Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applying any Conditional Access (CA) policy on SharePoint in Microsoft 365 is also applied to Teams. However, some organizations want to block access to SharePoint files (upload, download, view, edit, create) yet allow their employees to use Teams desktop, mobile, and web clients on unmanaged devices. Under the CA policy rules, blocking SharePoint would lead to blocking Teams as well. This article explains how you can work around this limitation and allow your employees to continue using Teams while completely blocking access to files stored in SharePoint.
Note
Blocking or limiting access on unmanaged devices relies on Microsoft Entra Conditional Access policies. Learn about Microsoft Entra ID licensing. For an overview of conditional access in Microsoft Entra ID, see Conditional access in Microsoft Entra ID. For info about recommended SharePoint Online access policies, see Policy recommendations for securing SharePoint sites and files. If you limit access on unmanaged devices, users on managed devices must use one of the supported OS and browser combinations, or they will also have limited access.
You can block or limit access for:
Users in the organization or only some users or security groups.
All sites in the organization or only some sites.
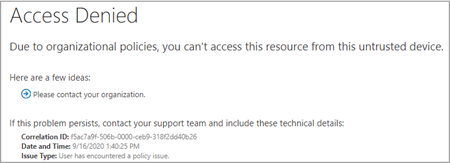
When access is blocked, users will see an error message. Blocking access helps provide security and protects secure data. When access is blocked, users will see an error message.
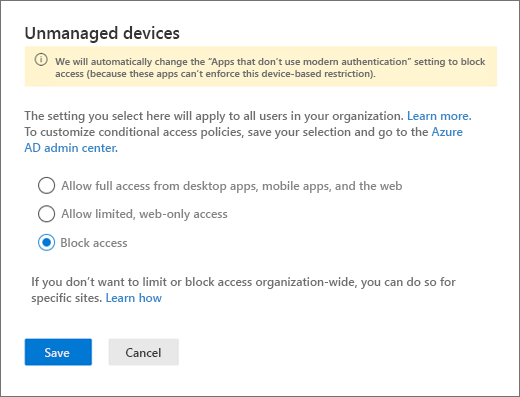
Open the SharePoint Admin Center.
Expand Policies > Access Policies.
In the Unmanaged Devices section, select Block Access and select Save.
Open the Microsoft Entra ID portal and navigate to Conditional Access Policies.
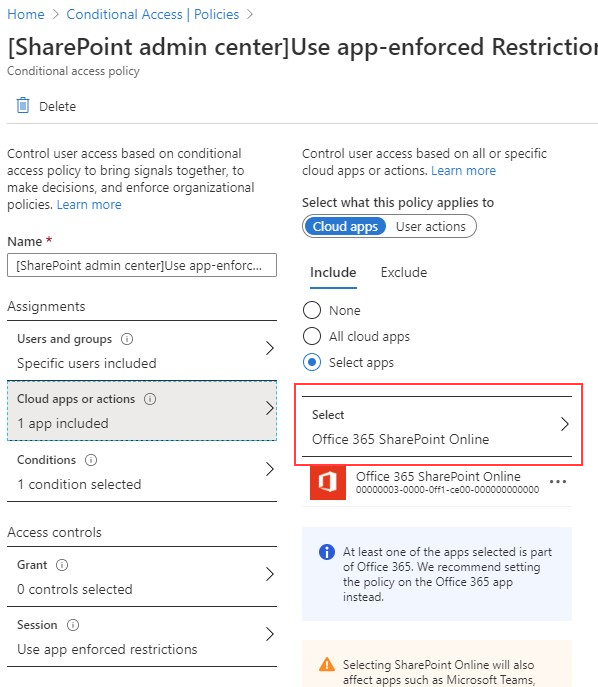
You'll see a new policy has been created by SharePoint that's similar to this example:
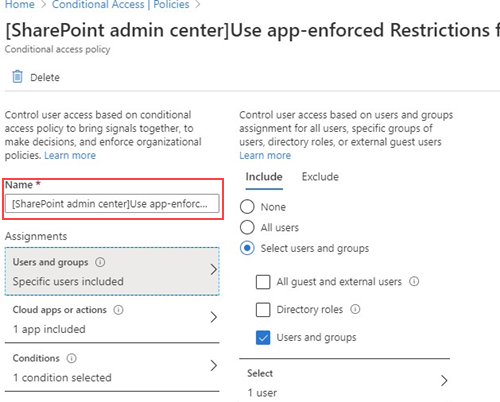
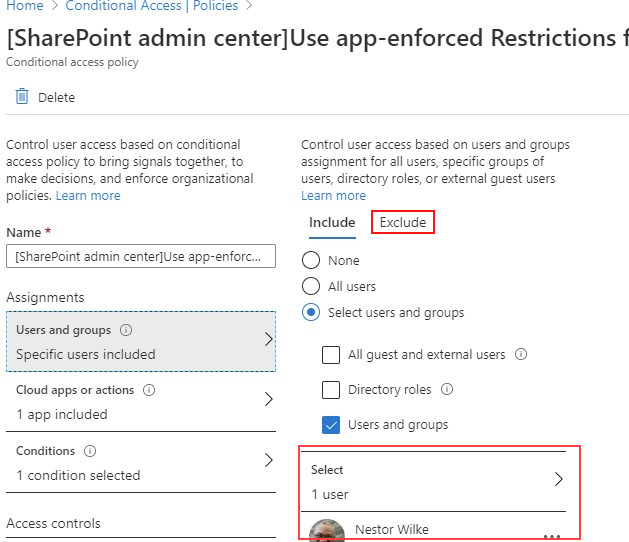
Update the policy to target only specific users or a group.
