로그인 보고서에서 자사 Microsoft 애플리케이션 확인
참고 항목
이 문서가 도움이 되었나요? 귀하의 입력은 우리에게 중요합니다. 이 페이지의 피드백 단추를 사용하여 이 문서가 얼마나 잘 작동했는지 또는 어떻게 개선할 수 있는지 알려주세요.
로그인 보고서를 검토할 때 소유하지 않고 식별하려는 애플리케이션이 로그인 보고서에 표시될 수 있습니다. 앱에 액세스한 기억이 없다면 해당 앱에 어떻게 로그인했는지 궁금할 수도 있습니다.
로그인 보고서 예제는 다음과 같습니다.
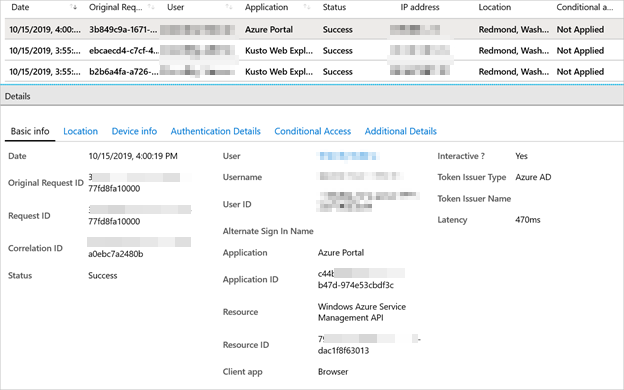
예를 들어 액세스할 learn.microsoft.com때 로그인 로그에 표시되는 애플리케이션이 표시 dev-rel-auth-prod되나 이에 대한 설명 learn.microsoft.com은 아닙니다.
로그인 보고서에 나열된 앱은 Microsoft가 소유하고 있으며 의심스러운 응용 프로그램은 아니지만 Microsoft Entra 로그에 있는 Microsoft Entra 서비스 주체를 소유하고 있는지 여부를 확인할 수 있습니다.
참고 항목
자사 Microsoft 애플리케이션이 항상 테넌트에서 만들어진 서비스 주체가 되는 것은 아닙니다. 이 경우 로그인 보고서에서 애플리케이션을 계속 볼 수 있습니다. 이 문서에서는 일반적으로 사용되는 Microsoft 애플리케이션의 애플리케이션 ID를 나열합니다.
Microsoft Entra 테넌트에서 자사 Microsoft 서비스 주체 확인
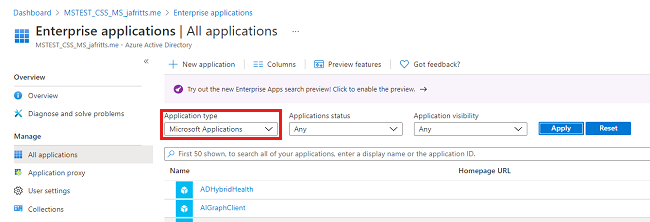
Microsoft Entra ID에서 엔터프라이즈 애플리케이션 목록을 엽니다.
탐색 창에서 모든 애플리케이션을 선택합니다.
애플리케이션 유형 드롭다운 목록에서 Microsoft 애플리케이션을 선택한 다음 적용을 선택합니다. 여기에 나열된 모든 애플리케이션은 Microsoft에서 소유합니다.
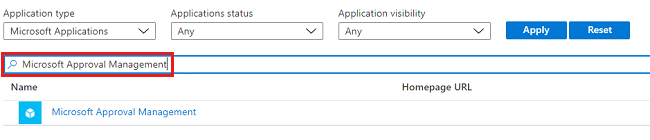
드롭다운 목록 아래의 검색 상자에서 특정 표시 이름 또는 응용 프로그램 ID를 추가하여 Microsoft 애플리케이션 목록을 필터링합니다.
원하는 앱을 선택한 다음 탐색 창에서 속성을 선택하여 나열된 앱의 속성을 봅니다. 다음 오류 메시지가 표시되는지 확인합니다.
