Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article describes how to install and configure the Microsoft Defender for Containers sensor on AKS, EKS, and GKE clusters by using Helm.
Defender for Containers supports multiple deployment models for deploying the sensor, including automatic provisioning and Helm-based installation. Helm-based deployment provides greater control over sensor versioning and upgrade timing, but it shifts some operational responsibility to you. When using Helm-based deployment, consider:
Sensor upgrades: By using Helm-based deployment, you manage sensor upgrades and upgrade timing. Automatic provisioning follows Microsoft-managed rollout schedules.
Automatic installation flows: When deploying the sensor by using Helm, skip automatic installation prompts and recommendations in the Azure portal to avoid conflicts with the existing deployment.
Prerequisites
Before you install the sensor by using Helm, make sure that:
You implement all prerequisite requirements for the Defender for Containers sensor as described in the Defender sensor network requirements.
Defender for Containers is enabled in the target subscription or security connector:
- Azure subscription: Enable Defender for Containers on AKS via portal
- Amazon Web Services (AWS): Enable Defender for Containers on AWS (EKS) via portal
- Google Cloud Project (GCP): Enable Defender for Containers on GCP (GKE) via portal
- Arc-enabled Kubernetes: Enable Defender for Containers on Arc-enabled Kubernetes via portal
The following components of the Defender for Containers plan are enabled:
- Defender sensor
- Kubernetes API access
For AWS and GCP environments: make sure the Auto provision Defender's sensor for Azure Arc toggle is disabled.
If you want to keep automatic provisioning enabled for other Arc-enabled clusters in the AWS account or GCP project, apply the
ms_defender_e2e_discovery_exclude=truetag to clusters where you intend to deploy the sensor by using Helm.Your environment doesn't have conflicting policy assignments that can deploy the generally available version of the sensor.
Review policy assignments that use the following policy definition ID, and remove any conflicting assignments:
64def556-fbad-4622-930e-72d1d5589bf5To review policy definitions, go to Policy definitions in the Azure portal, and search for the policy definition ID.
Install the Helm chart
Defender for Containers Helm charts are published to mcr.microsoft.com/azuredefender/microsoft-defender-for-containers.
The chart requires cluster identifier values under global.cloudIdentifiers. You can provide these values inline with --set, as shown in the following examples, or by using a values file.
To install the latest chart version, use the base Helm install command. Provide the required global.cloudIdentifiers values by using a values file or inline with --set, as shown in the environment-specific examples:
helm install defender-k8s oci://mcr.microsoft.com/azuredefender/microsoft-defender-for-containers
You can list the published versions by running the following command:
curl https://mcr.microsoft.com/v2/azuredefender/microsoft-defender-for-containers/tags/list
To install a specific version, include the version tag:
helm install defender-k8s oci://mcr.microsoft.com/azuredefender/microsoft-defender-for-containers:<tag>
To inspect configurable chart values, such as feature flags or pod resource limits, pull the chart and review the values.yaml file:
helm pull oci://mcr.microsoft.com/azuredefender/microsoft-defender-for-containers
To install the sensor for your environment:
For standard AKS clusters, use the mdc namespace.
For AKS Automatic clusters, use the kube-system namespace.
If your AKS cluster already has an existing Defender for Containers deployment, disable the existing deployment as described in Configure Defender for Containers for Azure, and remove any leftover resources by running the following commands:
kubectl delete crd/policies.defender.microsoft.com || true
kubectl delete crd/runtimepolicies.defender.microsoft.com || true
kubectl delete crd/securityartifactpolicies.defender.microsoft.com || true
kubectl delete ClusterRole defender-admission-controller-cluster-role || true
kubectl delete ClusterRole defender-admission-controller-resource-cluster-role || true
kubectl delete ClusterRoleBinding defender-admission-controller-cluster-role-binding || true
kubectl delete ClusterRoleBinding defender-admission-controller-cluster-resource-role-binding || true
Install the sensor:
helm install defender-k8s oci://mcr.microsoft.com/azuredefender/microsoft-defender-for-containers \
--create-namespace --namespace <namespace> \
--set global.cloudIdentifiers.Azure.subscriptionId="<cluster-subscription-id>" \
--set global.cloudIdentifiers.Azure.resourceGroupName="<cluster-resource-group>" \
--set global.cloudIdentifiers.Azure.clusterName="<cluster-name>" \
--set global.cloudIdentifiers.Azure.region="<cluster-region>"
Replace <namespace> with:
mdcfor standard AKS clusters.kube-systemfor AKS Automatic clusters.
Verify the installation
Verify that the installation succeeded by using the namespace you used during installation.
helm list --namespace mdc
The installation is successful if the STATUS field displays deployed.
