licenses. These licenses are assigned to each user who needs access to the services. Microsoft Entra ID is the underlying infrastructure that supports identity management for all Microsoft cloud services and stores information about license assignment states for users. Traditionally, administrators would use one of the management portals (Office or Azure) and PowerShell cmdlets to manage licenses. Microsoft Entra ID supports group-based licensing which enables you to assign one or more product licenses to a group of users.
Microsoft Entra ID in Microsoft 365 Education scenarios
Microsoft Entra ID helps students and faculty sign in and access resources and services in, including:
Sign in and authorization to resources
Domains for sign in and email are configured for cloud authentication in Microsoft Entra ID.
Most external collaboration capabilities use Microsoft Entra B2B collaboration.
Microsoft office 365 capabilities
Microsoft Entra identities are assigned Office 365 licenses, which triggers provisioning.
Office 365 objects such as distribution lists, Modern Groups, contacts, and Microsoft Teams, are represented by Microsoft Entra directory objects, and managed in Microsoft Entra ID.
Office 365 services provide authorization using Microsoft Entra groups.
Access to Office 365 is controlled through Microsoft Entra ID.
Governance and Security
Management and security features such as Intune for Education rely on Microsoft Entra users, groups, devices, and policies.
Privileged Identity Management to allow Just-in-Time (JIT) and Just Enough Administration (JEA) access to privileged operations.
Governance capabilities such as Access Reviews.
-
Microsoft Entra ID provides the hybrid capabilities to synchronize from on-premises Active Directory through Microsoft Entra Connect.
Microsoft Entra Connect enables you to configure the authentication method appropriate for your organization, including password hash synchronization, pass-through authentication, or federation integration with AD FS or non-Microsoft SAML identity provider.
APIs to provision directory objects from SIS using School Data Sync