Note
Setting this policy will cut your access to the SharePoint admin portal. We recommended that you configure the exclusion policy and select the Global and SharePoint admins.
Verify that only SharePoint is selected as targeted Cloud App
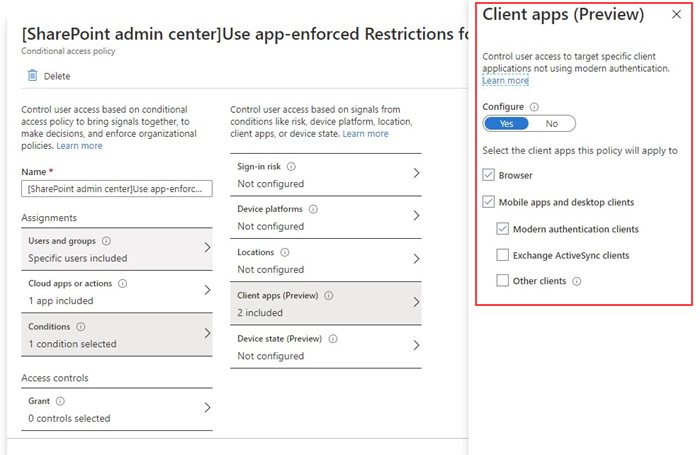
Update Conditions to include desktop clients, as well.
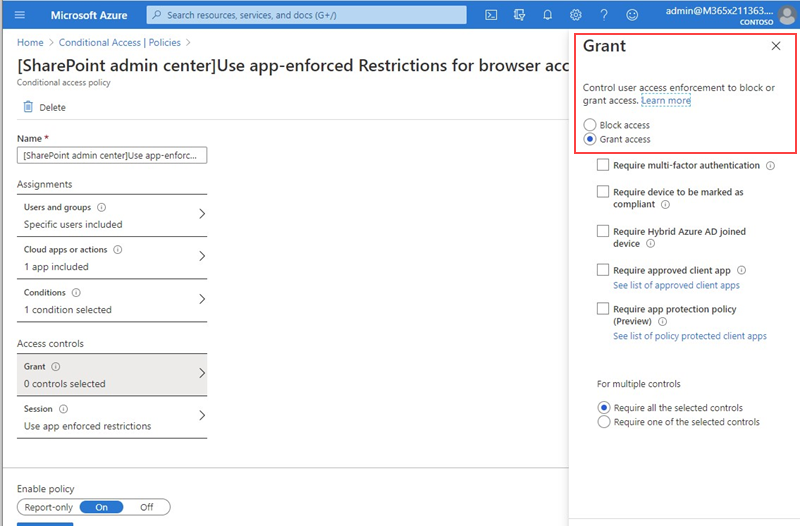
Make sure that Grant access is enabled
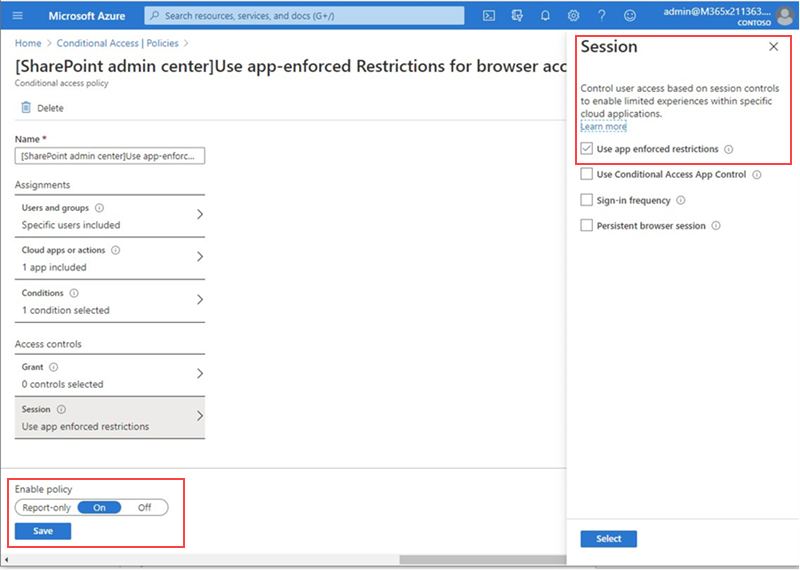
Make sure Use app enforced restrictions is enabled.
Enable your policy and select Save.
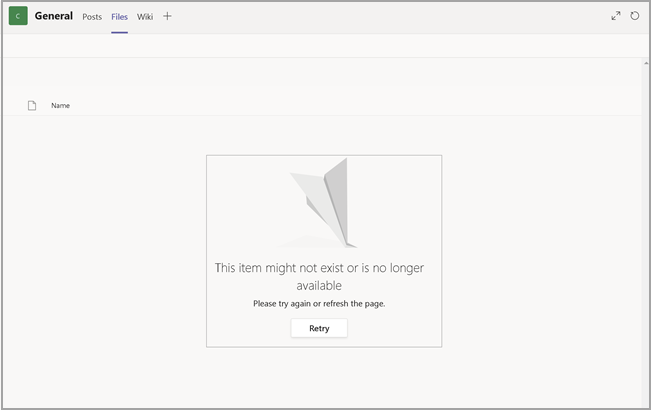
To test your policy, you need to sign out from any client such as the Teams desktop app or the OneDrive for Business sync client and sign in again to see the policy working. If your access has been blocked, you'll see a message in Teams that states the item might not exist.
In SharePoint, you'll receive an access denied message.