Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article discusses how to configure Microsoft's BitLocker Administration and Monitoring (MBAM) with Secure Network Communication.
Original KB number: 2754259
Summary
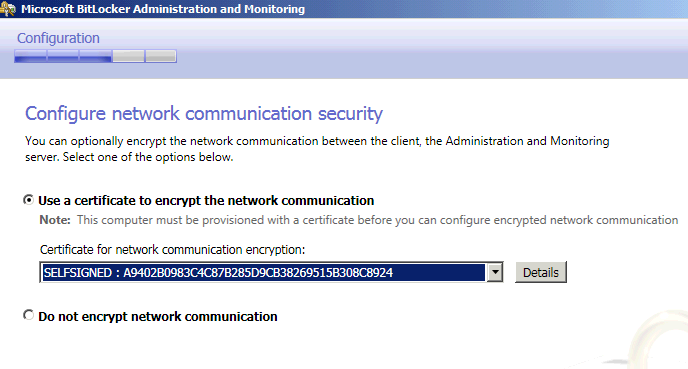
MBAM can encrypt the communication between the MBAM Recovery and Hardware Database, the Administration, and Monitoring servers and the MBAM clients. If you decide to encrypt the communication, you're asked to select the certification authority-provisioned certificate that will be used for encryption.
The channel between MBAM Administration & Monitoring Server and SQL SSRS can also be encrypted. An Administrator needs a certificate approved from CA (Certificate Authority) or a Self-Signed Certificate before deploying MBAM.
Note
If you decide to go with SSL, make sure you have the correct certificate to configure SSL before running MBAM Setup on your server.
Step 1: Encrypt Channel between MBAM Client and Administration & Monitoring Server.
Using Self Signed Certificate.
- Connect to Server where MBAM Administration & Monitoring Role will be installed.
- Make sure you have installed IIS.
- Open Server Manager and Click on Roles.
- Select webserver and click on IIS.
- In Feature View, Double-Click Server Certificates.
- Under Actions Pane, Select Self-Signed Certificate.
- On the Create Self-Signed Certificate page, type a friendly name for the certificate in the Specify a friendly name for the certificate box, and then click OK.
Note
- This procedure generates a self-signed certificate that doesn't originate from a generally trusted source; therefore, you shouldn't use this certificate to help secure data transfers between Internet clients and your server.
- Self-signed certificates may cause your Web browser to issue phishing warnings.
Using Certificate Approved by Certificate Authority
There are two ways to import a certificate
Request or Import a certificate from a CA using IIS:
Request or Import a certificate into the Personal Certificate Store using Certificate Manager:
Windows help and learningCertificate Templates to be used:
MBAM Client to MBAM Administration & Monitoring Server: Use Standard Web Server Template.
After you have certificate ready, when you execute MBAM Setup, we will show you the thumbprint of the certificate in "Configure Network Communication Security" wizard for MBAM Setup.
Step 2: Encrypt Channel between MBAM Administration & Monitoring Server and MBAM Recovery & Hardware SQL DB.
MBAM can encrypt the communication between the Recovery and Hardware Database and the Administration and Monitoring servers. If you choose the option to encrypt communication, you're asked to select the Certificate Authority-provisioned certificate that is used for encryption.
Certificate Templates to be used:
MBAM SQL DB Server to Admin & Monitoring Server: Standard Server Authentication Template
When you execute MBAM Setup Program on a server where you'll install MBAM Recovery & Hardware DB Role, you can see the certificate thumbprint in "Configure Network Communication Security" wizard for MBAM Setup Program.

Step 3: How to configure SSL for SQL Compliance and Audit DB Server.
Note
You'll have to configure SSL for SQL before you run MBAM Setup on your server.
Open SQL Reporting Services Configuration Manager on Server where you installed MBAM Audit Reports Role.
Connect to your Server and click Web Service URL.
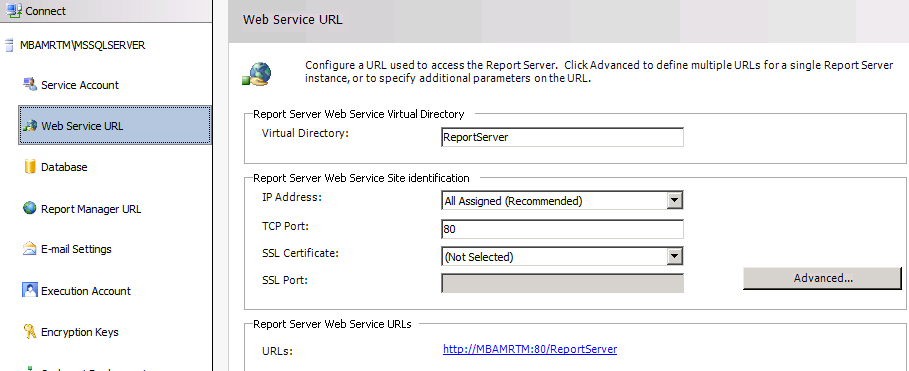
Click Advanced and then select your certificate. See image below:
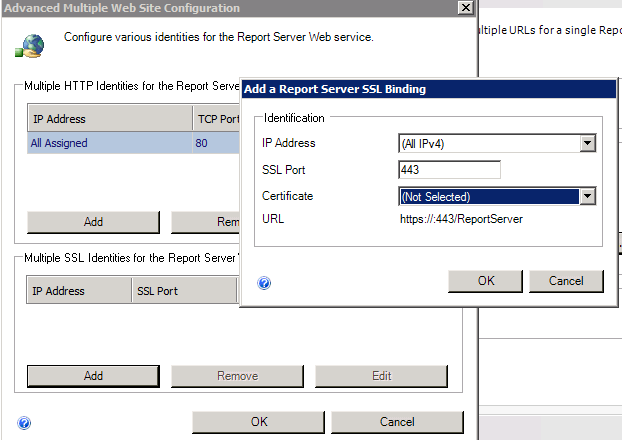
Repeat "Step 3" for Report Manager URL in SQL Reporting Services Configuration Manager.
Now when you open MBAM Reports it will use SSL to connect to SQL SSRS.
Step 4: Configure SQL to force encryption on all protocols.
Log in to SQL Server and Open SQL Server Configuration Manager.
Expand SQL Server Network Configuration and select "Protocols for MSSQLSERVER".
Right click on "Protocols for MSSQLSERVER" and select Yes for Force Encryption.
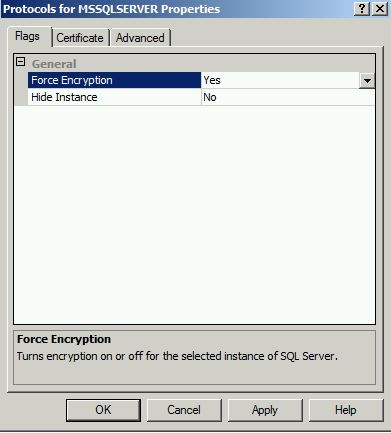
Select Certificates tab and choose your certificate from drop-down.
Click Apply and restart your SQL Services.
When you try to restart SQL Services, you'll hit an error message "The request failed or the service didn't respond in a timely fashion. Consult the event log or other applicable error logs for details."
It fails since SQL account doesn't have rights on Private keys of the certificate.
Open Certificate Manager MMC console and give the SQL account that is used for SQL services Full access on the certificate.

Restart the SQL Server Services now and it should be successful.