Network Access Protection (NAP) with System Center 2012 Configuration Manager
Network Access Protection (NAP) with System Center 2012 Configuration Manager
I am going to document (with screen shots) how to integrate System Center 2012 Configuration Manager with Microsoft Network Access Protection (NAP). All Servers are running Windows Server 2012 and clients are Windows 8.
There are different ways to implement NAP:
I setup a basic NAP implementation using DHCP Enforcement. The NAP DHCP server is running on a Windows Server 2012 Domain Controller with the DHCP server role installed along with Network Policy and Access Services Role. The NAP DHCP server restricts noncompliant client access by providing a limited IP address configuration to computers that do not meet health requirements. A limited access configuration has a subnet mask of 255.255.255.255 and no default gateway.
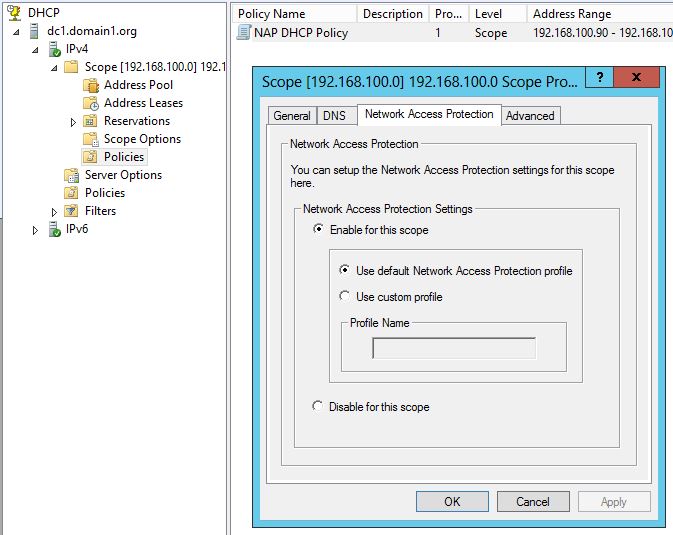
I will not go into detail on how to setup NAP, but here is a screen shot on how to enable it on DHCP. I also set a DHCP Policy to enable User Class for NAP and MAC Filter so I can target only a couple of machines in my lab environment.
Now for Configuration Manager integration...
Step 1: Install System Health Validator Point:
A System Health Validator point validates Configuration Manager Network Access Protection (NAP) policies. It must be installed on a NAP health policy server. In my lab environment, I installed the System Health Validator Point on my Domain Control that is also my DHCP and Network Policy and Access Server.
There are no properties to configure for this site system role. Configure the System Health Validator point component configuration for settings that apply to all System Health Validator points in the site.
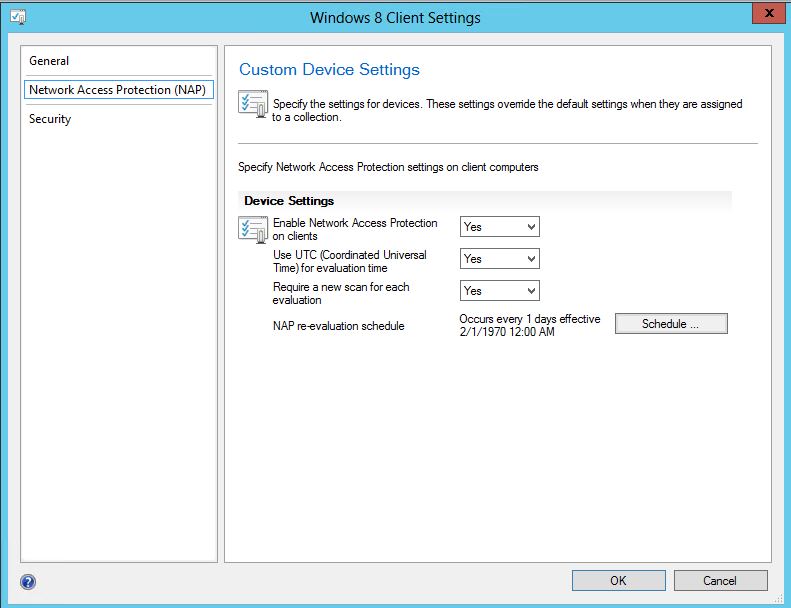
Step 2: Enable Network Access Protection on clients:
I created a separate Client Agent Policy that enables NAP. Then deployed it only to my Windows 8 Systems Collection. Here is a screen shot:
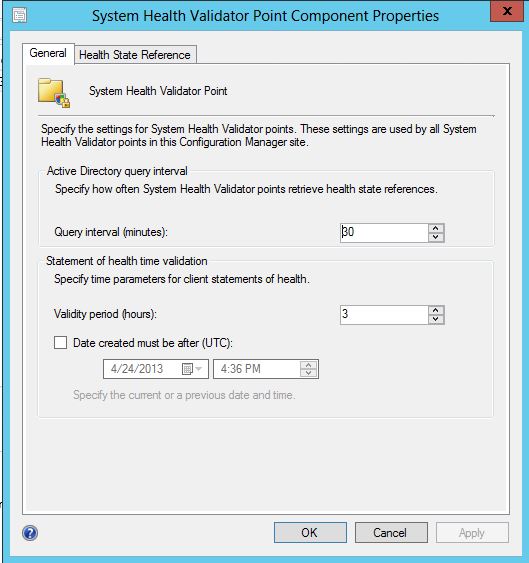
