Connect Azure Front Door Premium to a storage static website with Private Link
This article guides you through how to configure Azure Front Door Premium tier to connect to your storage static website privately using the Azure Private Link service.
Prerequisites
- An Azure account with an active subscription. You can create an account for free.
- Create a Private Link service for your origin web server.
- Storage static website is enabled on your storage account. Learn how to enable static website.
Enable Private Link to a storage static website
In this section, you map the Private Link service to a private endpoint created in Azure Front Door's private network.
Sign in to the Azure portal.
Within your Azure Front Door Premium profile, under Settings, select Origin groups.
Select the origin group that contains the storage static website origin you want to enable Private Link for.
Select + Add an origin to add a new storage static website origin or select a previously created storage static website origin from the list.
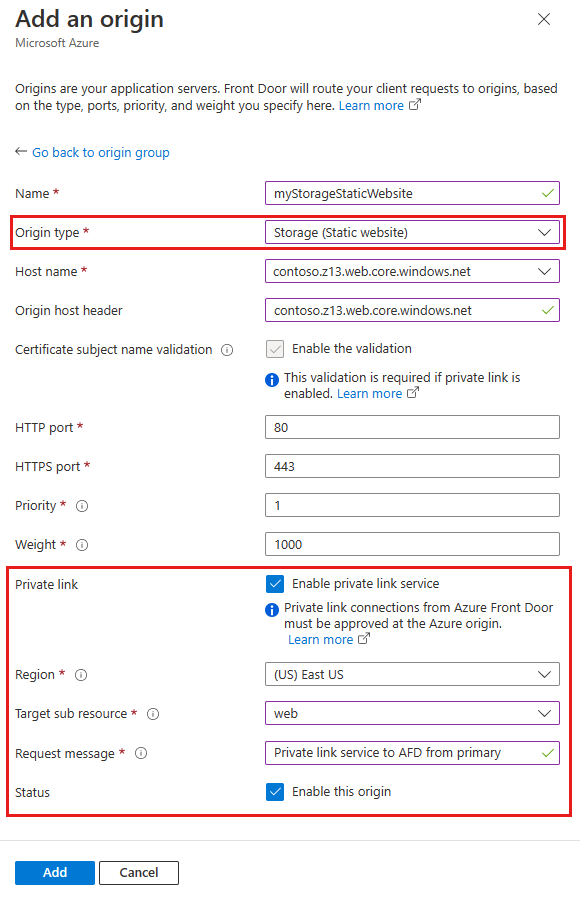
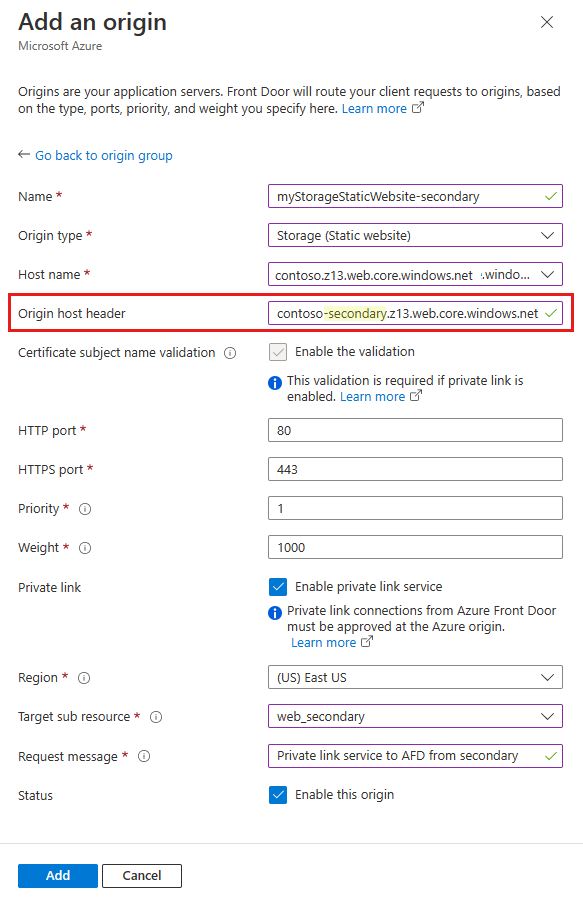
The following table has the information of what values to select in the respective fields while enabling private link with Azure Front Door. Select or enter the following settings to configure the storage static website you want Azure Front Door Premium to connect with privately.
