Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
To help protect devices (endpoints) against the initial access part of a ransomware attack:
- Deploy Intune as a mobile device management (MDM) and mobile application management (MAM) provider for your devices and enroll your organization-owned devices.
- Implement the Common identity and device access policies to validate the user account credentials and enforce device health and compliance requirements.
- Enable Network Protection in Microsoft Defender for Endpoint and Microsoft Defender XDR.
- Configure site and download checking and app and file checking in Microsoft Defender SmartScreen to block or warn.
- Enable Microsoft Defender Antivirus scanning of downloaded files and attachments.
- Set Remote Desktop security level to TLS in Microsoft Defender for Endpoint and Microsoft Defender XDR.
Windows 11 or 10 devices
To help protect against the lateral movement part of an attack from a Windows 11 or 10 device:
To reduce the impact of the attack:
To help protect against an attacker evading your security defenses:
- Keep cloud-delivered protection in Microsoft Defender Antivirus turned on.
- Keep Microsoft Defender Antivirus real-time behavior monitoring turned on.
- Turn on real-time protection.
- Turn on tamper protection in Microsoft Defender for Endpoint to prevent malicious changes to security settings.
To help protect against an attacker executing code as part of an attack:
- Turn on Microsoft Defender Antivirus.
- Block Win32 API calls from Office macros.
- Migrate all legacy workbooks requiring Excel 4.0 macros to the updated VBA macro format.
- Disable use of unsigned macros. Ensure all internal macros with business need are signed and leveraging trusted locations to ensure unknown macros will not run in your environment.
- Stop malicious XLM or VBA macros by ensuring runtime macro scanning by Antimalware Scan Interface (AMSI) is on. This feature (enabled by default) is on if the Group Policy setting for Macro Run Time Scan Scope is set to Enable for All Files or Enable for Low Trust Files. Get the latest group policy template files.
Impact on users and change management
As you implement these protections, perform change management for the following:
- The common Zero Trust identity and device access policies can deny access to users who have non-compliant devices.
- Downloading files might warn users before the download or it might be blocked.
- Some Office, Excel 4.0, XLM, or VBA macros might no longer run.
Resulting configuration
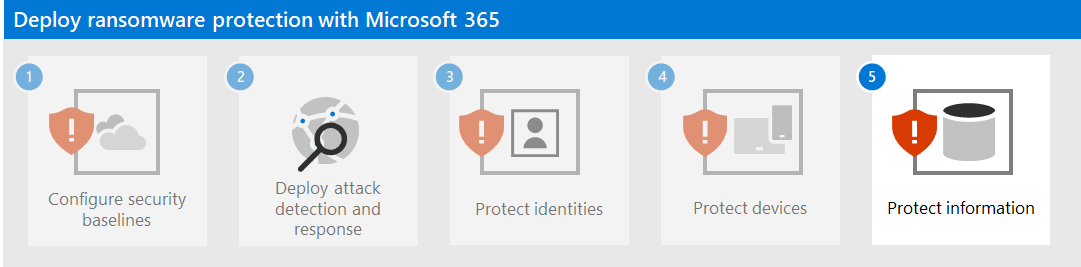
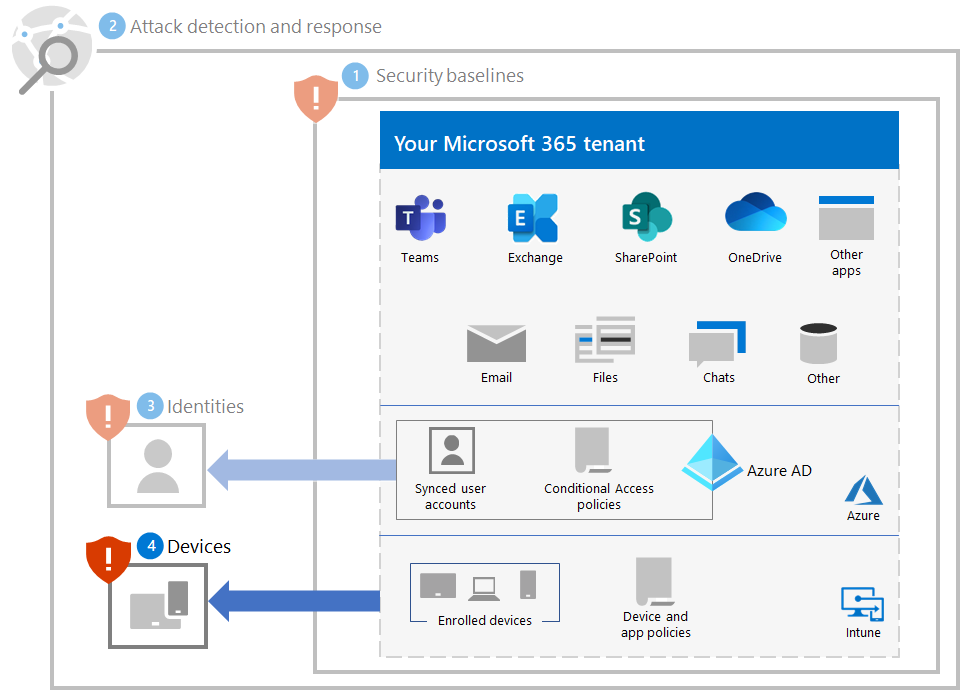
Here's the ransomware protection for your tenant for steps 1-4.
Next step
Continue with Step 5 to protect information in your Microsoft 365 tenant.