Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
You can use JAMF Pro to onboard macOS devices into Microsoft Purview solutions such as Endpoint data loss prevention (DLP).
Important
Use this procedure if you do not have Microsoft Defender for Endpoint (MDE) deployed to your macOS devices.
Applies to:
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview trials hub. Learn details about signing up and trial terms.
Before you begin
- Make sure your macOS devices are managed through JAMF pro and are associated with an identity (Microsoft Entra joined UPN) through JAMF Connect.
- OPTIONAL: Install the v95+ Microsoft Edge browser on your macOS devices for native Endpoint DLP support on Microsoft Edge.
Note
The three most recent major releases of macOS are supported.
Onboard devices into Microsoft Purview solutions using JAMF Pro
Prerequisites
Download the following files.
| File | Description |
|---|---|
| mdatp.mobileconfig | This is the bundled file. |
| schema.json | This is the MDE preference file. |
Tip
We recommend downloading the bundled mdatp.mobileconfig file, rather than the individual .mobileconfig files. The bundled file includes the following required files:
- accessibility.mobileconfig
- fulldisk.mobileconfig
- netfilter.mobileconfig
- sysext.mobileconfig
If any of these files are updated, you need to either download the updated bundle, or download each updated file individually.
Get the device onboarding and installation packages
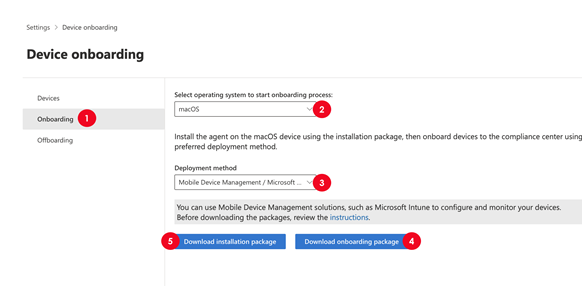
In the Purview portal, open Settings > Device Onboarding and then choose Onboarding.
For the Select operating system to start onboarding process value, choose macOS.
For Deployment method, choose Mobile Device Management/Microsoft Intune.
Choose Download onboarding package and then extract the contents of the device onboarding package. the DeviceComplianceOnboarding.plist file is downloaded to the JAMF folder.
Choose Download installation package.
Deploy onboarding packages
Create a new configuration profile in JAMF Pro. Use the following values:
- Name: MDATP onboarding for macOS
- Description: *MDATP EDR onboarding for macOS
- Category: none
- Distribution method: *`install automatically
- Level: computer level
For help with performing steps within the Jamf Pro console, refer to the JAMF Pro documentation, or contact Jamf Pro support.
Configure application preferences
Important
You must use com.microsoft.wdav as the Preference Domain value. Microsoft Defender for Endpoint uses this name and com.microsoft.wdav.ext to load the managed settings.
For information about how to create a new configuration profile in JAMF Pro, refer to the JAMF Pro documentation. Or contact Jamf Pro support.
Use these values:
- Name: MDATP MDAV configuration settings
- Description: Leave this blank
- Category: none
- Distribution method: install automatically
- Level: computer level
Deploy system configuration profiles
For information about how to deploy system configuration profiles in JAMF Pro, refer to the JAMF Pro documentation, or contact Jamf Pro support.
Offboard macOS devices using JAMF Pro
Important
Offboarding causes the device to stop sending sensor data to the portal. However, data from the device, including references to any alerts it has had, will be retained for up to six months.
If you aren't using MDE, uninstall the application. See the Package Deployment section in the JAMF Pro documentation.
Restart the macOS device. (Some applications may lose printing functionality until they're restarted.)