Setting Value Name Enter a name to identify this storage static website origin. Origin Type Storage (Static website) Host name Select the host from the dropdown that you want as an origin. Origin host header You can customize the host header of the origin or leave it as default. HTTP port 80 (default) HTTPS port 443 (default) Priority Different origin can have different priorities to provide primary, secondary, and backup origins. Weight 1000 (default). Assign weights to your different origin when you want to distribute traffic. Region Select the region that is the same or closest to your origin. Target sub resource The type of subresource for the resource selected previously that your private endpoint can access. You can select web or web_secondary. Request message Custom message to see while approving the Private Endpoint. Then select Add to save your configuration. Then select Update to save your changes.
Approve private endpoint connection from storage account
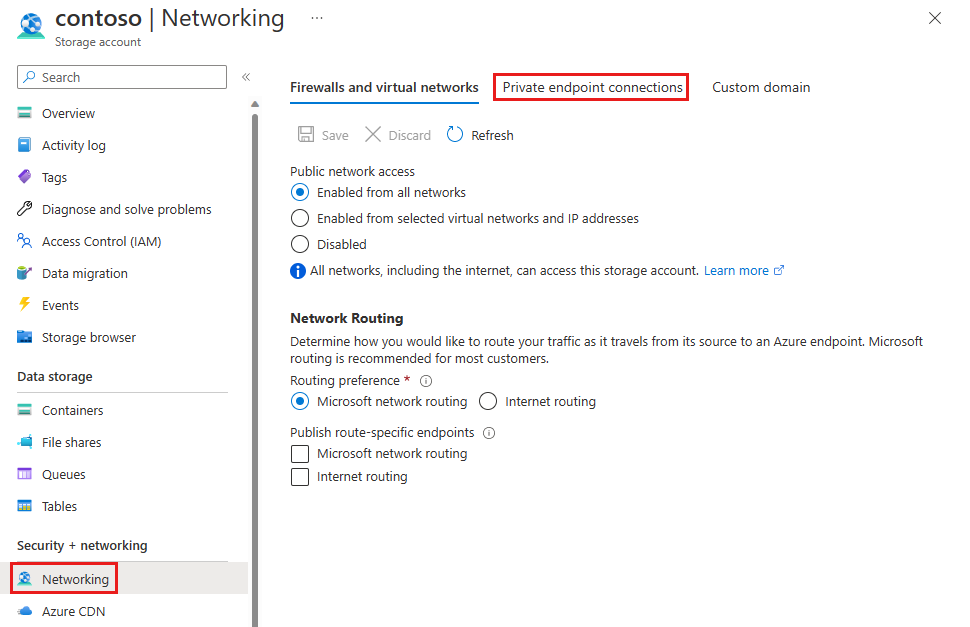
Go to the storage account that you want to connect to Azure Front Door Premium privately. Select Networking under Settings.
In Networking, select Private endpoint connections.
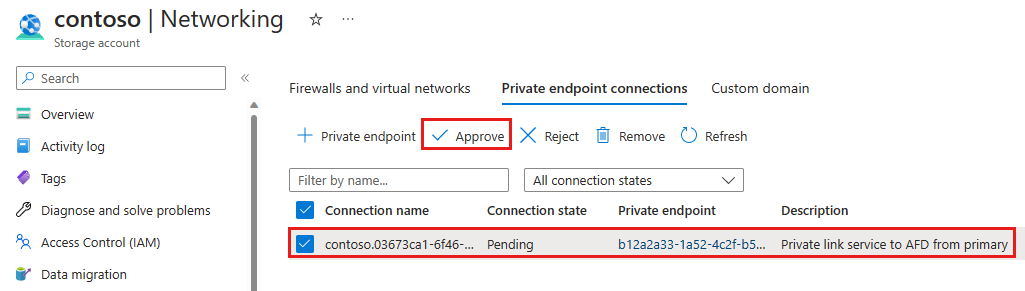
Select the pending private endpoint request from Azure Front Door Premium then select Approve.