You can't delete this application because it's a Microsoft first party application.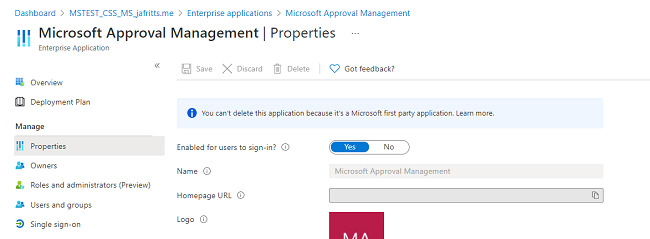
PowerShell을 통해 자사 Microsoft 서비스 주체 확인
PowerShell에서 Azure Active Directory 모듈을 엽니다.
PowerShell 모듈에서 다음 cmdlet을 입력합니다.
Get-AzureADServicePrincipal -Filter "DisplayName eq '<display-name>'" | fl *앱의 실제 표시 이름으로 바꿉
<display name>다.참고 항목
Azure AD와 MSOnline PowerShell 모듈은 2024년 3월 30일부터 더 이상 사용되지 않습니다. 자세히 알아보려면 사용 중단 업데이트를 참조하세요. 이 날짜 이후에는 이러한 모듈에 대한 지원이 Microsoft Graph PowerShell SDK 및 보안 수정 사항에 대한 마이그레이션 지원으로 제한됩니다. 사용되지 않는 모듈은 2025년 3월 30일까지 계속 작동합니다.
Microsoft Graph PowerShell로 마이그레이션하여 Microsoft Entra ID(이전의 Azure AD)와 상호 작용하는 것이 좋습니다. 일반적인 마이그레이션 관련 질문은 마이그레이션 FAQ를 참조하세요. 참고 항목: MSOnline 버전 1.0.x는 2024년 6월 30일 이후 중단될 수 있습니다.
결과를 검토합니다
AppOwnerTenantId.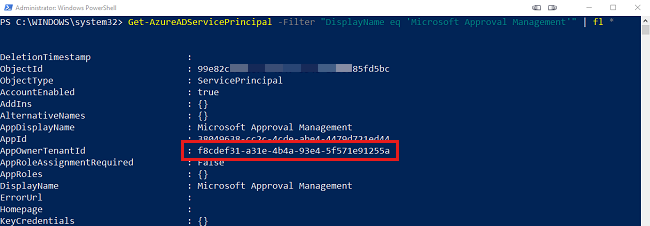
스크린샷
f8cdef31-a31e-4b4a-93e4-5f571e91255a은 Microsoft 서비스의 Microsoft Entra 테넌트 ID입니다.
일반적으로 사용되는 Microsoft 애플리케이션의 애플리케이션 ID
다음 표에는 일부 자사 Microsoft 애플리케이션이 나와 있습니다. 이러한 애플리케이션은 Microsoft Entra ID의 로그인 보고서에 표시할 수 있습니다.
| 애플리케이션 이름 | 애플리케이션 ID |
|---|---|
| ACOM Azure 웹 사이트 | 23523755-3a2b-41ca-9315-f81f3f566a95 |
| ADIbizaUX | 74658136-14ec-4630-ad9b-26e160ff0fc6 |
| AEM-DualAuth | 69893ee3-dd10-4b1c-832d-4870354be3d8 |
| App Service | 7ab7862c-4c57-491e-8a45-d52a7e023983 |
| ASM 캠페인 서비스 | 0cb7b9ec-5336-483b-bc31-b15b5788de71 |
| Azure Advanced Threat Protection | 7b7531ad-5926-4f2d-8a1d-38495ad33e17 |
| Azure Data Lake | e9f49c6b-5ce5-44c8-925d-015017e9f7ad |
| Azure Lab Services 포털 | 835b2a73-6e10-4aa5-a979-21dfda45231c |
| Azure Portal | c44b4083-3bb0-49c1-b47d-974e53cbdf3c |
| Azure SQL Database | 022907d3-0f1b-48f7-badc-1ba6abab6d66 |
| AzureSupportCenter | 37182072-3c9c-4f6a-a4b3-b3f91cacffce |
| Bing | 9ea1ad79-fdb6-4f9a-8bc3-2b70f96e34c7 |
| ContactsInferencingEmailProcessor | 20a11fe0-faa8-4df5-baf2-f965f8f9972e |
| CPIM 서비스 | bb2a2e3a-c5e7-4f0a-88e0-8e01fd3fc1f4 |
| CRM Power BI 통합 | e64aa8bc-8eb4-40e2-898b-cf261a25954f |
| Dataverse | 00000007-0000-0000-c000-0000000000000 |
| 엔터프라이즈 로밍 및 백업 | 60c8bde5-3167-4f92-8fdb-059f6176dc0f |
| Exchange 관리 센터 | 497effe9-df71-4043-a8bb-14cf78c4b63b |
| FindTime | f5eaa862-7f08-448c-9c4e-f4047d4d4521 |
| 중요 받은 편지함 | b669c6ea-1adf-453f-b8bc-6d526592b419 |
| GroupsRemoteApiRestClient | c35cb2ba-f88b-4d15-aa9d-37bd443522e1 |
