Common alert schema
The common alert schema standardizes the consumption of Azure Monitor alert notifications. Historically, activity log, metric, and log search alerts each had their own email templates and webhook schemas. The common alert schema provides one standardized schema for all alert notifications.
Using a standardized schema helps minimize the number of integrations, which simplifies the process of managing and maintaining your integrations. The common schema enables a richer alert consumption experience in both the Azure portal and the Azure mobile app.
The common alert schema provides a consistent structure for:
- Email templates: Use the detailed email template to diagnose issues at a glance. Embedded links to the alert instance on the portal and to the affected resource ensure that you can quickly jump into the remediation process.
- JSON structure: Use the consistent JSON structure to build integrations for all alert types using:
- Azure Logic Apps
- Azure Functions
- Azure Automation runbook
Note
- Alerts generated by VM insights do not support the common schema.
- Smart detection alerts use the common schema by default. You don't have to enable the common schema for smart detection alerts.
Structure of the common schema
The common schema includes information about the affected resource and the cause of the alert in these sections:
Essentials: Standardized fields, used by all alert types that describe the resource affected by the alert and common alert metadata, such as severity or description.
If you want to route alert instances to specific teams based on criteria such as a resource group, you can use the fields in the Essentials section to provide routing logic for all alert types. The teams that receive the alert notification can then use the context fields for their investigation.
Alert context: Fields that vary depending on the type of the alert. The alert context fields describe the cause of the alert. For example, a metric alert would have fields like the metric name and metric value in the alert context. An activity log alert would have information about the event that generated the alert.
Custom properties: Additional information that is not included in the alert payload by default can be included in the alert payload using custom properties. Custom properties are a Key:Value pair that can include any information configured in the alert rule.
Sample alert payload
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/<subscription ID>/providers/Microsoft.AlertsManagement/alerts/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e",
"alertRule": "WCUS-R2-Gen2",
"severity": "Sev3",
"signalType": "Metric",
"monitorCondition": "Resolved",
"monitoringService": "Platform",
"alertTargetIDs": [
"/subscriptions/<subscription ID>/resourcegroups/pipelinealertrg/providers/microsoft.compute/virtualmachines/wcus-r2-gen2"
],
"configurationItems": [
"wcus-r2-gen2"
],
"originAlertId": "3f2d4487-b0fc-4125-8bd5-7ad17384221e_PipeLineAlertRG_microsoft.insights_metricAlerts_WCUS-R2-Gen2_-117781227",
"firedDateTime": "2019-03-22T13:58:24.3713213Z",
"resolvedDateTime": "2019-03-22T14:03:16.2246313Z",
"description": "",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": null,
"conditionType": "SingleResourceMultipleMetricCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Percentage CPU",
"metricNamespace": "Microsoft.Compute/virtualMachines",
"operator": "GreaterThan",
"threshold": "25",
"timeAggregation": "Average",
"dimensions": [
{
"name": "ResourceId",
"value": "3efad9dc-3d50-4eac-9c87-8b3fd6f97e4e"
}
],
"metricValue": 7.727
}
]
}
},
"customProperties": {
"Key1": "Value1",
"Key2": "Value2"
}
}
}
For sample alerts that use the common schema, see Sample alert payloads.
Essentials fields
| Field | Description |
|---|---|
| alertId | The unique resource ID that identifies the alert instance. |
| alertRule | The name of the alert rule that generated the alert instance. |
| Severity | The severity of the alert. Possible values are Sev0, Sev1, Sev2, Sev3, or Sev4. |
| signalType | Identifies the signal on which the alert rule was defined. Possible values are Metric, Log, or Activity Log. |
| monitorCondition | When an alert fires, the alert's monitor condition is set to Fired. When the underlying condition that caused the alert to fire clears, the monitor condition is set to Resolved. |
| monitoringService | The monitoring service or solution that generated the alert. The monitoring service determines which fields are in the alert context. |
| alertTargetIDs | The list of the Azure Resource Manager IDs that are affected targets of an alert. For a log search alert defined on a Log Analytics workspace or Application Insights instance, it's the respective workspace or application. |
| configurationItems | The list of affected resources of an alert. In some cases, the configuration items can be different from the alert targets. For example, in metric-for-log or log search alerts defined on a Log Analytics workspace, the configuration items are the actual resources sending the data, and not the workspace.
