Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
You can use the Active Directory Federation Services (AD FS) sign-in page to check if authentication is working. To do this test, you go to the page and sign in. Also, you can use the sign-in page to verify that all SAML 2.0 relying parties are listed.
Enable the IdP-initiated sign-in page
By default, AD FS in Windows 2016 doesn't have the sign-in page enabled. To enable the page, use the PowerShell command Set-AdfsProperties. Use the following procedure to enable the page:
Open Windows PowerShell.
Enter
Get-AdfsProperties.Verify that the
EnableIdpInitiatedSignonPageproperty is set toFalse.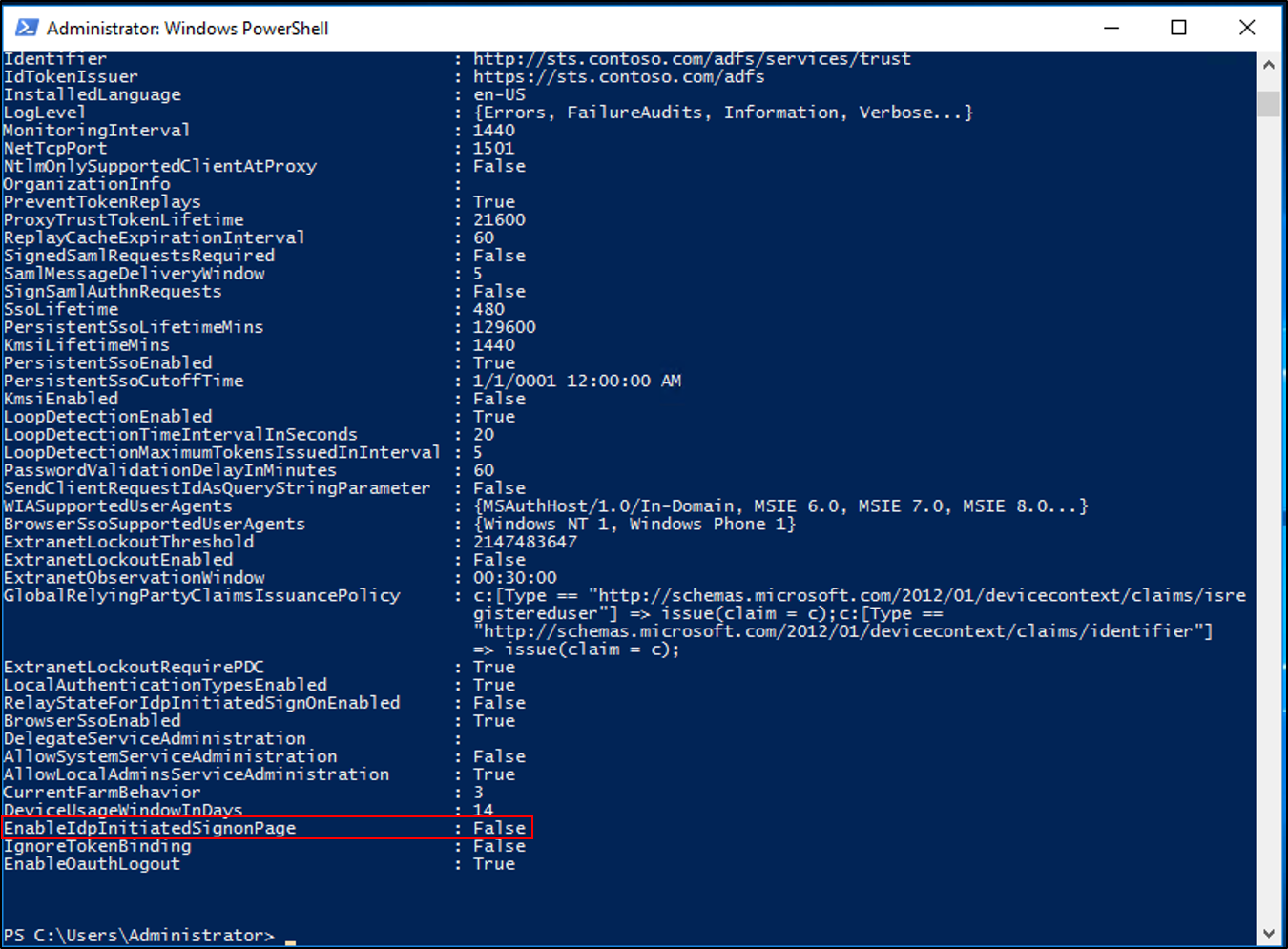
In PowerShell, enter
Set-AdfsProperties -EnableIdpInitiatedSignonPage $true.PowerShell doesn't provide a confirmation for the
Set-AdfsPropertiescommand. To confirm that theEnableIdpInitatedSignonPageproperty is set toTrue, enter theGet-AdfsPropertiescommand again and check the value for the property.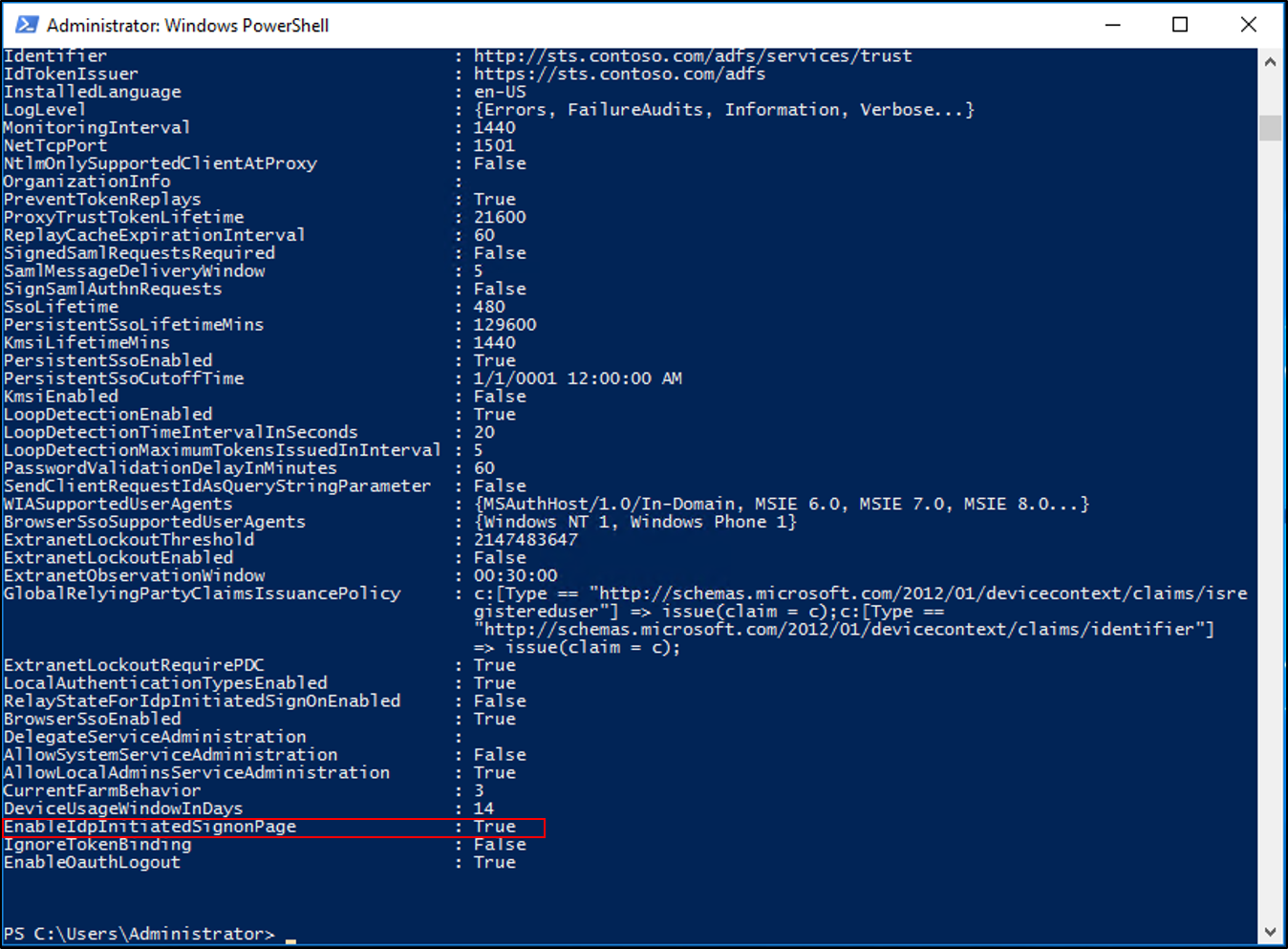
Test authentication
Use the following procedure to test AD FS authentication with the Identity Provider (IdP)-initiated sign-in page.