| HxService | d9b8ec3a-1e4e-4e08-b3c2-5baf00c0fcb0 |
| IAM 지원 가능성 | a57aca87-cbc0-4f3c-8b9e-dc095fdc8978 |
| IrisSelectionFrontDoor | 16aeb910-ce68-41d1-9ac3-9e1673ac9575 |
| MCAPI Authorization Prod | d73f4b35-55c9-48c7-8b10-651f6f2acb2e |
| 미디어 분석 및 변환 서비스 | 944f0bd1-117b-4b1c-af26-804ed95e767e 0cd196ee-71bf-4fd6-a57c-b491ffd4fb1e |
| Microsoft 365 보안 및 준수 센터 | 80ccca67-54bd-44ab-8625-4b79c4dc7775 |
| Microsoft 365 지원 서비스 | ee272b19-4411-433f-8f28-5c13cb6fd407 |
| Microsoft 앱 액세스 패널 | 0000000c-0000-0000-c000-0000000000000 |
| Microsoft 승인 관리 | 65d91a3d-ab74-42e6-8a2f-0add61688c74 38049638-cc2c-4cde-abe4-4479d721ed44 |
| Microsoft 인증 브로커 | 29d9ed98-a469-4536-ade2-f981bc1d605e |
| Microsoft Azure CLI | 04b07795-8ddb-461a-bbee-02f9e1bf7b46 |
| Microsoft Azure PowerShell | 1950a258-227b-4e31-a9cf-717495945fc2 |
| MicrosoftAzureActiveAuthn | 0000001a-0000-0000-c000-0000000000000 |
| Microsoft Bing Search | cf36b471-5b44-428c-9ce7-313bf84528de |
| Microsoft Edge용 Microsoft Bing Search | 2d7f3606-b07d-41d1-b9d2-0d0c9296a6e8 |
| Microsoft Bing 기본 검색 엔진 | 1786c5ed-9644-47b2-8aa0-7201292175b6 |
| Microsoft Defender for Cloud 앱 | 3090ab82-f1c1-4cdf-af2c-5d7a6f3e2cc7 |
| Microsoft Defender for Identity(이전의 Radius Aad Syncer) | 60ca1954-583c-4d1f-86de-39d835f3e452 |
| Microsoft Docs | 18fbca16-2224-45f6-85b0-f7bf2b39b3f3 |
| Microsoft Dynamics ERP | 00000015-0000-0000-c000-0000000000000 |
| Microsoft Edge Insider Addons Prod | 6253bca8-faf2-4587-8f2f-b056d80998a7 |
| Microsoft Exchange ForwardSync | 99b904fd-a1fe-455c-b86c-2f9fb1da7687 |
| Microsoft Exchange Online 보호 | 00000007-0000-0ff1-ce00-0000000000000 |
| Microsoft Exchange ProtectedServiceHost | 51be292c-a17e-4f17-9a7e-4b661fb16dd2 |
| Microsoft Exchange REST API 기반 Powershell | fb78d390-0c51-40cd-8e17-fdbfab77341b |
| Microsoft Exchange 웹 서비스 | 47629505-c2b6-4a80-adb1-9b3a3d233b7b |
| Microsoft Exchange 메시지 추적 서비스 | 6326e366-9d6d-4c70-b22a-34c7ea72d73d |
| Microsoft Forms | c9a559d2-7aab-4f13-a6ed-e7e9c52aec87 |
| Microsoft Graph | 00000003-0000-0000-c000-0000000000000 |
| Microsoft Intune 웹 회사 포털 | 74bcdadc-2fdc-4bb3-8459-76d06952a0e9 |
| Microsoft Intune Windows 에이전트 | fc0f3af4-6835-4174-b806-f7db311fd2f3 |
| Microsoft Office | d3590ed6-52b3-4102-aeff-aad2292ab01c |
| Microsoft Office 365 포털 | 00000006-0000-0ff1-ce00-000000000000 |