configurationItems field is used to correlate alerts to resources in a configuration management database. |
| originAlertId | The ID of the alert instance, as generated by the monitoring service generating it. |
| firedDateTime | The date and time when the alert instance was fired in Coordinated Universal Time (UTC). |
| resolvedDateTime | The date and time when the monitor condition for the alert instance is set to Resolved in UTC. Currently only applicable for metric alerts. |
| description | The description, as defined in the alert rule. |
| alertRuleID | The ID of the alert rule that generated the alert instance. |
| resourceType | The resource type affected by the alert. |
| resourceGroupName | Name of the resource group for the impacted resource. |
| essentialsVersion | The version number for the essentials section. |
| alertContextVersion | The version number for the alertContext section. |
| investigationLink | Link to investigate the alert in Azure Monitor. Currently requires limited preview registration. |
Alert context fields for metric alerts
| Field | Description |
|---|---|
| properties | (Optional.) A collection of customer-defined properties. |
| conditionType | The type of condition selected for the alert rule: - static threshold - dynamic threshold - webtest |
| condition | |
| windowSize | The time period analyzed by the alert rule. |
| allOf | Indicates that all conditions defined in the alert rule must be met to trigger an alert. |
| alertSensitivity | In an alert rule with a dynamic threshold, indicates how sensitive the rule is, or how much the value can deviate from the upper or lower threshold. |
| failingPeriods | In an alert rule with a dynamic threshold, the number of evaluation periods that don't meet the alert threshold that trigger an alert. For example, you can indicate that an alert is triggered when 3 out of the last five evaluation periods aren't within the alert thresholds. |
| numberOfEvaluationPeriods | The total number of evaluations. |
| minFailingPeriodsToAlert | The minimum number of evaluations that do no meet the alert rule conditions. |
| ignoreDataBefore | (Optional.) In an alert rule with a dynamic threshold, the date from which the threshold is calculated. Use this value to indicate that the rule shouldn't calculate the dynamic threshold using data from before the specified date. |
| metricName | The name of the metric monitored by the alert rule. |
| metricNamespace | The namespace of the metric monitored by the alert rule. |
| operator | The logical operator of the alert rule. |
| threshold | The threshold defined in the alert rule. For an alert rule with a dynamic threshold, this value is the calculated threshold. |
| timeAggregation | The aggregation type of the alert rule. |
| dimensions | The metric dimension that triggered the alert. |
| name | The dimension name. |
| value | The dimension value. |
| metricValue | The metric value at the time that it violated the threshold. |
| webTestName | If the condition type is webtest, the name of the webtest. |
| windowStartTime | The start time of the evaluation window in which the alert fired. |
| windowEndTime | The end time of the evaluation window in which the alert fired. |
Sample metric alert with a static threshold when the monitoringService = Platform
{
"alertContext": {
"properties": null,
"conditionType": "SingleResourceMultipleMetricCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Percentage CPU",
"metricNamespace": "Microsoft.Compute/virtualMachines",
"operator": "GreaterThan",
"threshold": "25",
"timeAggregation": "Average",
"dimensions": [
{
"name": "ResourceId",
"value": "3efad9dc-3d50-4eac-9c87-8b3fd6f97e4e"
}
],
"metricValue": 31.1105
}
],
"windowStartTime": "2019-03-22T13:40:03.064Z",
"windowEndTime": "2019-03-22T13:45:03.064Z"
}
}
}
Sample metric alert with a dynamic threshold when the monitoringService = Platform
{
"alertContext": {
"properties": null,
"conditionType": "DynamicThresholdCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"alertSensitivity": "High",
"failingPeriods": {
"numberOfEvaluationPeriods": 1,
"minFailingPeriodsToAlert": 1
},
"ignoreDataBefore": null,
"metricName": "Egress",
"metricNamespace": "microsoft.storage/storageaccounts",
"operator": "GreaterThan",
"threshold": "47658",
"timeAggregation": "Total",
"dimensions": [],
"metricValue": 50101
}
],
"windowStartTime": "2021-07-20T05:07:26.363Z",
"windowEndTime": "2021-07-20T05:12:26.363Z"
}
}
}
Sample metric alert for availability tests when the monitoringService = Platform
{
"alertContext": {
"properties": null,
"conditionType": "WebtestLocationAvailabilityCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Failed Location",
"metricNamespace": null,
"operator": "GreaterThan",
"threshold": "2",
"timeAggregation": "Sum",
"dimensions": [],
"metricValue": 5,
"webTestName": "myAvailabilityTest-myApplication"
}
],
"windowStartTime": "2019-03-22T13:40:03.064Z",
"windowEndTime": "2019-03-22T13:45:03.064Z"
}
}
}
Alert context fields for log search alerts
Note
When you enable the common schema, the fields in the payload are reset to the common schema fields. Therefore, log search alerts have these limitations regarding the common schema:
- The common schema is not supported for log search alerts using webhooks with a custom email subject and/or JSON payload, since the common schema overwrites the custom configurations.