Configure security rules for gated deployment
Note
Kubernetes gated deployment is supported on AKS Automatic clusters only when the sensor is installed by using Helm in the kube-system namespace. Add-on deployment isn’t supported for this scenario.
Important
When you create rules, the selected subscription might show as not supported for Gated deployment. This status occurs because you installed the Defender for Containers components by using Helm rather than through the dashboard's automatic installation.
Define security rules to control what you can deploy into your Kubernetes clusters. These rules help you block or audit container images based on security criteria, such as images with too many vulnerabilities.
Sign in to the Azure portal.
Go to Defender for Cloud > Environment settings.
Select Security rules.
Select Gated deployment > Vulnerability assessment.
Select a rule to edit it, or select + Add rule to create a new one.
Handle existing recommendations
Important
If you install the sensor by using Helm, don't use existing Defender for Cloud recommendations to install the Defender profile or Arc extension for the same cluster. Remediating these recommendations can create a conflicting deployment.
Depending on your deployment type, the following recommendations might still appear in Defender for Cloud:
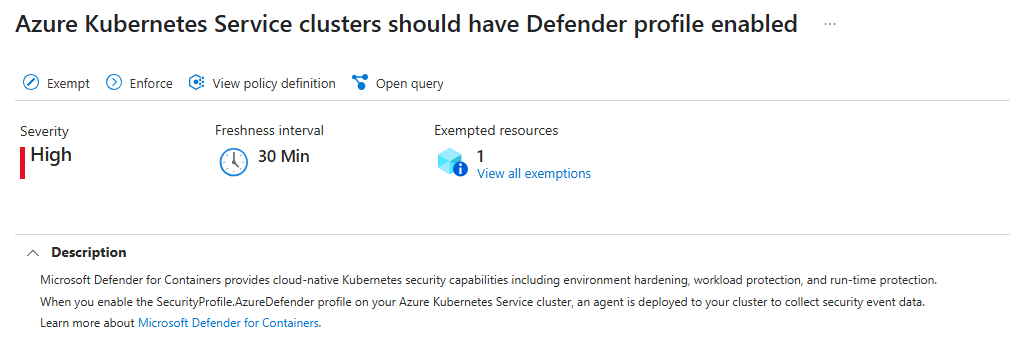
Azure: Azure Kubernetes Service clusters should have Defender profile enabled - Microsoft Azure
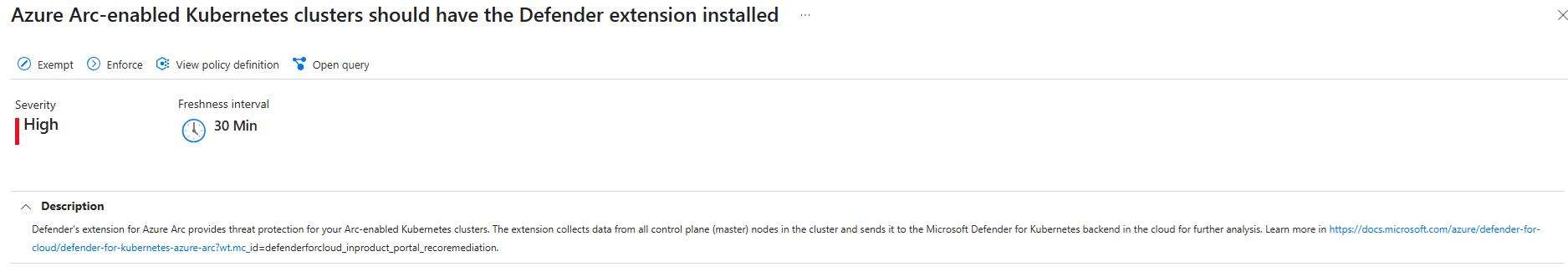
Arc-enabled Kubernetes clusters: Azure Arc-enabled Kubernetes clusters should have the Defender extension installed - Microsoft Azure
Upgrade an existing Helm-based deployment
With Helm-based deployment, you manage sensor upgrades. Defender for Cloud doesn't automatically apply them.
Run the following command to update an existing Helm-based deployment. Use the namespace you used during installation.
helm upgrade defender-k8s \
oci://mcr.microsoft.com/azuredefender/microsoft-defender-for-containers \
--namespace <namespace> \
--reuse-values
For <namespace>, use:
mdcfor standard AKS, EKS, and GKE clusters.kube-systemfor AKS Automatic clusters.
If the upgrade fails because of resource conflicts, add the following options to the upgrade command:
--server-side=true --resolve-conflicts