Theoretical Thinking and the June 2014 Bulletin Release
As security professionals, we are trained to think in worst-case scenarios. We run through the land of the theoretical, chasing “what if” scenarios as though they are lightning bugs to be gathered and stashed in a glass jar. Most of time, this type of thinking is absolutely the correct thing for security professionals to do. We need to be prepared for when, not if, these disruptive events occur. However, every now and then, it can be productive to draw ourselves out of this hypothetical mentality and look instead at the real impact in the here and now.
Speaking of the here and now, today we release seven security bulletins, two rated Critical and five rated Important in severity, addressing 66 Common Vulnerabilities and Exposures (CVEs) for Microsoft Windows, Internet Explorer, and Microsoft Office customers. But before we get into the details of the updates, I want to take a moment to provide some additional insight into how we assess and recommend those severity ratings. For every issue, we consider ”what if”– what’s the severest outcome from a potential cyberattack? We want to provide our best guidance on the risk assessment for our customers, and that requires consideration of the worst-case scenario.
If we consider the worst-case scenario analogous to a tree falling in the woods, is there a sound if no one is around to hear it? Similarly, does a vulnerability make a sound if it never gets exploited? When we become aware of a potential security issue, we work to fix it regardless of whether or not it is under active attack. In other words, it doesn’t matter if that falling tree makes a noise; we still have an action to take. Why? Because one day in the future, it’s possible what we’re delivering today could get exploited if not addressed. However, we’re not in the future; we’re in the land of the here and now. And while we are in this land, we sometimes confuse theoretical thinking with the actuality of impact to real people. Until something actually occurs it is still theory; we’re taking the theoretical and making practical updates against future “what ifs”.
Let’s look at an example from this month’s release. The security bulletin for Internet Explorer (IE) resolves 59 items, including CVE-2014-1770. The most serious of these could allow remote code execution if a user views a webpage specially crafted by a cybercriminal. We still haven’t seen any active attacks attempting to exploit any of the other CVEs addressed by this bulletin. While there are a number of things being addressed this time around, it’s important to note that, to our knowledge, none of these now-addressed CVEs have caused any customer impact to date.
Addressing items before active attacks occur helps keep customers better protected. The Internet Explorer update for this month includes additional security updates that will help protect our customers, which is yet another reason why it’s good to stay current with the latest updates.
If you’ve seen the recent blog from the IE team, you’ll also see another message: Customers should update to the latest version of Internet Explorer. For Windows 7 and Windows 8.1, that means Internet Explorer 11—the most modern, secure browser we’ve ever built. IE11 has advanced security features like Enhanced Protection Mode (EPM) and SmartScreen Filter, support for modern web standards, and Enterprise Mode for rendering legacy web apps. Internet Explorer 11 is much more secure than older versions, which is why we encourage customers to upgrade.
There are six other bulletins released today to improve your security as well. For more information about this month’s security updates, including the detailed view of the Exploit Index broken down by CVE, visit the Microsoft Bulletin Summary Web page.
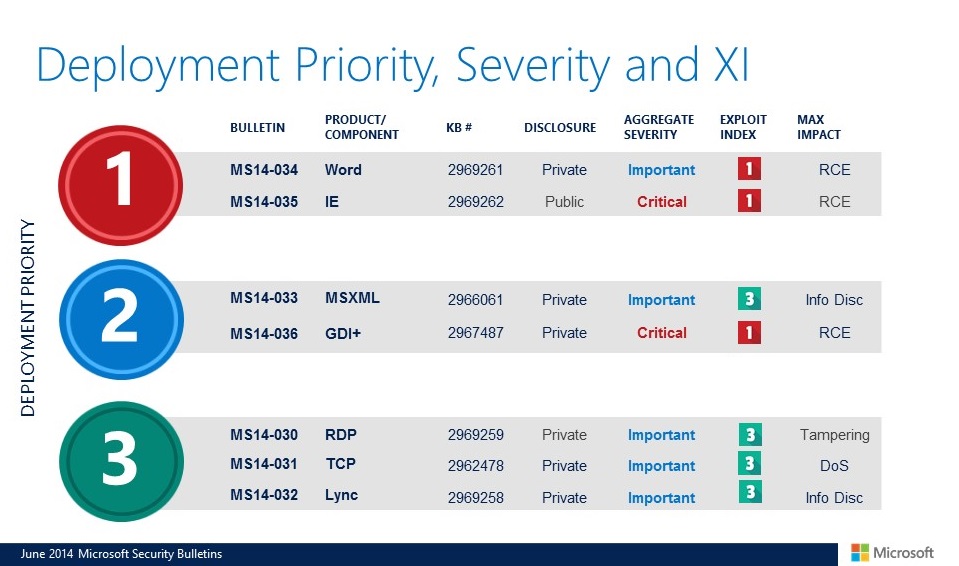
Here’s an overview of all the updates released today:
As always, we encourage you to apply all of the updates, but for those who prioritize, we recommend the Word and Internet Explorer updates be on the top of your list.
Finally, we are revising Security Advisory 2755801 with the latest update for Adobe Flash Player. in Internet Explorer. The update addresses the vulnerabilities described in Adobe Security bulletin APSB14-16. For more information about this update, including download links, see Microsoft Knowledge Base Article 2966072.
Watch the bulletin overview video below for a brief summary of today's releases.
Andrew Gross and I will host the monthly security bulletin webcast, scheduled for Wednesday, June 11, 2014, at 11 a.m. PDT. I invite you to register here, and tune in to learn more about this month’s security bulletins.
For all the latest information, you can also follow us at @MSFTSecResponse.
I look forward to hearing any questions about this month’s release during our webcast tomorrow.
Thanks,
Dustin Childs
Group Manager, Response Communications
Microsoft Trustworthy Computing
Comments
- Anonymous
June 10, 2014
Pingback from Theoretical Thinking and the June 2014 Bulletin Release - The WSUS Support Team Blog - Site Home - TechNet Blogs - Anonymous
June 10, 2014
Pingback from Theoretical Thinking and the June 2014 Bulletin Release - The WSUS Support Team Blog - Site Home - TechNet Blogs - Anonymous
June 10, 2014
Pingback from Theoretical Thinking and the June 2014 Bulletin Release - The WSUS Support Team Blog - Site Home - TechNet Blogs