- Alerts using the common schema have an upper size limit of 256 KB per alert. If the log search alerts payload includes search results that cause the alert to exceed the maximum size, the search results aren't embedded in the log search alerts payload. You can check if the payload includes the search results with the
IncludedSearchResultsflag. UseLinkToFilteredSearchResultsAPIorLinkToSearchResultsAPIto access query results with the Log Analytics API if the search results are not included.
| Field | Description |
|---|---|
| SearchQuery | The query defined in the alert rule. |
| SearchIntervalStartTimeUtc | The start time of the evaluation window in which the alert fired in UTC. |
| SearchIntervalEndTimeUtc | The end time of the evaluation window in which the alert fired in UTC. |
| ResultCount | The number of records returned by the query. For metric measurement rules, the number or records that match the specific dimension combination. |
| LinkToSearchResults | A link to the search results. |
| LinkToFilteredSearchResultsUI | For metric measurement rules, the link to the search results after they've been filtered by the dimension combinations. |
| LinkToSearchResultsAPI | A link to the query results using the Log Analytics API. |
| LinkToFilteredSearchResultsAPI | For metric measurement rules, the link to the search results using the Log Analytics API after they've been filtered by the dimension combinations. |
| SearchIntervalDurationMin | The total number of minutes in the search interval. |
| SearchIntervalInMin | The total number of minutes in the search interval. |
| Threshold | The threshold defined in the alert rule. |
| Operator | The operator defined in the alert rule. |
| ApplicationID | The Application Insights ID on which the alert was triggered. |
| Dimensions | For metric measurement rules, the metric dimensions on which the alert was triggered. |
| name | The dimension name. |
| value | The dimension value. |
| SearchResults | The complete search results. |
| table | The table of results in the search results. |
| name | The name of the table in the search results. |
| columns | The columns in the table. |
| name | The name of the column. |
| type | The type of the column. |
| rows | The rows in the table. |
| DataSources | The data sources on which the alert was triggered. |
| resourceID | The resource ID affected by the alert. |
| tables | The draft response tables included in the query. |
| IncludedSearchResults | Flag that indicates if the payload should contain the results. |
| AlertType | The alert type: - Metric Measurement - Number Of Results |
Sample log search alert when the monitoringService = Log Analytics
{
"alertContext": {
"SearchQuery": "Perf | where ObjectName == \"Processor\" and CounterName == \"% Processor Time\" | summarize AggregatedValue = avg(CounterValue) by bin(TimeGenerated, 5m), Computer",
"SearchIntervalStartTimeUtc": "3/22/2019 1:36:31 PM",
"SearchIntervalEndtimeUtc": "3/22/2019 1:51:31 PM",
"ResultCount": 2,
"LinkToSearchResults": "https://portal.azure.com/#Analyticsblade/search/index?_timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToFilteredSearchResultsUI": "https://portal.azure.com/#Analyticsblade/search/index?_timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/workspaceID/query?query=Heartbeat×pan=2020-05-07T18%3a11%3a51.0000000Z%2f2020-05-07T18%3a16%3a51.0000000Z",
"LinkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/workspaceID/query?query=Heartbeat×pan=2020-05-07T18%3a11%3a51.0000000Z%2f2020-05-07T18%3a16%3a51.0000000Z",
"SeverityDescription": "Warning",
"WorkspaceId": "12345a-1234b-123c-123d-12345678e",
"SearchIntervalDurationMin": "15",
"AffectedConfigurationItems": [
"INC-Gen2Alert"
],
"SearchIntervalInMinutes": "15",
"Threshold": 10000,
"Operator": "Less Than",
"Dimensions": [
{
"name": "Computer",
"value": "INC-Gen2Alert"
}
],
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "$table",
"type": "string"
},
{
"name": "Computer",
"type": "string"
},
{
"name": "TimeGenerated",
"type": "datetime"
}
],
"rows": [
[
"Fabrikam",
"33446677a",
"2018-02-02T15:03:12.18Z"
],
[
"Contoso",
"33445566b",
"2018-02-02T15:16:53.932Z"
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/bbbb1b1b-cc2c-dd3d-ee4e-ffffff5f5f5f/resourcegroups/test/providers/microsoft.operationalinsights/workspaces/test",
"tables": [
"Heartbeat"
]
}
]
},
"IncludedSearchResults": "True",
"AlertType": "Metric measurement"
}
}
Sample log search alert when the monitoringService = Application Insights
{
"alertContext": {
"SearchQuery": "requests | where resultCode == \"500\" | summarize AggregatedValue = Count by bin(Timestamp, 5m), IP",
"SearchIntervalStartTimeUtc": "3/22/2019 1:36:33 PM",
"SearchIntervalEndtimeUtc": "3/22/2019 1:51:33 PM",
"ResultCount": 2,
"LinkToSearchResults": "https://portal.azure.com/AnalyticsBlade/subscriptions/12345a-1234b-123c-123d-12345678e/?query=search+*+&timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToFilteredSearchResultsUI": "https://portal.azure.com/AnalyticsBlade/subscriptions/12345a-1234b-123c-123d-12345678e/?query=search+*+&timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToSearchResultsAPI": "https://api.applicationinsights.io/v1/apps/0MyAppId0/metrics/requests/count",
"LinkToFilteredSearchResultsAPI": "https://api.applicationinsights.io/v1/apps/0MyAppId0/metrics/requests/count",
"SearchIntervalDurationMin": "15",
"SearchIntervalInMinutes": "15",
"Threshold": 10000.0,
"Operator": "Less Than",
"ApplicationId": "00001111-aaaa-2222-bbbb-3333cccc4444",
"Dimensions": [
{
"name": "IP",
"value": "1.1.1.1"
}
],
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "$table",
"type": "string"
},
{
"name": "Id",
"type": "string"
},
{
"name": "Timestamp",
"type": "datetime"
}
],
"rows": [
[
"Fabrikam",
"33446677a",
"2018-02-02T15:03:12.18Z"
],
[
"Contoso",
"33445566b",
"2018-02-02T15:16:53.932Z"
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/cccc2c2c-dd3d-ee4e-ff5f-aaaaaa6a6a6a/resourcegroups/test/providers/microsoft.operationalinsights/workspaces/test",
"tables": [
"Heartbeat"
]
}
]
},
"IncludedSearchResults": "True",
"AlertType": "Metric measurement"
}
}
Sample log search alert when the monitoringService = Log Alerts V2
Note
Log search alert rules from API version 2020-05-01 use this payload type, which only supports common schema. Search results aren't embedded in the log search alerts payload when you use this version. Use dimensions to provide context to fired alerts. You can also use LinkToFilteredSearchResultsAPI or LinkToSearchResultsAPI to access query results with the Log Analytics API. If you must embed the results, use a logic app with the provided links to generate a custom payload.
