Configure credential manager - Microsoft Graph API
APPLIES TO: All API Management tiers
This article guides you through the steps required to create a managed connection to the Microsoft Graph API within Azure API Management. The authorization code grant type is used in this example.
You learn how to:
- Create a Microsoft Entra application
- Create and configure a credential provider in API Management
- Configure a connection
- Create a Microsoft Graph API in API Management and configure a policy
- Test your Microsoft Graph API in API Management
Prerequisites
Access to a Microsoft Entra tenant where you have permissions to create an app registration and to grant admin consent for the app's permissions. Learn more
If you want to create your own developer tenant, you can sign up for the Microsoft 365 Developer Program.
A running API Management instance. If you need to, create an Azure API Management instance.
Enable a system-assigned managed identity for API Management in the API Management instance.
Step 1: Create a Microsoft Entra application
Create a Microsoft Entra application for the API and give it the appropriate permissions for the requests that you want to call.
Sign in to the Azure portal with an account with sufficient permissions in the tenant.
Under Azure Services, search for Microsoft Entra ID.
On the left menu, select App registrations, and then select + New registration.
On the Register an application page, enter your application registration settings:
In Name, enter a meaningful name that will be displayed to users of the app, such as MicrosoftGraphAuth.
In Supported account types, select an option that suits your scenario, for example, Accounts in this organizational directory only (Single tenant).
Set the Redirect URI to Web, and enter
https://authorization-manager.consent.azure-apim.net/redirect/apim/<YOUR-APIM-SERVICENAME>, substituting the name of the API Management service where you will configure the credential provider.Select Register.

On the left menu, select API permissions, and then select + Add a permission.

- Select Microsoft Graph, and then select Delegated permissions.
Note
Make sure the permission User.Read with the type Delegated has already been added.
- Type Team, expand the Team options, and then select Team.ReadBasic.All. Select Add permissions.
- Next, select Grant admin consent for Default Directory. The status of the permissions changes to Granted for Default Directory.
- Select Microsoft Graph, and then select Delegated permissions.
On the left menu, select Overview. On the Overview page, find the Application (client) ID value and record it for use in Step 2.
On the left menu, select Certificates & secrets, and then select + New client secret.

