Welcome to our new Microsoft Q&A Platform.
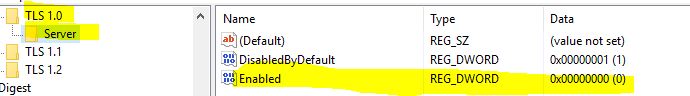
Based on your description, we could knew that you've only created the subkey named Server under the Registry key Protocols. It controls the the use of TLS 1.0 Protocol on the TLS server, which means when you configure to disable it, the other machine cannot access this machine through TLS 1.0 Protocol. But not making this computer don't have access to the other computers through the TLS 1.0 protocol.
If you don't want this machine have access to other machine through TLS 1.0 protocol. You could create a subkey named Client under the Registry key named Protocols (Registry path: HKLM SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols).
To enable the TLS 1.0 protocol, create an Enabled entry in either the Client subkey. This entry does not exist in the registry by default. After you have created the entry, change the DWORD value to 1. To disable TLS 1.0 for Client, change the DWORD value to 0. If an SSPI app requests to use TLS 1.0, it will be denied. To disable TLS 1.0 by default, create a DisabledByDefault entry and change the DWORD value to 1. If an SSPI app explicitly requests to use TLS 1.0, it may be negotiated.
Also providing you some articles for you to refer:
Transport Layer Security (TLS) registry settings: https://learn.microsoft.com/en-us/windows-server/security/tls/tls-registry-settings#tls-10
How to disable TLS 1.0 in Windows 10: https://windowsreport.com/how-to-disable-tls-1-0/
Hopefully those things above will help you.