{
"alertContext": {
"properties": {
"name1": "value1",
"name2": "value2"
},
"conditionType": "LogQueryCriteria",
"condition": {
"windowSize": "PT10M",
"allOf": [
{
"searchQuery": "Heartbeat",
"metricMeasureColumn": "CounterValue",
"targetResourceTypes": "['Microsoft.Compute/virtualMachines']",
"operator": "LowerThan",
"threshold": "1",
"timeAggregation": "Count",
"dimensions": [
{
"name": "Computer",
"value": "TestComputer"
}
],
"metricValue": 0.0,
"failingPeriods": {
"numberOfEvaluationPeriods": 1,
"minFailingPeriodsToAlert": 1
},
"linkToSearchResultsUI": "https://portal.azure.com#@12345a-1234b-123c-123d-12345678e/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%212345a-1234b-123c-123d-12345678e%2FresourceGroups%2FContoso%2Fproviders%2FMicrosoft.Compute%2FvirtualMachines%2FContoso%22%7D%5D%7D/q/eJzzSE0sKklKTSypUSjPSC1KVQjJzE11T81LLUosSU1RSEotKU9NzdNIAfJKgDIaRgZGBroG5roGliGGxlYmJlbGJnoGEKCpp4dDmSmKMk0A/prettify/1/timespan/2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToFilteredSearchResultsUI": "https://portal.azure.com#@12345a-1234b-123c-123d-12345678e/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%212345a-1234b-123c-123d-12345678e%2FresourceGroups%2FContoso%2Fproviders%2FMicrosoft.Compute%2FvirtualMachines%2FContoso%22%7D%5D%7D/q/eJzzSE0sKklKTSypUSjPSC1KVQjJzE11T81LLUosSU1RSEotKU9NzdNIAfJKgDIaRgZGBroG5roGliGGxlYmJlbGJnoGEKCpp4dDmSmKMk0A/prettify/1/timespan/2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToSearchResultsAPI": "https://api.loganalytics.io/v1/subscriptions/12345a-1234b-123c-123d-12345678e/resourceGroups/Contoso/providers/Microsoft.Compute/virtualMachines/Contoso/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282020-07-09T13%3A44%3A34.0000000%29..datetime%282020-07-09T13%3A54%3A34.0000000%29%29×pan=2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/subscriptions/12345a-1234b-123c-123d-12345678e/resourceGroups/Contoso/providers/Microsoft.Compute/virtualMachines/Contoso/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282020-07-09T13%3A44%3A34.0000000%29..datetime%282020-07-09T13%3A54%3A34.0000000%29%29×pan=2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z"
}
],
"windowStartTime": "2020-07-07T13:54:34Z",
"windowEndTime": "2020-07-09T13:54:34Z"
}
}
}
Alert context fields for activity log alerts
See Azure activity log event schema for detailed information about the fields in activity log alerts.
Sample activity log alert when the monitoringService = Activity Log - Administrative
{
"alertContext": {
"authorization": {
"action": "Microsoft.Compute/virtualMachines/restart/action",
"scope": "/subscriptions/<subscription ID>/resourceGroups/PipeLineAlertRG/providers/Microsoft.Compute/virtualMachines/WCUS-R2-ActLog"
},
"channels": "Operation",
"claims": "{\"aud\":\"https://management.core.windows.net/\",\"iss\":\"https://sts.windows.net/12345a-1234b-123c-123d-12345678e/\",\"iat\":\"1553260826\",\"nbf\":\"1553260826\",\"exp\":\"1553264726\",\"aio\":\"42JgYNjdt+rr+3j/dx68v018XhuFAwA=\",\"appid\":\"11112222-bbbb-3333-cccc-4444dddd5555\",\"appidacr\":\"2\",\"http://schemas.microsoft.com/identity/claims/identityprovider\":\"https://sts.windows.net/12345a-1234b-123c-123d-12345678e/\",\"http://schemas.microsoft.com/identity/claims/objectidentifier\":\"22223333-cccc-4444-dddd-5555eeee6666\",\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier\":\"22223333-cccc-4444-dddd-5555eeee6666\",\"http://schemas.microsoft.com/identity/claims/tenantid\":\"12345a-1234b-123c-123d-12345678e\",\"uti\":\"v5wYC9t9ekuA2rkZSVZbAA\",\"ver\":\"1.0\"}",
"caller": "22223333-cccc-4444-dddd-5555eeee6666",
"correlationId": "aaaa0000-bb11-2222-33cc-444444dddddd",
"eventSource": "Administrative",
"eventTimestamp": "2019-03-22T13:56:31.2917159+00:00",
"eventDataId": "161fda7e-1cb4-4bc5-9c90-857c55a8f57b",