| Microsoft Office Web Apps 서비스 | 67e3df25-268a-4324-a550-0de1c7f97287 |
| Microsoft Online Syndication 파트너 포털 | d176f6e7-38e5-40c9-8a78-3998aab820e7 |
| Microsoft Outlook | 5d661950-3475-41cd-a2c3-d671a3162bc1 |
| Microsoft 암호 재설정 서비스 | 93625bc8-bfe2-437a-97e0-3d0060024faa |
| Microsoft Power BI | 871c010f-5e61-4fb1-83ac-98610a7e9110 |
| Microsoft Storefronts | 28b567f6-162c-4f54-99a0-6887f387bbcc |
| Microsoft Stream 포털 | cf53fce8-def6-4aeb-8d30-b158e7b1cf83 |
| Microsoft 기판 관리 | 98db8bd6-0cc0-4e67-9de5-f187f1cd1b41 |
| Microsoft 지원 | fdf9885b-dd37-42bf-82e5-c3129ef5a302 |
| Microsoft 팀 | 1fec8e78-bce4-4aaf-ab1b-5451cc387264 |
| Microsoft Teams Services | cc15fd57-2c6c-4117-a88c-83b1d56b4bbe |
| Microsoft Teams 웹 클라이언트 | 5e3ce6c0-2b1f-4285-8d4b-75ee78787346 |
| Microsoft Whiteboard 서비스 | 95de633a-083e-42f5-b444-a4295d8e9314 |
| O365 SkypeSpaces 수집 서비스 | dfe74da8-9279-44ec-8fb2-2aed9e1c73d0 |
| O365 Suite UX | 4345a7b9-9a63-4910-a426-35363201d503 |
| Office 365 Exchange Online | 00000002-0000-0ff1-ce00-0000000000000 |
| Office 365 Management | 00b41c95-dab0-4487-9791-b9d2c32c80f2 |
| Office 365 Search Service | 66a88757-258c-4c72-893c-3e8bed4d6899 |
| Office 365 SharePoint Online | 00000003-0000-0ff1-ce00-0000000000000 |
| Office Delve | 94c63fef-13a3-47bc-8074-75af8c65887a |
| Office Online 추가 기능 SSO | 93d53678-613d-4013-afc1-62e9e444a0a5 |
| Office Online 클라이언트 Microsoft Entra ID - 확대 루프 | 2abdc806-e091-4495-9b10-b04d93c3f040 |
| Office Online 클라이언트 Microsoft Entra ID - Loki | b23dd4db-9142-4734-867f-3577f640ad0c |
| Office Online 클라이언트 Microsoft Entra ID - Maker | 17d5e35f-655b-4fb0-8ae6-86356e9a49f5 |
| Office Online 클라이언트 MSA- Loki | b6e69c34-5f1f-4c34-8cdf-7fea120b8670 |
| Office Online Core SSO | 243c63a3-247d-41c5-9d83-7788c43f1c43 |
| Office Online Search | a9b49b65-0a12-430b-9540-c80b3332c127 |
| Office.com | 4b233688-031c-404b-9a80-a4f3f2351f90 |
| Office365 Shell WCSS-Client | 89bee1f7-5e6e-4d8a-9f3d-ecd601259da7 |
| OfficeClientService | 0f698dd4-f011-4d23-a33e-b36416dcb1e6 |
| OfficeHome | 4765445b-32c6-49b0-83e6-1d93765276ca |
| OfficeShredderWacClient | 4d5c2d63-cf83-4365-853c-925fd1a64357 |
| OMSOctopiPROD | 62256cef-54c0-4cb4-bcac-4c67989bdc40 |
| OneDrive SyncEngine | ab9b8c07-8f02-4f72-87fa-80105867a763 |
| OneNote | 2d4d3d8e-2be3-4bef-9f87-7875a61c29de |
| Outlook Mobile | 27922004-5251-4030-b22d-91ecd9a37ea4 |