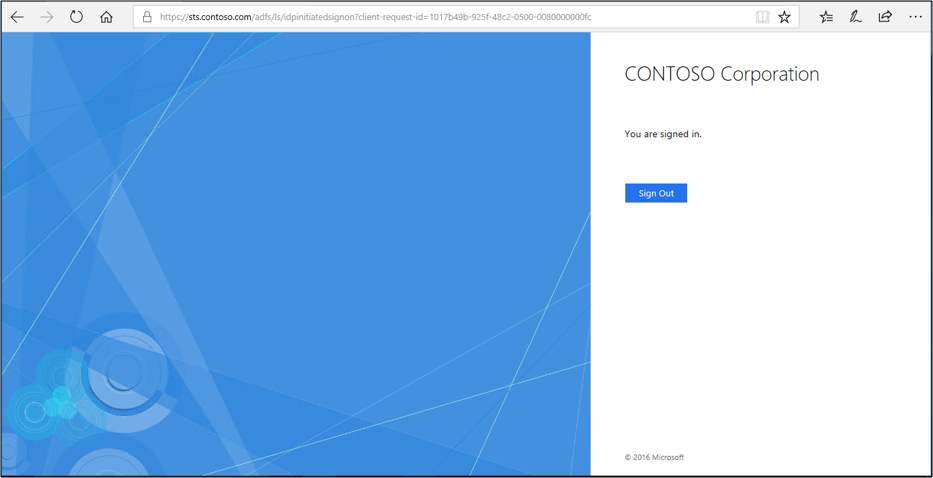
Open a web browser, and go to the IdP sign-in page. Your URL might look like
https://sts.contoso.com/adfs/ls/idpinitiatedsignon.aspx.You're prompted to sign in. Enter your credentials.
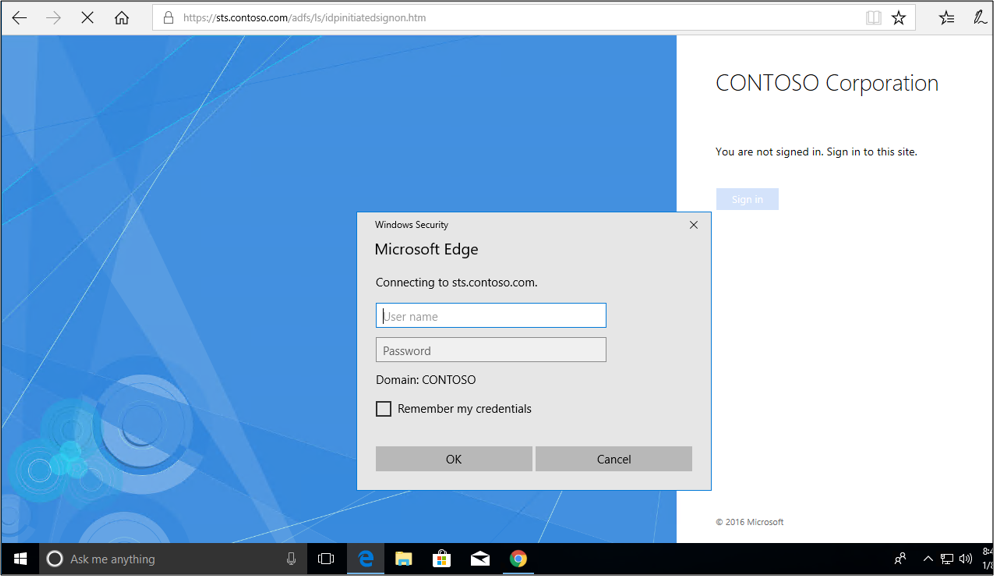
If the process succeeds, you're signed in.
Test authentication with seamless sign-in
You can test the seamless sign-in experience by making sure that the URL for your AD FS servers is added to the local intranet zone of your internet options. Use the following procedure:
On a Windows 10 client, select Start, enter internet options, and select Internet Options.
Select the Security tab, and then select Local intranet > Sites.

Select Advanced.
Enter your URL, and then select Add > Close.
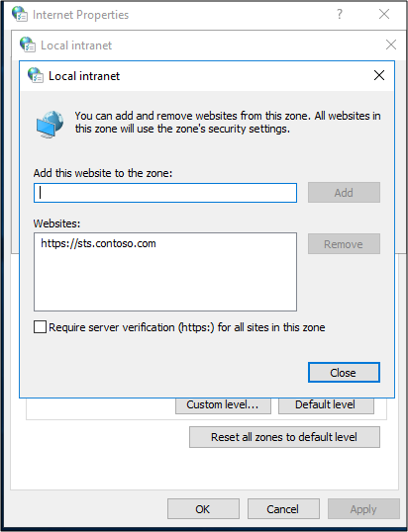
Select OK. Then select OK to close the internet options.
Open a web browser and go to the IdP sign-in page. Your URL might look like
https://sts.contoso.com/adfs/ls/idpinitiatedsignon.aspx.Select Sign in. You should automatically sign in and not be prompted for credentials.
Known issues
The AD FS sign-in page can't be used to initiate a sign-in with a claims provider trust that's configured with a WS-Federation passive endpoint only.