Step 3: Configure Site Component (optional)
There are a few Component properties that can be adjusted: Active Directory query interval (minutes), Statement of health time validation (hours) and Designate an Active Directory forest in different. In my lab environment, I left the default settings. Screen shot below:
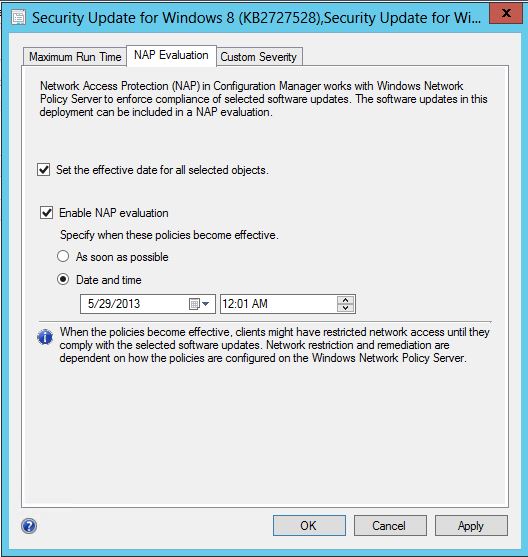
Step 4 (Final Step): Enable Software Updates for NAP Evaluation
Select 1 or more Software Updates (hold down control key) from a Software Update Group and/or Software Update Deployment Package, click the NAP Evaluation Tab and select to enable NAP Evaluation.
I then deployed Software Updates to Windows 8 System Collection. I marked the Deployment as Available to help with Screen Shots and Demos from the Client Side.
Windows 8 Client experience...
On the Windows Client system, I setup the Network Access Protection Service to Automatic and started the service. I have enabled Windows Security Health Agent (SHA) to check the following:
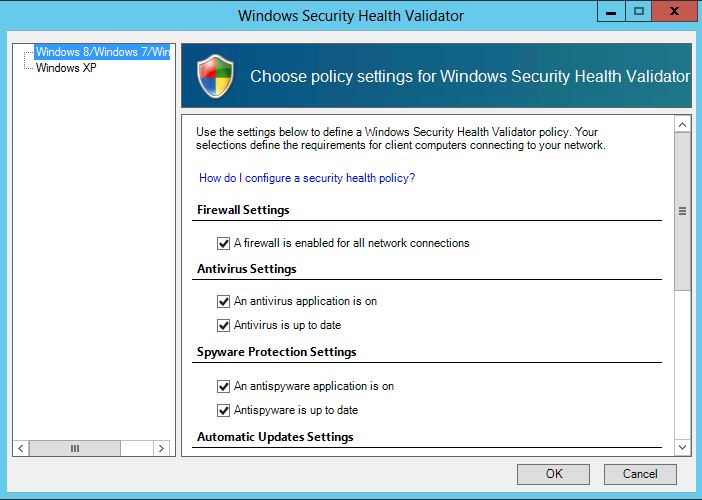
Firewall Settings
-
- A firewall is enabled for all network connections
Antivirus Settings
-
- An antivirus application is on
- Antivirus is up to date
Spyware Protection Settings
-
- An antispyware application is on
- Antispyware is up to date
I did NOT enable the following (these will be handled by System Center 2012 Configuration Manager):
Automatic Updates Settings
Security Updates Settings
These settings are configured on the Network Policy Server, screen shot below:
I have enabled Configuration Manager 2012 System Health Agent (SHA) to check the following:
Software Updates:
-
- Security Update for Microsoft Windows (KB2830290)
- Security Update for Microsoft Windows (KB2829361)
- Adobe Reader 10.1.7 Update*
- Adobe Flash Player 32-bit/64-bit ActiveX 11.7.700.202*
*I have installed and configured System Center Updates Publisher 2011 to integrate with Configuration Manager. Now I am able to add 3rd Party Updates to the NAP Policy (i.e. Adobe Reader, Flash, etc...)