- Enter a Description.
- Select an option for Expires.
- Select Add.
- Copy the client secret's Value before leaving the page. You will need it in Step 2.
Step 2: Configure a credential provider in API Management
Sign into the portal and go to your API Management instance.
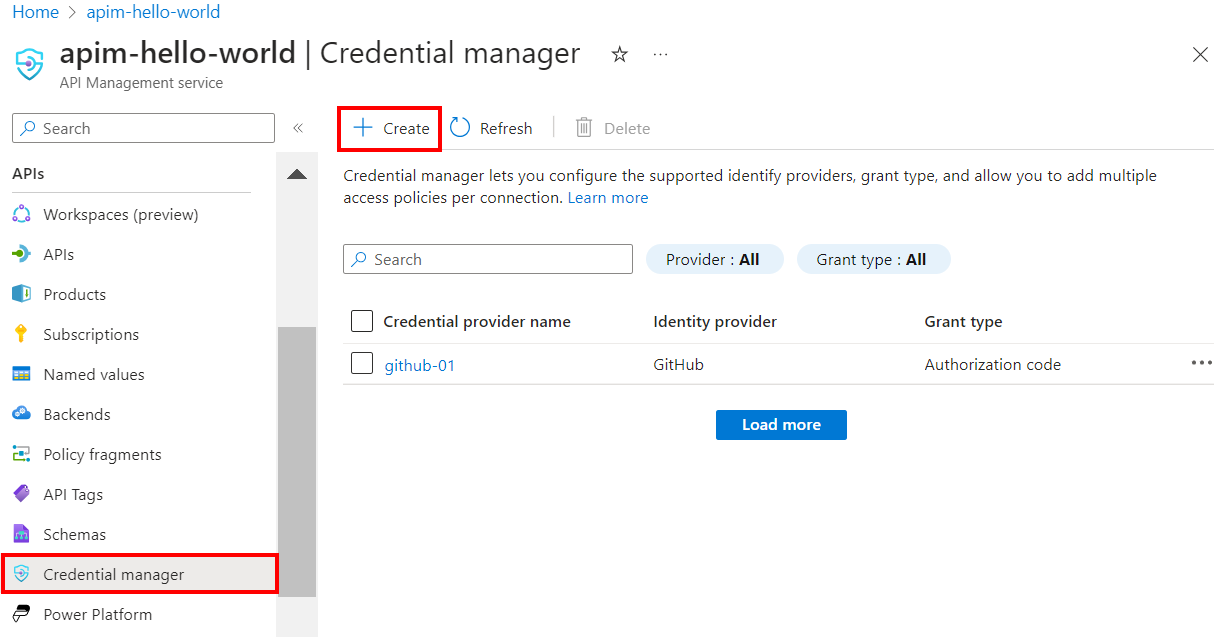
On the left menu, select Credential manager, and then select + Create.
On the Create credential provider page, enter the following settings, and select Create:
Settings Value Credential provider name A name of your choice, such as MicrosoftEntraID-01 Identity provider Select Azure Active Directory v1 Grant type Select Authorization code Authorization URL Optional for Microsoft Entra identity provider. Default is https://login.microsoftonline.com.Client ID Paste the value you copied earlier from the app registration Client secret Paste the value you copied earlier from the app registration Resource URL https://graph.microsoft.comTenant ID Optional for Microsoft Entra identity provider. Default is Common. Scopes Optional for Microsoft Entra identity provider. Automatically configured from Microsoft Entra app's API permissions.
Step 3: Configure a connection
On the Connection tab, complete the steps for your connection to the provider.
Note
When you configure a connection, API Management by default sets up an access policy that enables access by the instance's systems-assigned managed identity. This access is sufficient for this example. You can add additional access policies as needed.
- Enter a Connection name, then select Save.
- Under Step 2: Login to your connection (for authorization code grant type), select the link to login to the credential provider. Complete steps there to authorize access, and return to API Management.
- Under Step 3: Determine who will have access to this connection (Access policy), the managed identity member is listed. Adding other members is optional, depending on your scenario.
- Select Complete.
The new connection appears in the list of connections, and shows a status of Connected. If you want to create another connection for the credential provider, complete the preceding steps.
Tip
Use the portal to add, update, or delete connections to a credential provider at any time. For more information, see Configure multiple connections.
Note
If you update your Microsoft Graph permissions after this step, you will have to repeat Steps 2 and 3.
Step 4: Create a Microsoft Graph API in API Management and configure a policy
Sign into the portal and go to your API Management instance.
On the left menu, select APIs > + Add API.
Select HTTP and enter the following settings. Then select Create.
Setting Value Display name msgraph Web service URL https://graph.microsoft.com/v1.0API URL suffix msgraph Navigate to the newly created API and select Add Operation. Enter the following settings and select Save.
Setting Value Display name getprofile URL for GET /me Follow the preceding steps to add another operation with the following settings.
Setting Value Display name getJoinedTeams URL for GET /me/joinedTeams Select All operations. In the Inbound processing section, select the (</>) (code editor) icon.
Copy and paste the following snippet. Update the
get-authorization-contextpolicy with the names of the credential provider and connection that you configured in the preceding steps, and select Save.- Substitute your credential provider name as the value of
provider-id - Substitute your connection name as the value of
authorization-id
<policies> <inbound> <base /> <get-authorization-context provider-id="MicrosoftEntraID-01" authorization-id="first-connection" context-variable-name="auth-context" identity-type="managed" ignore-error="false" /> <set-header name="Authorization" exists-action="override"> <value>@("Bearer " + ((Authorization)context.Variables.GetValueOrDefault("auth-context"))?.AccessToken)</value> </set-header> </inbound> <backend> <base /> </backend> <outbound> <base /> </outbound> <on-error> <base /> </on-error> </policies>- Substitute your credential provider name as the value of
The preceding policy definition consists of two parts:
- The get-authorization-context policy fetches an authorization token by referencing the credential provider and connection that were created earlier.
- The set-header policy creates an HTTP header with the fetched access token.
Step 5: Test the API
On the Test tab, select one operation that you configured.
Select Send.

A successful response returns user data from the Microsoft Graph.
Related content
- Learn more about authentication and authorization policies in Azure API Management.
- Learn more about scopes and permissions in Microsoft Entra ID.