Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
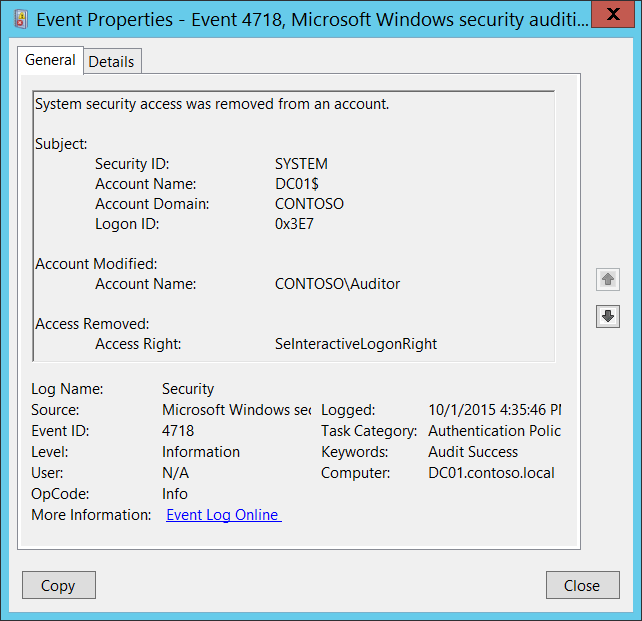
Subcategory: Audit Authentication Policy Change
Event Description:
This event generates every time local logon user right policy is changed and logon right was removed from an account.
You will see unique event for every user if logon user rights were removed for multiple accounts.
Note For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4718</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>13569</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2015-10-01T23:35:46.375134200Z" />
<EventRecordID>1049773</EventRecordID>
<Correlation />
<Execution ProcessID="500" ThreadID="5028" />
<Channel>Security</Channel>
<Computer>DC01.contoso.local</Computer>
<Security />
</System>
- <EventData>
<Data Name="SubjectUserSid">S-1-5-18</Data>
<Data Name="SubjectUserName">DC01$</Data>
<Data Name="SubjectDomainName">CONTOSO</Data>
<Data Name="SubjectLogonId">0x3e7</Data>
<Data Name="TargetSid">S-1-5-21-3457937927-2839227994-823803824-2104</Data>
<Data Name="AccessRemoved">SeInteractiveLogonRight</Data>
</EventData>
</Event>
Required Server Roles: None.
Minimum OS Version: Windows Server 2008, Windows Vista.
Event Versions: 0.
Field Descriptions:
Subject:
- Security ID [Type = SID]: SID of account that made a change to local logon right user policy. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Note A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that made a change to local logon right user policy.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Account Modified:
- Account Name [Type = SID]: the SID of the security principal for which logon right was removed. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Access Removed:
- Access Right [Type = UnicodeString]: the name of removed logon right. This event generates only for logon rights, which are as follows:
| Value | Group Policy Name |
|---|---|
| SeNetworkLogonRight | Access this computer from the network |
| SeRemoteInteractiveLogonRight | Allow logon through Terminal Services |
| SeDenyNetworkLogonRight | Deny access to this computer from the network |
| SeDenyBatchLogonRight | Deny logon as a batch job |
| SeDenyServiceLogonRight | Deny logon as a service |
| SeDenyInteractiveLogonRight | Deny logon locally |
| SeDenyRemoteInteractiveLogonRight | Deny logon through Terminal Services |
| SeBatchLogonRight | Log on as a batch job |
| SeServiceLogonRight | Log on as a service |
| SeInteractiveLogonRight | Log on locally |
Security Monitoring Recommendations
For 4718(S): System security access was removed from an account.
| Type of monitoring required | Recommendation |
|---|---|
| Actions typically performed by the SYSTEM account: This event and certain other events should be monitored to see if they are triggered by any account other than SYSTEM. | Because this event is typically triggered by the SYSTEM account, we recommend that you report it whenever “Subject\Security ID” is not SYSTEM. |
| High-value accounts: You might have high-value domain or local accounts for which you need to monitor each action. Examples of high-value accounts are database administrators, built-in local administrator account, domain administrators, service accounts, domain controller accounts and so on. |
Monitor this event with the “Subject\Security ID” and “Account Modified\Account Name” that correspond to the high-value account or accounts. |
| Anomalies or malicious actions: You might have specific requirements for detecting anomalies or monitoring potential malicious actions. For example, you might need to monitor for use of an account outside of working hours. | When you monitor for anomalies or malicious actions, use the “Subject\Security ID” (with other information) to monitor how or when a particular account is being used. |
| Non-active accounts: You might have non-active, disabled, or guest accounts, or other accounts that should never be used. | Monitor this event with the “Subject\Security ID” that corresponds to the accounts that should never be used. |
| Account allowlist: You might have a specific allowlist of accounts that are the only ones allowed to perform actions corresponding to particular events. | If this event corresponds to an “allowlist-only” action, review the “Subject\Security ID” for accounts that are outside the allowlist. If you have specific user logon rights policies, for example, an allowlist of accounts that can log on to certain computers, monitor this event to confirm that it was appropriate that the “Access Right” was removed from “Account Modified\Account Name.” |
| Accounts of different types: You might want to ensure that certain actions are performed only by certain account types, for example, local or domain account, machine or user account, vendor or employee account, and so on. | If this event corresponds to an action you want to monitor for certain account types, review the “Subject\Security ID” and “Account Modified\Account Name” to see whether the account type is as expected. For example, if critical remote network service accounts have user logon rights which should never be removed (for example, SeNetworkLogonRight), monitor this event for the “Account Modified\Account Name” and the appropriate rights. As another example, if non-service accounts should never be granted certain logon rights (for example, SeServiceLogonRight), you might monitor this event, because a right can be removed only after it was previously granted. |
| External accounts: You might be monitoring accounts from another domain, or “external” accounts that are not allowed to perform certain actions (represented by certain specific events). | Monitor this event for the “Subject\Account Domain” corresponding to accounts from another domain or “external” accounts. |
| Restricted-use computers or devices: You might have certain computers, machines, or devices on which certain people (accounts) should perform only limited actions, or no actions at all. | Monitor the target Computer: (or other target device) for actions performed by the “Subject\Security ID” that you are concerned about. Also be sure to check “Account Modified\Account Name” to see whether logon rights should be removed from that account. For high-value servers or other computers, we recommend that you track this event and investigate whether the specific “Access Right” should be removed from “Account Modified\Account Name” in each case. |
| Logon rights that should be restricted: You might have a list of user logon rights that you want to monitor (for example, SeServiceLogonRight). “Deny” rights that should not be removed: Your organization might use “Deny” rights that should not be removed, for example, SeDenyRemoteInteractiveLogonRight. |
- Monitor this event and compare the “Access Right” to your list of restricted rights. Monitor this event to discover the removal of a right that should never have been granted, so that you can investigate further. You can also monitor this event to discover the removal of “Deny” rights. When these rights are removed, it could be an approved action, done by mistake, or part of malicious activity. These rights include: SeDenyNetworkLogonRight: SeDenyBatchLogonRight SeDenyServiceLogonRight SeDenyInteractiveLogonRight SeDenyRemoteInteractiveLogonRight |
| Account naming conventions: Your organization might have specific naming conventions for account names. | Monitor “Subject\Account Name” for names that don’t comply with naming conventions. |