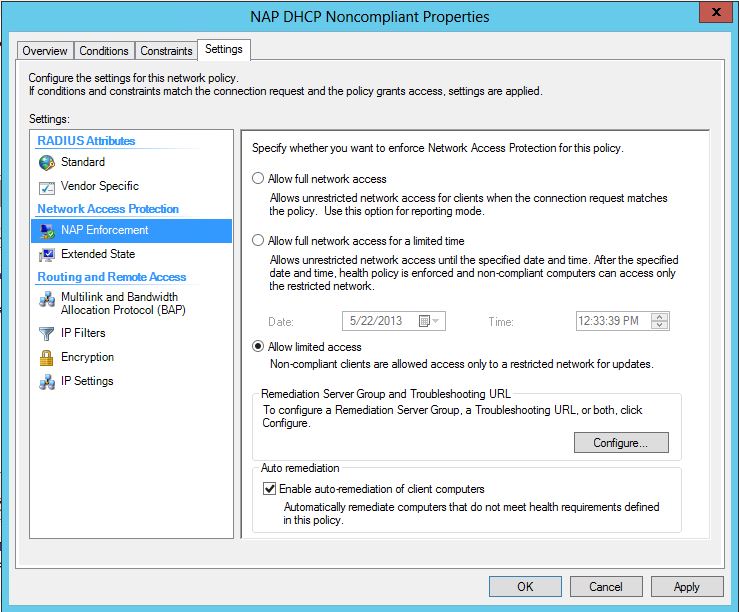
The default settings for NAP Enforcement on Non-compliant systems is "Allow limited access". Non-compliant clients are allowed access only to a restricted network for updates. I configured my Remediation Server Group to include Network Policy Server and Configuration Manager Server. This way, clients can still access Remediation Servers while having limited network access.
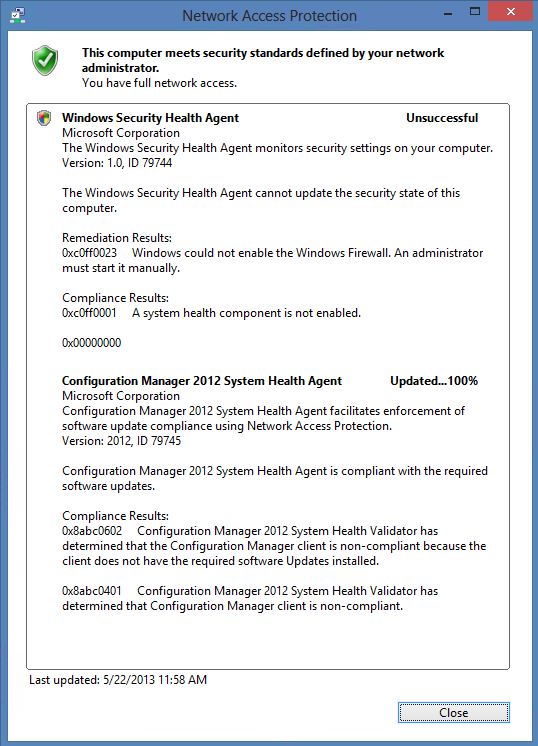
However, for demo purposes, I checked "Allow full network access" for Non-Complaint Systems. That is why the screen shot below will show "You have full network access"
Windows Security Health Agent is unsuccessful because I have disable Windows Firewall. You can have NAP Automatically Remediate the firewall if it is not enforced by Local or Domain Group Policy.
Configuration Manager 2012 System Health Agent is unsuccessful (non-compliant) because I uninstalled Security Update KB2830290. The first time I logged in with NAP enabled, Configuration Manager automatically installed the Security Updates to make the client Compliant. I went back and manually removed the Update so NAP will report Non-Compliant for this screen shot.
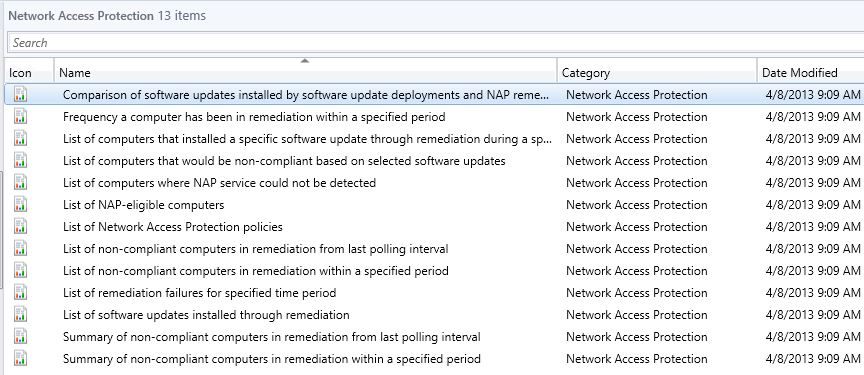
Monitoring
And finally, all Network Access Protection can be monitored from Configuration Manager Reporting. You can sort by Category - Network Access Protection and there are 13 built-in reports.