| 파트너 고객 위임 관리자 오프라인 프로세서 | a3475900-ccec-4a69-98f5-a65cd5dc5306 |
| 암호 위반 인증자 | bdd48c81-3a58-4ea9-849c-ebea7f6b6360 |
| PeoplePredictions | 35d54a08-36c9-4847-9018-93934c62740c |
| Power BI 서비스 | 00000009-0000-0000-c000-0000000000000 |
| 일정 계획 | ae8e128e-080f-4086-b0e3-4c19301ada69 |
| SharedWithMe | ffcb16e8-f789-467c-8ce9-f826a080d987 |
| SharePoint Online 웹 클라이언트 확장성 | 08e18876-6177-487e-b8b5-cf950c1e598c |
| 등록 | b4bddae8-ab25-483e-8670-df09b9f1d0ea |
| Skype for Business Online | 00000004-0000-0ff1-ce00-0000000000000 |
| SpoolsProvisioning | 61109738-7d2b-4a0b-9fe3-660b1ff83505 |
| 스티커 메모 API | 91ca2ca5-3b3e-41dd-ab65-809fa3dffffa |
| 기판 컨텍스트 서비스 | 13937bba-652e-4c46-b222-3003f4d1ff97 |
| SubstrateDirectoryEventProcessor | 26abc9a8-24f0-4b11-8234-e86ede698878 |
| 기판 검색 설정 관리 서비스 | a970bac6-63fe-4ec5-8884-8536862c42d4 |
| Sway | 905fcf26-4eb7-48a0-9ff0-8dcc7194b5ba |
| 대본 수집 | 97cb1f73-50df-47d1-8fb0-0271f2728514 |
| 유니버설 스토어 네이티브 클라이언트 | 268761a2-03f3-40df-8a8b-c3db24145b6b |
| Viva Engage(이전의 Yammer) | 00000005-0000-0ff1-ce00-0000000000000 |
| Viva Insights | fe93bfe1-7947-460a-a5e0-7a5906b51360 |
| WeveEngine | 3c896ded-22c5-450f-91f6-3d1ef0848f6e |
| Microsoft Azure Active Directory | 00000002-0000-0000-c000-0000000000000 |
| Windows Azure 보안 리소스 공급자 | 8edd93e1-2103-40b4-bd70-6e34e586362d |
| Windows Azure Service Management API | 797f4846-ba00-4fd7-ba43-dac1f8f63013 |
| WindowsDefenderATP 포털 | a3b79187-70b2-4139-83f9-6016c58cd27b |
| Windows 검색 | 26a7ee05-5602-4d76-a7ba-eae8b7b67941 |
| Windows 추천 | 1b3c667f-cde3-4090-b60b-3d2abd0117f0 |
| 비즈니스용 Windows Store | 45a330b1-b1ec-4cc1-9161-9f03992aa49f |
| Yammer Web | c1c74fed-04c9-4704-80dc-9f79a2e515cb |
| Yammer 웹 포함 | e1ef36fd-b883-4dbf-97f0-9ece4b576fc6 |
Microsoft 테넌트 소유 애플리케이션의 애플리케이션 ID
다음 표에는 Microsoft 테넌트 소유 애플리케이션(테넌트 ID: 72f988bf-86f1-41af-91ab-2d7cd011db47)이 나열되어 있습니다.
| 애플리케이션 이름 | 애플리케이션 ID |
|---|---|
| 그래프 탐색기 | de8bc8b5-d9f9-48b1-a8ad-b748da725064 |
| Microsoft Graph 명령줄 도구 | 14d82eec-204b-4c2f-b7e8-296a70dab67e |
| OutlookUserSettingsConsumer | 7ae974c5-1af7-4923-af3a-fb1fd14dcb7e |
| Vortex [wsfed enabled] | 5572c4c0-d078-44ce-b81c-6cbf8d3ed39e |
자세한 정보
자세한 내용은 Microsoft Entra 관리 센터의 로그인 활동 보고서를 참조 하세요.
도움을 요청하십시오.
질문이 있거나 도움이 필요한 경우 지원 요청을 생성하거나Azure 커뮤니티 지원에 문의하세요. Azure 피드백 커뮤니티에 제품 피드백을 제출할 수도 있습니다.