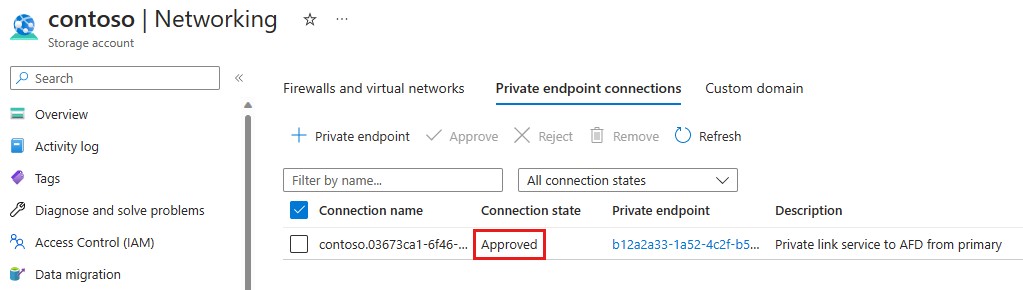
Once approved, you can see the private endpoint connection status is Approved.
Create private endpoint connection to web_secondary
When creating a private endpoint connection to the storage static website's secondary sub resource, you need to add a -secondary suffix to the origin host header. For example, if your origin host header is contoso.z13.web.core.windows.net, you need to change it to contoso-secondary.z13.web.core.windows.net.
Once the origin is added and the private endpoint connection is approved, you can test your private link connection to your storage static website.
This article will guide you through how to configure Azure Front Door Premium tier to connect to your Storage Account privately using the Azure Private Link service with Azure CLI.
Prerequisites - CLI
Prerequisites
Use the Bash environment in Azure Cloud Shell. For more information, see Quickstart for Bash in Azure Cloud Shell.
If you prefer to run CLI reference commands locally, install the Azure CLI. If you're running on Windows or macOS, consider running Azure CLI in a Docker container. For more information, see How to run the Azure CLI in a Docker container.
If you're using a local installation, sign in to the Azure CLI by using the az login command. To finish the authentication process, follow the steps displayed in your terminal. For other sign-in options, see Sign in with the Azure CLI.
When you're prompted, install the Azure CLI extension on first use. For more information about extensions, see Use extensions with the Azure CLI.
Run az version to find the version and dependent libraries that are installed. To upgrade to the latest version, run az upgrade.
- An Azure account with an active subscription. Create an account for free.
- Have a functioning Azure Front Door Premium profile, an endpoint and an origin group. For more information on how to create an Azure Front Door profile, see Create a Front Door - CLI.
Enable Private Link to a Storage Static Website in Azure Front Door Premium
- Run az afd origin create to create a new Azure Front Door origin. Enter the following settings to configure the Storage Static Website you want Azure Front Door Premium to connect with privately. Notice the
private-link-locationmust be in one of the available regions and theprivate-link-sub-resource-typemust be web.
az afd origin create --enabled-state Enabled \
--resource-group testRG \
--origin-group-name default-origin-group \
--origin-name pvtStaticSite \
--profile-name testAFD \
--host-name example.z13.web.core.windows.net\
--origin-host-header example.z13.web.core.windows.net\
--http-port 80 \
--https-port 443 \
--priority 1 \
--weight 500 \
--enable-private-link true \
--private-link-location EastUS \
--private-link-request-message 'AFD Storage static website origin Private Link request.' \
--private-link-resource /subscriptions/00000000-0000-0000-0000-00000000000/resourceGroups/testRG/providers/Microsoft.Storage/storageAccounts/testingafdpl \
--private-link-sub-resource-type web
Approve Private Endpoint Connection from Storage Account
- Run az network private-endpoint-connection list to list the private endpoint connections for your storage account. Note down the 'Resource ID' of the private endpoint connection available in your storage account, in the first line of your output.
az network private-endpoint-connection list -g testRG -n testingafdpl --type Microsoft.Storage/storageAccounts
- Run az network private-endpoint-connection approve to approve the private endpoint connection.
az network private-endpoint-connection approve --id /subscriptions/00000000-0000-0000-0000-000000000000/resourceGroups/testRG/providers/Microsoft.Storage/storageAccounts/testingafdpl/privateEndpointConnections/testingafdpl.00000000-0000-0000-0000-000000000000
Create Private Endpoint Connection to Web_Secondary
When creating a private endpoint connection to the storage static website's secondary sub-resource, you need to add a -secondary suffix to the origin host header. For example, if your origin host header is example.z13.web.core.windows.net, you need to change it to example-secondary.z13.web.core.windows.net.
Once the origin is added and the private endpoint connection is approved, you can test your private link connection to your storage static website.
Next steps
Learn about Private Link service with storage account.
