Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Securing DevOps environments is no longer a choice for developers. Bad actors are shifting left so you must implement Zero Trust principles that include verify explicitly, use least privilege access, and assume breach in DevOps environments.
This article describes best practices for securing your DevOps environments with a Zero Trust approach for preventing bad actors from compromising developer boxes, infecting release pipelines with malicious scripts, and gaining access to production data via test environments.
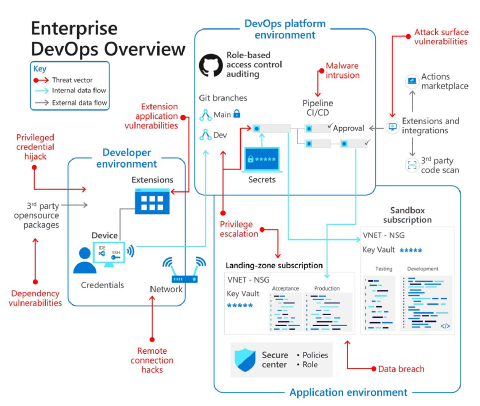
Our Securing Enterprise DevOps Environments eBook features the following visualization of the developer, DevOps platform, and application environments along with the potential security threats for each.
Notice in the previous diagram how connections between environments and to external integrations expand the threat landscape. These connections can increase opportunities for bad actors to compromise the system.
Bad actors stretch across enterprises to compromise DevOps environments, gain access, and unlock new dangers. Attacks go beyond the typical breadth of cybersecurity breaches to inject malicious code, assume powerful developer identities, and steal production code.
As companies transition to ubiquitous, work-from-anywhere scenarios, they must strengthen device security. Cybersecurity offices might lack consistent understanding of where and how developers secure and build code. Bad actors take advantage of these weaknesses with remote connection hacks and developer identity thefts.
DevOps tools are key entry points for bad actors, from pipeline automation to code validation and code repositories. If bad actors infect code before it reaches production systems, in most cases, it can pass through cybersecurity checkpoints. To prevent compromise, ensure that your development teams are engaged with peer reviews, security checks with IDE security plugins, secure coding standards, and branch review.
Cybersecurity teams aim to prevent bad actors from sieging production environments. However, environments now include supply chain tools and products. Open source tool breach can heighten global cybersecurity risks.
Learn more about developer-specific articles with the following DevSecOps articles in the Developer guidance section of the Zero Trust Guidance Center:
- Secure the DevOps platform environment helps you to implement Zero Trust principles in your DevOps platform environment and highlights best practices for secret and certificate management.
- Secure the developer environment helps you to implement Zero Trust principles in your development environments with best practices for least privilege, branch security, and trusting tools, extensions, and integrations.
- Embed Zero Trust security into your developer workflow helps you to innovate quickly and securely.
Next steps
- Accelerate and secure your code with Azure DevOps with tools that give developers the fastest and most secure code to cloud experience.
- Sign up for Azure Developer CLI, an open-source tool that accelerates the time it takes to get started on Azure.
- Configure Azure to trust GitHub's OIDC as a federated identity. OpenID Connect (OIDC) allows your GitHub Actions workflows to access resources in Azurewithout needing to store the Azure credentials as long-lived GitHub secrets.
- The DevOps resource center helps you with DevOps practices, Agile methods, Git version control, DevOps at Microsoft, and how to assess your organization's DevOps progress.
- Learn how the Microsoft DevSecOps solution integrates security into every aspect of the software delivery lifecycle to enable DevSecOps, or secure DevOps, for apps on the cloud (and anywhere) with Azure and GitHub.