"level": "Informational",
"operationName": "Microsoft.Compute/virtualMachines/restart/action",
"operationId": "310db69b-690f-436b-b740-6103ab6b0cba",
"status": "Succeeded",
"subStatus": "",
"submissionTimestamp": "2019-03-22T13:56:54.067593+00:00"
}
}
Sample activity log alert when the monitoringService = Activity Log - Policy
{
"alertContext": {
"authorization": {
"action": "Microsoft.Resources/checkPolicyCompliance/read",
"scope": "/subscriptions/<GUID>"
},
"channels": "Operation",
"claims": "{\"aud\":\"https://management.azure.com/\",\"iss\":\"https://sts.windows.net/<GUID>/\",\"iat\":\"1566711059\",\"nbf\":\"1566711059\",\"exp\":\"1566740159\",\"aio\":\"42FgYOhynHNw0scy3T/bL71+xLyqEwA=\",\"appid\":\"<GUID>\",\"appidacr\":\"2\",\"http://schemas.microsoft.com/identity/claims/identityprovider\":\"https://sts.windows.net/<GUID>/\",\"http://schemas.microsoft.com/identity/claims/objectidentifier\":\"<GUID>\",\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier\":\"<GUID>\",\"http://schemas.microsoft.com/identity/claims/tenantid\":\"<GUID>\",\"uti\":\"Miy1GzoAG0Scu_l3m1aIAA\",\"ver\":\"1.0\"}",
"caller": "<GUID>",
"correlationId": "<GUID>",
"eventSource": "Policy",
"eventTimestamp": "2019-08-25T11:11:34.2269098+00:00",
"eventDataId": "<GUID>",
"level": "Warning",
"operationName": "Microsoft.Authorization/policies/audit/action",
"operationId": "<GUID>",
"properties": {
"isComplianceCheck": "True",
"resourceLocation": "eastus2",
"ancestors": "<GUID>",
"policies": "[{\"policyDefinitionId\":\"/providers/Microsoft.Authorization/policyDefinitions/<GUID>/\",\"policySetDefinitionId\":\"/providers/Microsoft.Authorization/policySetDefinitions/<GUID>/\",\"policyDefinitionReferenceId\":\"vulnerabilityAssessmentMonitoring\",\"policySetDefinitionName\":\"<GUID>\",\"policyDefinitionName\":\"<GUID>\",\"policyDefinitionEffect\":\"AuditIfNotExists\",\"policyAssignmentId\":\"/subscriptions/<GUID>/providers/Microsoft.Authorization/policyAssignments/SecurityCenterBuiltIn/\",\"policyAssignmentName\":\"SecurityCenterBuiltIn\",\"policyAssignmentScope\":\"/subscriptions/<GUID>\",\"policyAssignmentSku\":{\"name\":\"A1\",\"tier\":\"Standard\"},\"policyAssignmentParameters\":{}}]"
},
"status": "Succeeded",
"subStatus": "",
"submissionTimestamp": "2019-08-25T11:12:46.1557298+00:00"
}
}
Sample activity log alert when the monitoringService = Activity Log - Autoscale
{
"alertContext": {
"channels": "Admin, Operation",
"claims": "{\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/spn\":\"Microsoft.Insights/autoscaleSettings\"}",
"caller": "Microsoft.Insights/autoscaleSettings",
"correlationId": "<GUID>",
"eventSource": "Autoscale",
"eventTimestamp": "2019-08-21T16:17:47.1551167+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Insights/AutoscaleSettings/Scaleup/Action",
"operationId": "<GUID>",
"properties": {
"description": "The autoscale engine attempting to scale resource '/subscriptions/d<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS' from 9 instances count to 10 instances count.",
"resourceName": "/subscriptions/<GUID>/resourceGroups/voiceassistancedemo/providers/Microsoft.Compute/virtualMachineScaleSets/alexademo",
"oldInstancesCount": "9",
"newInstancesCount": "10",
"activeAutoscaleProfile": "{\r\n \"Name\": \"Auto created scale condition\",\r\n \"Capacity\": {\r\n \"Minimum\": \"1\",\r\n \"Maximum\": \"10\",\r\n \"Default\": \"1\"\r\n },\r\n \"Rules\": [\r\n {\r\n \"MetricTrigger\": {\r\n \"Name\": \"Percentage CPU\",\r\n \"Namespace\": \"microsoft.compute/virtualmachinescalesets\",\r\n \"Resource\": \"/subscriptions/<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS\",\r\n \"ResourceLocation\": \"eastus\",\r\n \"TimeGrain\": \"PT1M\",\r\n \"Statistic\": \"Average\",\r\n \"TimeWindow\": \"PT5M\",\r\n \"TimeAggregation\": \"Average\",\r\n \"Operator\": \"GreaterThan\",\r\n \"Threshold\": 0.0,\r\n \"Source\": \"/subscriptions/<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS\",\r\n \"MetricType\": \"MDM\",\r\n \"Dimensions\": [],\r\n \"DividePerInstance\": false\r\n },\r\n \"ScaleAction\": {\r\n \"Direction\": \"Increase\",\r\n \"Type\": \"ChangeCount\",\r\n \"Value\": \"1\",\r\n \"Cooldown\": \"PT1M\"\r\n }\r\n }\r\n ]\r\n}",
