Get started with your Microsoft Defender for Endpoint deployment
Applies to:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender XDR
Want to experience Microsoft Defender for Endpoint? Sign up for a free trial.
Tip
As a companion to this article, we recommend using the Microsoft Defender for Endpoint automated setup guide when signed in to the Microsoft 365 admin center. This guide will customize your experience based on your environment. To review best practices without signing in and activating automated setup features, go to the Microsoft 365 setup guide.
Maximize available security capabilities and better protect your enterprise from cyber threats by deploying Microsoft Defender for Endpoint and onboarding your devices. Onboarding your devices enables you to identify and stop threats quickly, prioritize risks, and evolve your defenses across operating systems and network devices.
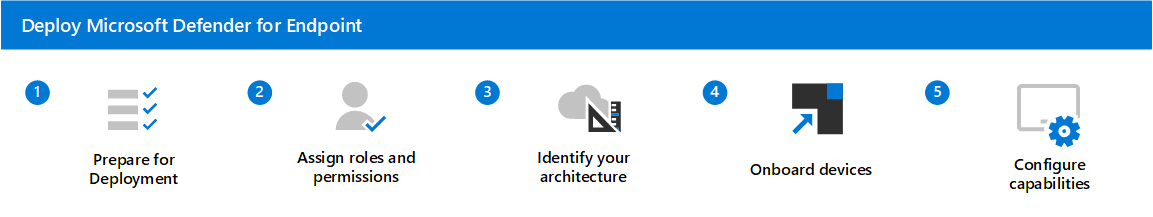
This guide provides five steps to help deploy Defender for Endpoint as your multi-platform endpoint protection solution. It helps you choose the best deployment tool, onboard devices, and configure capabilities. Each step corresponds to a separate article.
The steps to deploy Defender for Endpoint are:
- Step 1 - Set up Microsoft Defender for Endpoint deployment: This step focuses on getting your environment ready for deployment.
- Step 2 - Assign roles and permissions: Identify and assign roles and permissions to view and manage Defender for Endpoint.
- Step 3 - Identify your architecture and choose your deployment method: Identify your architecture and the deployment method that best suits your organization.
- Step 4 - Onboard devices: Assess and onboard your devices to Defender for Endpoint.
- Step 5 - Configure capabilities: You're now ready to configure Defender for Endpoint security capabilities to protect your devices.
Requirements
Here's a list of prerequisites required to deploy Defender for Endpoint:
- You're a global admin
- Your environment meets the minimum requirements
- You have a full inventory of your environment. The following table provides a starting point to gather information and ensure your environment is deeply understood by stakeholders, which helps identify potential dependencies and/or changes required in technologies or processes.
| What | Description |
|---|---|
| Endpoint count | Total count of endpoints by operating system. |
| Server count | Total count of Servers by operating system version. |
| Management engine | Management engine name and version (for example, System Center Configuration Manager Current Branch 1803). |
| CDOC distribution | High level CDOC structure (for example, Tier 1 outsourced to Contoso, Tier 2 and Tier 3 in-house distributed across Europe and Asia). |
| Security information and event (SIEM) | SIEM technology in use. |
Next step
Start your deployment with Step 1 - Set up Microsoft Defender for Endpoint deployment
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for