"lastScaleActionTime": "Wed, 21 Aug 2019 16:17:47 GMT"
},
"status": "Succeeded",
"submissionTimestamp": "2019-08-21T16:17:47.2410185+00:00"
}
}
Sample activity log alert when the monitoringService = Activity Log - Security
{
"alertContext": {
"channels": "Operation",
"correlationId": "<GUID>",
"eventSource": "Security",
"eventTimestamp": "2019-08-26T08:34:14+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Security/locations/alerts/activate/action",
"operationId": "<GUID>",
"properties": {
"threatStatus": "Quarantined",
"category": "Virus",
"threatID": "2147519003",
"filePath": "C:\\AlertGeneration\\test.eicar",
"protectionType": "Windows Defender",
"actionTaken": "Blocked",
"resourceType": "Virtual Machine",
"severity": "Low",
"compromisedEntity": "testVM",
"remediationSteps": "[\"No user action is necessary\"]",
"attackedResourceType": "Virtual Machine"
},
"status": "Active",
"submissionTimestamp": "2019-08-26T09:28:58.3019107+00:00"
}
}
Sample activity log alert when the monitoringService = ServiceHealth
{
"alertContext": {
"authorization": null,
"channels": 1,
"claims": null,
"caller": null,
"correlationId": "bbbb1111-cc22-3333-44dd-555555eeeeee",
"eventSource": 2,
"eventTimestamp": "2019-06-24T11:31:19.0312699+00:00",
"httpRequest": null,
"eventDataId": "<GUID>",
"level": 3,
"operationName": "Microsoft.ServiceHealth/maintenance/action",
"operationId": "<GUID>",
"properties": {
"title": "Azure Synapse Analytics Scheduled Maintenance Pending",
"service": "Azure Synapse Analytics",
"region": "East US",
"communication": "<MESSAGE>",
"incidentType": "Maintenance",
"trackingId": "<GUID>",
"impactStartTime": "2019-06-26T04:00:00Z",
"impactMitigationTime": "2019-06-26T12:00:00Z",
"impactedServices": "[{\"ImpactedRegions\":[{\"RegionName\":\"East US\"}],\"ServiceName\":\"Azure Synapse Analytics\"}]",
"impactedServicesTableRows": "<tr>\r\n<td align='center' style='padding: 5px 10px; border-right:1px solid black; border-bottom:1px solid black'>Azure Synapse Analytics</td>\r\n<td align='center' style='padding: 5px 10px; border-bottom:1px solid black'>East US<br></td>\r\n</tr>\r\n",
"defaultLanguageTitle": "Azure Synapse Analytics Scheduled Maintenance Pending",
"defaultLanguageContent": "<MESSAGE>",
"stage": "Planned",
"communicationId": "<GUID>",
"maintenanceId": "<GUID>",
"isHIR": "false",
"version": "0.1.1"
},
"status": "Active",
"subStatus": null,
"submissionTimestamp": "2019-06-24T11:31:31.7147357+00:00",
"ResourceType": null
}
}
Sample activity log alert when the monitoringService = ResourceHealth
{
"alertContext": {
"channels": "Admin, Operation",
"correlationId": "<GUID>",
"eventSource": "ResourceHealth",
"eventTimestamp": "2019-06-24T15:42:54.074+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Resourcehealth/healthevent/Activated/action",
"operationId": "<GUID>",
"properties": {
"title": "This virtual machine is stopping and deallocating as requested by an authorized user or process",
"details": null,
"currentHealthStatus": "Unavailable",
"previousHealthStatus": "Available",
"type": "Downtime",
"cause": "UserInitiated"
},
"status": "Active",
"submissionTimestamp": "2019-06-24T15:45:20.4488186+00:00"
}
}
Alert context fields for Prometheus alerts
See Azure Monitor managed service for Prometheus rule groups (preview) for detailed information about the fields in Prometheus alerts.
Sample Prometheus alert
{
"alertContext": {
"interval": "PT1M",
"expression": "sql_up > 0",
"expressionValue": "0",
"for": "PT2M",
"labels": {
"Environment": "Prod",
"cluster": "myCluster1"
},
"annotations": {
"summary": "alert on SQL availability"
},
"ruleGroup": "/subscriptions/<subscription ID>/resourceGroups/myResourceGroup/providers/Microsoft.AlertsManagement/prometheusRuleGroups/myRuleGroup"
}
}
Custom properties fields
If the alert rule that generated your alert contains action groups, custom properties can contain additional information about the alert. The custom properties section contains “key: value” objects that are added to webhook notifications.
If custom properties aren't set in the alert rule, the field is null.
Enable the common alert schema
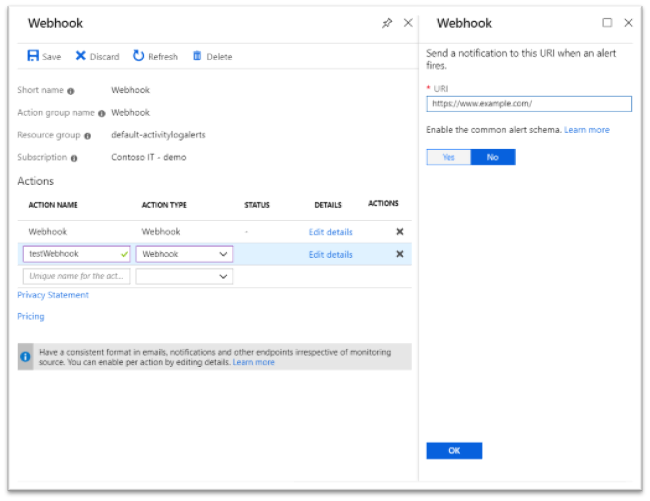
Use action groups in the Azure portal or use the REST API to enable the common alert schema. Schemas are defined at the action level. For example, you must separately enable the schema for an email action and a webhook action.
Enable the common schema in the Azure portal
- Open any existing action or a new action in an action group.
- Select Yes to enable the common alert schema.
Enable the common schema using the REST API
You can also use the Action Groups API to opt in to the common alert schema. In the create or update REST API call,
- Set the "useCommonAlertSchema" flag to
trueto enable the common schema - Set the "useCommonAlertSchema" flag to
falseto use the non-common schema for email, webhook, Logic Apps, Azure Functions, or Automation runbook actions.
Sample REST API call for using the common schema
The following create or update REST API request:
- Enables the common alert schema for the email action "John Doe's email."
- Disables the common alert schema for the email action "Jane Smith's email."
- Enables the common alert schema for the webhook action "Sample webhook."
{
"properties": {
"groupShortName": "sample",
"enabled": true,
"emailReceivers": [
{
"name": "John Doe's email",
"emailAddress": "johndoe@email.com",
"useCommonAlertSchema": true
},
{
"name": "Jane Smith's email",
"emailAddress": "janesmith@email.com",
"useCommonAlertSchema": false
}
],
"smsReceivers": [
{
"name": "John Doe's mobile",
"countryCode": "1",
"phoneNumber": "1234567890"
},
{
"name": "Jane Smith's mobile",
"countryCode": "1",
"phoneNumber": "0987654321"
}
],
"webhookReceivers": [
{
"name": "Sample webhook",
"serviceUri": "http://www.example.com/webhook",
"useCommonAlertSchema": true
}
]
},
"location": "Global",
"tags": {}
}